Q1. What Is an AI SOC for SaaS, and Why Does It Exist?
An AI SOC for SaaS is a security operations center purpose-built to detect, investigate, and respond to threats that occur at the SaaS application layer: OAuth token abuse, API exploitation, shadow identity proliferation, CI/CD pipeline compromise, and SaaS supply chain attacks. Unlike traditional SOCs focused on endpoints and network traffic, an AI SOC for SaaS ingests SaaS-native telemetry and uses AI-driven correlation to defend the layer where modern SaaS companies actually get breached.
Here’s the reality most security teams haven’t fully internalized. Roughly 80% of business-critical workflows now run through third-party SaaS applications. The Verizon 2025 DBIR confirmed that third-party involvement in breaches doubled from 15% to 30% year-over-year, and a significant share of that growth traces back to SaaS-to-SaaS trust relationships going wrong. Meanwhile, CyberArk’s research shows machine identities are expanding faster than human accounts, with organizations carrying 20–40% more non-human identities than they even track. The paradigm shift is clear: attackers no longer “break in” through perimeters. They “log in” through stolen tokens and over-permissioned APIs.
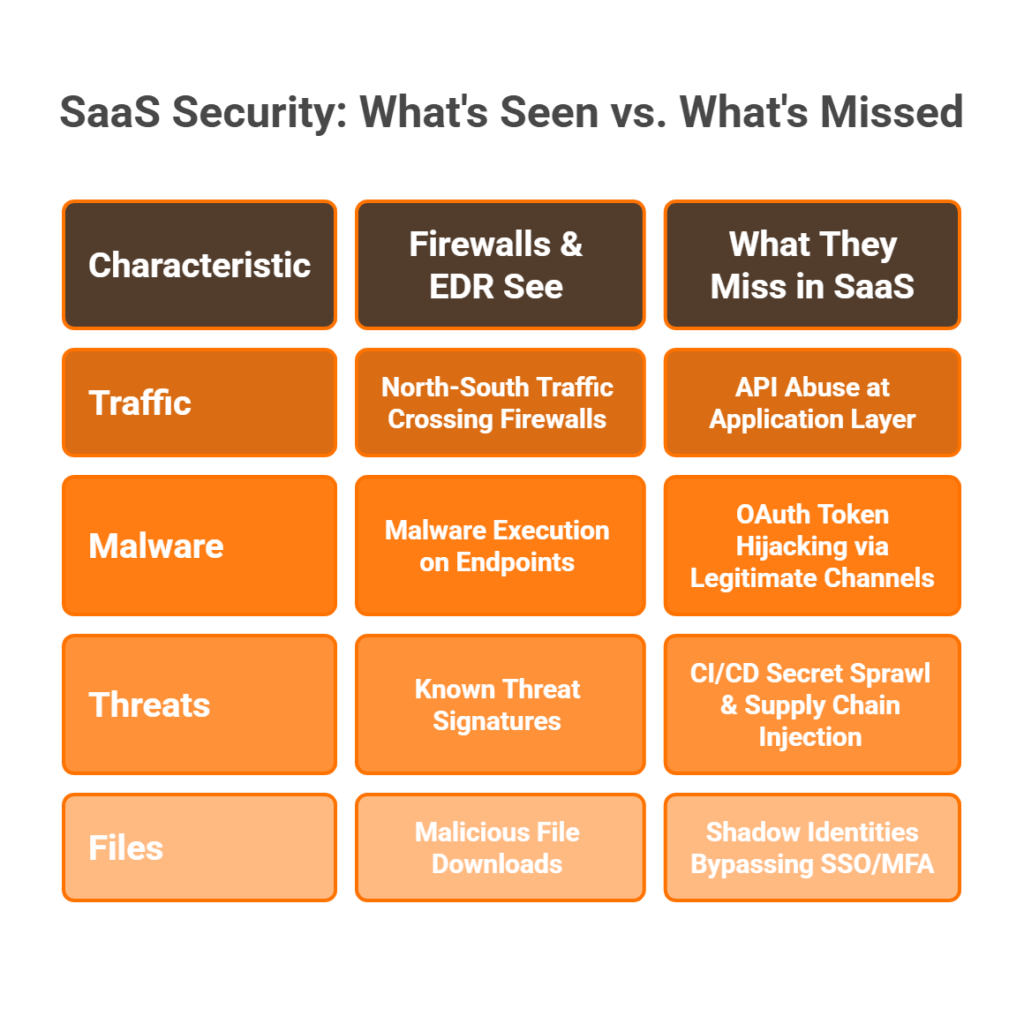
⚠️ Why Traditional Security Tools Are Architecturally Blind
Firewalls inspect packets at OSI layers 3–4. EDR monitors endpoint processes. Legacy SIEM correlates on-prem log events. Not a single one of these sees SaaS-layer activity: OAuth grant events, API call patterns, CI/CD deployment mutations, or shadow identity creation. Traditional MDR providers like Arctic Wolf, CrowdStrike, and ReliaQuest inherit these same architectural blind spots. They deliver alert volume scoped to endpoints and the network layer, not the SaaS application layer where SaaS companies actually get breached. ReliaQuest returns tickets without clear investigation context. Arctic Wolf pushes proprietary stack replacement with zero SaaS-native telemetry. These tools were designed for a world where the network was the perimeter, and that world simply doesn’t exist anymore for SaaS-native organizations.
🔑 Identity Is the New Perimeter
In a SaaS-first company, there is no network perimeter to defend. The security boundary is identity, both human and non-human. An AI SOC built for SaaS must reason across OAuth scopes, API behaviors, identity provider events, and CI/CD deployment logs simultaneously. This is exactly why the “AI SOC + Human Ally” model represents the new operational standard: a system that doesn’t just detect endpoint malware but understands the full causal chain, from compromised OAuth token to lateral SaaS movement to data exfiltration. If your SOC can’t trace that chain end-to-end, you have a blind SOC operating in a SaaS-first world.
✅ How UnderDefense Sees What Others Can’t
This is precisely why we built UnderDefense MAXI the way we did. Our platform integrates vendor-agnostically with 250+ tools, including SaaS-native telemetry sources such as OAuth logs, API audit trails, and identity provider events. AI-driven correlation works across identity, endpoint, cloud, and SaaS in a single context-aware detection layer. And here’s what changes the operational reality at 2 AM: our ChatOps-driven verification resolves SaaS behavioral alerts by asking users directly via Slack or Teams. “Did you authorize this OAuth app at 2:41 AM?” Unlike monitoring-only tools, we contain threats by revoking compromised tokens, isolating accounts, and blocking lateral movement while your team sleeps.
While traditional MDR providers still debate endpoint telemetry coverage, SaaS breaches have doubled year-over-year. We’ve detected threats 2 days faster than CrowdStrike OverWatch in documented case studies, because SaaS threats require SaaS-native visibility that endpoint-focused tools fundamentally cannot provide. The question is not whether your organization needs an AI SOC for SaaS, but how long you can afford to run without one.
Q2. What SaaS-Specific Threats Do Firewalls and EDR Completely Miss?
Traditional security tools were engineered for a perimeter-centric world. Firewalls, EDR agents, and legacy SIEM systems excel at what they were built for: network packet inspection, endpoint process monitoring, and on-prem log correlation. But SaaS-native attack vectors operate on a completely different plane. Below is a four-category taxonomy of SaaS-specific threats that fall entirely into this architectural visibility gap.
| Threat Vector | What It Is | Why Firewalls/EDR Miss It | Real-World Example |
|---|---|---|---|
| OAuth Token Abuse | Attackers steal or forge OAuth tokens for persistent, MFA-bypassing SaaS access | OAuth grant events don’t traverse the network or touch endpoints | Salesloft-Drift attack (2025): 700+ orgs compromised via OAuth token replay |
| API Exploitation | Over-permissioned keys, misconfigured endpoints, SaaS-to-SaaS integration abuse | API calls between SaaS platforms never hit a firewall or generate endpoint telemetry | Exposed Salesforce APIs leaking customer data through third-party integrations |
| Shadow Identities (NHIs) | Service accounts, API tokens, bot users, machine credentials proliferating unmonitored | EDR monitors endpoint processes; service accounts don’t run on endpoints | Enterprises carry 20–40% more NHIs than tracked |
| CI/CD Pipeline Compromise | Secrets leakage, deployment tampering, dependency poisoning in build pipelines | CI/CD events generate zero endpoint alerts; pipelines live entirely in cloud/SaaS | CircleCI (2023), Codecov (2021) |
🔓 OAuth Token Abuse: The Front Door Nobody’s Watching
OAuth tokens persist beyond password resets and bypass MFA entirely, by design. Once a user grants consent, the token provides ongoing access without re-authentication. Attackers exploit this by creating malicious OAuth apps disguised as legitimate integrations, or by compromising existing SaaS vendors in the supply chain. The Salesloft-Drift campaign hit over 700 organizations in 2025, including Cloudflare and Palo Alto Networks, by replaying valid OAuth tokens to authenticate directly into customer Salesforce environments. No password was stolen. No endpoint was compromised. Firewalls logged nothing.
⚙️ API Exploitation: The Silent Data Channel
SaaS companies expose APIs internally and externally, creating three specific risk categories. First, over-permissioned API keys grant admin-level access to SaaS data stores. Second, misconfigured API endpoints expose sensitive data without proper authentication. Third, SaaS-to-SaaS integration abuse allows a compromised third-party app to use its legitimate API access for silent data exfiltration. None of these actions generate firewall alerts or endpoint detections because API traffic between SaaS platforms is invisible to network-layer tools.
👻 Shadow Identities: Hiding Inside Your Approved Tools
Service accounts, API tokens, bot users, and machine credentials proliferate silently inside sanctioned SaaS tools. CyberArk’s research confirms enterprises carry 20–40% more non-human identities than they actively track. These identities often hold admin-level permissions, never rotate credentials, never trigger MFA, and never get offboarded. EDR monitors endpoint processes, but service accounts don’t run on endpoints. Legacy SIEM logs identity creation events but lacks the SaaS-native context to distinguish legitimate automation from attacker-created persistence.
🔧 CI/CD Pipeline Compromise: When the Product Becomes the Payload
A compromised pipeline means a compromised product. Secrets leaking into repositories, deployment configurations being tampered with, or dependencies getting poisoned: these happen entirely inside CI/CD environments that generate zero endpoint alerts. The CircleCI breach in 2023 exposed customer secrets and environment variables. The Codecov attack in 2021 injected malicious code into a bash uploader used by thousands of organizations. Neither triggered traditional SOC detection.
✅ UnderDefense MAXI ingests SaaS-native telemetry, including OAuth grant events, API audit logs, identity provider signals, and CI/CD deployment events, alongside traditional endpoint and network data. This SaaS-aware detection layer closes the visibility gaps that endpoint-focused MDR providers leave wide open, with 96% MITRE ATT&CK coverage extended to cloud and SaaS attack techniques.
Q3. How Do Attackers Exploit OAuth Tokens to Bypass MFA and Move Laterally Across SaaS?
A developer on your team clicks a consent prompt for what looks like a legitimate code review integration. Within minutes, an attacker-controlled OAuth app has read access to your GitHub repos, Slack messages, and Google Drive. No password was stolen. No MFA was triggered. No endpoint was compromised. Your EDR is silent. Your firewall logged nothing. The attacker is already inside your SaaS ecosystem, and they walked in through the front door.
This scenario is not hypothetical but an operational reality documented across 700+ organizations in 2025. The Salesloft-Drift OAuth supply chain campaign played out exactly this way. Attackers replayed valid OAuth tokens to authenticate directly into customer Salesforce environments, bypassing every layer of traditional perimeter security. Microsoft customers faced similar consent phishing campaigns: attackers created fake partner apps that looked trusted, tricked users into granting access, and then leveraged those tokens for persistent, silent data exfiltration.
⚠️ Why OAuth Tokens Are a Perfect Attack Vector
OAuth tokens are designed to persist; that’s their core function. They bypass MFA by design because the user already authenticated when granting consent. Tokens survive password resets. Refresh tokens let attackers continuously mint new access tokens, enabling long-term persistence. Three compounding problems make this especially dangerous:
- ⏰ Dwell time: OAuth-based attacks often exceed 200 days undetected because traditional tools have zero detection mechanism for token abuse
- 💥 Blast radius: One compromised token cascades access across every SaaS app the user authorized
- 🔗 Supply chain amplification: A single compromised vendor propagates access across every downstream customer simultaneously
EDR sees endpoints, not OAuth grant events. Firewalls see packets, not consent flows. Legacy SIEM may log identity events but lacks the SaaS-native context to tell a legitimate integration from an attacker-controlled app requesting mailbox full-access at 3 AM.
🛡️ How the Right AI SOC Handles This
The right AI SOC monitors OAuth grant events in real time, flags unusual scope requests, correlates token usage patterns across SaaS applications, and, critically, verifies with the affected user directly. At UnderDefense, we built MAXI to do exactly this: ingest OAuth telemetry, apply AI-driven behavioral analysis, and use ChatOps to verify before containing. “Did you authorize this app?” is asked directly via Slack or Teams. If the answer is no, we revoke tokens, block app access, and isolate accounts while your team sleeps.
✅ The Operational Difference
From silent OAuth compromise to contained threat in under 15 minutes: that’s the gap between a SaaS-aware AI SOC and endpoint-limited MDR. We maintain 100% ransomware prevention across 500+ MDR clients because we see the attack vectors that endpoint-only tools were never built to detect.
“We’ve tackled potential threats directly from our Slack channels, regardless of the hour. It’s like having a security command center right in our daily chat tool.”
— Alexander B., CEO UnderDefense G2 – Verified Review
“Their SOC team is responsive and knows their stuff. When they escalate something, they include the context we need to understand the issue quickly.”
— Verified User in Marketing and Advertising UnderDefense G2 – Verified Review
“Started out well but over the years the service has consistently not met expectations. Analysts provide little context, and when asked for more information in the investigation nothing is ever provided.”
— CISO, Manufacturing Arctic Wolf – Gartner Verified Review
Q4. Why Are Shadow Identities and SaaS Supply Chain Risks the Biggest Blind Spots in SaaS Security?
Most security teams understand shadow IT: unauthorized applications employees adopt without IT approval. Fewer understand shadow identities, and that distinction matters enormously. Shadow SaaS refers to unsanctioned apps. Shadow identities are non-human accounts, including service accounts, API tokens, bot users, machine credentials, and OAuth app identities, that proliferate inside your approved, sanctioned SaaS tools without security oversight. They’re far more dangerous than shadow SaaS because they exist inside your sanctioned environment, carry persistent privileged access, and remain completely invisible to identity governance designed for human users.
Here are the six most common shadow identity types in SaaS environments:
- Service accounts — Created for integrations, often with admin-level permissions that never get rotated
- API tokens — Long-lived credentials granting programmatic access to sensitive SaaS data
- Bot users — Automated accounts for workflows like Slack bots, CI/CD service users, and RPA processes
- OAuth app identities — Third-party apps authorized via consent prompts, maintaining persistent token-based access
- Machine credentials — Workload identities used in cloud-to-SaaS and SaaS-to-SaaS communication
- Orphaned accounts — Former employees’ service accounts, tokens, and API keys that were never deprovisioned
📊 The Scale of NHI Proliferation Is Staggering
The numbers should give every CISO pause. CyberArk’s research confirms that enterprises carry 20–40% more non-human identities than they actively track. Service accounts outnumber human users 3-to-1 on average across mid-market and enterprise environments. These identities frequently hold admin-level permissions, never rotate credentials, never trigger MFA challenges, and never get offboarded when the project or employee that created them is gone. EDR monitors processes on endpoints, but service accounts don’t run on endpoints. Legacy SIEM logs identity creation events but lacks the SaaS-native context to distinguish legitimate automation from attacker-created persistence mechanisms. The result is a massive, persistent attack surface entirely invisible to traditional security stacks.
🔗 SaaS Supply Chain: When One Vendor Breach Becomes Everyone’s Problem
Third-party breach involvement doubled to 30% year-over-year according to the Verizon DBIR 2025. Every SaaS-to-SaaS integration creates a supply chain dependency, and when a third-party vendor is compromised, every customer who integrated that vendor’s app inherits the breach. The Salesloft-Drift OAuth supply chain campaign demonstrated this at massive scale: a single compromised vendor propagated unauthorized access across 700+ organizations simultaneously, including major security companies like Cloudflare and Palo Alto Networks.
Here’s the compounding factor: supply chain compromises propagate through the very shadow identities, including OAuth app tokens, service accounts, and API credentials, that the vendor integration originally created. Traditional SOC tools have zero visibility into either the supply chain dependency graph or the shadow identities enabling that propagation. The intersection of these two blind spots is what makes them so dangerous together. Shadow identities are the propagation mechanism for supply chain attacks. Without visibility into both simultaneously, you’re defending against symptoms while the root cause, unmonitored non-human access, continues to expand unchecked.
✅ How UnderDefense Closes Both Blind Spots
We built UnderDefense MAXI to monitor both human and non-human identity behavior across your entire SaaS ecosystem. That means detecting anomalous API token usage, flagging service accounts with excessive permissions, tracking SaaS-to-SaaS integration permission changes, and alerting on shadow identity creation in real time. When behavioral alerts need human context, our analysts verify directly with the responsible team via Slack or Teams, because the fastest way to confirm whether that new service account is legitimate is not spinning up another dashboard or opening another ticket. It’s asking the engineer who created it, right now, in the channel where they already work.
Q5. How Do CI/CD Pipeline Compromises Turn Your DevOps Workflow into an Attack Vector?
Your engineering team pushes 47 deployments a day. Each one passes through your CI/CD pipeline, pulling dependencies, accessing secrets, building containers, and deploying to production. Now imagine an attacker injects a single malicious step into that pipeline. Every deployment from that moment forward ships compromised code to your customers. No endpoint was infected. No phishing email was sent. Your product itself became the attack vector, and your SOC saw nothing.
This is not a theoretical edge case but an operational reality already documented at scale. The CircleCI breach in January 2023 played out exactly this way. Attackers compromised an engineer’s session token, gained access to CircleCI’s production systems, and exfiltrated customer secrets, including environment variables, API keys, AWS credentials, and deploy tokens stored in CI/CD pipelines. CircleCI had to instruct every customer to rotate every secret immediately. The Codecov breach in 2021 followed the same playbook: attackers modified a bash uploader script that ran inside customer CI environments for over two months, silently extracting credentials from every organization using the tool.
⚠️ Why CI/CD Pipelines Are the New Crown Jewels
SaaS companies live in CI/CD. Pipelines have privileged access to source code repositories, secrets vaults, container registries, cloud deployment credentials, and production environments. They authenticate using service accounts and API tokens, the exact shadow identities covered in Q4. Compromising a pipeline doesn’t just compromise one system; it compromises the supply chain. Every customer who receives your software inherits whatever the attacker injected. The blast radius scales with your customer base.
Three hidden costs make CI/CD compromise uniquely devastating:
- ⏰ Detection lag: Average 60+ days before CI/CD supply chain attacks are identified, because traditional SOC tools don’t ingest deployment telemetry
- 💸 Remediation cost: Forensic analysis of every build artifact since compromise, plus customer notification and credential rotation across the entire downstream base
- ❌ Customer trust damage: When your product becomes the attack vector, the reputational impact persists far beyond the technical remediation
🛡️ How an AI SOC Should Handle CI/CD Telemetry
An AI SOC built for SaaS must treat CI/CD pipeline telemetry as a first-class data source, monitoring deployment logs, pipeline configuration changes, secrets access events, and dependency pulls. UnderDefense MAXI ingests this telemetry alongside identity, endpoint, and cloud data, applying AI-driven correlation across systems: unexpected pipeline modifications at 2 AM + new secrets access by unfamiliar service accounts + unusual dependency sources = attack chain detected before a single compromised build reaches production. Human analysts investigate with organizational context, verifying with DevOps leads directly via Slack or Teams before containment.
The Bottom Line
Your CI/CD pipeline has more privileged access than your CEO, and zero SOC coverage from traditional MDR providers. Arctic Wolf doesn’t ingest deployment events. CrowdStrike doesn’t monitor pipeline configurations. UnderDefense changes that equation by treating DevOps telemetry as security telemetry, because in a SaaS company, the build pipeline IS the attack surface.
Q6. What Is the ‘SaaS Kill Chain,’ and Where Does a Traditional SOC Lose Visibility?
The Lockheed Martin Cyber Kill Chain (reconnaissance, weaponization, delivery, exploitation, installation, command & control, and actions on objectives) was designed for network and endpoint intrusions. It assumes malware gets “delivered,” “installed,” and “beacons” to a C2 server. SaaS attacks follow none of these stages. There’s no malware delivery, no endpoint installation, no C2 beacon. SaaS attackers “log in” with stolen tokens, “move laterally” across SaaS apps via API calls, and “exfiltrate” through legitimate export functions. The traditional kill chain is structurally incapable of modeling the way SaaS-first companies actually get breached.
📊 The SaaS Kill Chain: 6 Stages
| Stage | Attack Action | How It Works | Traditional SOC Visibility |
|---|---|---|---|
| 1. Initial Access | OAuth consent phishing, compromised SaaS vendor, stolen API key | Attacker gains persistent SaaS access without touching endpoints | ❌ None |
| 2. SaaS Foothold | Persistent token access, mailbox rule creation, app permission escalation | Attacker establishes persistence within SaaS applications | ❌ None |
| 3. Lateral SaaS Movement | Cross-app API access, SaaS-to-SaaS integration abuse | Attacker moves across SaaS apps using legitimate API connections | ❌ None |
| 4. Persistence & Privilege Escalation | Shadow identity creation, service account manipulation, CI/CD credential theft | Attacker creates durable access mechanisms invisible to identity governance | ⚠️ Partial (only if IdP logs ingested) |
| 5. Data Discovery | Cross-app search, document enumeration via API, bulk metadata queries | Attacker identifies and maps high-value data across SaaS ecosystem | ❌ None |
| 6. Exfiltration | Legitimate export functions, API bulk data pulls, cloud storage sync | Attacker extracts data using sanctioned SaaS features | ⚠️ Limited (only if DLP configured for SaaS) |
❌ Where Traditional SOC Goes Blind
The pattern is stark: zero visibility at Stages 1–3 (all SaaS-layer activity), partial visibility at Stage 4 (only if identity provider logs are properly ingested), zero at Stage 5 (API-level enumeration generates no alerts), and limited at Stage 6 (only if DLP is configured for SaaS exports, which it usually is not). By the time a traditional SOC detects anything, the attacker is at Stage 5 or 6. Exfiltration is already underway.
✅ Where an AI SOC Maintains Detection at Every Stage
An AI SOC ingesting OAuth grant logs, API audit trails, identity provider events, and CI/CD deployment logs has detection capability at every single stage. UnderDefense MAXI’s multi-system correlation works like this: unusual OAuth grant (Stage 1) + anomalous API access pattern (Stage 3) + new service account creation (Stage 4) = confirmed SaaS attack chain, contained at Stage 3 before data discovery begins. ChatOps verification at each detection point adds the human context that AI alone cannot provide. “Did your team authorize this integration?” is answered directly in Slack, in real time.
The Structural Truth
The SaaS Kill Chain reveals something fundamental: traditional SOC tools don’t have SaaS-specific detection gaps but rather SaaS-specific blindness. The entire attack chain from Stage 1 through Stage 5 occurs in a layer that firewalls, EDR, and legacy SIEM were never designed to observe. An AI SOC built for SaaS is not optional but the difference between detecting at Stage 1 and discovering a breach at Stage 6.
Q7. What Telemetry Must an AI SOC Ingest to Detect SaaS-Layer Attacks?
The gap between what traditional SOC tools collect and what SaaS-native detection requires is enormous, and it’s the single biggest reason SaaS breaches keep accelerating despite record security spending. Here’s the comparison that matters.
📊 Traditional SOC Telemetry vs. SaaS-Required Telemetry
| Data Category | Traditional SOC Collects | SaaS-Required but Missing |
|---|---|---|
| Network | Firewall logs, NetFlow, IDS/IPS alerts | SaaS-to-SaaS API traffic (never touches your network) |
| Endpoint | Process execution, file changes, registry events | Service account authentication (no endpoint involved) |
| Identity | On-prem AD authentication logs | OAuth grant events, SaaS IdP sign-ins, NHI activity |
| Application | On-prem app logs | SaaS configuration changes, API audit trails |
| Cloud | Basic cloud infra logs (if configured) | CI/CD deployment events, container registry changes |
| Data Movement | DLP on email/endpoint | SaaS export functions, API bulk data pulls |
🔍 The 8 Essential SaaS Telemetry Categories
Every AI SOC defending SaaS environments must ingest these eight data streams. Missing even one creates a detection blind spot attackers will find.
| Telemetry Category | Key Data Points | SaaS Kill Chain Stage Detected |
|---|---|---|
| 1. OAuth/OIDC Grant Events | Consent grants, scope changes, token refresh patterns | Stage 1: Initial Access |
| 2. SaaS API Audit Logs | Call volumes, data access patterns, bulk operations | Stages 3 & 5: Lateral Movement, Data Discovery |
| 3. Identity Provider Events | Okta/Azure AD sign-in logs, MFA events, admin changes | Stages 1 & 4: Access, Privilege Escalation |
| 4. SaaS Configuration Changes | Security setting modifications, admin role changes | Stage 4: Persistence |
| 5. CI/CD Pipeline Events | Deployment logs, secrets access, pipeline config changes | Stage 4: Persistence, Supply Chain |
| 6. SaaS-to-SaaS Integration Logs | Cross-app data flows, integration permission changes | Stage 3: Lateral SaaS Movement |
| 7. Non-Human Identity Activity | Service account auth, API key usage, bot behavior | Stages 2–4: Foothold through Escalation |
| 8. Cloud Platform Audit Trails | AWS CloudTrail, Azure Activity Logs, GCP Audit Logs | Stages 4–6: Persistence through Exfiltration |
⚙️ Why Correlation Across Sources Is Non-Negotiable
Individual telemetry streams are necessary but insufficient. Each event looks benign in isolation. An OAuth grant event alone isn’t suspicious. An API call pattern alone isn’t alarming. A new service account alone isn’t unusual. But together, OAuth grant event (source 1) + anomalous API call pattern (source 2) + new service account creation (source 3) = confirmed SaaS attack chain. Without multi-source correlation, SSPM tools (configuration-only) and standalone identity governance (human-only) leave critical gaps.
✅ What UnderDefense Ingests, and What to Ask Your Provider
UnderDefense MAXI ingests all 8 telemetry categories through 250+ native integrations, including SaaS-native sources that endpoint-focused MDR providers simply don’t collect. Detection Logic as Code (written in Python, versioned, unit-tested, and deployed via CI/CD) ensures detection rules evolve at the same velocity as the SaaS threat landscape. Ask your current MDR provider three questions: Can you see our OAuth grants? Can you see our API audit logs? Can you see our CI/CD deployment events? If the answer to any of these is no, you have SaaS-specific blindness, and no amount of endpoint coverage will fix it.
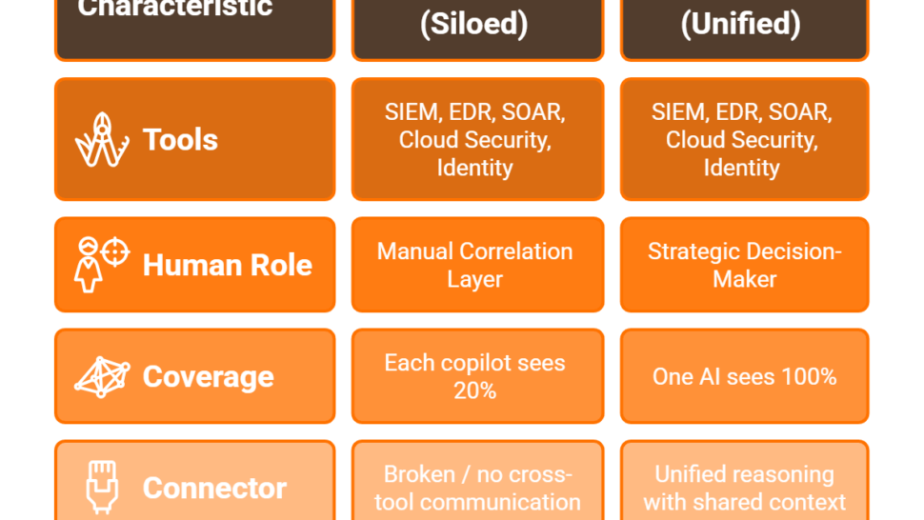
Q8. How Does an AI SOC with Human Ally Support Defend SaaS Environments, Including Compliance?
SaaS companies have more security tools than ever: EDR, CSPM, SSPM, SIEM, SOAR, and identity governance stacked on top of each other. Yet SaaS breaches keep accelerating. The paradox is not about tool quality but about fragmented context. Each tool sees one slice. No single tool reasons across OAuth tokens, API behavior, identity anomalies, and CI/CD events simultaneously. Alert fatigue in SaaS environments is not just a volume problem but a context problem across tools that don’t speak to each other.
❌ Why Traditional MDR Fails SaaS Companies
Arctic Wolf operates on a proprietary stack with no SaaS-native telemetry from your existing environment, and the architectural limitation is well-documented by customers. CrowdStrike Falcon Complete excels at endpoints but inherits EDR’s fundamental SaaS blindness. ReliaQuest promises AI-driven detection but returns tickets without clear answers and lacks human concierge verification. All three share the same structural limitation: built for endpoint and network security, retrofitted for “cloud.” SaaS is not cloud infrastructure. SaaS security requires SaaS-native detection.
✅ The AI SOC + Human Ally Model for SaaS
AI provides speed and correlation: analyzing OAuth grant patterns across thousands of users, detecting API anomalies across millions of calls, and identifying shadow identity creation in real time. Humans provide context AI cannot: “Is this new OAuth app something your team deployed, or an attacker’s persistence mechanism?” The model doesn’t just detect. It verifies, contains, and remediates. And critically, the same unified telemetry pipeline that enables SaaS-native detection automatically generates compliance evidence for SOC 2 Type I/II, ISO 27001, HIPAA, and PCI-DSS. Audit-ready security operations should be a byproduct of proper detection, not a separate manual workstream.
🛡️ UnderDefense’s SaaS Defense Architecture
Four capabilities plus built-in compliance define the operational model:
- SaaS-Native Telemetry Ingestion — OAuth logs, API audit trails, identity events, and CI/CD data through 250+ integrations
- AI-Driven Cross-Layer Correlation — identity → SaaS → cloud → endpoint in one context-aware detection engine
- ChatOps User Verification — resolving SaaS behavioral alerts by asking users directly via Slack or Teams
- Instant Containment & Response — revoking tokens, isolating accounts, and blocking lateral SaaS movement
MAXI Compliance (replacement for Vanta/Drata) provides auto evidence collection, continuous control validation, and framework-specific reporting, built on the same security operations platform. Detection Logic as Code ensures rules evolve at SaaS development velocity. Forever-free compliance kits for SOC 2, ISO 27001, and HIPAA included. 💰 Transparent pricing: $11–15/endpoint/month with 30-day turnkey onboarding.
⭐ What Operators Say
“The platform works really well with our other security tools, which makes things much simpler. And we really appreciate that we can customize the threat detection to focus on our specific needs.”
— Serhii B., CISO UnderDefense – G2 Verified Review
“We received little value from ArcticWolf. The product offered little visibility when we were using it. Anything you want to look at or changes you need to make must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“It also solved our problem of having separate security tools that didn’t work well together. Now, everything is connected and easier to manage.”
— Inga M., CEO UnderDefense – G2 Verified Review
Q9. Is Your Security Operations Team Ready for SaaS-Specific Threats? [Self-Assessment Checklist]
Most security teams can’t answer a simple question: does our SOC actually see what’s happening inside our SaaS applications? Not at the network layer, not at the endpoint, but inside the SaaS apps where your data, identities, and workflows actually live. This 10-item self-assessment cuts through vendor marketing and gives you an honest read on where your SaaS-specific detection stands right now.
📋 Score Your SOC’s SaaS Security Readiness
Each unchecked box is a blind spot attackers are already exploiting:
- ☐ Does your SOC monitor OAuth grant events and token usage in real time?
- ☐ Can your SOC detect anomalous API call patterns across SaaS applications?
- ☐ Do you have visibility into non-human identities (service accounts, API tokens, and bot users)?
- ☐ Are CI/CD pipeline events (deployments, secrets access, and config changes) ingested as security telemetry?
- ☐ Can your team identify and track SaaS-to-SaaS integration permissions and changes?
- ☐ Does your provider verify suspicious SaaS activity directly with affected users (not just escalate tickets)?
- ☐ Can your SOC contain SaaS-layer threats (revoke tokens, isolate accounts) within 30 minutes?
- ☐ Are SaaS security events correlated with endpoint, cloud, and identity telemetry in one unified view?
- ☐ Does your security monitoring generate compliance evidence (SOC 2, ISO 27001) automatically?
- ☐ Is your detection logic versioned and deployable via CI/CD to match your development velocity?
📊 What Your Score Means
⭐ 8–10 checks = SaaS-mature operations. Your SOC has SaaS-native visibility. Focus shifts to optimization, proactive threat hunting, and reducing mean time to contain. You’re in the top tier of SaaS security readiness.
⚠️ 4–7 checks = Critical SaaS-specific gaps. You likely have some identity and cloud visibility but are missing OAuth abuse detection, shadow identity monitoring, or CI/CD pipeline coverage. Attackers exploit exactly these gaps. They’re the path of least resistance into your SaaS ecosystem.
❌ 0–3 checks = SOC built for a pre-SaaS world. Your security operations were architected for endpoints and networks. The entire SaaS application layer, where your company actually runs, has fundamental visibility gaps that attackers are actively exploiting. This is where most organizations land when they honestly assess their readiness, and it’s not because they haven’t invested in security. It’s because traditional MDR providers don’t collect SaaS-native telemetry.
✅ Turning Every Unchecked Box into a ✓
UnderDefense MAXI is designed to close every gap on this checklist. SaaS-native telemetry ingestion covers OAuth, API, CI/CD, and identity events. AI-driven cross-layer correlation unifies SaaS signals with endpoint and cloud data in one detection engine. ChatOps-driven user verification resolves suspicious activity directly with affected users, with no ticket queues and no waiting. Instant containment revokes tokens, isolates accounts, and blocks lateral SaaS movement in minutes. And MAXI Compliance automates evidence generation for SOC 2, ISO 27001, and HIPAA, built into the same platform, not bolted on as an afterthought.
Most security teams go from 2–3 checks to 10/10 within 30 days of onboarding. That’s not a marketing claim but the outcome of 30-day turnkey deployment backed by dedicated Tier 3–4 analysts who learn your specific SaaS ecosystem from day one.
The Proof Behind the Checklist
UnderDefense clients achieve 96% MITRE ATT&CK coverage extended to SaaS and cloud techniques, with 99% alert noise reduction within the first month. Comprehensive SaaS protection shouldn’t require a 20-person SOC. It requires the right architecture, the right telemetry, and analysts who understand your environment.
Q10. Who Are the Best AI SOC Providers for SaaS Companies in 2026?
The leading AI SOC providers for SaaS companies in 2026 include UnderDefense, Obsidian Security, Valence Security, and specialized SaaS-native detection platforms, each with distinct architectural approaches to OAuth monitoring, API security, shadow identity discovery, and CI/CD pipeline defense. The market has evolved well beyond generic endpoint-focused security operations, and the differentiators now are SaaS-native telemetry ingestion, cross-layer correlation, human analyst verification, and integrated compliance automation.
🔍 What Separates Top AI SOC Providers for SaaS
Five criteria matter most when evaluating providers for SaaS-specific security operations:
- SaaS-native telemetry — Does the provider ingest OAuth grant events, API audit logs, CI/CD deployment events, and identity provider signals, or just endpoint and network data?
- Vendor-agnostic integration — Does it work with your existing security stack, or does it require proprietary tool replacement that creates lock-in and limits flexibility?
- Human analyst access — Can analysts communicate directly with affected users via Slack or Teams, or is everything ticket-based escalation with days of turnaround?
- Response capability — Can the provider contain SaaS threats (token revocation, account isolation, and integration blocking), or is it detection-only with remediation left entirely to your team?
- Compliance integration — Does security monitoring automatically generate audit evidence for SOC 2, ISO 27001, and HIPAA, or do you need separate tools like Vanta or Drata running alongside?
📊 How the Key Players Compare
Each provider excels in different scenarios, and understanding the architectural differences matters more than feature lists. Obsidian Security focuses on SaaS posture management and supply chain visibility through its Knowledge Graph, with strengths in SaaS-to-SaaS integration risk mapping, OAuth scope analysis, and behavioral baselining across identities and APIs. It’s a powerful detection and posture platform, but primarily focused on visibility rather than full managed response with human analyst containment.
Valence Security specializes in SaaS discovery, shadow IT identification, and identity governance, making it excellent for understanding your complete SaaS footprint, enforcing least-privilege across applications, and remediating identity exposure paths. Valence provides strong governance capabilities and compliance reporting for SOC 2 and ISO 27001, but its strength is posture management rather than real-time 24/7 threat detection and incident response.
✅ Where UnderDefense Fits
UnderDefense uniquely combines SaaS-native AI detection with human concierge response and integrated compliance: a full managed detection and response service that ingests the same SaaS telemetry as specialized SSPM tools while providing 24/7 analyst-driven investigation, ChatOps verification, and instant containment. The right choice depends on your current security stack, SaaS footprint, and whether you need detection-only or full managed detection and response across your environment.
🔗 Deep-Dive: Full Vendor Comparison
9 Best AI SOC Providers in 2026: A Complete Vendor Comparison
Complete vendor comparison with features, pricing, SaaS-specific capabilities, and deployment considerations for each AI SOC provider.
This analysis is based on documented response times, G2 reviews, published pricing, MITRE ATT&CK coverage scores, and operational outcomes across 500+ MDR deployments.
1. Why do traditional firewalls and EDR tools fail to protect SaaS companies from API and OAuth-based attacks?
We see this consistently across the SaaS companies we protect: firewalls and EDR were engineered for a world where threats cross network perimeters or execute malicious code on endpoints. SaaS-specific attacks operate entirely differently.
API abuse happens at the application layer—attackers exploit misconfigured endpoints, overprivileged OAuth tokens, and insecure service-to-service authentication. None of this generates the endpoint telemetry that EDR monitors. Firewalls see network traffic, not the semantic meaning of an API call that exfiltrates customer data through a legitimately authorized OAuth scope.
Consider this: an attacker compromises an OAuth token with broad read permissions. They access your CRM data, export customer records, and pivot through connected SaaS applications—all using valid credentials through authorized channels. Your EDR sees nothing because no malware was executed. Your firewall sees nothing because the traffic is encrypted HTTPS to legitimate SaaS endpoints.
We built our AI SOC capabilities to reason across identity, API behavior, and SaaS application context simultaneously. This means detecting when an OAuth token is used outside its normal behavioral pattern—something that requires correlating identity context with application-layer intelligence, not just endpoint telemetry.
2. What are shadow identities in SaaS environments, and how does an AI SOC detect them?
Shadow identities are user accounts, service accounts, and OAuth grants that exist outside your identity provider’s visibility. We’re talking about personal Gmail accounts invited to collaborate in Figma, generic team logins like [email protected], former employee accounts still active in apps months after offboarding, and service accounts created for automation with no linked owner.
The scale is staggering. Research shows nearly 80% of SaaS logins are invisible to IT, and 67% of logins bypass corporate SSO entirely. These shadow identities cannot be protected by MFA, cannot be governed by access policies, and create direct compliance failures under SOC 2, ISO 27001, and HIPAA.
An AI SOC detects shadow identities by correlating authentication patterns across your entire SaaS ecosystem—not just the apps connected to your IdP. It identifies accounts that authenticate without SSO, service accounts with no human owner, and OAuth grants that persist beyond their intended lifecycle.
We address this through our MAXI platform’s unified detection layer, which ingests identity signals from across your SaaS stack and uses behavioral analysis to surface unmanaged accounts before they become breach vectors. Our concierge analysts then verify findings directly with your team via Slack or Teams.
3. How does an AI SOC protect CI/CD pipelines from supply chain attacks and secret sprawl?
CI/CD pipelines are the operational backbone of every SaaS company—and one of the most under-secured attack surfaces we encounter. The threats are specific and well-documented: exposed secrets (API keys, tokens, database passwords) stored in repos or environment files, vulnerable open-source dependencies shipped with every deployment, misconfigured CI/CD tools with default permissions, and shadow pipelines that bypass security review entirely.
Traditional security tools have zero visibility into this domain. Your EDR doesn’t monitor GitHub Actions runners. Your firewall doesn’t inspect build artifact integrity. Your SIEM collects logs but cannot reason about whether a deployment script was modified to inject a backdoor.
An AI SOC purpose-built for SaaS environments monitors the entire CI/CD lifecycle:
-
Detecting secrets committed to repositories before they reach production
-
Identifying anomalous deployment patterns (unexpected builds at unusual hours, code pushed by service accounts that normally don’t deploy)
-
Correlating pull request approvals with deployment activity to flag bypassed review gates
-
Monitoring dependency changes for known supply chain attack patterns
We’ve built DevSecOps-aware detection into our SOC operations so your engineering team ships code fast while we monitor for the security signals they shouldn’t have to watch.
4. What makes an AI SOC different from a traditional SOC or SIEM for SaaS-specific threat detection?
A traditional SOC—whether in-house or outsourced—operates on a log-collect-alert model. SIEM ingests logs, correlation rules generate alerts, and analysts investigate. This works when threats produce clear log signatures. SaaS threats rarely do.
The difference with an AI SOC built for SaaS environments is threefold:
Context-aware reasoning: Instead of matching static correlation rules, an AI SOC reasons across identity, application behavior, and organizational context simultaneously. When an OAuth token accesses data outside its normal pattern, the AI SOC understands who granted the token, what data it typically accesses, and whether this deviation matches known attack patterns.
SaaS-native telemetry: Traditional SIEMs collect network and endpoint logs. An AI SOC ingests SaaS audit logs, API call metadata, OAuth grant histories, CI/CD pipeline events, and identity provider signals—the data sources where SaaS threats actually manifest.
Automated verification at scale: When thousands of behavioral anomalies occur daily, manual investigation breaks. An AI SOC automates enrichment and can verify suspicious activity directly with affected users.
We’ve documented why most AI SOC vendors automate the wrong things—and how we’ve architected MAXI to focus on the signals that actually matter for SaaS environments.
5. Can an AI SOC work with our existing security tools, or do we need to replace our entire stack?
This is the question we hear most from SaaS companies evaluating AI SOC solutions—and it’s the right one to ask. Many vendors force you onto proprietary platforms, abandoning your existing EDR, SIEM, or cloud security investments. That approach is expensive, disruptive, and unnecessary.
We built our AI SOC on a vendor-agnostic architecture specifically because SaaS companies already invest heavily in specialized tools: CrowdStrike or SentinelOne for endpoints, Splunk or Elastic for logs, Okta or Azure AD for identity, and native AWS/Azure/GCP security services for cloud. The problem isn’t the tools—it’s the lack of a unified intelligence layer that reasons across all of them.
Our MAXI platform integrates with 250+ existing security tools without forcing replacement. We ingest telemetry from your entire stack—endpoints, cloud, identity, SaaS applications, CI/CD systems—and correlate it through AI-driven detection that understands your organizational context.
The practical impact: you protect your existing investments, avoid the 6-month migration timelines that proprietary platforms demand, and get value from your AI SOC within 30 days of onboarding. Your SIEM rules, automation workflows, and business logic stay with you.
6. How does an AI SOC detect OAuth token abuse and overprivileged API access in real time?
OAuth token abuse is one of the most effective SaaS attack vectors because it leverages legitimate authorization mechanisms. Attackers don’t need to break anything—they simply exploit tokens with overly broad scopes, hijack consent flows, or abuse dormant grants that were never revoked.
Here’s what real-time detection looks like in practice:
-
Scope anomaly detection: The AI SOC baselines each OAuth token’s normal usage patterns—which APIs it calls, what data it accesses, at what frequency. When a token suddenly accesses an API endpoint it has never touched, or downloads data volumes 10x its normal pattern, it triggers immediate investigation.
-
Consent flow monitoring: Phishing-based OAuth attacks trick users into granting permissions to malicious applications. The AI SOC monitors new OAuth grants in real time, flagging applications requesting suspicious scope combinations.
-
Token lifecycle governance: Many breaches involve tokens that should have been revoked weeks or months ago. The AI SOC continuously audits token lifecycles, identifying dormant tokens with broad permissions.
We combine this detection with our 24/7 managed detection and response capability, so when OAuth abuse is detected, our analysts don’t just alert you—they contain the threat by revoking compromised tokens and communicating directly with affected users to verify legitimacy.
7. What SaaS-specific compliance risks do shadow identities and unmanaged OAuth grants create?
Shadow identities and unmanaged OAuth grants directly undermine the compliance frameworks that SaaS companies depend on—SOC 2, ISO 27001, HIPAA, and GDPR. The risks are specific and auditable:
Access control failures: SOC 2 Trust Service Criteria CC6.1 requires that logical access is restricted to authorized users. Shadow accounts bypass this entirely—they exist outside your IdP, aren’t governed by access policies, and can’t be revoked during offboarding.
Audit gaps: ISO 27001 Annex A.9 requires access management controls with clear accountability. When OAuth grants persist without ownership and service accounts have no linked human, you cannot demonstrate who authorized what access or when.
Data residency violations: Shadow SaaS applications may store data in jurisdictions that violate GDPR data residency requirements. If an employee signs up for a SaaS tool using personal credentials and processes customer data there, you have a compliance exposure you don’t even know about.
Least privilege violations: Overprivileged OAuth tokens with read/write access to sensitive data violate the principle of least privilege across virtually every compliance framework.
We address these risks through our compliance automation capabilities bundled with our AI SOC, which continuously audits identity posture and generates audit-ready evidence of access governance across your SaaS ecosystem.
8. How quickly can an AI SOC be deployed for a SaaS company without disrupting engineering velocity?
Deployment speed is a critical concern for SaaS companies because engineering velocity is revenue velocity—any security deployment that slows CI/CD pipelines, creates tool fatigue, or demands engineering attention is a non-starter.
Our deployment model is designed around this reality:
Week 1: Integration and telemetry ingestion. We connect to your existing tools—SIEM, EDR, identity provider, cloud platforms, SaaS applications—through API-based integrations. No agents to deploy on developer workstations, no pipeline modifications required. Your engineers keep shipping code without interruption.
Week 2-3: Baseline and custom detection tuning. Our AI SOC learns your organizational context—who your VIPs are, what normal API usage patterns look like, which OAuth grants are legitimate, and which CI/CD deployment patterns are expected. We tune detections to eliminate false positives before going live.
Week 4: Full operational coverage. 24/7 monitoring, detection, and response is live. Our concierge analysts understand your environment and can verify alerts directly with your team via Slack or Teams.
We invest a full 30 days in high-quality onboarding because cutting corners here means months of alert noise and analyst fatigue later. Learn more about how our SOC-as-a-Service model works for fast-moving SaaS teams.
The result: enterprise-grade SaaS security operational in 30 days, with zero disruption to your engineering pipeline.
The post AI SOC for SaaS: Protect CI/CD Pipelines, APIs, and OAuth Tokens appeared first on UnderDefense.