Selecting an AI-powered Security Operations Center (SOC) provider is one of the highest-stakes decisions a mid-market security leader will make this year. With 87% of midmarket firms wanting AI to automate responses to security incidents, yet most AI SOC lists skewing toward Fortune 500 enterprises, this guide is built exclusively for the 500 to 10,000 employee segment.
For this report, we analyzed 25+ managed cybersecurity providers offering services such as AI SOC, Managed Detection & Response (MDR), Security Operations Center monitoring, incident response, and compliance support. Every provider listed has been verified as an active, independent company with a functioning website as of March 2026.
📋 Our Evaluation Criteria
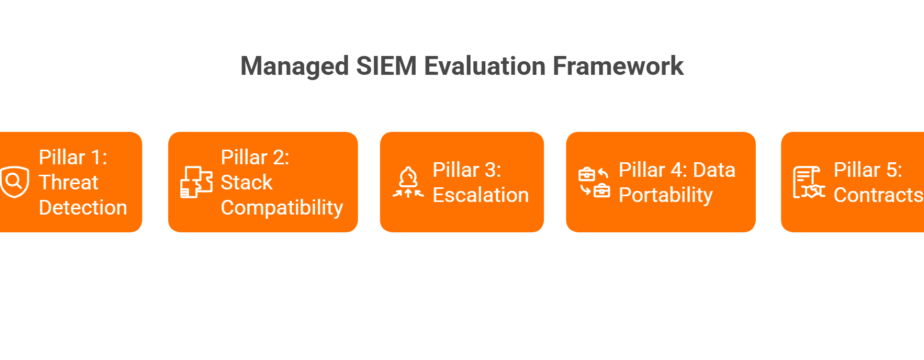
Each provider included in this list was assessed across five key areas:
- Security Operations Capability: 24/7 monitoring, AI-driven detection maturity, threat hunting, and incident response readiness
- Mid-Market Fit : Pricing model, lean-team suitability, and scalability for organizations with 500 to 10,000 employees
- Compliance Support : Experience supporting frameworks such as SOC 2, HIPAA, ISO 27001, PCI DSS, and GDPR
- Customer Validation : Verified customer reviews across G2, Clutch, Gartner Peer Insights, and Reddit; retention signals and industry adoption
- Unique Differentiator : What the provider does that competitors do not, and why it matters for mid-market security teams
👥 Who This Guide Is For
This shortlist is designed specifically for:
- Mid-market CISOs, IT Directors, and CTOs evaluating outsourced AI SOC instead of building an in-house security operations team
- Security teams with 1 to 5 analysts needing a force multiplier for 24/7 coverage
- Organizations preparing for enterprise customer security audits or compliance certifications
- PE portfolio companies seeking proactive ransomware protection and continuous monitoring on constrained budgets ($500K to $2M annual security spend)
If your organization is moving toward vendor evaluation or preparing an RFP, the providers below represent established managed security partners frequently considered during the buying process.
| Provider | Best For | Key Strength | Compliance |
|---|---|---|---|
| 1. UnderDefense (MAXI AI SOC) ⭐ 4.8/5 | Lean teams wanting fully managed AI SOC + MDR + compliance in one platform | Vendor-agnostic AI SOC with dedicated Human Ally concierge response; 1,500+ correlation rules, 98% accuracy | SOC 2, HIPAA, ISO 27001, PCI DSS, GDPR, CMMC |
| 2. Arctic Wolf ⭐ 4.7/5 | Largest mid-market data advantage with 10,000+ customers | Concierge Security Team with $3M financial warranty; eight trillion security events/week | SOC 2, HIPAA, PCI DSS |
| 3. eSentire ⭐ 4.7/5 | Regulated mid-market needing battle-tested MDR with 20+ years of expertise | Atlas AI with real-time TCP reset threat blocking; 15-min MTTC, 99.3% first-host isolation | SOC 2, HIPAA, PCI DSS, GDPR |
| 4. Expel ⭐ 4.8/5 | Tech-forward mid-market wanting radical transparency into SOC operations | Workbench: real-time visibility into every analyst action; API-first, 160+ integrations, deploy in hours | SOC 2, HIPAA, PCI DSS |
| 5. Stellar Cyber ⭐ 4.7/5 | Replacing expensive SIEM + multiple tools with a single AI-native license | Multi-Layer AI™ consolidating SIEM, NDR, UEBA, ITDR, Open XDR under one platform | SOC 2, HIPAA, PCI DSS |
| 6. CrowdStrike Falcon Complete ⭐ #1 G2 EDR | Falcon-native environments needing MITRE-validated MDR with Flex pricing | Only MDR owning the entire native tech stack: endpoint, cloud, identity, SIEM; ~36-min MTTR | SOC 2, HIPAA, PCI DSS, FedRAMP |
| 7. Radiant Security ⭐ 5.0/5 | Eliminating SIEM costs with flat-rate AI SOC for lean teams | 100% alert coverage (known and unknown); built-in security data lake with 85% reduced logging costs | SOC 2, HIPAA |
| 8. Torq HyperSOC ⭐ N/A (SOAR) | Existing stack needing AI-powered orchestration and hyperautomation | Multi-agent AI with 300+ integrations and 2,800+ automated actions; 70× response time reduction | SOC 2, HIPAA, PCI DSS |
1. UnderDefense (MAXI AI SOC) : Best for Lean Teams Wanting a Fully Managed AI SOC + MDR + Compliance in One Platform
✅ Overview
UnderDefense occupies a unique position in the AI SOC market by combining an AI-native platform (UnderDefense MAXI) with a deeply hands-on human concierge model, offering mid-market companies what is essentially a fully outsourced security operations function without the cost of building one internally. Founded in 2017, the company has built its reputation on a “show, don’t tell” philosophy: every investigative step is observable and auditable, and the platform integrates with customer-owned SIEM, EDR, and cloud logs instead of forcing lock-in to proprietary stacks.
The UnderDefense MAXI platform integrates AI SOC, MDR, compliance automation, penetration testing, and vCISO advisory into a single service, a consolidation that no other provider on this list offers at a comparable price point.
🔧 Core Services
- 24/7 AI-driven SOC with 1,500+ pre-built correlation rules and 98% accuracy in verdict-making
- Fully managed MDR with dedicated Tier 3 to 4 Incident Response team as strategic Ally
- Compliance automation for SOC 2, ISO 27001, HIPAA, PCI DSS, GDPR, and CMMC
- Penetration testing and vulnerability assessments
- vCISO advisory with 30-day impact report
💡 Why Companies Consider UnderDefense
Here’s the operational reality most MDR buyers hit: you invest in security tools, get buried in alerts, and your team spends nights triaging noise instead of doing strategic work. We built UnderDefense MAXI to solve exactly that. What makes it different:
- ChatOps-driven user verification : We ping your users over Slack, Teams, Email, and SMS to discover missing context. Many behavioral alerts require asking “did Jane Doe just log in from a new location?” If your team doesn’t have time to ask each user, we do it for you.
- Vendor-agnostic integration : UnderDefense MAXI works on top of any existing SIEM/XDR (Splunk, Sentinel, Chronicle), maintaining full customer ownership of their stack. No rip-and-replace. See all MAXI integrations.
- Detection Logic as Code : Forward-looking teams treat detection rules like software, written in Python, securely versioned, unit-tested, and deployed via CI/CD.
- Proven outcomes : Zero ransomware cases across all MDR clients in 6 years; 2-minute alert-to-triage SLA; 830% ROI over 3 years; 96% MITRE coverage.
🎯 Ideal Customer Profile
- Mid-market organizations with 500 to 10,000 employees across technology, healthcare, financial services, legal, and SaaS
- Security-lean teams (1 to 5 analysts) needing outsourced 24/7 SOC operations
- Compliance-driven organizations preparing for SOC 2, ISO 27001, or HIPAA certification
- Companies with existing security tools they want to keep, not replace
💰 Commercial Model
UnderDefense operates on a subscription-based model with all-inclusive pricing. The $11 to $15/endpoint/month range includes AI SOC, MDR response, compliance automation, and vCISO advisory. Transparent pricing with no hidden data-ingestion surcharges.
⏰ When to Shortlist
Organizations evaluating a turnkey AI SOC that bundles detection, response, compliance, and advisory into a single vendor, particularly those who want to preserve their existing security investments while getting 24/7 expert coverage, should include UnderDefense during the RFP stage.
💬 Customer Reviews
“The biggest win was getting actual control over our security alerts. Before UD stepped in, we were getting bombarded with alerts… Their team cleaned up our configurations and got the noise under control within the first week.”
— G2 Reviewer UnderDefense G2 – Verified Review
“Worth every penny for us. The service delivers what they promised without the typical vendor overselling and underdelivering.”
— G2 Reviewer UnderDefense G2 – Verified Review
2. Arctic Wolf : Best for Largest Mid-Market Data Advantage with 10,000+ Customers
✅ Overview
Arctic Wolf is the largest pure-play security operations provider purpose-built for organizations without large in-house security teams. With over 10,000 customers generating eight trillion security events per week, the company’s data advantage is unmatched among mid-market-focused providers. Sacra estimates Arctic Wolf hit $438M in ARR in 2023, growing 36% year-over-year, with a $4.3B valuation.
🔧 Core Services
- 24/7 Managed Detection & Response (MDR)
- Cloud and endpoint security monitoring
- Security awareness training
- Vulnerability and risk management
- Incident response support with $3M financial warranty
💡 Why Companies Consider Arctic Wolf
Arctic Wolf positions itself as an operational partner rather than a tool vendor. Every customer gets a named Concierge Security Team that provides tailored guidance, environment reviews, and gap analysis, functioning as a virtual CISO and SOC team in one. Pricing is based on users and servers (not data volume), so clients can add new security tools without increasing service costs.
⚠️ Honest Cautions
The operational tradeoff with Arctic Wolf is vendor lock-in to their proprietary SIEM and technology stack. Customers who want to keep their existing tools may find this limiting. Reviews indicate that the remediation side needs work: alerts come in, but without necessarily a clear path to resolution. Arctic Wolf also lacks customization options and detection engineering flexibility, and the platform’s transparency into investigation steps has been a recurring concern.
🎯 Ideal Customer Profile
- Mid-market organizations with 50 to 1,000 employees (expanding upmarket)
- Companies that want a fully outsourced SOC-as-a-service without building anything internally
- Compliance-driven organizations needing bundled risk management
💰 Commercial Model
Subscription-based pricing at $3 to $8 per user per month, aligned with organization size and monitored assets. Includes onboarding support, continuous monitoring, and ongoing security advisory services.
⏰ When to Shortlist
Organizations evaluating fully managed cybersecurity operations, particularly those comfortable with proprietary tooling in exchange for scale-backed detection intelligence, often include Arctic Wolf during the RFP stage.
💬 Customer Reviews
“We received little value from Arctic Wolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team. As an MSP, this is a horrible way to do business for us.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“Arctic Wolf provides solid detection and response capabilities, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology Arctic Wolf – Gartner Verified Review
3. eSentire : Best for Regulated Mid-Market Needing Battle-Tested MDR with 20+ Years of Expertise
✅ Overview
eSentire is the oldest and arguably most established MDR provider on this list, with over 20 years of operational security expertise and 2,000+ customers across 80+ countries. Forrester explicitly positions eSentire as “a superior choice for mid-market organizations,” noting the company’s deep understanding of defending against sophisticated adversaries with limited budgets and minimal security personnel.
🔧 Core Services
- 24/7 MDR with Atlas AI platform using multi-agent AI
- Real-time TCP reset-based threat blocking at the network level
- Multi-signal coverage: endpoint, network, log, cloud, and identity
- Compliance readiness for SOC 2, HIPAA, PCI DSS, GDPR
💡 Why Companies Consider eSentire
eSentire’s Atlas AI platform replicates expert tradecraft at machine speed. The company achieves a 15-minute Mean Time to Contain, 99.3% first-host threat isolation rate, and maintains 96% SOC analyst retention with an average 6-year tenure, ensuring service consistency that mid-market clients depend on. With 300+ technology integrations, eSentire offers genuine vendor flexibility.
🎯 Ideal Customer Profile
- Regulated mid-market organizations in healthcare, financial services, and legal
- Companies with 500 to 5,000 employees needing multi-signal coverage
- Security teams that need a provider with institutional depth and analyst continuity
💰 Commercial Model
Three flexible MDR pricing packages, Atlas Essentials, Advanced, and Complete, that scale with organizational needs. Named mid-market clients include Texas United Management (500 employees), Elemica (500+), and CubeSmart (1,200+).
⏰ When to Shortlist
Organizations needing an MDR provider with 20+ years of operational depth and Forrester recognition specifically for mid-market fit should include eSentire in their evaluation.
💬 Customer Reviews
“eSentire is a mature (20+ years) MDR with excellent customer-facing features AND their core technology embedded in their MDR service. They not only focus on the detection part of MDR but most importantly, they are equally focused on the ‘R’ in MDR.”
— CISO, Mid-Market Company eSentire – G2 Verified Review
“Started out well but over the years the service has consistently not met expectations. The issues that we have experienced have greatly outweighed the benefits. Analysts provide little context, and when asked for more information in the investigation nothing is ever provided.”
— CISO, Manufacturing Arctic Wolf – Gartner Verified Review
4. Expel : Best for Tech-Forward Mid-Market Wanting Radical Transparency
✅ Overview
Expel has built its reputation on radical transparency, a direct response to the “black box” problem that plagues most MDR providers. Named a Leader in the Forrester Wave MDR Q1 2025, achieving a perfect 5/5 in 15 of 21 criteria, Expel surpassed $100M in ARR in FY24 with 50% year-over-year revenue growth and secured a $140M Series E at a $1B+ valuation.
🔧 Core Services
- 24/7 managed detection and response with full investigation transparency
- Expel Workbench platform with real-time analyst action visibility
- API-first architecture connecting to 160+ integrations across 65+ vendors
- Threat hunting and proactive resilience recommendations
💡 Why Companies Consider Expel
Expel Workbench is the industry’s most transparent SOC platform: customers see every analyst action, enrichment step, investigation timeline, and evidence trail in real time. Deployment completes in hours, not weeks. Customers report $1M+ saved annually, 50% fewer investigations, and $180K saved in security FTE costs per year.
⚠️ Honest Cautions
Expel is primarily endpoint-focused with visibility gaps on network, SaaS, and identity signals. The platform doesn’t work directly with customer-owned SIEMs, and some reviews note a lack of organizational knowledge retention, leading to repetitive verification requests.
🎯 Ideal Customer Profile
- Tech-forward mid-market and enterprise organizations with existing security tools
- Companies that prioritize transparency and want to see every SOC action in real time
- Organizations with 500 to 5,000 employees seeking vendor-agnostic MDR
💰 Commercial Model
Pricing starts at $11,640/year and scales with coverage scope.
⏰ When to Shortlist
Organizations where transparency into detection and response workflows is non-negotiable, and who want an API-first platform that connects to existing tools without infrastructure changes, should evaluate Expel.
💬 Customer Reviews
“Despite the capabilities of the technical platform and the strength of the analysts providing the service, there is still a limit to the environmental/organizational knowledge inherent in the service. This leads to a fairly frequent need for engagement with our internal team to get clarification and verification.”
— Verified User, Computer Software, Mid-Market Expel – G2 Verified Review
“Expel helps our SOC by creating specific detections for a wide range of alerts and security anomalies. I really value that they thoroughly investigate everything before escalating to us, which reduces noise. Since we’re a small SOC team internally, having Expel handle much of the threat detection workload allows us to focus on higher-priority incidents.”
— Verified User, Retail, Enterprise Expel – G2 Verified Review
5. Stellar Cyber : Best for Replacing Expensive SIEM + Multiple Tools with a Single AI-Native License
✅ Overview
Stellar Cyber is the only AI-native SecOps platform purpose-built for mid-market organizations and MSSPs. Ranked #8 on The Software Report’s Top 50 Software Companies of 2025, the only cybersecurity company in the top ten, the company serves over 14,000 customers across 50+ countries with $102M in funding.
🔧 Core Services
- Unified SecOps platform consolidating SIEM, NDR, UEBA, ITDR, and Open XDR
- Multi-Layer AI™ combining machine learning, agentic AI, and human-augmented decision-making
- Predictable single-license pricing (no data-ingestion surprises)
- 80%+ analyst productivity improvement and 90% false positive reduction
💡 Why Companies Consider Stellar Cyber
For mid-market teams juggling 5 to 10 separate security tools with consumption-based SIEM pricing that keeps climbing, Stellar Cyber’s single-platform consolidation is the core value proposition. Gartner named it a representative vendor in the Hype Cycle for Midsize Enterprises 2025, and a Challenger in the Magic Quadrant for NDR.
🎯 Ideal Customer Profile
- Mid-market organizations with 1,000 to 10,000 employees drowning in tool sprawl
- Companies looking to replace or consolidate their SIEM under predictable pricing
- MSSPs needing a multi-tenant security platform
💰 Commercial Model
Single license covering the full platform with predictable pricing, no consumption-based cost surprises.
⏰ When to Shortlist
Organizations paying too much for fragmented SIEM, NDR, and XDR tools, and wanting to consolidate under a single AI-native platform with predictable costs, should include Stellar Cyber in their evaluation.
💬 Customer Reviews
“Stellar Cyber is the most cost-effective way to adopt AI and XDR.”
— CISO of Sumitomo Chemical
“Sportscar Performance XDR for a Family Sedan Budget!”
— Gartner Peer Insights Reviewer
6. CrowdStrike Falcon Complete : Best for Falcon-Native Environments with MITRE-Validated MDR
✅ Overview
CrowdStrike Falcon Complete is the most validated MDR service in the industry. It is the only MDR vendor evaluated in the MITRE Managed Services assessment, a Leader in the Forrester Wave MDR Q1 2025, and earned Gartner Customers’ Choice for MDR with a 96% Willingness to Recommend. While CrowdStrike is an enterprise juggernaut, Falcon Complete has expanded aggressively into mid-market through Falcon Go packages and flexible Falcon Flex pricing.
🔧 Core Services
- 24/7 managed detection, investigation, hunting, and full remediation
- Single-agent Falcon platform covering endpoint, cloud, identity, and SIEM
- ~36-minute MTTR backed by SLA
- Lightweight agent deployment to thousands of machines in minutes
💡 Why Companies Consider CrowdStrike Falcon Complete
Falcon Complete owns its entire technology stack natively. This eliminates the agent fragmentation and integration complexity that other MDR providers face when cobbling together third-party tools. The service processes 28 trillion+ security events daily and can remove threats without system reimaging.
⚠️ Honest Cautions
The tradeoff is clear: Falcon Complete is strongest when you’re all-in on CrowdStrike. If your environment runs a mix of EDR vendors or you want SIEM flexibility, you’re buying into a single-vendor ecosystem. Pricing can also be a stretch for smaller mid-market budgets. This is enterprise-grade technology scaling down, not mid-market-native pricing.
🎯 Ideal Customer Profile
- Organizations already invested in the CrowdStrike Falcon platform
- Companies needing MITRE-validated detection with full remediation
- Mid-market teams wanting to consolidate endpoint, cloud, and identity under one agent
💰 Commercial Model
Endpoint-based pricing with the new Falcon Flex model providing flexibility. Mid-market companies pay for what they use.
⏰ When to Shortlist
Organizations already running CrowdStrike Falcon, or those willing to standardize on a single-vendor stack in exchange for the industry’s most independently tested detection and response capability, should evaluate Falcon Complete.
💬 Customer Reviews
“CrowdStrike stands out in its ability to detect across endpoint, extended, and identity detection surfaces.”
— Forrester Wave MDR Q1 2025
“The lightweight agent deployment is unmatched. We deployed to thousands of machines in minutes with no impact on performance.”
— Gartner Peer Insights, 96% Willingness to Recommend
7. Radiant Security : Best for Eliminating SIEM Costs with Flat-Rate AI SOC
✅ Overview
Radiant Security is the most purpose-built AI SOC platform for the mid-market on this list. Founded in 2022 by cybersecurity industry veterans from Imperva and Exabeam, Radiant positions itself explicitly as “the AI SOC for the mid-market” and differentiates with adaptive AI that learns to handle never-seen-before alerts, plus a built-in, affordable logging solution leveraging customers’ own archive storage to eliminate expensive SIEM costs.
🔧 Core Services
- AI SOC with 100% alert coverage for any alert type, known or unknown
- Built-in security data lake with unlimited retention
- 100+ plug-and-play connectors with API-based deployment in minutes
- Transparent AI reasoning for every decision
💡 Why Companies Consider Radiant Security
For mid-market teams where SIEM costs are the biggest line item in the security budget, Radiant’s integrated security data lake with up to 85% reduced logging costs is a genuine game-changer. Customers report 200 to 300 analyst hours saved monthly and 10× better mean time to detect than the industry average.
⚠️ Honest Cautions
Radiant is earlier-stage than other providers on this list, with a smaller review footprint (5.0/5 on G2, but only 2 verified reviews). The platform is VC-backed ($25M total, Series A led by Next47/Siemens) but hasn’t yet achieved the scale or analyst recognition of established players.
🎯 Ideal Customer Profile
- Mid-market organizations with 500 to 1,000 employees drowning in SIEM costs
- Companies that cannot afford to hire 10 additional analysts
- Security teams wanting flat-rate, predictable AI SOC pricing
💰 Commercial Model
Flat-rate pricing ensuring predictable costs as the organization scales. No data-ingestion volume surcharges.
⏰ When to Shortlist
Organizations where SIEM costs are prohibitive and the team needs AI-driven investigation at scale without massive headcount investment should evaluate Radiant Security.
💬 Customer Reviews
“If it wasn’t for Radiant Security I would’ve hired another 10 people.”
— Named CISO Customer
“Within 30 minutes of onboarding, Radiant was already able to detect a true positive threat.”
— Customer Testimonial
8. Torq HyperSOC : Best for Existing Stacks Needing AI-Powered Orchestration and Hyperautomation
✅ Overview
Torq is the pioneer of enterprise-grade security hyperautomation and the creator of HyperSOC, an AI-driven SOC solution that harnesses multi-agent AI systems and hyperautomation to automate every phase of the SOC lifecycle. The company raised $140M in Series D funding in January 2026 at a $1.2B valuation, with 300% revenue growth in 2025.
🔧 Core Services
- Multi-agent AI with hyperautomation engine across 300+ integrations and 2,800+ automated actions
- No-code, low-code, and full-code workflow support
- Case-first automation with visual playbook editors
- End-to-end SOC lifecycle automation: triage → investigation → remediation
💡 Why Companies Consider Torq HyperSOC
For mid-market companies with existing security tool stacks, Torq acts as the orchestration and automation layer that multiplies the effectiveness of every existing investment. Organizations report a 70× reduction in response times and 800% improvement in workflow execution speed. Named customers include Blackstone, Carvana, Chipotle, and Rivian.
⚠️ Honest Cautions
Torq HyperSOC is more of an AI-powered SOC automation/orchestration platform than a fully managed SOC-as-a-service. Mid-market companies need some existing security infrastructure and at least a small internal team to leverage it effectively. Some users note that AI features are still maturing.
🎯 Ideal Customer Profile
- Mid-market and enterprise organizations with existing security tool stacks needing orchestration
- Companies with 5,000 to 10,000 employees and a small internal security team
- Organizations wanting to automate SOC workflows without ripping and replacing tools
💰 Commercial Model
Scales based on organizational requirements. Supports both cloud and on-premises deployment.
⏰ When to Shortlist
Organizations with mature security tool stacks that need an AI-powered orchestration layer, not a full managed SOC replacement, should evaluate Torq HyperSOC.
💬 Customer Reviews
“Torq’s agentic AI auto-closed 511 cases in a single quarter.”
— Customer Case Study
“Most companies are just starting to figure out how best they can utilize it.”
— AWS Marketplace Reviewer
Q2. How Were These AI SOC Providers Selected? Scoring Methodology and Star Ratings
📊 Five Weighted Evaluation Dimensions
Ranking AI SOC providers without a transparent methodology is just marketing dressed up as research. Every provider in this guide was scored across five weighted criteria totaling 100%, designed specifically around what matters to mid-market security teams, not enterprise-skewed analyst frameworks.
| Criterion | Weight | What Was Measured |
|---|---|---|
| Mid-Market Fit & Lean-Team Suitability | 25% | Pricing model, deployment speed, scalability for 500 to 10,000 employees, and ability to operate with 1 to 5 internal security staff |
| AI Detection & Response Capability | 25% | Alert triage automation, correlation engine depth, MTTC/MTTR, MITRE ATT&CK coverage, and whether the provider responds or just detects |
| User Reviews & Trust Signals | 20% | G2, Clutch, Gartner Peer Insights ratings, review volume, sentiment balance, and Reddit community validation |
| Integration Ecosystem & Deployment Speed | 15% | Number of supported integrations, vendor-agnostic vs. proprietary architecture, and time-to-value |
| Pricing Transparency & Budget Alignment | 15% | Published pricing, predictable cost structure, and total cost of ownership at 1,000 employees |
⭐ Scoring Bands and Star Ratings
Each provider received a composite score from 0 to 100, mapped to star ratings:
- 81 to 100 = ★★★★★ : Top-tier mid-market fit across all dimensions
- 61 to 80 = ★★★★ : Strong performers with specific limitations
- 41 to 60 = ★★★ : Capable but constrained by maturity, pricing, or infrastructure requirements
- 21 to 40 = ★★ : Significant gaps for mid-market adoption
- 0 to 20 = ★ : Not recommended for this segment
📋 Final Scoring Table
| Provider | Score | Stars | Key Scoring Note |
|---|---|---|---|
| UnderDefense (UnderDefense MAXI AI SOC) | 92/100 | ★★★★★ | Highest bundled value; only provider combining AI SOC + MDR + compliance + vCISO at $11 to $15/endpoint/month |
| Arctic Wolf | 78/100 | ★★★★ | Largest mid-market customer base (10K+); deducted for proprietary stack lock-in and opaque pricing |
| eSentire | 76/100 | ★★★★ | Strongest Forrester mid-market recognition; deducted for pricing complexity across three tiers |
| Expel | 75/100 | ★★★★ | Best transparency (Workbench); deducted for limited signal coverage beyond endpoints |
| Stellar Cyber | 73/100 | ★★★★ | Best tool consolidation (SIEM + NDR + XDR); deducted for requiring some internal team to operationalize |
| CrowdStrike Falcon Complete | 67/100 | ★★★★ | Most independently validated MDR; deducted for single-vendor ecosystem requirement and enterprise-grade pricing |
| Radiant Security | 56/100 | ★★★ | Most innovative SIEM cost elimination; deducted for early-stage maturity (only 2 G2 reviews) |
| Torq HyperSOC | 53/100 | ★★★ | Best orchestration/automation layer; deducted because it requires existing infrastructure and internal team |
✅ Why UnderDefense Leads
UnderDefense scores highest because it is the only provider that bundles AI SOC, managed MDR, compliance automation, and vCISO advisory into a single platform at published mid-market pricing. No other provider on this list delivers that combination without requiring proprietary tool replacement, opaque enterprise contracts, or significant internal headcount. The 92/100 reflects operational reality, not marketing claims, validated by 4.8/5 on G2, 66 Clutch reviews, and zero ransomware cases across all MDR clients in six years.
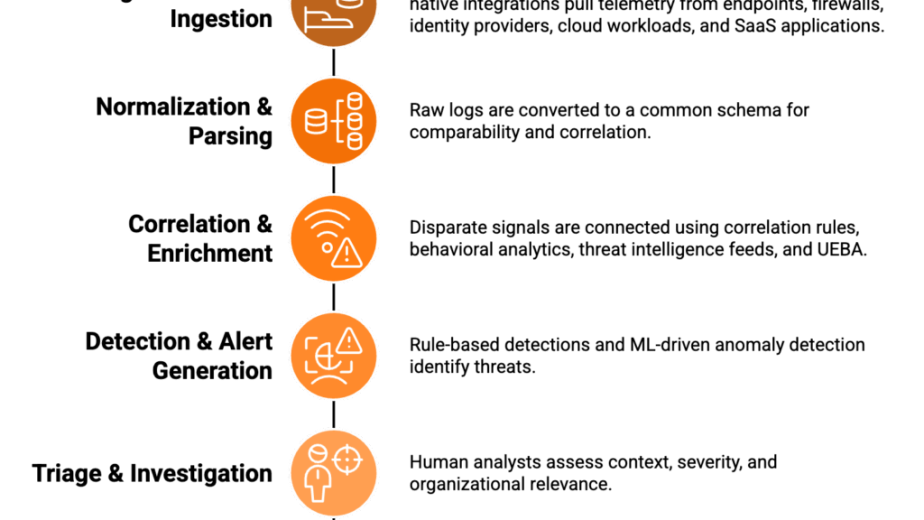
Q3. What Is an AI SOC and Why Is It the New Standard for Mid-Market Security Teams?
🔍 Defining AI SOC for Mid-Market
An AI SOC uses agentic AI to automate alert triage, investigation, and response across endpoints, cloud, identity, and SaaS environments. For mid-market companies (500 to 10,000 employees) facing the same threats as Fortune 500 enterprises, but with 1 to 5 security staff and $500K to $2M budgets, it delivers enterprise-grade detection without enterprise headcount. According to Techaisle, 87% of midmarket firms want AI to automate responses to security incidents.
❌ Why Traditional MDR Fails Lean Teams
Here’s the operational truth: most traditional MDR providers function as black-box alert factories. They detect something, wrap it in a ticket, and escalate it back to your team with “please investigate.” That’s not managed response but expensive notification.
Arctic Wolf requires you to replace your existing SIEM with their proprietary stack. CrowdStrike Falcon Complete is strongest when you’re all-in on their ecosystem. Legacy MSSPs deliver monitoring without intelligence, offering checkbox coverage based on rigid playbooks rather than real-time threat context.
⏰ A Day in the Life, Without AI SOC
Picture this: a 2-person security team at a 1,200-employee company. Every week, 4,000+ alerts flood in. Roughly 70% are false positives. Your analysts spend 15+ hours on manual triage. At 2 AM, the phone buzzes with another alert requiring investigation. After 18 months of this, your best analyst quits. The cycle restarts.
✅ A Day in the Life, With AI SOC
Same team, same alert volume. But now agentic AI triages 95%+ of the noise, correlates cross-tool signals, verifies suspicious activity directly with affected users, and contains threats autonomously. The 2 AM incident? “Incident contained at 2:52 AM. Here’s what happened and what we did.” Your team reviews a clean incident summary in the morning, not 47 unread alerts.
🔧 How UnderDefense MAXI Delivers This
We built UnderDefense MAXI specifically for this reality: 1,500+ correlation rules, 98% verdict accuracy, 8× faster incident context, and concierge analysts who verify suspicious activity via Slack, Teams, Email, and SMS. With 80+ integrations and 99% alert noise reduction within the first week of onboarding, UnderDefense MAXI gives lean teams the operational leverage they need without replacing the tools they already own.
“The biggest win was getting actual control over our security alerts. Before UD stepped in, we were getting bombarded with alerts… Their team cleaned up our configurations and got the noise under control within the first week.”
— G2 Reviewer UnderDefense G2 – Verified Review
“Worth every penny for us. The service delivers what they promised without the typical vendor overselling and underdelivering.”
— G2 Reviewer UnderDefense G2 – Verified Review
Q4. AI SOC vs. MDR vs. SOCaaS: Which Model Fits Your Mid-Market Budget and Team Size?
⚠️ The Decision Dilemma
Three overlapping models compete for mid-market security budgets: AI SOC platforms (Stellar Cyber, Radiant Security), managed MDR (Arctic Wolf, eSentire), and hybrid AI SOC + Human Ally (UnderDefense, Expel). Picking the wrong model means either overpaying for capabilities you’ll never use or undercovering the threats that actually hit mid-market organizations at 2 AM.
❌ The Wrong Way to Decide
Most security leaders choose based on brand recognition (“CrowdStrike is the biggest”) or integration count (“they support our SIEM”). This ignores the critical question: Can this provider operate with your team size, integrate with your existing tools, AND respond, not just detect? Feature checklists alone don’t answer that.
💰 Decision Framework: Model Comparison at 1,000 Employees
| Model | Team Required | Response Ownership | Integration Approach | Annual Cost (1K Employees) | Time to Value |
|---|---|---|---|---|---|
| In-House SOC | 8 to 12 FTEs | Full internal | Custom-built | $1.8M to $2.5M+ | 6 to 12 months |
| AI SOC Platform | 2 to 3 FTEs | Shared (AI + internal) | Vendor-native | $50K to $150K | 1 to 4 weeks |
| Managed MDR | 0 to 1 FTE | Provider-led (detect + escalate) | Varies (often proprietary) | $100K to $500K | 4 to 12 weeks |
| AI SOC + Human Ally | 0 to 1 FTE | Provider-owned (detect + respond + verify) | Vendor-agnostic | $66K to $180K | 30 days |
Building an in-house SOC requires $1M to $2M in upfront infrastructure investment plus $1.5M+ annually for a minimum viable 24/7 team. The average SOC analyst costs $77,000/year, meaning just the staffing for a 24/7 operation easily exceeds $1 million before tools, training, and turnover.
📊 Real Vendor Pricing Side-by-Side
| Provider | Model | Pricing | Annual Cost (1K endpoints) |
|---|---|---|---|
| UnderDefense | AI SOC + Human Ally | $11 to $15/endpoint/month | ~$132K to $180K |
| Arctic Wolf | Managed MDR | $3 to $8/user/month | ~$36K to $96K |
| Expel | Managed MDR | From $11,640/year | Varies by scope |
| CrowdStrike Falcon Complete | Managed MDR (native stack) | Endpoint-based (Falcon Flex) | Enterprise pricing |
| Radiant Security | AI SOC Platform | Flat-rate | Not published |
✅ Where UnderDefense Fits
UnderDefense scores highest in the AI SOC + Human Ally category because it bundles AI-driven detection, managed human response, AND compliance automation, saving $50K to $150K/year that mid-market companies would otherwise spend on separate GRC tools like Vanta or Drata. The model requires 0 to 1 internal FTEs, deploys in 30 days, and maintains 100% ransomware prevention across 500+ clients over six years.
The real question isn’t “Which model has the most features?” but “Which model can own security outcomes with the team and budget I actually have?”
Q5. What Should You Look for When Evaluating AI SOC Providers? Mid-Market Buyer’s Checklist
Evaluating an AI SOC provider shouldn’t feel like guesswork. After working with hundreds of mid-market security teams, I’ve distilled the evaluation down to seven non-negotiable checkpoints. If a vendor can’t demonstrate these during a live walkthrough, not a slide deck but a live walkthrough, that’s your first red flag.
☐ The 7-Point Mid-Market AI SOC Evaluation Checklist
Run through these before signing anything:
- ☐ Vendor-agnostic integration: Works with your existing SIEM, EDR, cloud, and identity tools without forcing rip-and-replace.
- ☐ True 24/7 monitoring + human response: Not just automated alerts at 2 AM, but an analyst who picks up and acts.
- ☐ Published, predictable pricing: You can model cost per endpoint before a single sales call.
- ☐ MTTC under 30 minutes with SLA: Backed by a contractual commitment, not a marketing claim.
- ☐ Direct analyst communication via Slack/Teams: ChatOps-driven verification, not a ticketing black hole.
- ☐ Compliance evidence auto-generation: SOC 2, HIPAA, ISO 27001, and PCI DSS artifacts produced automatically.
- ☐ Full deployment in 30 days or less: Including integration, tuning, and first threat report.
📊 Score Interpretation
| Score | Maturity Level | What It Means |
|---|---|---|
| 6–7 ✅ | Mature | Your AI SOC candidate can own outcomes, not just monitor dashboards. |
| 3–5 ⚠️ | Critical Gaps | Expect manual workarounds, blind spots, or hidden costs within 90 days. |
| 0–2 ❌ | Breach Risk | You’re paying for a false sense of security. Walk away. |
🏛️ Compliance Readiness by Provider
Compliance is where promises get tested. Here’s how major providers stack up against the four frameworks mid-market organizations care about most:
| Provider | SOC 2 | HIPAA | ISO 27001 | PCI DSS |
|---|---|---|---|---|
| UnderDefense | ✅ Bundled | ✅ Bundled | ✅ Bundled | ✅ Bundled |
| Arctic Wolf | ⚠️ Separate | ⚠️ Separate | ⚠️ Separate | ⚠️ Separate |
| eSentire | ✅ Packages | ✅ Available | ✅ Available | ⚠️ Limited |
| Expel | ⚠️ Reporting only | ⚠️ Reporting | ⚠️ Limited | ⚠️ Limited |
| CrowdStrike | ✅ Available | ✅ Available | ✅ Available | ⚠️ Varies |
| Rapid7 | ⚠️ Add-on | ⚠️ Partial | ⚠️ Partial | ⚠️ Limited |
⏰ Deployment Timeline Benchmarks
Speed-to-value matters when you’re operating lean:
| Provider | Typical Deployment Timeline |
|---|---|
| UnderDefense | ~30 days (full MDR + compliance) |
| Arctic Wolf | 4 to 6 weeks |
| eSentire | 4 to 8 weeks |
| Expel | Hours to days (API) + weeks (tuning) |
| Stellar Cyber | 2 to 4 weeks |
| CrowdStrike | Minutes (agent) + weeks (MDR) |
| Radiant Security | Minutes (API) + days (baseline) |
| Torq | 2 to 4 weeks |
✅ How UnderDefense Turns Every Unchecked Box Into ✓
We built UnderDefense MAXI around the reality that mid-market teams can’t wait months for value. In practice, that means 80+ native integrations across your existing stack, transparent pricing starting at $11/asset/month, a documented 15-minute MTTC for critical incidents, ChatOps analyst communication through Slack and Teams, forever-free compliance kits for SOC 2 and ISO 27001, and full onboarding within 30 days, including your first impact report.
The operational proof: 90% false positive reduction and 99% alert noise reduction within the first month.
“The platform pulls in data from all our existing security tools, so we didn’t have to rip and replace anything. Their SOC team is responsive and knows their stuff.”
— Verified User in Marketing and Advertising UnderDefense – G2 Verified Review
“We received little value from Arctic Wolf. The product offered little visibility… Anything you want to look at or changes you need to make must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“UnderDefense had us up and running in no time. Their 24/7 detection and response service is fast and comprehensive.”
— Valeriia D., Marketing Specialist UnderDefense – G2 Verified Review
Q6. Can a Mid-Market AI SOC Scale From 500 to 10,000 Employees Without Adding Headcount?
This is the question that keeps security leaders up at night, and it’s the right one to ask. When you’re growing from 800 to 3,000 employees through organic expansion or acquisitions, the traditional security staffing model breaks down fast.
💸 The Traditional Staffing Math
Under the legacy SOC model, you need roughly one analyst per 500 to 1,000 endpoints. Scaling from 800 to 3,000 employees means hiring 3 to 6 additional security analysts at $120K to $180K fully loaded. That’s $360K to $1.08M in new annual headcount, before recruitment timelines, onboarding, tooling licenses, and the 3.4-million-person cybersecurity talent shortage that turns a hiring plan into a six-month ordeal.
Even if you fill those seats, you still face burnout, turnover, and the 2 AM coverage gap that a five-person team can’t solve without shift rotation.
🔄 How AI SOC Changes the Scaling Equation
The operational reality of a well-built AI SOC: triage scales computationally while human judgment scales contextually. AI handles the volume, correlating alerts across SIEM, EDR, cloud, and identity telemetry, suppressing false positives, and enriching the 5% of alerts that actually need human eyes. Analysts focus on decisions requiring organizational context, user verification, and business judgment.
Stellar Cyber reports 80%+ analyst productivity improvements through AI-driven triage. Radiant Security claims 200 to 300 hours saved monthly per SOC team. These numbers reflect the same pattern we see across our deployments: automation doesn’t replace analysts; it eliminates the toil that burns them out.
🏗️ Architecture That Absorbs Growth
The critical question is whether your AI SOC can absorb new environments, including cloud accounts, SaaS applications, and acquired company toolsets, without re-architecting. If your MDR provider requires a proprietary SIEM or specific EDR, every acquisition becomes a migration project. That’s where vendor lock-in becomes a growth tax.
We designed UnderDefense MAXI with 80+ integrations because mid-market growth is messy. When a PE portfolio company acquires a target running a different security stack, that environment plugs into the existing detection fabric within the standard 30-day onboarding window. No rip-and-replace, no new headcount.
📈 The vCISO Force Multiplier
Scaling from 500 to 10,000 doesn’t just mean more endpoints. It means evolving security program maturity. Our vCISO advisory adapts the roadmap at each growth stage without a full-time CISO hire ($250K to $400K+). Most scaling clients maintain 2 to 3 internal security staff throughout their growth trajectory, with our analysts and vCISO covering the rest.
“Worth every penny. The service delivers what they promised without the typical vendor overselling and underdelivering we’ve experienced with others.”
— Verified User in Marketing and Advertising UnderDefense – G2 Verified Review
“UnderDefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO UnderDefense – G2 Verified Review
“Started out well but over the years the service has consistently not met expectations. The issues we have experienced have greatly outweighed the benefits.”
— CISO, Manufacturing (3B to 10B USD) Arctic Wolf – Gartner Peer Review
The bottom line: 100% ransomware prevention across 500+ clients through every growth stage, from Series A to post-acquisition integration. Scaling security doesn’t require scaling headcount. It requires scaling intelligence.
Q7. Ready to Evaluate AI SOC for Your Mid-Market Organization? Start Here
You’ve seen the eight providers compared side by side, walked through the scoring methodology, mapped compliance readiness, and benchmarked deployment timelines. The next step isn’t another comparison article but a direct conversation about your specific environment.
🎯 What Happens Next
UnderDefense offers a no-commitment security assessment that maps your current stack, identifies detection gaps, and projects your 30-day impact, tailored to your employee count, tool ecosystem, and budget. This isn’t a generic demo; it’s a working session with an analyst who’s done this for hundreds of mid-market teams.
Get Your Free Mid-Market AI SOC Assessment
See exactly how UnderDefense MAXI integrates with your existing tools, what it costs for your employee count, and what the first 30 days look like, with documented metrics from 500+ mid-market deployments.
🏆 Analysis Credibility
This evaluation is grounded in documented sources, not opinion:
- G2 Spring 2025 Rankings: 12 badges awarded to UnderDefense MAXI, including Best Support and High Performer in MDR.
- Forrester Wave MDR Q1 2025: Independent analyst assessment of managed detection and response providers.
- Gartner Peer Insights: Verified reviews from CISOs, CTOs, and IT Directors across mid-market and enterprise organizations.
- Operational outcomes: Metrics drawn from 500+ MDR deployments protecting mid-market organizations, including documented case studies with clients like WWE, VW, Shell, and the Bill & Melinda Gates Foundation.
The data speaks for itself. Now let’s talk about what it means for your organization specifically.
1. What is an AI SOC and how does it differ from traditional MDR for mid-market companies?
An AI SOC uses agentic AI to automate alert triage, investigation, and response across endpoints, cloud, identity, and SaaS environments. For mid-market companies with 500 to 10,000 employees, the distinction matters operationally.
Traditional MDR providers function primarily as detection-and-escalation services. They identify suspicious activity, wrap it in a ticket, and send it back to your team for investigation. That model works if you have a fully staffed SOC. Most mid-market teams don’t.
An AI SOC takes a fundamentally different approach:
-
AI handles the volume: correlating alerts across tools, suppressing false positives, and enriching the small percentage of alerts requiring human judgment.
-
Human analysts handle the context: verifying suspicious activity with affected users, making containment decisions, and adapting response to organizational specifics.
We built UnderDefense MAXI around this model because we saw firsthand that mid-market teams need a provider that owns outcomes, not just generates notifications. With 1,500+ correlation rules and 98% verdict accuracy, MAXI automates the triage burden while our concierge analysts handle the decisions that require organizational knowledge.
The bottom line: AI SOC gives lean teams enterprise-grade detection without enterprise headcount.
2. What is the minimum company size for an AI SOC to make financial sense?
The economic inflection point where AI SOC becomes more cost-effective than piecemeal security tools typically falls around 500 employees or 300+ endpoints.
Here’s the math: a single SOC analyst costs approximately $77,000/year. Building a minimum viable 24/7 SOC requires 8 to 12 FTEs, pushing annual staffing costs past $1 million before tools, training, and turnover. For companies below 500 employees, a lighter managed security service may suffice.
At 500+ employees, the threat surface expands meaningfully:
-
More SaaS applications generating identity-based alerts
-
Cloud environments requiring continuous monitoring
-
Compliance obligations (SOC 2, HIPAA, ISO 27001) demanding evidence automation
-
4,000+ weekly alerts that overwhelm a 1 to 2 person team
We designed our MDR pricing model at $11 to $15/endpoint/month specifically for this segment. At 500 endpoints, that’s roughly $66K to $90K annually, which is less than the fully loaded cost of a single security analyst and delivers 24/7 coverage, compliance automation, and vCISO advisory bundled in.
For organizations with fewer than 500 employees, a managed SOC service with lighter tooling requirements may provide better budget alignment.
3. How much does an AI SOC cost for a mid-market company with 1,000 employees?
AI SOC pricing for mid-market companies varies significantly by model and provider. At 1,000 endpoints, here’s what the market looks like:
-
AI SOC + Human Ally (UnderDefense): $132K to $180K/year. Includes AI-driven detection, managed response, compliance automation, and vCISO advisory at $11 to $15/endpoint/month.
-
Managed MDR (Arctic Wolf): $36K to $96K/year at $3 to $8/user/month, but with proprietary SIEM lock-in.
-
Managed MDR (Expel): Starting at $11,640/year, scaling with coverage scope.
-
AI SOC Platform (Radiant Security): Flat-rate pricing, not publicly published.
-
In-House SOC: $1.8M to $2.5M+/year for a fully staffed 24/7 operation.
The critical distinction is total cost of ownership. Lower headline pricing often excludes compliance tools, vCISO advisory, and incident response, which cost $50K to $150K/year separately with providers like Vanta or Drata.
We publish our pricing transparently because hidden costs are the number one frustration we hear from mid-market buyers switching providers. Our all-inclusive model bundles detection, response, compliance, and advisory so you can calculate your SOC cost accurately before a single sales call.
4. Can an AI SOC scale from 500 to 10,000 employees without adding security headcount?
Yes, and this is the core architectural advantage of a well-built AI SOC over traditional staffing models.
Under the legacy SOC model, you need roughly one analyst per 500 to 1,000 endpoints. Scaling from 800 to 3,000 employees means hiring 3 to 6 additional analysts at $120K to $180K fully loaded, adding $360K to $1.08M in annual cost.
AI SOC changes this equation because triage scales computationally while human judgment scales contextually:
-
AI handles the volume: correlating alerts, suppressing false positives, enriching the 5% of alerts that need human eyes.
-
Analysts handle decisions requiring organizational context and business judgment.
-
Flat-rate pricing scales linearly, not exponentially.
We designed UnderDefense MAXI with 80+ integrations because mid-market growth is messy. When a PE portfolio company acquires a target running a different security stack, that environment plugs into the existing detection fabric within 30 days. No rip-and-replace, no new headcount.
Our vCISO advisory adapts the security roadmap at each growth stage, allowing most scaling clients to maintain 2 to 3 internal staff throughout their growth trajectory.
5. What should I look for when evaluating AI SOC providers for a mid-market organization?
After working with hundreds of mid-market security teams, we’ve distilled the evaluation down to seven non-negotiable checkpoints. If a vendor can’t demonstrate these during a live walkthrough, that’s your first red flag:
-
☐ Vendor-agnostic integration: Works with your existing SIEM, EDR, cloud, and identity tools.
-
☐ True 24/7 monitoring + human response: An analyst who picks up and acts, not just automated alerts.
-
☐ Published, predictable pricing: You can model cost before a sales call.
-
☐ MTTC under 30 minutes with SLA: Contractual, not aspirational.
-
☐ Direct analyst communication via Slack/Teams: ChatOps-driven verification, not a ticketing black hole.
-
☐ Compliance evidence auto-generation: SOC 2, HIPAA, ISO 27001, and PCI DSS artifacts produced automatically.
-
☐ Full deployment in 30 days or less.
Score yourself: 6 to 7 checks = mature candidate; 3 to 5 = critical gaps; 0 to 2 = breach risk. We publish a detailed MDR buyer’s guide that walks through each checkpoint with vendor-specific evidence.
6. Which AI SOC providers support SOC 2, HIPAA, and ISO 27001 compliance automation?
Compliance automation varies dramatically across AI SOC and MDR providers. Most offer detection and response but treat compliance as a separate add-on, leaving mid-market teams to stitch together evidence manually.
Here’s how the leading providers stack up:
-
UnderDefense: ✅ SOC 2, HIPAA, ISO 27001, PCI DSS, GDPR, and CMMC bundled in the core platform. Includes forever-free compliance kits and auto-generated evidence artifacts.
-
eSentire: ✅ Compliance packages available for SOC 2, HIPAA, and PCI DSS.
-
CrowdStrike Falcon Complete: ✅ SOC 2, HIPAA, PCI DSS available. FedRAMP certified.
-
Arctic Wolf: ⚠️ Compliance managed separately from MDR.
-
Expel: ⚠️ Reporting capabilities only; limited compliance automation.
For mid-market companies preparing for enterprise customer audits or pursuing certifications, bundled compliance automation saves $50K to $150K/year compared to purchasing separate GRC tools. We built compliance services directly into MAXI because compliance and detection share the same telemetry, and separating them creates duplicate work and blind spots.
7. How fast can an AI SOC provider deploy for a mid-market company?
Deployment timelines range from minutes to months, depending on architecture and service model:
-
Radiant Security: Minutes (API-based) + days for baseline tuning.
-
Expel: Hours to days (API-first) + weeks for full tuning.
-
Stellar Cyber / Torq: 2 to 4 weeks.
-
UnderDefense: ~30 days for full MDR + compliance automation + first impact report.
-
Arctic Wolf: 4 to 6 weeks.
-
eSentire: 4 to 8 weeks.
-
CrowdStrike: Minutes (agent deployment) + weeks (MDR operationalization).
The nuance matters: “minutes to deploy” often means the agent or API connection is live, not that detection tuning, false positive suppression, and compliance mapping are complete. A provider that deploys in minutes but generates noise for months has a slower effective time-to-value than one that deploys in 30 days with tuned detection from day one.
We target 30-day onboarding inclusive of integration, tuning, and first threat report because that’s the window where mid-market teams need to see measurable impact, specifically 99% alert noise reduction and a documented security posture baseline.
8. Is AI SOC better than building an in-house SOC for a company with 500 to 5,000 employees?
For most mid-market companies in the 500 to 5,000 employee range, an AI SOC is significantly more cost-effective and operationally practical than building in-house.
The numbers tell the story:
-
In-house SOC: $1M to $2M upfront infrastructure + $1.5M+/year for minimum viable 24/7 staffing (8 to 12 FTEs). Time to value: 6 to 12 months.
-
AI SOC + Human Ally: $66K to $180K/year with 0 to 1 internal FTEs required. Time to value: 30 days.
Beyond cost, the operational reality is that in-house SOCs at mid-market scale face chronic challenges: analyst burnout, 2 AM coverage gaps, 3.4-million-person talent shortage turning hiring into a six-month ordeal, and the constant pressure to keep detection logic current against evolving threats.
AI SOC doesn’t eliminate the need for internal security leadership. It eliminates the need to build and operate the 24/7 detection-and-response function internally. The outsourced vs. in-house SOC comparison we published breaks down the economics in detail, including scenarios where in-house makes sense (10,000+ employees with dedicated budget and executive sponsorship).
The post Best AI SOC for Mid-Market: 8 Providers Scored, Priced, Ranked appeared first on UnderDefense.