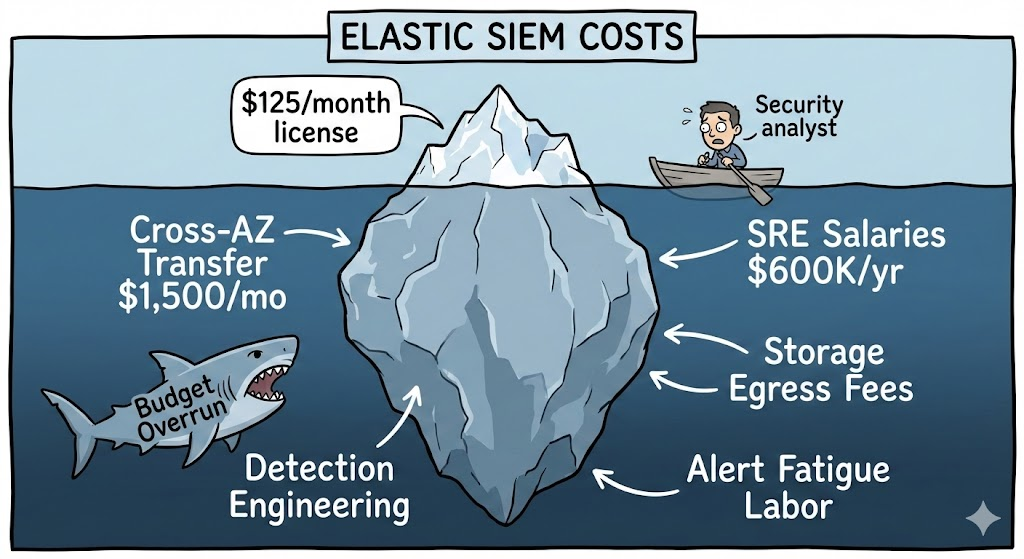
That $125/month Elastic SIEM license? It’s costing you closer to $70,000 per year. And if you’re self-managing it, try $700,000.
Elastic SIEM promises enterprise-grade security without the “ingest tax” of traditional SIEMs. Security leaders see the initial pricing and breathe a sigh of relief – finally, something affordable. But six months into production, the real Elastic SIEM costs surface: Elastic cross-zone fees hitting $1,500 monthly, specialized talent commanding $200K salaries, and the “licensing trap” that forces you into expensive tiers just to make storage affordable.
Organizations routinely discover their “budget-friendly” Elastic SIEM TCO costs 2-3x initial projections. One company hemorrhaged $600,000 annually before switching strategies.
In this article, you’ll discover:
- The three hidden cost multipliers that turn a $1,500 annual license into a $700K operational nightmare – and why vendor quotes conveniently omit them
- The “licensing trap” that forces you to pay premium fees for the very features designed to reduce your costs (spoiler: it’s called Searchable Snapshots)
- Real TCO breakdowns showing exactly where money disappears: cross-AZ networking taxes ($1,500+/month), normalization labor (40-60% of engineer time), and the $600K annual cost of a minimal 3-person operations team
The Elastic SIEM Pricing Illusion: Why “Resource-Based” Doesn’t Mean “Predictable”
Managing a modern Security Operations Center in 2026 means grappling with a harsh economic reality: what looks affordable on paper can drain your budget by hundreds of thousands before you realize what hit you.
Elastic SIEM has rightfully earned its reputation as a powerful, scalable security platform. Born from the legendary ELK Stack, it’s evolved into a sophisticated Search AI platform. But here’s the uncomfortable truth that surfaces six months into production: that initial subscription fee is just the visible tip of a massive fiscal iceberg when you account for the full Elastic SIEM TCO.
Elastic disrupted the SIEM market by abandoning traditional volume-based licensing in favor of a resource-consumption model. Instead of paying per gigabyte ingested – a metric that penalized data-rich organizations – Elasticsearch pricing charges for the compute, memory, and storage you actually provision. This shift sounds revolutionary until you realize what “resource consumption” actually means in practice.
The Three Faces of Elastic Pricing
Understanding your true Elastic SIEM costs starts with recognizing that Elastic offers three fundamentally different pricing models, each with unique cost drivers and hidden multipliers:
- Elastic Cloud Hosted: This is the managed service where Elastic handles infrastructure. You pay for provisioned capacity measured in RAM, CPU cores, and tiered storage. Elastic Cloud pricing consolidates costs under Elastic Consumption Units (ECUs), where $1.00 equals one ECU. The catch? That capacity needs to run 24/7 whether you’re actively ingesting logs or not. During a weekend with light traffic, you’re still paying full freight for idle resources.
- Elastic Cloud Serverless: The newest option eliminates capacity planning by charging purely for consumption via Virtual Compute Units (VCUs). One VCU represents 1GB of RAM plus associated compute. This sounds perfect for unpredictable workloads – until your ingestion spikes during a security incident and your costs explode without warning. Organizations report 300-400% month-over-month cost variations during high-activity periods.
- Self-Managed Elastic: The “free” option that’s anything but. While the Basic license costs nothing, the Elastic Enterprise license cost for the tier required for production SIEM features runs approximately $7,200 to $12,800 per node annually. And that’s before you account for the infrastructure, labor, and operational overhead that can dwarf the license cost itself.
The resource-based model shifts financial risk from the vendor to you. Miss your capacity planning? You’ll hit performance walls mid-incident. Overprovision to be safe? You’re burning cash on unused resources. This is a warning that “flexible pricing” requires sophisticated monitoring and constant SIEM cost optimization to avoid bill shock.
The Subscription Tier Trap: When “Standard” Means “Insufficient”
Elastic’s four-tier licensing model – Standard, Gold, Platinum, and Enterprise – looks reasonable until you map your actual security requirements to available features. The problem? Almost everything a modern SOC needs is locked behind the expensive tiers, impacting your Elastic Security pricing.
The Standard tier at $95-$99 monthly might work for basic monitoring, but it lacks the advanced detection engines, machine learning capabilities, and behavioral analytics that make a SIEM effective against modern threats. You’ll find yourself immediately pushed toward Platinum ($125-$131/month) just to access features like automated anomaly detection and ransomware protection.
But the real trap is the Enterprise tier. Not because of AI capabilities or advanced analytics – those are nice but not always essential. The killer feature locked behind Searchable Snapshots licensing requirements is access to the Frozen storage tier. This feature allows you to store petabytes of historical logs on cheap object storage like Amazon S3 (roughly $0.02 per GB per month) while keeping that data searchable.
Without Searchable Snapshots, you’re stuck paying $0.15-$0.17 per GB monthly for Hot tier NVMe storage. For an organization retaining 100TB of logs for compliance, that’s the difference between $2,000 and $17,000 per month in Elastic SIEM storage costs alone. The Enterprise license might cost an extra $5,000-$10,000 monthly, but you’re forced to pay it because the alternative – keeping everything on expensive storage – is financially catastrophic.
This is what we call the “licensing trap”: the feature you need to reduce costs is the same feature that increases your license fees. You save on infrastructure but lose it back to software licensing.
The Hidden Cost Multipliers: Where Budgets Go to Die
The most dangerous aspect of Elastic SIEM costs isn’t what’s on the invoice – it’s what’s missing from it. These “invisible” costs typically multiply your stated budget by 2x to 3x within the first 18 months of production deployment, making SIEM cost optimization critical from day one.
The Network “Chatter Tax”: When High Availability Gets Expensive
Elasticsearch is a distributed system by design. To maintain data integrity and high availability, nodes within your cluster must constantly communicate – replicating shards, coordinating searches, and synchronizing state. In an on-premises data center, this chatter is free. In the cloud, every byte crossing an Availability Zone boundary triggers a billing event through Elastic cross-zone fees.
Let’s make this concrete. You’ve architected your production SIEM across three AWS Availability Zones for resilience – a best practice that Elastic itself recommends. Your cluster ingests 5TB of log data daily with a replica factor of 1 (meaning each shard exists on two nodes for redundancy).
Here’s what actually happens to your costs:
- Initial ingestion: 5TB enters your cluster
- Replication across AZs: Another 5TB is copied to replica nodes in different zones
- Search coordination: Every query triggers cross-AZ communication as nodes aggregate results
- Shard rebalancing: Routine cluster maintenance moves data between zones
AWS charges approximately $0.01 per GB for cross-AZ transfer – in each direction. That 5TB of daily ingest generates roughly 10-15TB of actual network traffic when you account for replication and cluster operations. At $0.01 per GB, you’re looking at $1,500+ per month in pure Elastic cross-zone fees that have nothing to do with your license, storage, or compute costs.
And this cost scales linearly with your data volume. Double your ingestion to 10TB daily? Double your cross-AZ tax to $3,000 monthly. Organizations regularly miss this cost during POCs because small-scale tests don’t trigger noticeable networking fees – but production environments absolutely do.
The brutal irony? The more you optimize for reliability and performance by distributing your cluster across availability zones, the more you pay in invisible networking taxes. This is why experienced Elastic architects obsess over shard placement strategies and use tools like AWS PrivateLink to minimize cross-AZ traffic – but even with optimization, you can’t eliminate this cost entirely.
Get a transparent, no-BS analysis of your Elastic SIEM TCO.
The Storage Paradox: When Saving Money Costs More Money
We mentioned the licensing trap earlier, but it deserves deeper examination because it’s the single most counterintuitive cost in the Elastic ecosystem and a major factor in overall Elastic SIEM storage costs.
Storage tiers in Elastic – Hot, Warm, Cold, and Frozen – exist to match performance requirements with cost efficiency. Hot tier uses premium NVMe SSDs for real-time searches on recent data. Frozen tier uses object storage like S3 for archival data that’s rarely accessed but must remain searchable for compliance.
The economics seem straightforward:
- Hot tier: $0.15-$0.17 per GB per month (expensive but fast)
- Frozen tier: $0.02 per GB per month (95% cheaper but slower)
For a security operation retaining 200TB of logs annually, migrating 80% of that data to Frozen tier should save roughly $250,000 per year. The math works beautifully – on paper.
The problem? Searchable Snapshots – the feature that makes Frozen tier data queryable – requires Searchable Snapshots licensing at the Enterprise level. If you’re running a 50-node cluster, upgrading to Enterprise might cost an additional $200,000-$300,000 annually. Suddenly, your $250K storage savings evaporates into a net cost increase.
But it gets worse. Because Elastic often licenses based on RAM-bound Enterprise Resource Units (ERUs), adding memory to improve Frozen tier query performance triggers a “double-penalty”: you pay for the additional RAM in infrastructure costs while simultaneously increasing your software license liability.
This creates a scenario where organizations are paralyzed: keeping data on expensive Hot storage destroys your budget, but moving to cheap Frozen storage requires expensive licensing. Neither option feels economically rational.
The strategic solution? Most mid-to-large enterprises ultimately bite the bullet and pay for Enterprise tier because the storage savings, despite the licensing cost, still results in net positive ROI. But small-to-mid-market organizations often can’t justify the Elastic Enterprise license cost, leaving them stuck with unsustainable storage costs or reduced data retention that compromises security and compliance.
The Data Normalization Tax: Why Your Logs Are Useless Without Expensive Labor
Here’s a reality that vendor demos never show: raw logs flowing into Elastic are essentially gibberish until someone transforms them into structured, queryable data. This represents significant Elastic SIEM labor costs that are often overlooked in initial budgeting.
Unlike “schema-on-read” systems that parse data at query time, Elastic uses a “schema-on-write” architecture based on the Elastic Common Schema (ECS). This means every log source – firewalls, cloud platforms, EDR tools, custom applications – must be mapped to standardized field names and data types before ingestion.
This normalization process requires:
- Field Identification and Mapping: An engineer examines raw log formats, identifies which fields contain source IPs, destination ports, user agents, etc., and maps them to ECS field names (e.g., source.ip, destination.port, user_agent.original).
- Ingest Pipeline Development: Writing Logstash grok patterns or Ingest Node processors to extract, transform, and structure the data. A complex log format might require 40-60 lines of parsing logic.
- Type Validation and Testing: Ensuring fields are mapped with correct data types. Mapping an IP address as text instead of ip breaks aggregations and geographic visualizations – requiring a complete reindex of historical data to fix.
- Continuous Maintenance: As applications update and log formats change, pipelines break. Someone needs to monitor for parsing errors and update mappings accordingly.
In practice, this “normalization tax” consumes 40-60% of a security engineer’s time during the onboarding of new data sources. For an organization with 50+ different log sources (typical for mid-sized enterprises), this represents months of skilled labor before the SIEM is fully operational, directly impacting your Elastic SIEM labor costs.
The direct cost is substantial – a senior security engineer costs $150K-$200K annually. But the indirect cost is worse: while your team builds parsers, they’re not hunting threats, tuning detections, or responding to incidents. This opportunity cost is immeasurable but very real.
Managed SIEM providers sidestep this entirely by maintaining pre-built parsers for hundreds of common log sources, which is why the “build vs. buy” calculation often favors managed services despite seemingly higher monthly fees.
The Labor Overhead Nobody Budgets For
If you’ve read this far, you might be thinking, “But the license only costs $125 per month for Platinum – that’s incredibly cheap!” And you’d be technically correct. But focusing on the license cost while ignoring Elastic SIEM labor costs is like buying a Ferrari and being shocked by the maintenance costs.
Elastic is fundamentally a platform, not a turnkey product. The software gives you powerful search and indexing capabilities, but you’re responsible for everything else: cluster architecture, performance tuning, detection engineering, incident response, and continuous optimization. This requires specialized talent that commands premium salaries in a competitive market.
The Three-Headed Personnel Monster
A production Elastic SIEM requires three distinct skill sets, which may be consolidated into one or more Full-Time Employees (FTEs) depending on scale. Understanding these Elastic SIEM labor costs is crucial for accurate budget planning:
1. Elasticsearch SRE / Cluster Administrator ($120K-$180K annually)
This role owns infrastructure health: shard management, Index Lifecycle Management (ILM) policy tuning, performance optimization, capacity planning, and disaster recovery. For a self-managed cluster, expect 20-40 hours per month for routine maintenance, plus significantly more during incidents, upgrades, or scaling events.
A single botched upgrade can take the entire SIEM offline for hours. A poorly designed shard allocation strategy can degrade search performance to the point where security analysts can’t investigate incidents in real-time. This person is your insurance policy against catastrophic failures.
2. Detection Engineer ($130K-$200K annually)
Raw visibility means nothing without actionable alerts. This role develops and tunes correlation rules, integrates threat intelligence feeds, maps detections to the MITRE ATT&CK framework, and ensures the SIEM identifies modern attack techniques.
Out-of-the-box rules are only a starting point. Every environment has unique network architecture, business applications, and user behaviors that generate false positives. A Detection Engineer refines logic to achieve high-fidelity alerts – the difference between a SOC drowning in noise versus one that catches real threats quickly.
Organizations that skip this role suffer from “alert fatigue”: analysts spend 70-80% of their time investigating false positives, miss real incidents buried in the noise, and eventually become desensitized to alerts entirely. The cost of a missed breach dwarfs the salary of a good detection engineer.
3. Data Engineer / Pipeline Specialist ($110K-$160K annually)
The person focused on log ingestion, normalization, ECS mapping, and data quality. Without this role, you get “garbage in, garbage out” – logs that are technically stored but functionally useless because fields aren’t properly parsed or mapped.
This role also manages the balance between data retention and cost, implementing aggressive filtering to drop low-value logs before they hit the indexing engine and configuring tiered storage policies to optimize for both performance and budget.
The Math Is Brutal
A minimal three-person team costs roughly $360K-$540K in base salaries. Add 30% for benefits, payroll taxes, equipment, and overhead, and you’re at $468K-$702K annually – a major component of your Elastic SIEM TCO. Let’s call it an average of $600K per year – which is why that figure keeps appearing in case studies of organizations that switched to managed services.
For perspective: a fully managed SIEM service might cost $50K-$150K annually depending on asset count and data volume. Even at the high end of $150K, you’re spending 75% less than the cost of the internal team alone – and that doesn’t even account for the Elastic infrastructure and licensing costs you’re also paying.
Stop Overpaying for Noise: Your Elastic SIEM TCO Guide
The Proactive Path: Architecture and Strategy That Actually Works
Enough doom and gloom about Elastic SIEM hidden costs. Let’s talk about how sophisticated organizations successfully deploy Elastic SIEM without falling into budget traps. These strategies come from real production environments managing petabytes of security data – including organizations that achieved the mythical “50% TCO reduction” that vendor case studies promise but rarely explain.
Aggressive Tiered Storage Management: Make the Enterprise License Pay for Itself
The most impactful Elastic SIEM cost optimization is also the most controversial: paying for the Elastic Enterprise license cost specifically to unlock Searchable Snapshots and Frozen storage.
Here’s the math that makes this work: Let’s say you’re retaining 200TB of data annually for compliance. Keeping it all on Hot tier NVMe storage at $0.16 per GB costs roughly $32,000 per month. Moving 80% of that data to Frozen tier at $0.02 per GB drops your Elastic SIEM storage costs to $9,600 per month – a savings of $22,400 monthly or $268,800 annually.
If upgrading 50 nodes from Platinum to Enterprise costs an extra $15,000-$20,000 monthly ($180K-$240K annually), you’re still net positive by $28K-$88K per year on storage costs alone. And that doesn’t account for the performance improvements from keeping Hot tier focused on recent, frequently accessed data.
The strategic insight: Don’t think of the Elastic Enterprise license cost as an expensive upgrade – think of it as infrastructure cost arbitrage. You’re shifting expenses from storage hardware (where costs are linear and unavoidable) to software licensing (where you get additional features and better performance as a bonus).
Organizations that resist this logic out of sticker shock often end up spending more money on storage while getting worse performance and fewer features. It’s a textbook case of being “penny wise, pound foolish.”
Architect for Networking Cost Mitigation: AZ-Aware Deployments
Elastic cross-zone fees are unavoidable in multi-AZ deployments, but they’re not unmanageable. Sophisticated architectures reduce this “chatter tax” by 40-60% through strategic design.
Strategy 1: AZ-Aware Shard Allocation
Configure shard allocation awareness so that Elasticsearch preferentially places primary shards and their replicas in ways that minimize cross-AZ queries. For read-heavy workloads (which SIEM environments typically are), this means ensuring that each AZ has a complete copy of frequently accessed indices.
Strategy 2: Use AWS PrivateLink for Ingest
Instead of sending logs directly from EC2 instances across public AWS networking, use PrivateLink endpoints to keep traffic within the AWS backbone. This reduces not just cost but also latency.
Strategy 3: Pre-Aggregate Before Replication
Use Logstash or Ingest Nodes to pre-process and filter data before it enters the Elasticsearch cluster. Reducing initial ingest volume by 20% through intelligent filtering at the edge means 20% less data to replicate across zones.
One organization cut their monthly Elastic cross-zone fees from $4,200 to $1,800 simply by implementing AZ-aware allocation and moving to PrivateLink – a $2,400 monthly savings ($28,800 annually) with zero sacrifice in availability or performance.
The Labor Trade-Off: When Managed Services Are Actually Cheaper
This is where many organizations experience cognitive dissonance. It feels wrong to pay a third party to manage infrastructure you could theoretically run yourself. But the economics are overwhelming once you do honest accounting of Elastic SIEM labor costs.
A managed Elastic SIEM service from providers like UnderDefense typically costs $10-$30 per asset per month (depending on data volume and complexity). For an organization with 500 monitored endpoints, that’s $5,000-$15,000 monthly or $60K-$180K annually.
Compare that to the internal alternative when calculating total Elastic SIEM TCO:
- Personnel: $600K annually for a minimal 3-person team
- Elastic infrastructure and licensing: $100K-$300K annually depending on scale
- Opportunity cost: Your security team spends time on platform operations instead of threat hunting
Total self-managed TCO: $700K-$900K annually versus managed service at $60K-$180K annually.
But raw cost comparison misses the hidden value: managed services include 24/7 monitoring, pre-built detection rules tuned for low false positives, threat intelligence integration, and expert incident response. You’re not just saving money – you’re getting better security outcomes.
The case study at the beginning of this article – the organization that saved $600K annually – made exactly this calculation. They weren’t just replacing salaries; they were replacing the entire operational burden of SIEM management with a team of specialists who do nothing but Elastic security at scale.
Take Control of Your SIEM Economics Before They Control You
If you’ve read this far, you understand the uncomfortable truth: the Elastic SIEM pricing tag on the vendor website has almost nothing to do with what you’ll actually spend over three years of operation.
The initial license – $95 for Standard, $125 for Platinum, even $300 for Enterprise – represents less than 10% of your total Elastic SIEM TCO. The real money hemorrhages through Elastic cross-zone fees you didn’t know existed, Elastic SIEM labor costs you assumed was “figure-out-able,” and Elastic SIEM storage costs that balloon exponentially as compliance requirements force longer retention.
Organizations that succeed with Elastic SIEM share three common behaviors:
- They account for ALL costs upfront, not just the visible ones. They budget for cross-AZ transfer, specialized labor, and the Enterprise licensing tier that becomes inevitable once data volumes grow.
- They implement aggressive architectural optimization. They use tiered storage, AZ-aware deployments, and ILM policies to minimize waste while maintaining performance and availability.
- They honestly evaluate the build-vs-buy equation. They recognize that a $150K managed service can deliver better outcomes than a $700K internal team, and they’re willing to make the financially rational choice even if it feels counterintuitive.
The question isn’t whether Elastic is the right SIEM platform – it’s powerful, scalable, and battle-tested. The question is whether you’re prepared to deploy it intelligently or whether you’ll join the long list of organizations that discovered their “cost-effective” security solution costs 2-3x what they budgeted.
Your CFO will eventually ask pointed questions about Elastic SIEM costs. Better that you have the answers before the budget review, not during.
UnderDefense provides managed detection and response (MDR) services powered by Elastic Security, delivering 24/7 threat monitoring, expert detection engineering, and rapid incident response without the overhead of building and staffing an internal SOC. With proven case studies including $600K+ in annual savings and $650K in prevented ransomware losses, UnderDefense transforms Elastic from a complex platform into a turnkey security solution.
Need help now?
UnderDefense’s Security Team is available 24/7. Immediate triage, containment, and forensic assistance.
1. What is Elastic SIEM, and how is it different from traditional SIEM solutions?
Elastic SIEM is built on the Elasticsearch platform and uses a resource-based pricing model instead of charging per gigabyte of data ingested. Unlike traditional SIEMs like Splunk, which can become prohibitively expensive as data volumes grow, Elasticsearch pricing charges for the compute, memory, and storage you provision. This makes it theoretically more cost-effective for high-volume environments – but only if you properly manage the Elastic SIEM hidden costs that come with it, including infrastructure, labor, and networking costs.
2. How much does Elastic SIEM actually cost once you include hidden expenses?
The license subscription is just the beginning. For a mid-sized deployment, your total Elastic SIEM TCO includes:
- License: $125-$131/month for Platinum (minimum viable for SOC operations)
- Infrastructure: $2,000-$10,000/month depending on data volume and retention requirements
- Cross-AZ networking: $500-$5,000/month for production multi-AZ deployments (Elastic cross-zone fees)
- Labor: $50K-$600K annually depending on whether you self-manage (3-person team at ~$600K in Elastic SIEM labor costs) or use managed services (~$50K-$150K)
Total realistic TCO for self-managed: $700K-$900K annually. Total for managed service: $150K-$300K annually depending on scale.
3. What are the biggest hidden costs in Elastic SIEM deployments?
The three biggest cost multipliers that catch organizations by surprise:
- Elastic cross-zone fees for data transfer ($1,500-$5,000/month for production clusters)
- Specialized Elastic SIEM labor costs for platform management and detection engineering ($360K-$600K annually for internal team)
The “licensing trap” where Elastic Enterprise license cost is required to access cost-effective Frozen storage via Searchable Snapshots licensing, forcing you into higher licensing fees to reduce Elastic SIEM storage costs
4. How does Elastic SIEM pricing compare to Splunk and Microsoft Sentinel?
Each has a different economic profile when comparing Elastic Security pricing:
- Splunk: Charges per GB ingested, typically $150-$200 per GB for SIEM use cases. Best for low-volume, high-value scenarios. Most expensive at scale but unmatched for out-of-the-box detection content.
- Microsoft Sentinel: Charges per GB ingested with significant discounts for Microsoft logs. Best for Azure-native organizations, but costs escalate quickly with third-party data sources.
- Elastic: Charges for infrastructure resources (RAM, CPU, storage) via Elastic Cloud pricing. Most cost-effective at high volumes if properly optimized with SIEM cost optimization, but requires expertise and has the highest operational overhead.
For a 1TB/day ingestion rate, rough annual costs: Splunk ($5M+), Sentinel ($1.5M-$2M), Elastic self-managed ($700K-$1.2M including labor), Elastic managed ($300K-$600K).
5. What's the minimum Elastic subscription tier needed for effective SIEM operations?
Platinum ($125-$131/month) is the practical minimum for SOC operations because it unlocks:
- Behavioral anomaly detection
- Machine learning capabilities
- Automated ransomware protection
- Advanced threat detection engines
Standard and Gold tiers lack the security analytics needed for modern threat detection. Elastic Enterprise license cost ($200-$300+/month) becomes necessary when you need Searchable Snapshots licensing for cost-effective long-term retention and to manage Elastic SIEM storage costs effectively.
6. How quickly can I deploy Elastic SIEM compared to building an in-house solution?
- Managed service: 2-7 days to production-ready detection and response
- Self-managed with expertise: 3-6 months for initial deployment, 12-24 months to fully mature detection engineering and operations
- Self-managed without expertise: 6-12 months for initial deployment, often never reaches full maturity due to ongoing operational challenges
The time-to-value gap is one of the strongest arguments for managed services – especially considering that every day without effective detection is a day of exposure.
7. Can Elastic SIEM handle compliance requirements like PCI-DSS, HIPAA, or GDPR?
Yes, but compliance is about how you deploy and operate Elastic, not just the platform itself. Key requirements:
- Long-term log retention (Elastic supports this with tiered storage)
- Audit trails and access controls (RBAC and audit logging available)
- Data encryption at rest and in transit (supported)
- Integrity validation (log file integrity checks available)
Managed SIEM providers often include compliance-ready configurations and reporting as part of their service, significantly reducing the burden of demonstrating compliance during audits.
8. What happens to my data if I decide to leave Elastic or switch providers?
Data portability is straightforward for Elastic:
- Logs are stored in standard Elasticsearch indices that can be exported
- You can use snapshot/restore APIs to extract data
- Beware egress costs: Moving terabytes of data out of cloud storage triggers egress fees ($0.02-$0.09 per GB), which can be substantial for large datasets
Always clarify data portability terms and costs with managed service providers before signing contracts.
9. How can I calculate the ROI of switching from self-managed to managed Elastic SIEM?
Use this simplified formula to understand your Elastic SIEM TCO:
Self-Managed Annual TCO = (License Costs) + (Infrastructure) + (Elastic cross-zone fees) + (Elastic SIEM labor costs: $600K for 3-person team) + (Opportunity Cost of inefficiency)
Managed Service Annual Cost = (Monthly Service Fee × 12) + (Minimal Internal Oversight)
Annual ROI = Self-Managed TCO – Managed Service Cost
For most mid-market organizations, this calculation shows $400K-$700K in annual savings, plus intangible benefits like faster detection, better rule tuning, and elimination of operational headaches.
10. What metrics should I track to know if my Elastic SIEM is cost-optimized?
Monitor these metrics for effective SIEM cost optimization:
- Cost per GB stored broken down by storage tier (Hot, Warm, Cold, Frozen)
- Cross-AZ data transfer as % of total infrastructure cost (should be <15%) – tracking Elastic cross-zone fees
- Average search query latency by tier (degrading performance indicates scaling needs)
- Percentage of data in Frozen tier (should be 60-80% for compliance-heavy retention) to optimize Elastic SIEM storage costs
- False positive rate and analyst time spent on alert triage (high rates indicate poor tuning)
- Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) (your actual security outcomes)
If you can’t answer these questions with concrete numbers, your Elastic SIEM TCO is likely out of control.
The post Elastic SIEM TCO: The $600K Question Nobody Asks Until It’s Too Late appeared first on UnderDefense.