Q1. What Is an AI SOC Breach Warranty, and Why Should Every Security Leader Care?
An AI SOC breach warranty is a contractual guarantee from your managed detection and response (MDR) provider promising financial reimbursement, typically up to $1 million, if a breach occurs on systems the provider was hired to protect. Over the past three years, CrowdStrike, Sophos, and SentinelOne have each introduced their own versions, riding the wave of AI SOC adoption and increasing buyer skepticism that boils down to one pointed question: if your AI is so good, put money behind it.
The Warranty Arms Race Started as a Marketing Play
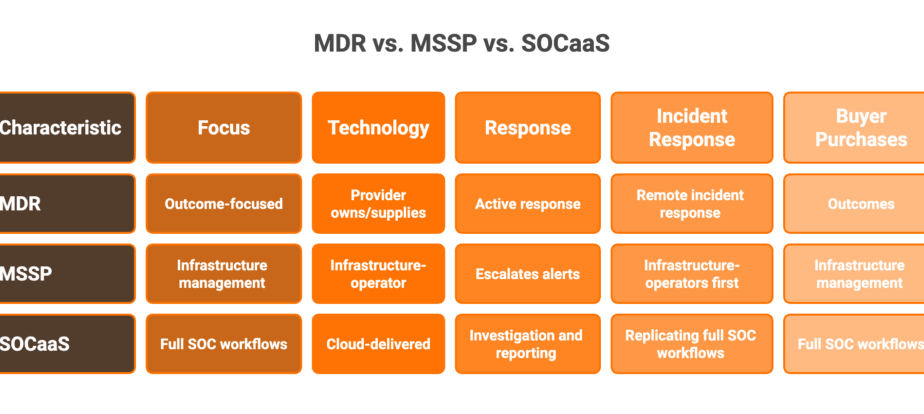
Here’s the operational reality most vendor landing pages won’t tell you: the majority of these warranties are marketing instruments, not genuine financial protection. Traditional MDR providers like Arctic Wolf and ReliaQuest don’t even offer breach warranties. Their detection-only, escalation-only models can’t underwrite the risk of a missed threat because they don’t own the response. They alert you, hand the ticket back, and hope your team handles it at 2 AM.
Vendors that do offer warranties bury exclusions deep enough that payouts are functionally near-zero. And here’s a critical distinction every CISO needs to internalize: a breach warranty is not cyber insurance, and neither is an SLA service credit. These are three entirely different financial instruments with different triggers, different coverage scopes, and different claims processes. Conflating them, which most vendor marketing encourages you to do, is a mistake that leaves you underprotected.
Why AI Changes the Warranty Calculus
An AI SOC that combines autonomous detection with human analyst response fundamentally shifts what a warranty can mean. When the same entity that detects the threat can also verify it with affected users and contain it, revoking credentials, isolating endpoints, and terminating sessions, the provider can stand behind outcomes (breach prevention), not just tool performance (uptime SLAs). This is the difference between “we’ll monitor your alerts” and “we’ll own your security outcomes.”
The architecture that makes this possible is what we at UnderDefense call the “AI SOC + Human Ally” model. Our UnderDefense MAXI platform pairs AI-driven detection, covering 96% of MITRE ATT&CK techniques, with concierge analyst response, delivering a documented 2-minute alert-to-triage SLA and 15-minute escalation for critical incidents. The provider that detects the threat also contains it. No escalation back to your overwhelmed team. No black-box investigation you never see.
✅ Accountability Through Operational Depth, Not Marketing Headlines
That operational depth is what separates warranty credibility from warranty marketing. When your MDR provider can demonstrate a 100% ransomware prevention record across 500+ clients, not in a lab but in production environments with real attack traffic, the warranty conversation changes entirely. It moves from “how much will they pay us after a breach?” to “how likely is a breach in the first place?”
But what do these warranties actually say in the fine print? Let’s break it down vendor by vendor.
Q2. What Does the $1M Breach Warranty Actually Cover, Vendor by Vendor?
The headline is always the same, “$1 million in breach protection,” but the mechanics underneath vary dramatically. Here’s what each major vendor’s warranty actually covers, based on their published legal terms, not their marketing pages.
Side-by-Side Warranty Comparison
| Dimension | CrowdStrike (Falcon Complete) | Sophos (MDR Complete) | SentinelOne | Arctic Wolf |
|---|---|---|---|---|
| Aggregate Cap | $1M (EDR); $2M (EDR + Identity Protection) | $1M per year | Up to $1M | ❌ No breach warranty |
| Per-Device Limit | $2,000/endpoint | $1,000/endpoint | $1,000/endpoint | N/A, SLA credits only |
| Qualifying Tier | Falcon Complete Next-Gen MDR (top tier) | MDR Complete (top tier) | Complete + Vigilance + WatchTower (top tiers) | N/A |
| Waiting Period | Not publicly specified | 60 days from subscription start | Not publicly specified | N/A |
| Covered Expenses | Legal fees, forensic investigation, notification, credit monitoring, PR, and extortion payments | Legal fees, notification, PR, regulatory fines, and ransom (capped at $100K) | Primarily ransomware-specific damages | N/A |
| Key Restriction | All endpoints must run Falcon Complete; breach must occur within protected environment | Account Health Check score must be 100; all endpoints must have agent deployed; 12-month continuous subscription minimum | Products must be “correctly installed and fully operational” on all protected devices | Liability limited to service credits (typically 5–10% of monthly fees) |
What Expenses Are Actually Covered?
CrowdStrike’s warranty covers a relatively broad range of breach response expenses: legal consultation, forensic services, notification costs, credit monitoring, PR communications, and even extortion payments. Their updated Falcon Complete warranty now offers up to $2 million for customers using both EDR and Identity Threat Protection, calculated at $2,000 per impacted endpoint.
Sophos explicitly covers legal fees, notification expenses, public relations costs, regulatory fines, and ransom payments, but caps ransom reimbursement at $100,000 per claim and limits per-device payouts to $1,000. So if you have 50 endpoints, your real maximum is $50,000, not $1 million.
SentinelOne’s warranty historically focused on ransomware-specific damages, reimbursing up to $1,000 per device affected. The full $1M payout would require 1,000 machines to be simultaneously compromised with the latest SentinelOne software running, a scenario that exposes the mathematical reality behind the headline number.
⚠️ Qualifying Conditions Create Real Coverage Gaps
Every vendor requires their most expensive subscription tier. Every vendor mandates that products be “correctly installed and fully operational” across all protected devices. And every vendor includes broad language around “customer negligence” that gives them significant latitude to deny claims. Failing any single qualifying condition voids the entire warranty.
Arctic Wolf is notably absent from the warranty conversation entirely. Their liability is limited to SLA service credits, which in practice amounts to 5–10% of monthly fees. No breach warranty. No financial backstop.
How UnderDefense Approaches Accountability
We approach this differently. Instead of marketing a headline warranty figure with exclusions designed to prevent payouts, we deliver operational outcomes: 2-minute alert-to-triage, direct analyst containment, and a documented 100% ransomware prevention record across 500+ clients. These reduce the probability of ever needing a warranty payout. The best warranty is never needing one. Learn more about our incident protection warranty.
Q3. Where Does the $1M Coverage Apply, and Where Does the Fine Print Kill It?
Before trusting any $1M breach warranty headline, run this 10-point audit. Each unchecked item represents a scenario where the warranty will not pay out, regardless of the number on the marketing page.
🔍 The 10-Point Warranty Due Diligence Checklist
- ☐ Activation delay: Does coverage start immediately, or is there a waiting period? Sophos imposes 60 days of zero coverage from subscription start.
- ☐ Aggregate vs. per-incident: Is the $1M figure aggregate (per year) or per incident? Most vendors cap it annually.
- ☐ Per-device math: What’s the per-device cap vs. the headline aggregate? SentinelOne = $1K/endpoint, meaning 50 endpoints = $50K max. Sophos = $1K/endpoint with the same math.
- ☐ Tier requirement: Are you required to purchase the vendor’s most expensive subscription tier? (Answer: always yes.)
- ☐ Attack surface coverage: Does the warranty cover cloud-native attacks, SaaS compromise, and identity-based attacks, or only endpoint incidents? Most cover endpoints only.
- ☐ Nation-state exclusions: Are state-sponsored cyberattacks explicitly excluded? Sophos excludes attacks “reasonably believed to be related to state sponsored cyberattacks.”
- ☐ “Customer negligence” scope: How broadly is negligence defined? Sophos requires patching Critical CVEs (8.5+) within 7 days and High (7–8.5) within 30 days.
- ☐ Consequential damages: Does the warranty cover lost revenue, reputational harm, and regulatory fines, or only direct response expenses? Sophos explicitly disclaims “lost profits, lost business opportunities, business interruption.”
- ☐ Mandatory arbitration: Is there a mandatory arbitration clause preventing litigation? Sophos requires LCIA arbitration in London.
- ☐ Has the vendor EVER paid out? Sophos has publicly stated their warranty has never been triggered. If a warranty exists for 3+ years and has never paid a single claim, there are two explanations: either the product is perfect, or the exclusions are perfect at preventing claims.
📊 Score Interpretation
| Score | Meaning |
|---|---|
| ✅ 8–10 checked | Your warranty has genuine teeth |
| ⚠️ 4–7 checked | Significant exclusion gaps. You’re likely partially self-insured despite the headline number |
| ❌ 0–3 checked | The warranty is marketing, not protection |
The “Never Paid Out” Reality
This is the angle nobody in the industry wants to discuss. If a warranty has existed for multiple years and never paid a single claim, smart buyers should bet on the second explanation: the exclusions are perfect at preventing claims. The per-device caps alone make it mathematically improbable that most organizations will ever receive meaningful payouts. A 200-endpoint company with Sophos MDR Complete has a theoretical maximum of $200,000, not $1 million. And that’s before the 60-day waiting period, the health-score requirement, the patching mandates, and the negligence carve-outs.
How UnderDefense Eliminates Coverage Gaps Architecturally
Our vendor-agnostic architecture, with 250+ integrations spanning endpoint, cloud, identity, and SaaS, means threat detection isn’t limited to one attack surface. This eliminates the coverage-gap exclusion that makes endpoint-only warranties unreliable. When your provider monitors the full kill chain, the question shifts from “Does the warranty cover this attack type?” to “Was the attack prevented in the first place?”
Published SLAs (2-minute alert-to-triage and 15-minute escalation for critical incidents) create documented accountability, not vague “best effort” language. And our concierge analysts don’t just escalate. They contain, communicating directly with affected users to revoke credentials, isolate endpoints, and terminate sessions.
“The biggest win for me was getting actual control over our security alerts. Before the guys from UD stepped in, we were getting bombarded with alerts from all our security tools. Their team cleaned up our configurations and got the noise under control within the first week.”
— Verified User, Marketing and Advertising UnderDefense G2 – Verified Review
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., Enterprise UnderDefense G2 – Verified Review
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense G2 – Verified Review
Q4. Who Is Legally Liable When Your AI SOC Provider Misses a Breach?
When an AI SOC misses ransomware lateral movement or a credential stuffing attack that escalates to a full breach, the first question every security leader asks is: who is responsible? The answer depends entirely on your contract’s limitation-of-liability clause, and most vendors have written those clauses to protect themselves, not you.
The Three Legal Pathways After a Missed Detection
There are three avenues for recourse when your AI SOC fails: (a) contractual breach, did the vendor violate specific performance obligations in the agreement? (b) negligence/tort, did the vendor fail to exercise a reasonable standard of care? (c) product liability, was the AI system itself defective in its design or training? Each pathway has different evidentiary burdens, different damage calculations, and, critically, different outcomes depending on whether your contract’s limitation-of-liability clause preempts the claim entirely.
❌ Standard Contracts Are Built to Protect the Vendor
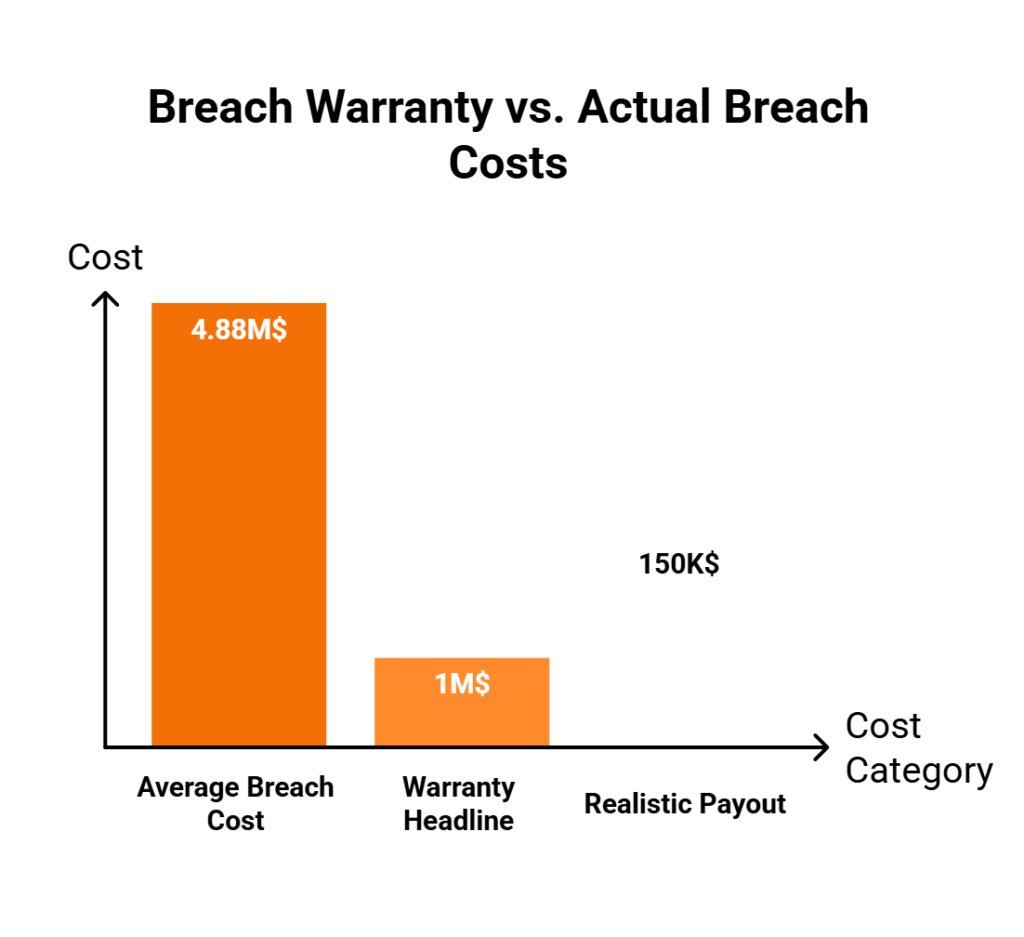
Standard MDR and AI SOC contracts include liability caps typically limited to fees paid in the prior 12 months, blanket exclusions for consequential damages, and carve-outs for “force majeure” and “acts beyond reasonable control.” In practice, this means a vendor whose AI missed a breach costing $4.88 million (IBM’s 2024 average breach cost) may owe you $150K–$200K in subscription fees at most.
SLA penalty mechanisms across the industry are toothless. Service credits amount to 5–10% of monthly fees. Some contracts, Arctic Wolf and ReliaQuest among them, don’t even offer a breach warranty; their entire liability is limited to those service credits. And as one Gartner-verified reviewer noted about Arctic Wolf:
“Lack of true remediation in the response, costing us significantly in resources and introducing risks in security.”
— VP of Technology, Services Arctic Wolf – Gartner Verified Review
⚠️ The AI-Specific Liability Gap
Here’s what keeps me up at night, and what I think every security leader should be asking their legal team about: when a human analyst misses a threat, negligence frameworks are well-established, covering duty of care, standard of care, and proximate cause. When an AI model fails due to model drift, training data gaps, adversarial evasion, or novel attack techniques, liability is legally murky.
The EU AI Act (effective 2025–2026) and evolving US state-level frameworks are beginning to address AI system liability, but most AI SOC contracts haven’t caught up. They were written for human-managed services and don’t account for AI-specific failure modes. This creates a novel risk category where buyers have limited legal recourse for AI-specific failures. The contract says “we’ll use commercially reasonable efforts” and the AI Act says “high-risk AI systems require specific accountability,” and nobody has reconciled the two in the MDR context yet.
✅ How the “AI SOC + Human Ally” Model Creates Dual Accountability
This is precisely why we built the dual-accountability architecture at UnderDefense. AI handles detection at scale, with 96% MITRE ATT&CK coverage, processing telemetry across 250+ integrated tools. Human analysts verify, contextualize, and respond, with a documented 2-minute alert-to-triage SLA and 15-minute escalation for critical incidents. This hybrid approach fundamentally reduces “missed breach” scenarios because each layer catches what the other misses.
Our concierge analysts don’t just escalate. They contain and remediate: credential revocation, endpoint isolation, and session termination, closing the gap between detection failure and breach impact. When you combine ChatOps-driven user verification (confirming directly with affected users whether a login was legitimate) with AI-driven anomaly detection, you get an accountability model that doesn’t depend on airtight contract language to protect you. It depends on operational outcomes you can observe and audit.
As one CISO-level reviewer from a $3B+ manufacturer noted about the limitations of the alternative:
“Log collectors show working, however when asked to provide logs for an investigation no logs could be provided. Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing Arctic Wolf – Gartner Verified Review
The contrast is clear: the best legal protection isn’t a better limitation-of-liability clause but an operational model where the provider who detects the threat also contains it, with human judgment backing AI speed, so the liability question becomes academic because the breach never materializes.
Q5. What Happens to Your Security Data When You Leave an AI SOC Provider?
Picture this scenario: you’ve spent 18 months with an AI SOC provider. Your team has tuned 200+ custom detection rules, built compliance dashboards for SOC 2 audits, and accumulated enriched threat intelligence alongside baseline behavioral models tailored to your environment. Now you want to switch, maybe the warranty terms don’t hold up, maybe response times degraded, maybe pricing changed at renewal.
❌ The Vendor’s Exit Policy Hits You Like a Wall
The vendor tells you: “Your data will be deleted 30 days after contract termination. Custom detection logic is proprietary to our platform. Compliance reports cannot be exported in a portable format.” Suddenly the switching cost isn’t the subscription but 18 months of institutional security knowledge locked inside a proprietary platform.
This problem isn’t accidental. Most AI SOC and MDR vendors use proprietary data formats, closed detection rule languages, and non-portable compliance frameworks as a retention strategy. A former CISO I spoke with on a recent webinar put it perfectly: when he switched SIEM vendors, all the business logic, correlation rules, automation rules, and custom integrations, stayed behind. He had to start the tuning process from scratch.
⚠️ The Hidden Costs of Switching
The financial and operational toll of a vendor exit is staggering when you account for what’s actually lost:
- Rebuilding detection rules from scratch: 2–4 months of analyst time
- Gap in 24/7 coverage during migration: weeks to months of degraded protection
- Lost compliance evidence trail: audit documentation trapped in non-exportable formats
- AI model re-tuning: 4–6 weeks of false positive floods while the new system learns your environment’s baseline
- Analyst re-familiarization: your new SOC team has zero context on your VIP users, critical assets, and organizational quirks
Each item on that list represents a window of vulnerability that attackers can exploit. And that’s the real danger of vendor lock-in in cybersecurity: your security posture actively degrades during any transition.
✅ How UnderDefense Keeps Your Data Where It Belongs
We built UnderDefense’s architecture around a principle that every mature CISO understands: your security data should live across YOUR existing tools, your SIEM, your EDR, and your cloud platform, not locked inside a proprietary layer. Detection rules are built on standard formats compatible with your existing tooling. Compliance evidence is generated within your own environment. If you leave, your security posture stays intact because we enhance your stack; we don’t replace it.
The Security Provider Switch Checklist provides a step-by-step guide for evaluating exit clauses before you sign.
“UnderDefense has changed our approach to cybersecurity. At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it. Now, with their security monitoring and incident response we know our endpoints are well-protected.”
— Yaroslava K., IT Project Manager UnderDefense G2 – Verified Review
“We received little value from ArcticWolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team. As an MSP, this is a horrible way to do business for us.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“The platform works really well with our other security tools, which makes things much simpler. And we really appreciate that we can customize the threat detection to focus on our specific needs.”
— Serhii B., Chief Information Security Officer UnderDefense G2 – Verified Review
The difference between vendor-agnostic and vendor-locked MDR is the difference between renting a security team and being held hostage by one.
Q6. How Does a Breach Warranty Compare to Cyber Insurance, and What’s the Right Layered Protection Strategy?
Security leaders frequently conflate breach warranties with cyber insurance, treating them as interchangeable financial backstops. They are fundamentally different instruments with different triggers, different coverage scopes, and different failure modes.
Breach Warranty vs. Cyber Insurance
| Dimension | Breach Warranty | Cyber Insurance |
|---|---|---|
| Issuer | Cybersecurity vendor (CrowdStrike, Sophos, etc.) | Insurance company (AIG, Zurich, Chubb, etc.) |
| Trigger | Breach occurs despite vendor’s product/service | Any qualifying cyber incident, regardless of which product failed |
| Covered Expenses | Direct response costs (forensics, notification, and PR) | Business interruption, regulatory fines, legal liability, and third-party claims |
| Typical Limit | $1M (with per-device caps) | $1M–$10M+ |
| Cost | Bundled with top-tier subscription | Separate premium ($5K–$100K+/year depending on coverage) |
| Exclusions | Narrow but strict: product must be “correctly installed,” no negligence | Broader coverage but excludes “acts of war,” nation-state attacks, and pre-existing conditions |
| Claims Process | Vendor-administered (inherent conflict of interest) | Third-party insurer with independent adjusters |
⚠️ Why Neither Is Sufficient Alone
A breach warranty covers the vendor-failure scenario but explicitly excludes insider threats, social engineering, supply chain attacks, and incidents originating outside the monitored perimeter. Cyber insurance covers broader scenarios but has security posture prerequisites: you must demonstrate reasonable controls. Claims processes take months. Policies increasingly exclude “acts of war” and nation-state activity.
IBM’s 2024 Cost of a Data Breach Report found the global average breach cost hit a record $4.88 million. A $1M warranty with per-device caps that realistically pays out $50K–$200K covers roughly 1–4% of total breach costs. Even a $1M cyber insurance policy falls short of covering the average incident.
💰 The 4-Layer Financial Protection Framework
- Operational Prevention — Choose an AI SOC with genuine operational accountability: detection + response + containment, not just alerts. This is where you reduce breach probability to near-zero.
- Contract Negotiation — Negotiate liability caps that match warranty promises, consequential damages carve-outs for security failures, and defined breach notification timelines aligned with GDPR (72 hours), HIPAA (60 days), and CIRCIA (72 hours).
- Vendor Warranty — Ensure qualifying conditions are met, exclusions are understood, and the claims process doesn’t require the vendor to adjudicate its own failure.
- Cyber Insurance Backstop — Layer a standalone cyber policy to cover consequential damages, regulatory fines, and attack vectors the warranty doesn’t reach.
UnderDefense’s “AI SOC + Human Ally” model addresses Layer 1 with a 100% ransomware prevention record across 500+ clients, while transparent SLAs, vendor-agnostic architecture, and published pricing ($11–15/endpoint/month) make Layers 2–3 straightforward to negotiate. The best financial protection strategy makes Layers 3–4 a backstop you never need, not a primary plan.
Q7. How Should You Negotiate AI SOC Contract Terms Before You Sign?
Negotiating an AI SOC contract isn’t like buying SaaS. The stakes include breach liability, data sovereignty, regulatory compliance, and operational continuity. Most security leaders focus on price per endpoint and detection capabilities but miss the fine print that determines what happens when things go wrong.
❌ The Wrong Way to Negotiate
- Accepting the vendor’s standard MSA without redlining liability caps
- Assuming the breach warranty IS the contractual liability (it’s usually a separate, lower-tier obligation)
- Ignoring data portability provisions until exit
- Failing to define “breach notification” timelines that align with YOUR regulatory obligations: 72 hours for GDPR, state-specific timelines in the US, and 72 hours for CIRCIA
- Not defining what constitutes a “missed breach” vs. an “undetectable zero-day”
✅ The 7-Clause Negotiation Framework
Every AI SOC contract should be scored on these seven clauses:
| # | Clause | What to Negotiate | Red Flag |
|---|---|---|---|
| 1 | Liability Cap Alignment | Ensure the contractual liability cap matches or exceeds the warranty promise, not just 12 months of fees | Cap limited to subscription fees only |
| 2 | Consequential Damages Carve-Out | Carve security failures out of the standard consequential damages exclusion | Blanket consequential damages waiver with no exceptions |
| 3 | Data Return/Destruction | Define exactly what data is returned, in what format, and within what timeframe post-termination | “Data deleted 30 days after termination” with no export option |
| 4 | Breach Notification Timeline | Align with GDPR (72h), US state laws, and CIRCIA (72h) requirements | No defined notification timeline or “commercially reasonable efforts” language |
| 5 | Warranty Trigger Definition | Precisely define what constitutes a “missed breach” vs. an “undetectable threat” | Vendor retains sole discretion to determine if warranty applies |
| 6 | Transition Assistance | Require active migration support for a defined period post-termination | No offboarding obligations |
| 7 | SLA Penalties with Teeth | Negotiate fee reductions or termination-for-cause triggers tied to MTTD failures | Service credits of 5–10% of monthly fees |
📊 How to Score Your Vendor
Score each vendor 0–2 on these seven criteria. A score of 10+ represents genuine contractual partnership. Below 7 means the contract protects the vendor, not you. Hand this scoring framework to your legal team alongside the vendor’s MSA before the first negotiation call.
UnderDefense scoring: Published SLAs (2-minute alert-to-triage and 15-minute escalation for critical incidents) = 2, Vendor-agnostic data portability = 2, Transparent $11–15/endpoint pricing = 2, Compliance kits included = 2, 30-day symmetric onboarding/offboarding = 2, Concierge analyst access = 2, ChatOps-driven response = 2. Total: 14/14.
Download the full 7-Clause AI SOC Contract Negotiation Checklist to bring to your next vendor call.
Q8. What Does a Worst-Case Breach Scenario Actually Look Like Under These Warranties?
Theory is useful. Seeing how vendor warranties actually perform under fire is better. Here’s a realistic breach scenario, step by step, stress-tested against each major vendor’s warranty terms.
⏰ The Breach Timeline
- Monday, 1:47 AM — A credential stuffing attack compromises an employee’s Azure AD account using credentials from a third-party data dump.
- 1:52 AM — Attacker accesses SharePoint and begins exfiltrating customer records.
- 2:14 AM — Lateral movement via compromised identity reaches the finance team’s shared drive.
- 2:38 AM — Ransomware deployed across 150 endpoints via Group Policy.
- 6:00 AM — Your team discovers the breach when employees report encrypted machines.
Total estimated breach cost: $2.8M (notification, forensics, legal fees, regulatory fines, business interruption, and PR/crisis management). Your AI SOC was monitoring the entire time. It missed the initial credential compromise because the login came from a recognized geography.
Why Each Vendor’s AI Likely Misses This
Identity-based attacks that don’t trigger endpoint alerts are the blind spot of endpoint-focused AI SOC providers. The Azure AD login looked normal: recognized geography, known device type. The SharePoint access was within policy boundaries. The lateral movement used legitimate credentials. The ransomware deployment at 2:38 AM was the first endpoint-level indicator, but by then, 40,000 customer records were already exfiltrated.
💸 Warranty Stress-Test: Vendor by Vendor
| Vendor | Coverage Calculation | Likely Payout | Recovery Rate |
|---|---|---|---|
| Sophos | $1K × 150 endpoints = $150K max. If customer < 60 days, $0. Identity-based vector likely outside endpoint scope. | $0–$150K | 0–5.4% |
| SentinelOne | $1K × 150 endpoints = $150K max. Must prove all 150 endpoints fully operational and updated. | $0–$150K | 0–5.4% |
| CrowdStrike | Requires Falcon Complete tier. Identity-based vector may fall outside definition. All qualifying conditions must be met across entire environment. | Up to $1M (if ALL conditions met, unlikely in mixed environments) | 0–35.7% |
| Arctic Wolf | ❌ No breach warranty. SLA credits only. | ~$0 | 0% |
Against a $2.8M breach, even the best-case vendor warranty scenario recovers 35 cents on the dollar, and that assumes every qualifying condition is met, which rarely happens in real-world mixed environments.
✅ How UnderDefense Would Handle This Differently
UnderDefense MAXI monitors across endpoint + cloud + identity (Azure AD) + SaaS (SharePoint), the full kill chain in this scenario. At 1:47 AM, the anomalous Azure AD login triggers an identity-based detection. Concierge analysts reach the employee directly via Slack/Teams: “Did you just log into Azure AD from [location]?”
No response at 1:47 AM + anomalous behavior pattern = confirmed suspicious. Immediate response: compromised credentials revoked, active sessions terminated, Azure AD account locked, and endpoints pre-isolated. The attack is contained at 1:52 AM, before SharePoint exfiltration begins.
Total breach cost: $0. Total warranty claim needed: $0.
From $2.8M in breach damages with a $150K warranty payout (5.4% recovery), to a contained incident resolved with a 1:52 AM Slack message and a morning incident summary. That’s the difference between warranty marketing and operational prevention. The best warranty isn’t the one with the biggest number but the one you never need to file.
Q9. Which AI SOC Providers Actually Back Their Detection With Financial Accountability?
The AI SOC providers that back their detection capabilities with meaningful financial accountability include UnderDefense (operational outcome guarantees + transparent SLAs + $2M breach prevention guarantee), CrowdStrike (Falcon Complete $1M breach prevention warranty), Sophos (MDR Complete $1M breach protection warranty), and SentinelOne (endpoint-level ransomware response warranty), each with fundamentally different accountability architectures and real-world coverage scope.
⚠️ Why Financial Accountability Has Evolved
Financial accountability in AI SOC has moved well beyond simple breach warranties. A $1M headline number means very little if the fine print restricts coverage to endpoint-only incidents while the fastest-growing attack vectors, identity compromise, cloud misconfiguration, and SaaS account takeover, fall outside the warranty scope entirely. The real differentiators are now warranty scope (endpoint-only vs. full-stack), qualifying conditions (how many ways to void it), response architecture (detection-only vs. detection + containment), and whether the provider’s operational model is designed to prevent the warranty trigger rather than just pay after the fact.
✅ What Separates Genuine Accountability From Marketing Warranties
- Coverage scope — Endpoint-only protection vs. endpoint + cloud + identity + SaaS. CrowdStrike and SentinelOne warranties cover endpoint breaches; identity-based attacks that bypass endpoints often fall outside coverage.
- Per-device caps vs. true aggregate coverage — SentinelOne caps payouts at $1,000/endpoint affected; Sophos caps at $1,000/breached machine. Both aggregate to $1M, but the per-device structure matters when multiple endpoints are hit simultaneously.
- Qualifying conditions — Sophos requires a 60-day waiting period before warranty activation, mandates patching critical vulnerabilities within 7 days, and excludes breaches originating from unprotected endpoints on the network.
- Response capability — Can the vendor contain and remediate, or only detect and notify? Providers without full containment authority may detect the breach but lack the operational mandate to stop it before warranty thresholds are breached.
- Operational track record — Documented prevention rates vs. warranty payout history. UnderDefense maintains a 100% ransomware prevention record across 500+ MDR clients over 6 years. The most reliable warranty is the one that never needs to trigger.
🔍 Where Each Provider Fits Best
Each provider excels in different scenarios. CrowdStrike’s warranty works best for Falcon-native environments where endpoints represent the primary attack surface. Sophos makes sense for organizations wanting bundled warranty with managed response across Windows and macOS devices. SentinelOne fits endpoint-heavy deployments that prioritize ransomware-specific coverage. And UnderDefense serves teams protecting existing multi-vendor stacks with vendor-agnostic coverage, a $2M breach prevention guarantee, transparent SLAs (2-minute alert-to-triage and 15-minute escalation for critical incidents), and an architecture where every investigative step is observable and auditable, so your security operation prevents the breach rather than relying on a post-breach payout.
The right choice depends on your current architecture, budget, and which warranty conditions you can realistically maintain across your environment.
This analysis is based on documented warranty terms, G2 Spring 2025 rankings, published pricing, and operational outcomes across 500+ MDR deployments.
Q10. The AI SOC Warranty Bottom Line: What Must Your Organization Do Right Now?
A $1M breach warranty headline means nothing if the fine print voids coverage for the exact attack scenarios growing fastest in 2025–2026: identity-based attacks, cloud misconfigurations, and supply chain compromises that bypass endpoint-only warranties entirely. Here are the 5 actions that actually protect your organization.
⏰ Your 5 Immediate Actions
- Audit your current AI SOC contract against the 10-point exclusion checklist from Q3. Score below 5 means you’re effectively self-insured, regardless of what the warranty headline promises. Pay special attention to identity attack exclusions, cloud coverage gaps, and per-device payout caps that reduce aggregate coverage to a fraction of the headline number.
- Negotiate the 7 critical contract clauses from Q7 before your next renewal, especially liability cap alignment and consequential damages carve-outs. If your vendor’s total liability is capped at 12 months of fees paid, a $1M warranty may actually cap at $150K for a mid-market deployment. Get that language tightened now, not after a breach.
- Layer a standalone cyber insurance policy to cover the gaps your warranty explicitly excludes. No AI SOC warranty covers regulatory fines, identity-based attack chains, supply chain compromise, or business interruption beyond direct response expenses. Cyber insurance isn’t a replacement for good security but a backstop for the scenarios warranties were designed to avoid.
- Evaluate vendor-agnostic AI SOC providers that monitor the full kill chain, endpoint + cloud + identity + SaaS, not just endpoints. Warranties scoped to endpoints miss the attack vectors responsible for the majority of modern breaches. If your provider can’t see identity compromise or cloud misconfiguration, the warranty gap is by design.
- Document a data portability exit plan NOW, before you need it. Define what data you own, what format it exports in, and what timeline applies post-termination. Vendor lock-in isn’t just a technology risk but a warranty risk, because switching providers mid-contract often voids coverage entirely. Use the Security Provider Switch Checklist to get started.
✅ How UnderDefense Makes This Easier
We built our AI SOC + Human Ally model to make every item on this list straightforward: vendor-agnostic coverage across 250+ tools, transparent SLAs with a documented 2-minute alert-to-triage and 15-minute escalation for critical incidents, published pricing ($11–15/endpoint/month), compliance automation included in every MDR engagement, and an architecture designed so exiting is as painless as onboarding. Your data stays in your SIEM; we never force vendor lock.
⭐ The Proof That Prevention Beats Payout
500+ MDR clients. Zero ransomware cases in 6 years. 2-minute alert-to-triage SLA. 96% MITRE ATT&CK coverage. 830% ROI over 3 years. Because the best financial protection isn’t a warranty you hope never triggers but a security operation that ensures it never needs to.
“It’s reassuring to know they’re always watching for threats, and it doesn’t cost a fortune. They catch and stop problems quickly, which is a huge relief.”
— Serhii B., Chief Information Security Officer UnderDefense G2 – Verified Review
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., Enterprise (1000+ emp.) UnderDefense G2 – Verified Review
“With their proactive monitoring and rapid incident response capabilities, we can detect and mitigate security threats.”
— Alexey S., CEO UnderDefense G2 – Verified Review
1. What does a $1M AI SOC breach warranty actually cover in practice?
Most $1M AI SOC breach warranties carry per-device caps that dramatically reduce real-world payouts. For example, SentinelOne and Sophos both cap at $1,000 per affected endpoint, which means a 150-endpoint ransomware event maxes out at $150K, not $1M. Coverage typically includes direct incident response costs such as forensics, breach notification, and crisis PR, but excludes business interruption, regulatory fines, legal liability, and third-party claims.
We’ve seen these warranties further limited by qualifying conditions: Sophos requires a 60-day waiting period before activation and mandates critical vulnerability patching within 7 days. CrowdStrike’s warranty requires the Falcon Complete tier and demands 100% deployment across the environment. In mixed or hybrid environments, meeting every condition is rare.
The critical gap is scope. Most warranties cover endpoint-only incidents while identity-based attacks, cloud misconfigurations, and SaaS account takeovers fall outside coverage entirely. At UnderDefense, we address this with vendor-agnostic, full-stack monitoring across endpoint, cloud, identity, and SaaS, paired with a $2M breach prevention guarantee that reflects the breadth of our detection architecture.
2. What are the most common AI SOC warranty exclusions that void coverage?
AI SOC warranty fine print typically contains exclusions that void coverage for the exact attack scenarios growing fastest today. The most common exclusions include:
- Identity-based attacks (credential stuffing, Azure AD compromise) that bypass endpoint monitoring
- Cloud misconfigurations and SaaS account takeovers outside the vendor’s monitored scope
- Supply chain compromises originating from third-party software
- Breaches on endpoints where the vendor’s agent was not deployed or not fully updated
- Incidents occurring within the first 30–60 days of service activation
- Customer negligence, including failure to patch critical vulnerabilities within vendor-specified timeframes
The vendor typically retains sole discretion over whether the warranty applies, creating an inherent conflict of interest. We built UnderDefense’s managed detection and response model around operational prevention rather than post-breach payouts, maintaining a 100% ransomware prevention record across 500+ clients over 6 years.
3. Who is liable when an AI SOC provider misses a breach?
Liability for a missed breach depends on the contract language, not the warranty headline. Most AI SOC vendors cap total contractual liability at 12 months of subscription fees paid, which for a mid-market deployment might equal $150K–$300K, far below the $4.88M global average breach cost reported by IBM.
The breach warranty and contractual liability are typically separate obligations. The warranty covers a narrow set of direct response costs under strict qualifying conditions. The MSA’s liability cap governs everything else, and most include blanket consequential damages waivers that exclude lost revenue, regulatory fines, and reputational harm.
The key question is whether “missed breach” vs. “undetectable zero-day” is defined in the contract. If the vendor retains sole discretion to make this determination, the warranty becomes functionally unenforceable. We recommend negotiating the 7-clause contract framework that separates warranty triggers from vendor self-adjudication.
4. How does a breach warranty compare to cyber insurance for security protection?
Breach warranties and cyber insurance are fundamentally different instruments. A breach warranty is issued by the cybersecurity vendor, triggered only when a breach occurs despite their specific product or service, and limited to direct response costs like forensics and notification. Cyber insurance is issued by an insurance company, covers any qualifying cyber incident regardless of which product failed, and extends to business interruption, regulatory fines, legal liability, and third-party claims.
Neither is sufficient alone. A warranty covers the vendor-failure scenario but excludes insider threats, social engineering, and supply chain attacks. Cyber insurance covers broader scenarios but requires demonstrated security controls and has lengthy claims processes.
The optimal strategy layers four components: operational prevention through a capable AI SOC platform, strong contract negotiation, the vendor warranty as a secondary safeguard, and a standalone cyber insurance policy to cover gaps the warranty explicitly excludes.
5. What happens to your security data when you leave an AI SOC provider?
When you exit most AI SOC providers, your security data faces a harsh reality: custom detection rules are proprietary to the platform, compliance reports cannot be exported in portable formats, and data is typically deleted 30 days after contract termination with no export option. This means 12–18 months of institutional security knowledge, including tuned correlation rules, behavioral baselines, and compliance evidence trails, gets locked inside a platform you no longer access.
The operational cost of switching includes 2–4 months rebuilding detection rules, weeks of degraded 24/7 coverage during migration, 4–6 weeks of false positive floods while the new system learns your baseline, and lost audit documentation. Each item represents a window of vulnerability attackers can exploit.
We designed UnderDefense’s architecture so your security data lives across your existing tools, your SIEM, EDR, and cloud platforms, not inside a proprietary layer. If you leave, your security posture stays intact. The Security Provider Switch Checklist helps evaluate exit clauses before signing.
6. How should you negotiate AI SOC contract terms to maximize protection?
Negotiating an AI SOC contract requires focusing on seven critical clauses beyond price and detection capabilities. These include: liability cap alignment (ensuring contractual liability matches or exceeds the warranty promise), consequential damages carve-outs for security failures, data return and destruction terms with defined formats and timelines, breach notification timelines aligned with GDPR (72 hours), HIPAA (60 days), and CIRCIA (72 hours), warranty trigger definitions that prevent vendor self-adjudication, transition assistance obligations, and SLA penalties with termination-for-cause triggers.
Score each vendor 0–2 on these seven criteria. A score of 10+ represents genuine contractual partnership. Below 7 means the contract protects the vendor, not you.
UnderDefense scores 14/14 on this framework with published SLAs (2-minute alert-to-triage and 15-minute escalation for critical incidents), transparent pricing ($11–15/endpoint/month), and 30-day symmetric onboarding and offboarding. Download the full 7-Clause AI SOC Contract Negotiation Checklist for your next vendor call.
7. What does a worst-case breach scenario look like under AI SOC warranty terms?
In a realistic worst-case scenario, a credential stuffing attack compromises an Azure AD account at 1:47 AM, the attacker exfiltrates 40,000 customer records via SharePoint by 2:14 AM, and ransomware deploys across 150 endpoints by 2:38 AM. The team discovers the breach at 6:00 AM. Total estimated cost: $2.8M.
Against this scenario, endpoint-focused warranties deliver minimal recovery. Sophos and SentinelOne each cap at $150K (150 endpoints × $1K). CrowdStrike could pay up to $1M if every qualifying condition is met, which is unlikely in mixed environments. Arctic Wolf offers no breach warranty at all. Even the best case recovers 35 cents on the dollar.
UnderDefense’s full-stack detection across endpoint, cloud, identity, and SaaS would catch the anomalous Azure AD login at 1:47 AM, with concierge analysts containing the attack before exfiltration begins, resulting in $0 breach cost and $0 warranty claims needed.
8. Which AI SOC providers offer meaningful financial accountability for missed threats?
Four major providers back detection with financial accountability, but each has fundamentally different architectures. CrowdStrike offers a $1M breach prevention warranty through Falcon Complete, scoped primarily to endpoint breaches. Sophos provides a $1M breach protection warranty through MDR Complete with a 60-day activation waiting period and per-device caps of $1,000. SentinelOne offers an endpoint-level ransomware warranty capped at $1,000 per affected device. UnderDefense provides a $2M breach prevention guarantee with vendor-agnostic, full-stack coverage across endpoint, cloud, identity, and SaaS.
The key differentiators are warranty scope (endpoint-only vs. full-stack), qualifying conditions (how many ways to void coverage), and whether the provider’s operational model prevents the warranty trigger rather than paying after the fact.
We maintain a 100% ransomware prevention record across 500+ MDR clients over 6 years, because the most reliable warranty is the one that never needs to trigger. The right choice depends on your current architecture, budget, and which warranty conditions you can realistically maintain.
The post AI SOC Breach Warranty Guide: What Financial Protection Providers Actually Offer? appeared first on UnderDefense.