Q1: What Is an AI SOC, an In-House SOC, and a Traditional MSSP, and Why Does the Three-Model Comparison Matter?
The Fragmented Security Reality No One Talks About
Here’s what I see every time we onboard a new client: CrowdStrike for endpoints, Splunk for logs, Okta for identity, separate AWS and Azure consoles, maybe a standalone email security gateway. Eight to twelve tools generating alerts, and nobody with a unified view of what’s actually happening. Alerts are everywhere, but understanding is nowhere. Every vendor dashboard tells part of the story. None tells the whole thing.
And yet, most articles still frame the security operations decision as a binary: build an in-house SOC or buy from an MSSP. That framing is outdated. Three distinct models now exist, each with fundamentally different architectures, cost structures, and response capabilities. If you’re making a decision without evaluating all three, you’re starting with an incomplete picture.
Why Traditional Models Hit a Ceiling
The In-House SOC gives you maximum control. You staff 8–12 FTEs across three analyst tiers, build custom detection logic tied to your business processes, and own every correlation rule. The cost? $1.6M–$2.86M per year on average, according to Ponemon Institute research, with a 6–18 month deployment timeline and 15–25% annual analyst turnover that constantly drains institutional knowledge.
The Traditional MSSP offers outsourced monitoring at $120K–$360K/year for SMBs, a fraction of in-house costs. But what you get is checkbox coverage: rigid playbooks, alert escalation without investigation context, and no containment capability. When something fires at 2 AM, the MSSP sends you an email. You still have to wake up, log in, and investigate.
Both models have a legitimate place. But both share a structural limit: they can’t scale detection intelligence without proportional headcount or cost growth.
The AI-Era Third Path: Detection Meets Response Meets Context
The architectural shift that created the AI SOC category comes down to two principles: detection without response is noise, and response without context is risk.
An AI SOC does not mean “no humans.” It means agentic AI handles L0–L1 triage, including automated enrichment, deduplication, severity scoring, and cross-tool correlation, autonomously and at machine speed. Human analysts focus on L2–L3 investigation, strategic threat hunting, digital forensics, and the judgment calls that require organizational context. This is synthesis, not replacement.
How UnderDefense MAXI Delivers the AI SOC + Human Ally Model
We built UnderDefense MAXI to operate as a vendor-agnostic AI SOC that integrates with 250+ existing security tools, including CrowdStrike, Splunk, SentinelOne, Microsoft Defender, Okta, and beyond, without forcing you to rip and replace anything. The architecture works like this:
- ✅ Agentic AI correlates alerts across endpoints, cloud, identity, and SaaS into a single context-aware detection layer
- ✅ Concierge Tier 3–4 analysts verify suspicious activity directly with affected users via Slack, Teams, or email, with no “please investigate” tickets back to your team
- ✅ Full containment capability, revoking compromised credentials, isolating endpoints, and blocking lateral movement, happens before your team wakes up
This is not monitoring. It is not just alerting. It’s partnership with containment.
The Three-Model Contrast That Frames Everything
An in-house SOC gives you control. A traditional MSSP gives you coverage. An AI SOC with Human Ally support gives you both, plus the speed and context that neither model alone can deliver. UnderDefense backs this with a 2-minute alert-to-triage SLA, 96% MITRE ATT&CK coverage, and zero ransomware cases across all MDR clients in six years of operation.
That’s the baseline for every comparison that follows.
Q2: What Does It Actually Cost to Build and Run an In-House SOC in 2026?
The Headline Number Most Boards Never See
An in-house SOC averages $2.86M per year according to Ponemon Institute research, with a 3-year total cost of ownership (TCO) ranging from $2M to $6.1M+ depending on organizational scale. The cost drivers break down into three buckets:
- Personnel: 65–70% of total spend ($600K–$2.1M/year depending on team size)
- SIEM/EDR/SOAR licenses: $200K–$500K/year for enterprise SIEM alone; add SOAR at ~$345K and XDR at ~$333K
- Infrastructure and facilities: $500K–$1M first-year CAPEX for physical or cloud-based SOC infrastructure
Year 1 is always the most expensive due to one-time capital expenditure plus the recruitment surge needed to fill every seat simultaneously.
⏰ The 24/7 Staffing Math Nobody Wants to Do
Here’s the number that catches every CFO off guard: one 24/7 “seat” requires 4.2–5 FTEs, accounting for shifts, PTO, sick leave, and training days. A minimum viable 24/7 SOC requires 8–12 FTEs just to cover basic operations.
| Role | Avg. Salary (US) | FTEs Needed | Annual Cost |
|---|---|---|---|
| Tier 1 Analyst | $65K–$85K | 4–6 | $260K–$510K |
| Tier 2 Analyst | $90K–$120K | 2–4 | $180K–$480K |
| Tier 3 / Threat Hunter | $130K–$170K | 1–2 | $130K–$340K |
| SOC Manager | $140K–$180K | 1 | $140K–$180K |
| Total (salary only) | 8–13 | $710K–$1.51M |
Add recruitment costs at 20–30% of salary per hire, 2–4 month hiring cycles in a market with 4.8 million unfilled cybersecurity positions globally, and 15–25% annual turnover rates, and the real people cost climbs significantly beyond base salaries.
💸 Hidden Costs That Erode Every Budget
Beyond headcount and tooling, several cost categories quietly consume 20–30% of the SOC budget:
- Training: $5K–$8K per course per analyst; SANS certifications run $7K–$9K each, and analysts need ongoing education to stay current
- The “tuning tax”: Continuous detection rule maintenance consumes 15–20% of analyst time, writing, testing, and refining correlation rules that are never truly “done”
- Burnout-driven turnover: Tier 1 analysts average 18-month tenure before leaving due to alert fatigue. Each departure triggers $15K–$25K in recruitment costs and months of ramp-up time
- Log ingestion costs: SIEM pricing scales non-linearly as telemetry grows, meaning more endpoints, more cloud workloads, more data, and exponentially higher licensing fees
💰 TCO Comparison Across All Three Models
| Model | Annual Cost (SMB) | Annual Cost (Enterprise) | Deployment Time |
|---|---|---|---|
| In-House SOC | $1.6M–$2.5M | $2.86M–$4M+ | 6–18 months |
| Traditional MSSP | $120K–$360K | $360K–$1.2M | 1–3 months |
| AI SOC / MDR | $120K–$360K | $360K–$900K | 2–4 weeks |
How UnderDefense Simplifies the Math
UnderDefense’s SOC Cost Calculator lets organizations model their specific TCO by inputting team size, tool stack, and compliance requirements. The UnderDefense MAXI platform delivers enterprise-grade SOC capabilities starting at $11–$15/endpoint/month, representing 830% ROI over 3 years with 30-day turnkey deployment, compared to the 6–18 month timeline and multi-million dollar commitment of building in-house.
Q3: Where Does an In-House SOC Genuinely Win on Customization, Control, and Compliance?
In-house SOCs genuinely excel in four areas: deep business-context integration, custom detection logic tied to proprietary systems, full data sovereignty for regulated industries, and institutional knowledge accumulation. Organizations in defense, government, or with unique threat models often need this level of control, and no article should pretend otherwise.
The Real Advantages Worth Acknowledging
✅ Business logic integration — Internal analysts understand org structure, VIP users, and project timelines. They can build non-standard detections, like correlating project management systems with access anomalies to catch insider threat patterns that no external provider would know to look for. GR, a former CISO of Micron and Darktrace, described exactly this scenario in our podcast: a team member’s weekend access triggered anomaly alerts, but only internal context (project timelines) explained it was legitimate.
✅ Custom SIEM ownership — All correlation rules, automation logic, and business-specific detections stay in-house even when MDR vendors change. As GR explained, “when I switch to another vendor, I get to start all over on that tuning process,” losing months or years of accumulated detection intelligence. Owning your SIEM means your institutional knowledge never walks out the door with a vendor contract.
✅ Regulatory data residency — Certain industries require logs and investigation data to remain on-premises or in specific jurisdictions. Healthcare organizations subject to HIPAA, financial services under GLBA, and defense contractors with ITAR requirements may have no alternative to controlling exactly where their security telemetry lives.
✅ Compliance control — Direct oversight of evidence collection, audit trails, and regulatory reporting gives in-house teams the ability to satisfy auditors without depending on a third party’s documentation cadence or format.
How UnderDefense Preserves These Advantages Without the In-House Cost
UnderDefense’s vendor-agnostic architecture was designed to preserve every advantage listed above. Customers own their SIEM, retain all detection logic, and keep data in their own data lake, while UnderDefense MAXI adds the AI correlation and concierge response layer on top. Our analysts log into your system. We don’t ask you to ship data to our proprietary platform.
What the Practitioners Say
GR put it best during our podcast conversation, and this is the exact perspective I look for in a mature security leader:
“I look for an MDR partner that will access the data where it lives. I want to control where that data lives. Some [MDR providers] will refuse that… that’s just not what I’m looking for.”
— GR, Former CISO of Micron/Darktrace
UnderDefense does exactly this. We meet your data where it lives, operate within your existing SIEM environment, and ensure that every detection rule, every automation workflow, and every piece of business logic remains yours, even if you decide to move on from us someday. That’s what vendor-agnostic actually means in practice, not just in a marketing slide.
Q4: Where Does an AI SOC Decisively Win on Scale, Speed, and 24/7 Coverage?
⚠️ The Scaling Problem That Breaks Every In-House SOC
The cybersecurity workforce gap has surged to 4.8 million unfilled positions globally, a 19% year-on-year increase according to the 2024 ISC2 Cybersecurity Workforce Study. Tier 1 analysts burn out in 18 months on average. A human SOC analyst processes 1,500+ alerts per day; half are false positives, but one hides a ransomware payload. In-house SOCs cannot scale detection capacity without proportional headcount growth, and traditional MSSPs add headcount without adding intelligence.
This is the fundamental math problem: threats scale exponentially with AI-assisted automation, but human analyst capacity scales linearly with budget. Something has to give.
What AI SOC Automates vs. What Still Needs Humans
This distinction matters. AI excels at:
- Tier 1 triage — automated enrichment, deduplication, and severity scoring at machine speed
- Cross-tool correlation — connecting alerts across SIEM, EDR, identity, cloud, and SaaS into a unified investigation context
- False positive filtering — 99% noise reduction through behavioral baselining and custom detection tuning
- 24/7/365 monitoring — without shift-pattern fragility, weekend coverage gaps, or holiday blind spots
Humans remain essential for:
- Complex incident response requiring judgment and organizational context
- Strategic threat hunting based on business intelligence
- Policy decisions and risk acceptance calls
- Digital forensics and evidence preservation
- The “is this person actually who they say they are?” verification that no algorithm can reliably answer alone
This is not replacement. It is augmentation. As I’ve said many times: automation scales routine work; humans handle edge cases.
❌ Why Monitoring-Only MSSPs Can’t Solve the Scaling Problem
Traditional MSSPs provide alerts without investigation, checkbox coverage based on rigid playbooks. MDR providers like Arctic Wolf or ReliaQuest operate as opaque alert factories: they show what was detected but not why it matters or what to do next. Neither solves the fundamental scaling problem because they still require your team to be the investigation layer.
✅ UnderDefense’s Specific Wins on Scale and Speed
- 24/7/365 coverage without shift-pattern fragility, consistent quality at 2 AM Tuesday and 3 PM Friday
- UnderDefense MAXI processes 6TB+ of security telemetry daily across 65K+ endpoints
- 2-minute alert-to-triage with enrichment and context automation
- 0.5-hour MTTR for critical incidents
- 15-minute escalation SLA for confirmed threats
- 99% false positive reduction through custom detection tuning + direct user verification via ChatOps
- 96% MITRE ATT&CK coverage
- Zero ransomware cases across all MDR clients in 6 years
While traditional MDR tells you “suspicious login detected, please investigate,” UnderDefense tells you who logged in, confirms with the user directly, and contains the threat before your team wakes up, with documented response times 2 days faster than CrowdStrike OverWatch.
What Real Users Say
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., CIO, Enterprise UnderDefense G2 – Verified Review
“The biggest problem they solved was our 24/7 coverage gap. We needed round-the-clock monitoring for compliance reasons, but building our own SOC wasn’t realistic with our budget and the current hiring market. UnderDefense fills that gap without us having to hire a full team.”
— Verified User, Marketing and Advertising UnderDefense G2 – Verified Review
“Over the past few years, we’ve undergone several external penetration tests, and during these assessments, Red Canary was not able to identify the malicious activity while the tests were ongoing.”
— Verified User, Insurance, Enterprise Red Canary – G2 Verified Review
That last review illustrates the gap between monitoring and actual detection effectiveness. An AI SOC with human allies doesn’t just watch. It hunts, verifies, and contains.
Q5: How Do Three Organization Profiles Compare on 3-Year TCO: Startup, Mid-Market, and Enterprise?
Most articles about SOC costs give you a range, “$200K to $2M,” and leave you to guess where you fall. You cannot walk into a budget meeting with a range that wide and expect anyone to approve the spend. So here is what no competing article provides: three real-world organization profiles, modeled across three SOC operating models, fully in-house, legacy MSSP, and AI SOC + MDR, with 3-year projections you can actually benchmark against.
The Three Profiles
- Profile A, 50-Person SaaS Startup: 200 endpoints, $5M revenue, zero dedicated security staff, SOC 2 required to close enterprise deals.
- Profile B, 500-Person Mid-Market Company: 1,500 endpoints, $75M revenue, 2-person security team, hybrid model candidate.
- Profile C, 2,000-Person Enterprise: 5,000 endpoints, $500M revenue, 8-person security team, regulated industry (healthcare or financial services).
Each profile faces the same fundamental question: build it, borrow it, or buy the AI-augmented version. The math is wildly different depending on where you sit.
📊 3-Year TCO Projection Table
| Dimension | Profile A (200 EP) | Profile B (1,500 EP) | Profile C (5,000 EP) |
|---|---|---|---|
| In-House SOC | ~$4.8M | ~$7.2M | ~$10.5M |
| Legacy MSSP | ~$450K | ~$1.8M | ~$3.6M |
| AI SOC + MDR | ~$250K | ~$650K | ~$1.2M (hybrid) |
| Staffing (In-House) | 5 FTEs minimum for 24/7, impractical at this size | 8–12 FTEs with 20–30% annual turnover | 15–20 FTEs, recruiting in Tier 1 markets |
| Tooling (In-House) | SIEM + EDR + cloud: $150K–$300K/yr | Enterprise SIEM alone: $200K–$500K/yr | Multi-tool stack: $500K–$1M/yr |
| Compliance Overhead | Separate SOC 2 tooling ($20K–$50K/yr) | Separate platform ($30K–$100K/yr) | Dedicated GRC team + tooling |
⚠️ The Hidden Multiplier: Turnover
The cybersecurity talent shortage, 3.4 million unfilled positions globally, means every analyst you lose takes 3–6 months to replace. During that gap, you run without 24/7 coverage, or your remaining team burns out covering extra shifts. That 15–25% annual turnover rate is not a line item most CFOs model, but it compounds fast: one departure in a five-person SOC cuts your coverage by 20% overnight.
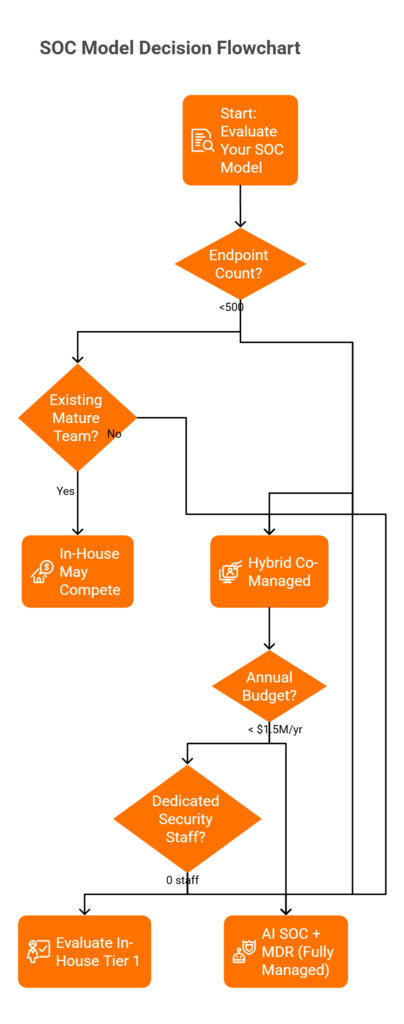
🔍 Decision Flowchart: Which SOC Model Fits?
- Under 500 endpoints? Skip in-house entirely. 500–2,000? Hybrid is your sweet spot. Over 5,000? In-house may compete if you already have a mature team in place.
- No dedicated security team? Fully managed AI SOC + MDR. Under 5 people? Hybrid co-managed. 8+ people? Evaluate whether in-house Tier 1 justifies the overhead.
- Regulated industry with data residency? Ensure the provider can operate within your data boundaries. On-prem SIEM plus external MDR is often ideal.
- Budget below $1.5M/year? In-house is off the table. Full stop.
✅ The Break-Even Reality
For organizations under 1,000 endpoints, in-house SOC costs 6–12x more than AI SOC + MDR, with equivalent or lower detection quality because small teams cannot maintain 24/7 vigilance, deep threat intelligence, and continuous detection engineering simultaneously. The break-even point where in-house starts to compete on cost-per-endpoint is approximately 5,000+ endpoints with an existing mature security team. Even then, only if the organization has solved the turnover problem, which most have not.
How UnderDefense Simplifies This
UnderDefense’s SOC Cost Calculator models these exact scenarios with your specific inputs. For Profile A startups, Under Defence MAXI + MDR delivers full 24/7 SOC plus compliance automation at approximately $7K/month. For Profile B mid-market, the hybrid co-managed model starts at roughly $18K/month. Published pricing at $11–$15/endpoint/month eliminates the guesswork, and compliance kits for SOC 2, ISO 27001, and HIPAA are included, not sold separately.
Q6: What About the Hybrid Model and the MSSP Repatriation Trend?
The hybrid model, outsourcing Tier 1 triage while keeping Tier 2/3 investigation and strategy in-house, is the most cost-effective approach for organizations with $10M+ revenue and existing security staff. But a second, equally important trend is emerging underneath: organizations that previously outsourced everything to an MSSP are pulling SOC operations back in-house, using AI SOC platforms to replace the MSSP while keeping a lean internal team for business context and strategic decision-making.
💰 Why the Hybrid Model Works
Having an external partner handle Tier 1 while your internal analysts own Tier 2/3 reduces blended labor spend by 30–40% versus fully in-house staffing. Tier 1 is commoditized work with high turnover. Partners manage that overhead far better than most internal HR teams. As one veteran CISO shared during an UnderDefense-hosted session: “If I can have a partner take on the level one work… that work tends to be very commoditized, very documented. People are frequently moving on in their career path, so it might make sense for me to ask a vendor to manage that turnover.”
🔍 The Knowledge Feedback Loop
When Tier 1 escalates to your internal Tier 2, those analysts bring business context. They know whether a flagged PowerShell script was an admin running a scheduled task or something genuinely suspicious. Over time, this feedback loop helps Tier 1 deflect more false positives, which frees your Tier 2 team for proactive threat hunting and security architecture work instead of chasing routine escalations all day.
⏰ The MSSP Repatriation Trend
Organizations frustrated with monitoring-only MSSPs, the kind that send “please investigate” tickets without enrichment or context, are using AI SOC platforms to replace the MSSP entirely. The AI handles what the MSSP did (24/7 monitoring) plus what the MSSP never did: enrichment, cross-tool correlation, automated triage, and direct user verification. This lets a lean 2–3 person internal team maintain strategic control without rebuilding a 12-person SOC from scratch.
⚠️ Critical Risk: SIEM Ownership
If your MDR partner owns the SIEM, switching vendors means losing all your business logic: correlation rules, custom detections, and automation playbooks built over months or years. A seasoned CISO put it plainly: “When I switch to another vendor, I get to start all over on that tuning process… I want to control where that data lives.” Always maintain SIEM ownership separately from the MDR relationship. This is not a theoretical concern. It is the number one lock-in trap in managed security.
How UnderDefense Supports Both Models
UnderDefense is built for both paths. For hybrid teams, our analysts log directly into your SIEM, preserving every custom detection rule, correlation, and automation you have built. Nothing leaves with us if you part ways. For organizations repatriating from legacy MSSPs, the full AI SOC + MDR model through Under Defence MAXI delivers the AI-powered detection layer, 24/7 analyst coverage, and ChatOps-driven user verification, without requiring you to rebuild a large team to replace what the MSSP used to provide.
UnderDefense detected threats 2 days faster than CrowdStrike OverWatch in documented case studies, because AI-driven detection without human context still leaves gaps that only analysts communicating directly with affected users can close.
Q7: How Does UnderDefense Compare to Arctic Wolf, CrowdStrike, and ReliaQuest?
Security leaders evaluating SOC options typically shortlist UnderDefense alongside Arctic Wolf, CrowdStrike Falcon Complete, and ReliaQuest. Each solves part of the problem, but through fundamentally different architectures that determine long-term cost, flexibility, response capability, and whether you retain ownership of your security data.
Arctic Wolf: Strong Brand, Proprietary Lock-In
Arctic Wolf has solid brand recognition and a dedicated Concierge Security Team. The limitation is architectural: you must replace your existing SIEM with their proprietary platform. Years of detection tuning in Splunk or Elastic disappear on migration. Pricing starts at $44,000/year for up to 100 users on AWS Marketplace and scales to $96K–$180K+ annually for mid-market organizations, none of it published on their website.
“We received little value from Arctic Wolf. The product offered little visibility… Anything you want to look at or changes you need to make must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
CrowdStrike Falcon Complete: Best-in-Class EDR, Narrow Ecosystem
Falcon Complete delivers arguably the best endpoint detection, within the Falcon ecosystem. Visibility into non-Falcon environments is limited. Standard EDR starts at $59.99/device/year (Falcon Go) through $184.99/device/year (Enterprise), while Falcon Complete MDR starts around $125/endpoint/year with custom quotes. OverWatch response times were documented at 2 days slower than UnderDefense in head-to-head comparison cases, because endpoint-native detection without organizational context leaves verification gaps.
ReliaQuest: Broad Integration, Stops at Escalation
ReliaQuest has invested heavily in AI-driven automation and broad integration. The limitation flagged repeatedly by users: responses that “lacked actionable insights,” poor reporting transparency, and tickets returning to customers without clear answers. No direct user verification via ChatOps, and TCO favors large enterprises only.
“Arctic Wolf provides solid detection and response capabilities, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology, Services Arctic Wolf – Gartner Review
📊 Side-by-Side Comparison
| Criterion | Arctic Wolf | CrowdStrike Complete | ReliaQuest | UnderDefense |
|---|---|---|---|---|
| Integration | Proprietary SIEM required | Falcon ecosystem native | Broad, AI-reliant | 250+ existing tools |
| Pricing | $44K–$180K+/yr (contact sales) | ~$125/ep/yr (custom) | $172K+ (contact sales) | $11–$15/ep/mo (published) |
| User Verification | ❌ Escalates to customer | ❌ Endpoint-only context | ❌ AI-automated | ✅ ChatOps (Slack/Teams) |
| Response Time | Not published | 2 days slower (documented) | Under 5 min (AI) | 2-minute alert-to-triage, 15-minute escalation for critical incidents |
| Compliance | Separate product | Separate product | Separate product | ✅ Included free |
| Onboarding | SIEM migration required | Falcon-native | Extended integration | 30-day turnkey |
| SIEM Ownership | ❌ Vendor-owned | N/A (EDR-focused) | ❌ Platform-dependent | ✅ Customer-owned |
Who Should Choose What
✅ Arctic Wolf, starting from zero with no existing stack, prefer single-vendor simplicity, comfortable with proprietary lock-in.
✅ CrowdStrike Falcon Complete, fully committed to the Falcon ecosystem, primary concern is endpoint-level depth.
✅ UnderDefense, protecting existing investments, need transparent pricing, want analysts who verify alerts directly with users rather than escalating back to your team.
“UnderDefense impressed us with their ability to tailor their services to our unique needs… Their proactive approach to threat detection gave us confidence in their ability to protect our business.”
— Serhii Bozhok, CIO of Security, ARX Insurance UnderDefense – Clutch Review
Q8: How Do You Build the Business Case for Your CFO: AI SOC vs. In-House SOC?
Security is not a revenue function, which makes proving ROI to a CFO one of the hardest conversations in cybersecurity. The whole topic of budget, as one experienced CISO shared during a session we hosted, “gets really specific to organizations, CFOs, and CISOs.” There is no universal formula. But there are frameworks that consistently work, and the best ones connect security spend directly to business outcomes your CFO already cares about.
Step 1: Map Current Spend Against NIST CSF Risk Families
List every security vendor, tool, and headcount cost. Then visualize that spend across the NIST Cybersecurity Framework families: Identify, Protect, Detect, Respond, and Recover. As one CISO described: “I might find that I have zero money being spent in a proactive capacity. Is that right? Maybe. But that’s the conversation to be had.” This single one-page visual becomes the opening slide of your board presentation. CFOs respond to gap visualization instantly, showing 80% of spend on “Protect” while “Detect” and “Respond” are nearly zero makes the case without technical jargon.
Step 2: Calculate True In-House SOC TCO
Most budget proposals undercount in-house costs. The real math:
- Staffing: 5 FTEs minimum for 24/7 shift rotation × $120K–$180K fully loaded = $600K–$900K/year just for bodies.
- Tooling: Enterprise SIEM ($150K–$500K/yr) + EDR + cloud monitoring + SOAR platform.
- Turnover: At 20–30% annual turnover, each departure costs 3–6 months of recruiting plus onboarding ramp.
- Opportunity cost: Every hour senior analysts spend on Tier 1 triage is an hour not spent on proactive threat hunting.
Total realistic 3-year in-house SOC cost for a mid-market company: $2.5M–$4M+.
Step 3: Model the AI SOC Alternative
At $11–$15/endpoint/month, a 500-endpoint organization pays $66K–$90K/year, or $198K–$270K over three years. That includes 24/7 monitoring, detection engineering, incident response, and compliance automation. Predictable OPEX, not variable CAPEX.
Step 4: Quantify the ROI
💰 UnderDefense documents 830% ROI over 3 years for MDR clients. But the strongest business-case signal is a revenue connection. As one CISO put it: “If I can find a clear connection between a security program and a customer or multiple customers, that’s where I want to be because the signal is really clear.” SOC 2 or ISO 27001 certification directly unblocks enterprise sales. For a 2-year-old startup, outsourced AI SOC + MDR is the fastest path to that certification and the customer trust that follows.
📊 CFO-Ready Comparison
| Dimension | In-House SOC | AI SOC + MDR |
|---|---|---|
| Cost Model | Variable CAPEX + OPEX | Fixed monthly OPEX |
| Time to Operational | 6–18 months | 30-day deployment |
| Turnover Risk | 20–30% annual, unpredictable | Provider-managed, zero client impact |
| Compliance | Separate tools ($15K–$50K/yr) | ✅ Included, forever-free kits |
| Budget Predictability | Low, surprises quarterly | High, published per-endpoint pricing |
| 24/7 Coverage | Requires 5+ FTEs minimum | Included by default |
How UnderDefense Simplifies the CFO Conversation
UnderDefense’s SOC Cost Calculator generates board-ready comparisons with your specific inputs in minutes. Published pricing at $11–$15/endpoint/month means the CFO sees a predictable line item, not a “we’ll scope it later” estimate. Forever-free compliance kits for SOC 2, ISO 27001, and HIPAA replace standalone tools like Vanta or Drata, collapsing two budget lines into one. And MAXI Compliance automates evidence collection so your team stops spending 40 hours per audit cycle pulling screenshots manually.
Q9: What Decision Framework and Readiness Checklist Should You Use?
Choosing between an AI SOC, in-house SOC, or traditional MSSP is a 3–5 year operational commitment affecting security posture, team structure, compliance readiness, and budget. The wrong choice means burning $2M+/year on a team you cannot retain, or paying for coverage that escalates alerts without context.
⚠️ The Wrong Way to Decide
Most security leaders choose based on brand recognition (“CrowdStrike is the biggest”) or integration count (“They support our SIEM”). This ignores the critical question: Can they respond to threats with context, or just escalate alerts back to you?
The Right Evaluation Framework
Score each provider 0–2 on these seven criteria. Providers scoring 10+ represent genuine operational partnership. Below 7 means you are buying an alert feed, not managed detection and response.
- Budget Reality, can you sustain $1.6M–$4M/year, or do you need predictable OPEX?
- Staffing Capacity, can you recruit and retain 8–12 SOC analysts at 20–30% annual turnover?
- 24/7 Coverage, truly 24/7/365, or business-hours with on-call gaps?
- Response Capability, contain threats within 30 minutes, or just detect and escalate?
- Tool Integration, works with existing stack, or forces proprietary replacement?
- Compliance Requirements, auto-generates audit evidence, or requires separate tooling?
- Growth Trajectory, scales with 2x–5x telemetry growth without proportional cost?
📊 Where Each Model Wins
| Criterion | In-House SOC | Traditional MSSP | AI SOC + Human Ally |
|---|---|---|---|
| Cost | ❌ Highest ($1.6M–$4M/yr) | ⚠️ Mid-range, opaque | ✅ Lowest, predictable |
| 24/7 Coverage | ⚠️ Requires 5+ FTEs | ✅ Included | ✅ Included |
| Response Speed | ⚠️ Team-dependent | ❌ Escalation only | ✅ 2-minute alert-to-triage, 15-minute escalation for critical incidents |
| Scalability | ❌ Linear cost growth | ⚠️ Contract-dependent | ✅ Elastic |
| Compliance | ❌ Separate tools | ❌ Separate tools | ✅ Included |
| Time-to-Value | ❌ 6–18 months | ⚠️ 30–90 days | ✅ 30 days |
| Data Sovereignty | ✅ Full ownership | ❌ Vendor-dependent | ✅ Customer-owned |
✅ Security Operations Readiness Checklist
- ☐ True 24/7/365 monitoring, not just during business hours?
- ☐ User verification capability via ChatOps (Slack, Teams, email)?
- ☐ Can contain a critical threat within 30 minutes of detection?
- ☐ Unified alert correlation across SIEM, EDR, cloud, and identity?
- ☐ Security monitoring auto-generates compliance evidence?
- ☐ Team focused on strategy, not consumed by daily alert triage?
- ☐ Direct Tier 3–4 analyst access, not just ticket-based support?
Score: 6–7 = mature, focus on optimization. 3–5 = critical gaps, hybrid or AI SOC needed. 0–2 = breach exposure is high, AI SOC urgently recommended.
Where UnderDefense Stands
UnderDefense scores 14/14 on this framework, purpose-built to turn every unchecked box into a check mark. Most teams go from 2–3 checks to 7/7 within 30 days of onboarding.
“UnderDefense has changed our approach to cybersecurity. At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it.”
— Yaroslava K., IT Project Manager Under Defence G2 – Verified Review
“With UnderDefense MAXI, we’ve reduced security breaches. Their adherence to SLAs gives me confidence… it lets me focus on strategy, knowing the day-to-day security is managed effectively.”
— Oleg K., Director Information Security Under Defence G2 – Verified Review
Q10: How Fast Can You Deploy an AI SOC vs. Building an In-House SOC?
Building an in-house SOC takes 6–18 months before you get meaningful security coverage. Recruiting 8–12 analysts averages 2–4 months per hire in most markets. SIEM deployment, detection rule development, and runbook creation add another 3–6 months. Then each analyst needs an additional 3–6 months to ramp to full productivity. An AI SOC + MDR provider can begin active monitoring within days of integration, with full operational maturity achieved in 30 days.
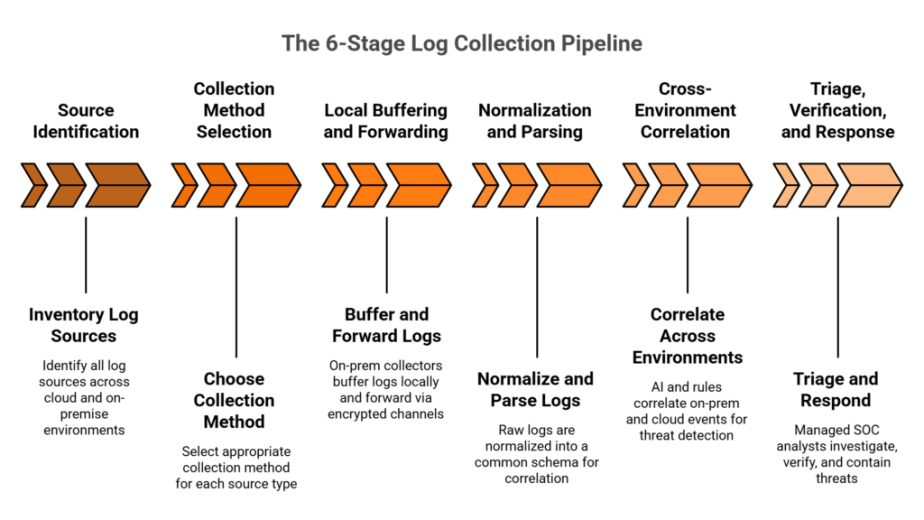
⏰ UnderDefense’s 30-Day Turnkey Deployment
- Week 1: Integration with your existing stack (SIEM, EDR, cloud, identity) + security hardening + toolset audit. During onboarding, we fine-tune configurations most teams have never optimized, and often discover misconfigurations that were creating blind spots.
- Week 2: Custom detection tuning based on organizational context + Active Directory/Azure/O365 fine-tuning. Not generic rules, but detections built around how your business actually operates, informed by your industry, your user behavior patterns, and your compliance requirements.
- Week 3: ChatOps configuration and user verification workflows. Analysts learn your org chart, your VIPs, and your technical users so verification happens in seconds, not hours of back-and-forth email chains.
- Week 4: Full 24/7 operational coverage with ransomware simulation testing (Caldera/Infection Monkey) to validate 100% use-case coverage. You see the system work before you trust it with your production environment.
📊 Deployment Timeline Comparison
| Dimension | In-House SOC | Traditional MSSP | AI SOC + MDR |
|---|---|---|---|
| Time to First Coverage | 6–18 months | 30–90 days | Days (Week 1) |
| Full Operational Maturity | 12–24 months | 90–180 days | 30 days |
| Recruitment Cost | $40K–$120K per analyst | N/A | N/A |
| Analyst Ramp Time | 3–6 months per person | N/A | Pre-trained team |
| Custom Detection Tuning | DIY, takes months | Limited or rigid | Included (Week 2) |
| Ransomware Simulation | Rarely done | Not included | ✅ Included (Week 4) |
💸 The Business Cost of Delay
Every month without 24/7 coverage is a month of breach exposure. Average dwell time increases 3x when analysts are overwhelmed or simply absent. For a startup needing SOC 2 to close an enterprise customer, 12 months of in-house SOC buildout versus 30-day AI SOC deployment is not an abstract timeline difference. It is real revenue sitting on the table waiting to be unlocked.
Consider this scenario: if a $5M-revenue SaaS company is blocked from closing a $500K enterprise deal until SOC 2 certification is complete, the 12-month delay costs far more than the security investment itself. The 30-day deployment path gets you to compliance, and to customer trust, while competitors are still interviewing their first SOC analyst.
How UnderDefense Simplifies This
UnderDefense invests a full 30 days in high-quality onboarding, building customized detections that deliver only confirmed and validated offenses. We cut 99% of alert noise from day one. Your team reviews confirmed incidents, not thousands of maybes. And because we test with real ransomware simulation tools before going live, you get observable, reproducible proof that the system works, no “trust me, it works” black boxes.
Q11: Which AI SOC Provider Should You Shortlist?
The leading AI SOC and SOC-as-a-Service providers for mid-market companies in 2026 include UnderDefense, Arctic Wolf, CrowdStrike Falcon Complete, Expel, Red Canary, and Sophos MDR, each with distinct architectures, pricing models, and response capabilities that serve fundamentally different buyer needs and operational priorities.
🔍 What Separates Top AI SOC Providers
The MDR market has evolved well beyond basic 24/7 monitoring. The differentiators that actually matter when shortlisting providers for evaluation:
- Vendor-agnostic integration vs. proprietary stack lock-in, does the provider work with your existing SIEM, EDR, and cloud tools, or force replacement? UnderDefense supports 250+ tools; Arctic Wolf requires its own proprietary SIEM.
- Human analyst access, direct communication with Tier 3–4 analysts via Slack or Teams, or ticket-based escalation queues that add hours to response time?
- Published response-time SLAs, documented 2-minute alert-to-triage and 15-minute escalation for critical incidents backed by case study evidence, or vague “rapid response” marketing claims with no published benchmarks?
- Pricing transparency, published per-endpoint rates you can budget around ($11–$15/endpoint/month), or opaque “contact sales” quotes that surprise you at contract renewal?
- Compliance support included, audit evidence generation bundled with MDR, or sold as a separate $15K–$50K/year add-on through standalone tools like Vanta or Drata?
Which Provider Fits Which Scenario
Each provider excels in different situations. Arctic Wolf works well for organizations starting from zero who prefer single-vendor simplicity, but requires proprietary SIEM replacement and locks you into their ecosystem. CrowdStrike Falcon Complete is strong for teams fully committed to the Falcon ecosystem with primarily endpoint-focused concerns. Expel offers solid software-driven MDR with transparent operations, though it lacks compliance bundling, and users report inconsistent organizational knowledge retention. Red Canary provides strong EDR-focused automation but has been flagged for over-reliance on CrowdStrike data sources and detection gaps during penetration tests. Sophos MDR delivers affordable AI-native coverage with broad integrations, though support responsiveness has been inconsistent.
The right choice depends on your current security investments, compliance requirements, and whether you need detection-only or full containment plus response. For a complete feature-by-feature breakdown with pricing, response times, and integration capabilities for all twelve leading providers, see the full evaluation below.
⭐ Full Provider Comparison
This analysis is based on documented response times, G2 Spring 2025 rankings, published pricing data, and operational outcomes across 500+ MDR deployments.
1. How much does an in-house SOC cost compared to an AI SOC over three years?
We model this across three real-world organization profiles because a single number never tells the full story.
-
For a 50-person SaaS startup with 200 endpoints, an in-house SOC runs approximately $4.8M over three years. An AI SOC + MDR model costs roughly $250K over the same period.
-
For a 500-person mid-market company with 1,500 endpoints, in-house reaches approximately $7.2M versus $650K for AI SOC + MDR.
-
For a 2,000-person enterprise with 5,000 endpoints, in-house hits $10.5M versus $1.2M for a hybrid AI SOC model.
These figures include staffing at 24/7 shift coverage (minimum 5 FTEs), enterprise SIEM licensing ($150K–$500K/yr), EDR, cloud monitoring, and the hidden multiplier most CFOs miss: 20–30% annual analyst turnover that costs 3–6 months per replacement cycle. We built our SOC Cost Calculator to model these exact scenarios with your specific inputs so you walk into budget meetings with defensible numbers, not ranges.
2. What is the hybrid SOC model, and why is it the most cost-effective approach for mid-market companies?
The hybrid SOC model means outsourcing Tier 1 alert triage to an external partner while keeping Tier 2/3 investigation and strategic security work in-house. We see this as the optimal path for organizations with $10M+ revenue and at least a small existing security team.
Here is why the economics work: Tier 1 is commoditized, high-turnover work. Partners manage that overhead far more efficiently than internal HR teams, reducing blended labor spend by 30–40% versus fully in-house staffing. Your internal Tier 2 analysts bring irreplaceable business context. They know whether a flagged PowerShell script is an admin task or something genuinely suspicious. Over time, this feedback loop trains Tier 1 to deflect more false positives, freeing your senior analysts for proactive threat hunting and architecture work.
The critical requirement is SIEM ownership. If your MDR partner controls the SIEM, switching vendors means losing all your detection logic.
3. How do we build a business case for our CFO to approve an AI SOC instead of an in-house SOC?
We recommend a four-step framework that translates security spend into language your CFO already understands.
-
Step 1: Map current spend across NIST CSF risk families (Identify, Protect, Detect, Respond, Recover). A single one-page visual showing 80% of spend on “Protect” while “Detect” and “Respond” sit near zero makes the gap impossible to ignore.
-
Step 2: Calculate true in-house TCO including staffing (5+ FTEs × $120K–$180K), tooling ($150K–$500K/yr for SIEM alone), turnover costs, and opportunity cost of senior analysts stuck on Tier 1 triage.
-
Step 3: Model the AI SOC alternative. At $11–$15/endpoint/month, a 500-endpoint company pays $66K–$90K/year, including 24/7 monitoring, detection engineering, and compliance automation.
-
Step 4: Connect security to revenue. SOC 2 or ISO 27001 certification directly unblocks enterprise sales. Use our MDR pricing page to generate board-ready cost comparisons in minutes.
We document 830% ROI over three years for MDR clients.
4. How fast can an AI SOC be deployed compared to building an in-house SOC from scratch?
An in-house SOC takes 6–18 months before delivering meaningful security coverage. Recruiting 8–12 analysts averages 2–4 months per hire. SIEM deployment, detection rule development, and runbook creation add 3–6 months. Each analyst then needs 3–6 months to ramp to full productivity.
We deploy operational AI SOC + MDR coverage in 30 days through a structured four-week process:
-
Week 1: Integration with your existing stack plus security hardening and toolset audit.
-
Week 2: Custom detection tuning based on how your business actually operates.
-
Week 3: ChatOps configuration and user verification workflows.
-
Week 4: Full 24/7 coverage validated through ransomware simulation testing.
Every month without coverage is a month of breach exposure. For a startup blocked from closing a $500K enterprise deal until SOC 2 is complete, the 12-month in-house delay costs far more than the security investment. Learn more about our Under Defence MAXI platform and the 30-day onboarding process.
5. How does UnderDefense compare to Arctic Wolf, CrowdStrike Falcon Complete, and ReliaQuest?
Each provider solves part of the SOC problem through fundamentally different architectures.
-
Arctic Wolf requires replacing your existing SIEM with their proprietary platform. Years of Splunk or Elastic detection tuning disappear on migration. Pricing starts at $44K/yr and scales to $96K–$180K+ annually, none published.
-
CrowdStrike Falcon Complete delivers best-in-class endpoint detection within the Falcon ecosystem. Visibility outside Falcon is limited. OverWatch response was documented 2 days slower than UnderDefense in head-to-head cases.
-
ReliaQuest offers broad AI-driven integration but users report responses “lacking actionable insights” and tickets returning without answers.
UnderDefense supports 250+ existing tool integrations, publishes pricing at $11–$15/endpoint/month, includes compliance kits for SOC 2, ISO 27001, and HIPAA at no extra charge, and delivers 2-minute alert-to-triage with 15-minute escalation for critical incidents. We log into your SIEM so your detection logic stays with you.
6. What is the MSSP repatriation trend, and should we bring SOC operations back in-house?
MSSP repatriation is the growing pattern of organizations pulling security operations away from legacy MSSPs, the kind that send “please investigate” tickets without enrichment or context, and either rebuilding internally or replacing them with AI SOC platforms.
The shift happens because legacy MSSPs provide monitoring without response. They detect alerts but escalate them back to your team for investigation, which defeats the purpose of outsourcing.
We see two repatriation paths:
-
Full in-house rebuild: Requires hiring 8–12 analysts, deploying SIEM, building runbooks. Takes 12–18 months and costs $1.6M–$4M/year.
-
AI SOC replacement: The AI handles what the MSSP did (24/7 monitoring) plus what the MSSP never did: enrichment, cross-tool correlation, automated triage, and direct user verification. A lean 2–3 person internal team maintains strategic control.
For a deeper comparison of managed vs. in-house approaches, we break down the full trade-off in our outsourced SOC vs. in-house SOC guide.
7. What decision framework should we use to choose between an AI SOC, in-house SOC, and traditional MSSP?
We recommend scoring each option 0–2 across seven criteria. Providers scoring 10+ represent genuine operational partnership. Below 7 means you are buying an alert feed.
-
Budget Reality: Can you sustain $1.6M–$4M/year, or do you need predictable OPEX?
-
Staffing Capacity: Can you recruit and retain 8–12 SOC analysts at 20–30% annual turnover?
-
24/7 Coverage: Truly 24/7/365, or business-hours with on-call gaps?
-
Response Capability: Contain threats within 30 minutes, or just detect and escalate?
-
Tool Integration: Works with your existing stack, or forces proprietary replacement?
-
Compliance Requirements: Auto-generates audit evidence, or requires separate tooling?
-
Growth Trajectory: Scales with 2x–5x telemetry growth without proportional cost increase?
For organizations under 500 endpoints, skip in-house entirely. For 500–2,000 endpoints, hybrid is the sweet spot. Budget below $1.5M/year means in-house is off the table. Download our SOC Provider Evaluation Checklist to score each vendor systematically.
8. Does AI SOC + MDR include compliance support, or is that an additional cost?
With most providers, compliance is a separate product. Arctic Wolf, CrowdStrike, and ReliaQuest all require standalone compliance tooling, typically $15K–$50K/year through platforms like Vanta or Drata on top of the MDR subscription.
We take a fundamentally different approach. UnderDefense bundles forever-free compliance kits for SOC 2, ISO 27001, and HIPAA directly into the MDR engagement. Our MAXI Compliance module automates evidence collection so your team stops spending 40 hours per audit cycle pulling screenshots manually.
For a 2-year-old startup, this is the fastest path to SOC 2 certification and the enterprise customer trust that follows. For regulated mid-market companies in healthcare or financial services, bundled compliance collapses two budget lines into one and eliminates the procurement overhead of evaluating, purchasing, and integrating separate GRC platforms.
The compliance savings alone often cover 20–30% of the total MDR cost, making the effective per-endpoint price even lower than the published $11–$15/month.
The post AI SOC vs. In-House SOC: 3-Year TCO Data Most Vendors Won’t Publish appeared first on UnderDefense.