Q1. Why Does the Alphabet Soup of Security Models, AI SOC, MDR, MSSP, SOAR, XDR, Still Confuse Even Experienced CISOs?
Here’s a reality most vendors won’t admit: the security industry has an acronym addiction, and it’s costing you time, money, and posture. AI SOC, MDR, MSSP, SOAR, XDR, SIEM, EDR, every vendor claims their model replaces the others, yet breaches keep climbing. Proofpoint’s 2025 Voice of the CISO report found that 76% of CISOs feel at risk of a material cyberattack in the next 12 months, and 58% say they’re unprepared to respond. Meanwhile, a 2025 survey of over 1,000 IT and security professionals found that 49% cite overlapping tools as their top challenge, and 41% link poor integrations directly to security risk. That’s not a technology problem but a decision crisis driven by a fragmented landscape where nobody agrees on definitions.
The Vendor Marketing Trap
Part of the confusion is self-inflicted by the industry. MDR providers rebrand as “AI SOC.” MSSPs slap “next-gen MDR” on their marketing. SOAR vendors add “agentic” to every slide deck. The result? Decision-makers can’t compare apples to apples. When a CISO asks three vendors what “MDR” means, they get three different answers: one delivers alert-only monitoring, another bundles EDR with outsourced triage, and the third claims full AI-driven investigation. This definitional chaos hits hardest at the alert triage layer: the 2025 SANS Detection & Response Survey found that 73% of organizations list false positives as their number one detection challenge. Microsoft and Omdia’s 2026 research puts it bluntly, 42% of alerts go entirely uninvestigated. That’s not noise. That’s exposure.
The Agentic AI Inflection Point
What’s different now is that agentic AI creates a genuine architectural shift, not another marketing rebrand. Unlike SOAR’s static playbooks (which break on every API change), agentic systems reason dynamically across telemetry sources. They correlate context, adapt investigation paths in real time, and reach explainable conclusions without someone manually authoring a workflow for every scenario. Early data from SOC platforms using agentic AI reports autonomous resolution of 92% of Tier-1 alerts, with MTTR reductions of up to 90%. That’s not a marginal improvement but a fundamentally different operating model. But here’s the honest caveat: these numbers hold only when the underlying telemetry is clean and the deployment matches your environment. AI doesn’t fix bad data or unclear processes.
What This Article Gives You
This article is designed to cut through the fog. Here’s what you’ll walk away with:
- Crisp, jargon-free definitions of all five models (AI SOC, MDR, MSSP, SOAR, and XDR)
- A head-to-head comparison table with cost anchors, the single artifact no competing article currently offers
- Where XDR actually fits (hint: it’s not competing with AI SOC)
- A before/after workflow comparison of SOAR vs. agentic AI
- Honest positioning on when each model is the right call, and when it isn’t
No vendor lock-in pitch. No black-box claims. Just a vendor-neutral framework built from operational experience across hundreds of security environments.
⚠️ One Stat to Anchor Your Reading
AI-driven SOCs auto-resolve 92% of Tier-1 alerts and cut response times by up to 90%, but only when deployed for the right use cases, with clean telemetry and human oversight in the loop. This article helps you determine if yours is one of them.
Q2. What Exactly Are AI SOC, MDR, MSSP, SOAR, and XDR, and How Do Their Architectures Differ?
Before you can choose the right model, you need to strip away the marketing and understand what each one actually does, and what it doesn’t. Too many comparison articles blur these lines. Let me fix that.
Model Definitions
1. AI SOC (AI-Powered Security Operations Center)
An AI-native platform that automates alert triage, investigation, and response using agentic reasoning, dynamically correlating data across tools without pre-written playbooks. What it doesn’t do: replace the need for human oversight on high-stakes decisions or generate its own telemetry.
2. MDR (Managed Detection & Response)
An outsourced service combining detection technology with human analysts providing 24/7 monitoring, investigation, and response. What it doesn’t do: always own response outcomes. Many MDR providers escalate alerts back to your team for action, which means you’re still the one at 2 AM.
3. MSSP (Managed Security Services Provider)
A broad outsourced model handling security monitoring (firewalls, logs, and compliance reporting), typically alert-only, without deep investigation or response. What it doesn’t do: investigate or remediate threats. MSSPs tell you something happened; you figure out what to do about it.
4. SOAR (Security Orchestration, Automation, and Response)
An orchestration platform that executes predefined playbooks for repetitive SOC workflows, enrichment, ticketing, and basic containment. What it doesn’t do: adapt to novel threats. If there’s no matching playbook, SOAR does nothing.
5. XDR (Extended Detection & Response)
A unified detection layer that correlates telemetry across endpoints, network, cloud, and identity into a single pane. What it doesn’t do: investigate or respond autonomously. XDR sees the signal; something else (AI SOC, MDR, or your team) must act on it.
📊 5-Model Comparison Table
| Dimension | AI SOC | MDR | MSSP | SOAR | XDR |
|---|---|---|---|---|---|
| Core Function | Automated triage, investigation, and response | Outsourced detection + human response | Broad security monitoring | Playbook-driven workflow automation | Unified cross-domain detection |
| Automation Approach | Agentic reasoning (dynamic) | Varies: some AI, mostly human | Minimal, rule-based alerting | Static playbooks (rule-based) | ML-based correlation |
| Human Dependency | Low for Tier-1; human oversight for Tier-2+ | High: analysts drive investigation | Low-quality human engagement | High: SOC engineers maintain playbooks | Moderate: analysts interpret correlated alerts |
| Response Capability | Autonomous containment + escalation | Analyst-driven response (varies by provider) | Alert notification only | Automated execution of predefined actions | Detection-focused; limited native response |
| Integration Model | Vendor-agnostic ingestion | Often vendor-locked or narrow stack | Tool-specific connectors | API-dependent (brittle) | Typically single-vendor ecosystem |
| Typical Annual Cost | $30K–$80K | $50K–$200K | $100K–$250K+ | $50K–$150K (licenses + engineering) | $20K–$100K (platform) |
| Compliance Support | Emerging: audit trails improving | Moderate: depends on provider | Strong: built for compliance reporting | Strong: structured governance trails | Limited: detection-focused |
| Best-Fit Org Profile | Mid-market to enterprise with existing stack | Orgs lacking 24/7 internal SOC | Orgs needing checkbox compliance | Mature SOCs with engineering capacity | Orgs consolidating detection layers |
| Scalability | Scales with compute | Scales with headcount (expensive) | Scales broadly but shallow | Linear with playbook count | Scales with telemetry volume |
| Key Limitation | Requires clean telemetry; emerging governance | Vendor lock-in; opaque escalation | No investigation or response depth | Playbook maintenance burden; brittle | Detection without action; single-vendor risk |
The Architectural Insight Most Articles Miss
These five models exist on entirely different axes. MDR is a service delivery model. SOAR is a workflow tool. XDR is a data/detection layer. MSSP is an outsourcing model. AI SOC is an intelligence and decision layer. Some of these combine naturally; some compete. The mistake is treating them as interchangeable alternatives when they’re actually stackable components of a security architecture.
✅ Where UnderDefense Fits
Our UnderDefense MAXI platform unifies the AI SOC intelligence layer with MDR-grade human response, vendor-agnostically integrating across 250+ existing tools. The goal isn’t to replace everything you own but to make what you already have work together so you can layer models strategically, not choose one and hope it covers your gaps.
Q3. How Does Agentic AI in an AI SOC Actually Replace Legacy SOAR Playbooks?
If your organization invested heavily in SOAR between 2017 and 2022, this is the question keeping your SOC engineers up at night: Is my SOAR investment now technical debt? The honest answer is nuanced, but the architectural shift is real, and understanding it matters more than any vendor pitch.
Why This Comparison Matters Now
SOAR was the first serious attempt to automate SOC workflows at scale. It brought structure, repeatability, and compliance-friendly audit trails. Those are genuine strengths. But the operational reality, the part that doesn’t make it into the vendor slide deck, is that SOAR’s maintenance burden has become its own full-time job. Industry practitioners consistently report that even a small SOC ends up dedicating at least one full-time engineer purely to playbook maintenance rather than actual threat investigation. That’s expensive headcount producing zero direct security value.
✅ What SOAR Gets Right
Let’s be fair about where SOAR still earns its place:
- Structured governance: Playbooks create a documented, auditable chain of actions, exactly what compliance teams want
- Repeatable workflows: For well-understood, high-frequency scenarios (phishing triage, known IOC lookups), SOAR executes consistently
- Compliance audit trails: Every action is logged, timestamped, and traceable
❌ Where SOAR Breaks Down
The limitations aren’t theoretical. They’re operational:
- Brittle integrations: API changes from any connected tool can break entire playbook chains, requiring emergency engineering cycles
- Playbook sprawl: Organizations end up maintaining hundreds of playbooks nobody fully understands, with undocumented dependencies between them
- Zero novel threat handling: If there’s no matching playbook for an attack pattern, SOAR does nothing. It can’t reason through something it wasn’t explicitly told to handle
- Engineering tax: SOAR maintenance consumes a disproportionate share of SOC engineering capacity. That’s time not spent on proactive threat hunting or detection engineering
How Agentic AI Operates Differently
Agentic AI doesn’t execute pre-written scripts. It reasons through alerts dynamically. It correlates data across systems, adapts investigation paths in real time, and reaches explainable conclusions without someone manually defining every possible workflow. Think of it as the difference between a GPS that follows one pre-loaded route (SOAR) and a GPS that recalculates in real time based on traffic, road closures, and your destination (agentic AI).
The hybrid nuance matters too: some organizations may keep SOAR for compliance-mandated workflows (where you need an exact, auditable sequence every time) while layering agentic AI for investigation and adaptive response. These aren’t always either/or decisions.
📊 SOAR vs. Agentic AI SOC: Side-by-Side
| Dimension | SOAR | Agentic AI SOC |
|---|---|---|
| Automation Logic | Rule-based (if/then playbooks) | Reasoning-based (dynamic investigation) |
| Maintenance Burden | High: continuous playbook engineering | Low: learns and adapts with minimal tuning |
| Novel Threat Handling | ❌ Fails without a matching playbook | ✅ Dynamically investigates unknown patterns |
| Integration Approach | API-dependent (breaks on changes) | Flexible ingestion across diverse sources |
| Scalability | Linear with playbook count | Scales with compute |
| Compliance Audit Trail | ✅ Strong: structured and documented | ⚠️ Emerging: improving but newer |
| Human Dependency | SOC engineers for maintenance | Analysts for oversight and edge cases |
| Time-to-Value | Months of playbook development | Days to weeks for initial deployment |
Where UnderDefense Stands
We built UnderDefense MAXI to combine agentic AI investigation with human analyst verification, preserving the governance and auditability that SOAR provides while eliminating the playbook maintenance tax. If you’ve already invested in SOAR, that investment isn’t wasted but augmented. We layer on top of your existing orchestration, handling the adaptive investigation that playbooks were never designed to do, while your compliance-mandated workflows keep running exactly as documented.
Q4. Where Does XDR Actually Fit in the AI SOC Architecture?
XDR is not an alternative to AI SOC but the unified data layer that makes AI SOC effective. XDR collects and correlates telemetry across endpoints, network, cloud, and identity. AI SOC reasons over that correlated data to triage, investigate, and respond. They’re complementary layers, not competing models, and this is the single biggest gap in most competitor content on the topic.
⚡ Key Facts
- XDR unifies detection signals; AI SOC unifies investigation and response logic. Without XDR (or equivalent cross-domain telemetry), AI SOC works with siloed data. With XDR, it gets the cross-domain context that dramatically improves reasoning accuracy.
- XDR replaces the need for separate EDR + NDR + cloud detection. AI SOC replaces manual triage across those detections. Different problems, different layers.
- Detection without automated investigation remains a bottleneck. SOC teams using XDR alone still face the same alert volume problem. XDR consolidates signals but doesn’t resolve them. According to the 2025 SANS survey, false positives remain the #1 detection challenge even among organizations with consolidated detection platforms.
- The combination accelerates outcomes. A Cloud Security Alliance benchmark study found that AI-assisted SOC analysts completed investigations 45–61% faster with 22–29% higher accuracy. That improvement comes from having both the data (XDR) and the reasoning engine (AI SOC) working together.
🧠 Think of It This Way
XDR is the nervous system, collecting and transmitting signals from across your environment. AI SOC is the brain, deciding what those signals mean and whether to act. You need both, but the brain decides whether to pull your hand from the fire.
The practical implication: if you’ve already invested in XDR (Microsoft Defender XDR, Palo Alto Cortex, or SentinelOne Singularity), you’ve built the data foundation. What you’re likely missing is the autonomous investigation layer that turns consolidated alerts into resolved incidents, without your team manually triaging every one.
✅ How UnderDefense Handles This
UnderDefense MAXI ingests XDR telemetry alongside standalone EDR, SIEM, and cloud signals, providing AI SOC reasoning whether or not you’ve consolidated into a single XDR platform. We’re vendor-agnostic by design, integrating across 250+ tools, precisely because operational reality is messy. Most organizations don’t have a clean, single-vendor stack. They have Microsoft Defender XDR for endpoints, a different SIEM for compliance, a cloud-native tool for AWS, and maybe Palo Alto for network. UnderDefense MAXI works across all of it.
The point isn’t to force you onto another platform but to make the tools you already own produce better outcomes, with AI that reasons across your actual environment and human analysts who understand your organizational context when edge cases arise.
Q5. AI SOC vs. MDR vs. MSSP: Which Security Model Fits Your Organization (And What Will It Actually Cost)?
Choosing the wrong security model means you’re either overpaying for alert-only coverage (MSSP at ~$100K–$250K/yr), getting detection without real response (many MDRs), or deploying AI your team can’t govern. The honest answer is “it depends,” but let me define exactly what it depends ON.
❌ The Wrong Way to Decide
Most security leaders pick by brand (“CrowdStrike is the biggest”), cost alone, or feature checklist. These ignore the only question that matters: Can they respond with context, or just escalate alerts back to you? A CISO from a $3B manufacturing firm learned this the hard way with Arctic Wolf:
“This is not an extension of our security team as was originally sold. Still not quite there with the remediation side of things. We receive alerts, but not necessarily a clear path to resolution.”
— Sr. Cybersecurity Engineer, Manufacturing Arctic Wolf – Gartner Peer Review
✅ The Right Evaluation Framework (8 Criteria)
Score each provider 0–2 on these dimensions. Anything below 10 means you’re buying an alert feed, not managed security.
- Integration Model — Vendor-agnostic or proprietary lock-in?
- Response Capability — Detection-only, escalate-and-hope, or full containment?
- Human Analyst Access — Direct Tier 3–4 communication, or ticket queues?
- Pricing Transparency — Published per-endpoint, or “contact sales”?
- Compliance Framework Support — Native audit evidence for SOC 2, HIPAA, PCI-DSS, NIS2/DORA, or separate tools required?
- Onboarding Speed — Weeks or months?
- TCO (Total Cost of Ownership) — Model the true cost: platform + internal FTEs for triage + integration/tuning + dual-spend transition + compliance tooling.
- Organizational Context — Does the provider learn YOUR environment, or treat every alert uniformly?
💰 TCO Reality Check
| Model | Estimated Annual TCO | What’s Included |
|---|---|---|
| Traditional MSSP | ~$150K–$300K | Contract + internal investigation labor |
| Traditional MDR | ~$80K–$200K | Detection + partial response |
| AI SOC + Human Ally | ~$40K–$100K | Highest automation offsets FTE costs |
Applying the Framework: Score Table
| Criterion | Typical MSSP | Traditional MDR (Arctic Wolf) | UnderDefense |
|---|---|---|---|
| Integration Model | 1 — Limited stack | 0 — Proprietary SIEM required | 2 — 250+ tools supported |
| Response Capability | 0 — Alert-only | 1 — Escalates with recommendations | 2 — Full containment, 2-minute alert-to-triage |
| Human Analyst Access | 1 — Ticket-based | 1 — Concierge, but limited remediation | 2 — Direct Tier 3–4, ChatOps verification |
| Pricing Transparency | 1 — Opaque contracts | 0 — $96K median, unpublished | 2 — Published $11–15/endpoint/month |
| Compliance Support | 1 — Separate tools | 1 — Partial | 2 — Forever-free compliance kits |
| Onboarding Speed | 0 — Months | 1 — Weeks with stack migration | 2 — 30-day turnkey |
| TCO | 0 — Highest | 1 — Mid-range | 2 — Lowest with automation |
| Org Context | 1 — Rigid playbooks | 1 — Some customization | 2 — Learns VIPs, assets, team structure |
| Total | 5/16 | 6/16 | 16/16 |
⭐ How to Use This
Choose MSSP if you need broad IT outsourcing with basic compliance. Choose MDR if you want 24/7 detection with some response. Choose AI SOC + Human Ally if you need contextual detection, immediate containment, compliance-native support (SOC 2, HIPAA, PCI-DSS, NIS2/DORA), and transparent pricing.
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User, Program Development UnderDefense – G2 Verified Review
Q6. Can You Actually Replace Your MSSP or MDR with an AI SOC, and What Does the Migration Path Look Like?
“We’ve been with our MSSP for three years, ripping that out feels risky, even if AI SOC sounds better on paper.”
⏰ Why the Anxiety Is Rational
This concern makes complete sense. MSSP and MDR relationships involve institutional knowledge, compliance dependencies, and operational inertia. Switching has real costs: dual-spend during transition, re-tuning detection rules, team retraining. I’ve seen CISOs whose custom correlation rules, built over years, vanished overnight when they switched SIEM vendors, because those rules lived in the vendor’s proprietary system, not the customer’s.
The question isn’t “is AI SOC better in theory.” Rather, it’s “is migration risk worth the operational gain for YOUR environment.” Here’s how to decide.
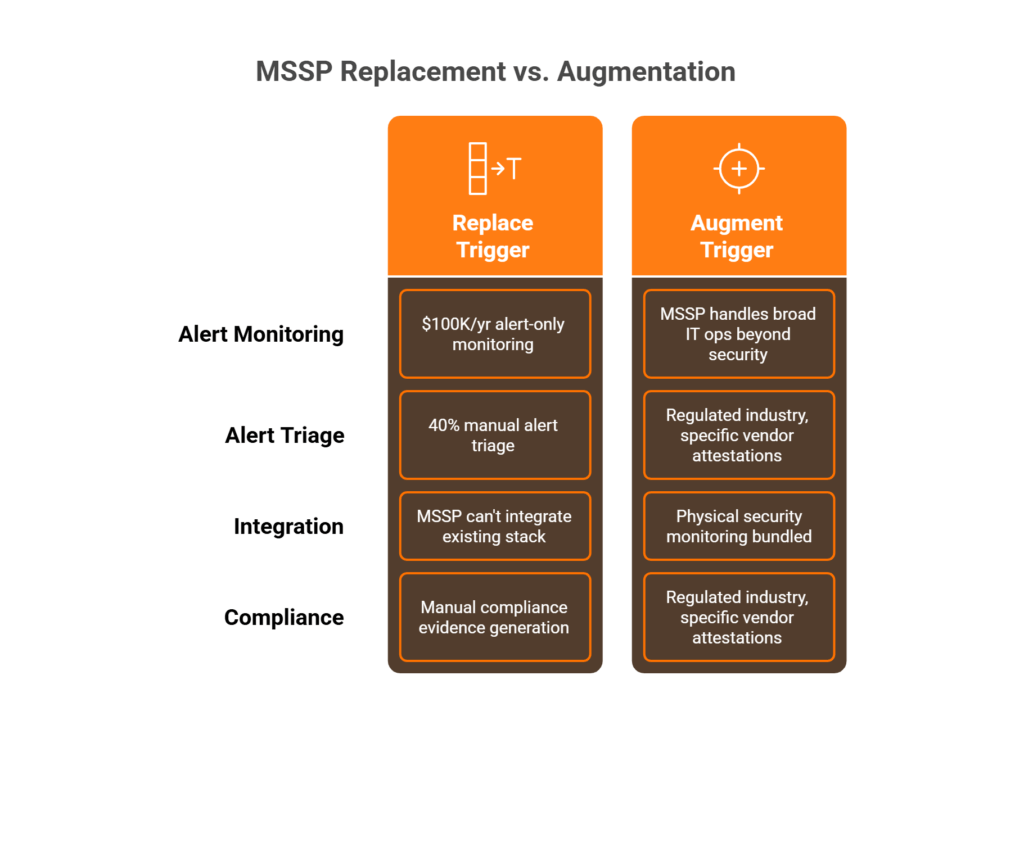
✅ REPLACE vs. AUGMENT Decision Matrix
REPLACE your MSSP/MDR if:
- Paying >$100K/yr for alert-only monitoring
- Your team triages >40% of alerts manually
- Your MSSP can’t integrate your existing stack
- Compliance evidence generation is still manual
AUGMENT (don’t replace) if:
- Your MSSP handles broad IT ops beyond security
- Regulated industry requires specific vendor attestations
- Physical security monitoring is bundled in the contract
A CISO reviewing Arctic Wolf put it bluntly:
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated. Support incidents are not worked to completion and communication evaporates.”
— CISO, Manufacturing ($3B–$10B) Arctic Wolf – Gartner Peer Review
If that sounds familiar, you’re a replacement candidate.
The MSSP → AI SOC Migration (4 Steps)
- Parallel Deployment — Run AI SOC alongside your MSSP for 30 days to validate detection coverage without creating gaps.
- Alert Comparison — Measure auto-resolution rate vs. MSSP alert volume to quantify noise reduction.
- Compliance Cutover — Migrate audit evidence generation to the AI SOC platform; verify it satisfies SOC 2, HIPAA, or PCI-DSS requirements.
- Contract Sunset — Phase out MSSP at renewal with documented coverage proof.
The MDR → AI SOC Migration (3 Steps)
- Stack Assessment — Identify which MDR detection rules can be replicated by AI SOC’s agentic reasoning.
- Human Overlay Calibration — Define which analyst tasks remain human-owned vs. AI-automated.
- Gradual Shift — Transition triage and investigation first, then response authority.
How We Built UnderDefense for This Exact Scenario
Our 30-day onboarding was designed for migration, not greenfield deployment. UnderDefense MAXI integrates with your existing stack on day one, no rip-and-replace. Dedicated concierge analysts learn your environment during transition: who your VIPs are, your org structure, your critical assets. Published pricing ($11–15/endpoint/month) eliminates the MSSP contract renewal ambiguity that keeps teams locked into underperforming providers.
“The platform works really well with our other security tools, which makes things much simpler. We really appreciate that we can customize the threat detection to focus on our specific needs.”
— Serhii B., CISO UnderDefense – G2 Verified Review
“We were looking for an MDR provider… after a few calls with UnderDefense we realized that we could get way more value, so they truly became our go-to cybersecurity ally.”
— Oleksii M., Mid-Market UnderDefense – G2 Verified Review
UnderDefense detected threats 2 days faster than CrowdStrike OverWatch in documented case studies, and integrated with, not replaced, the customer’s existing security deployment.
Q7. When Should You Absolutely NOT Use an AI SOC? (The Honest Answer)
Every AI SOC vendor, including us, has incentives to overstate capabilities. This section intentionally breaks that pattern. If you’re evaluating AI-powered security operations, you deserve to know where the technology genuinely falls short, not just where it shines.
⚠️ 7 Scenarios Where AI SOC Is the Wrong Tool
1. OT/ICS Environments with Air-Gapped Networks
Proprietary protocols (Modbus, DNP3, BACnet) in air-gapped operational technology environments aren’t what cloud-based AI models are trained on. If your shop floor runs PLCs from the 1990s, an AI SOC won’t parse those signals reliably. You need specialized OT security monitoring, such as Dragos, Claroty, or Nozomi, not a general-purpose detection layer.
2. Forensic Investigations Requiring Chain-of-Custody Evidence
Legal proceedings demand documented chain-of-custody for digital evidence. AI-generated investigation summaries don’t hold up in court. You need human forensic examiners with certified methodologies (EnCase, FTK) and witness-stand credibility.
When AI Summarizes but Can’t Testify
3. Threat Actor Attribution Requiring Geopolitical Intelligence
Determining whether an intrusion was state-sponsored (APT28, Lazarus Group) versus criminal requires geopolitical context that sits far outside any detection model’s training data. Attribution demands human intelligence analysts with classified or semi-classified feeds.
4. Organizations with <50 Endpoints
The cost-per-alert math simply doesn’t justify AI SOC at this scale. A well-configured EDR with basic managed monitoring handles the volume. Save the AI SOC investment for when your attack surface actually demands it.
5. Compliance-Specific Constraints
Regulated environments with specific human-accountability requirements present unique challenges:
- HIPAA-covered entities requiring Business Associate Agreements (BAAs) from a human-accountable provider, as AI can’t sign a BAA.
- NIS2/DORA requiring named incident response leads documented by regulation.
- PCI-DSS environments needing documented human review for cardholder data access anomalies, because automated disposition alone won’t satisfy QSA auditors.
6. Adversarial AI Attacks Targeting the AI SOC Itself
Model poisoning, evasion techniques, and prompt injection targeting the detection layer represent a real and growing threat class. If an adversary specifically targets your AI SOC’s reasoning engine, you need human analysts who can recognize when the AI itself is compromised. No model can reliably detect its own manipulation.
7. Executive/Board Communication During Active Incidents
AI generates excellent technical summaries. It does not translate “lateral movement detected across three subnets” into “we may lose $4M in customer data and trigger mandatory breach notification within 72 hours.” That translation requires a human who understands your business, your board, and your regulatory exposure.
“Not Yet” vs. “Never”
Some limitations are temporary: OT support is expanding, forensic AI is maturing, and detection models are getting harder to evade. Others are permanently human-dependent: board communication during crisis, legal attestation, and novel TTP analysis where no historical pattern exists. The distinction matters for planning.
Why We Built the “AI SOC + Human Ally” Model
This is precisely why UnderDefense doesn’t bet everything on automation. Agentic AI handles 80%+ of automatable detection and triage, while dedicated Tier 3–4 analysts own every scenario listed above. Knowing AI’s boundaries isn’t weakness, it’s the difference between a vendor and a partner.
Q8. What Does the Same Phishing-to-Lateral-Movement Attack Look Like Across All Five Models?
⏰ 2:47 AM, Tuesday.
A credential-phishing email bypasses your email gateway. An employee clicks, enters credentials on a spoofed page. Within 12 minutes: the attacker authenticates via VPN, escalates privileges using a known CVE, and begins lateral movement toward a PII file server holding 50,000 customer records. The clock is ticking. This is one of the 40% of alerts that goes uninvestigated at the average organization.
Here’s how each security model handles this exact scenario.
🔍 Five-Model Response Walkthrough
MSSP Response:
Detects anomalous VPN login → generates ticket → emails your team at 3:15 AM → waits for analyst response → 6–8 hours to containment. Your team wakes up to a ticket queue, not a resolved incident.
Traditional MDR Response:
Correlates credential theft + lateral movement → analyst investigates at 3:05 AM → escalates with a recommendation → 2–4 hours. Better, but your team still executes the containment.
SOAR Response:
Playbook triggers on “impossible travel” → auto-disables VPN token → BUT misses the lateral movement (no matching playbook for this specific CVE chain) → partial containment. The attacker is still inside.
XDR Response:
Correlates the full kill-chain into a unified alert → presents to analyst → BUT requires a human to execute response actions → fast detection, response depends on staffing. At 2:47 AM, staffing is the variable that kills you.
✅ AI SOC + Human Ally Response:
Correlates full kill-chain in <3 minutes → auto-enriches with threat intel + user context → analyst reaches the employee via Slack → AI isolates endpoint + revokes credentials + blocks lateral movement → FULL containment at 2:58 AM → your team gets a morning summary with the incident report ready before coffee.
💸 The Containment Time Gap
Every hour of delay increases breach cost by approximately $37K (IBM Cost of a Data Breach Report). The difference between MSSP’s 6–8 hours and AI SOC’s 11 minutes isn’t incremental, it’s existential for a 50,000-record PII exposure. The 90% false-positive rate at most organizations means MSSP/MDR analysts may deprioritize this real alert among noise. AI SOC’s 92% auto-resolution clears that noise so real threats get instant attention.
How This Actually Works in UnderDefense MAXI
This is the exact workflow our platform executes: agentic AI handles correlation and containment at machine speed, while concierge analysts handle judgment calls (user verification, CISO escalation with business-context summary). Contained before you wake up. Incident report ready before morning coffee.
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., Enterprise CIO UnderDefense – G2 Verified Review
From 6-hour MSSP alert queues to 11-minute AI-driven containment, that’s not an upgrade. It’s a different category of security operations.
Q9. Is Your Security Operation Ready for the AI SOC Shift? (Self-Assessment Checklist)
Before you evaluate a single vendor, you need to know where you actually stand. Too many security leaders jump straight into product demos without understanding their own operational gaps, and end up buying capabilities they can’t absorb or missing the ones that matter most.
I’ve run this exercise with dozens of CISOs, IT directors, and CTOs across industries. The pattern is consistent: teams overestimate their maturity until they see it scored on paper. Here’s the checklist we use.
⭐ Rate Your Security Operations: 8-Point Readiness Audit
Score your current security operations honestly against these eight criteria. Check only the boxes where you can point to documented evidence, not aspirations:
- ☐ 24/7/365 threat monitoring, not just business-hours coverage with an on-call rotation that nobody actually follows at 3 AM
- ☐ Critical threat containment within 30 minutes, from first detection signal to isolation, not from when someone finally reads the alert
- ☐ EDR, SIEM, cloud, and identity alerts correlated in a unified view, one console, not four tabs and a spreadsheet
- ☐ Suspicious activity verified directly with users before escalation, your analysts contact the person involved via Slack, Teams, or phone, not just forward the alert to IT
- ☐ Handle 1,000+ alerts/day without manual triage bottlenecks, automation actually resolves the routine; humans focus on the ambiguous
- ☐ Security monitoring auto-generates compliance evidence (SOC 2, HIPAA, ISO 27001), not a separate quarterly scramble
- ☐ Direct access to Tier 3–4 analysts, you can reach a senior analyst in minutes, not through a ticketing queue with a 4-hour SLA
- ☐ Team focuses on threat hunting and strategy, not consumed by alert noise, false positives, and ticket management
📊 What Your Score Means
| Score | Maturity Level | What It Tells You |
|---|---|---|
| ✅ 6–8 | Mature | Your operations are strong. AI SOC will accelerate and optimize what’s already working. Expect efficiency gains, not foundational fixes. |
| ⚠️ 3–5 | Critical gaps | You’re likely missing real threats or burning out your team on noise. AI SOC combined with dedicated human analyst support closes these gaps fast. |
| ❌ 0–2 | Foundational risk | Breach exposure is high and reactive processes dominate your posture. Start with MDR or co-managed SOC before layering AI SOC capabilities. |
Be honest with yourself here. A score of 3 doesn’t mean failure. It means you now know exactly where the investment needs to go.
✅ How UnderDefense Turns Unchecked Boxes Into Checked Ones
We built our platform specifically around these eight criteria because they represent what actually breaks in real security operations. UnderDefense MAXI delivers 24/7 monitoring with 2-minute alert-to-triage and 15-minute escalation for critical incidents, ChatOps user verification through Slack and Teams, 250+ tool integrations across your existing stack, and compliance automation that generates audit evidence continuously, all backed by dedicated Tier 3–4 analysts who know your environment.
Most teams go from 2–3 checks to 8/8 within 30 days of onboarding. That’s not a marketing claim but a documented outcome across 500+ MDR deployments.
“UnderDefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together. Now, everything is connected and easier to manage.”
— Inga M., CEO UnderDefense – G2 Verified Review
“With their proactive monitoring and rapid incident response capabilities, we can detect and mitigate security threats.”
— Alexey S., CEO UnderDefense – G2 Verified Review
⏰ Scored below 5? Book a 15-minute security gap assessment to see exactly where UnderDefense closes the holes, and get a documented roadmap within the first call.
Q10. Exploring the Right Security Model? Start With These Resources
Choosing between AI SOC, MDR, and MSSP isn’t something you resolve in a single article. It requires evaluating real providers against the criteria we’ve covered throughout this guide. The landscape shifts quarterly: new vendors emerge, existing ones rebrand their monitoring dashboards as “AI-powered,” and pricing models change without notice. Below are curated resources to accelerate your evaluation without starting from scratch.
What to Prioritize in Your Provider Evaluation
- Vendor-agnostic integration vs. proprietary lock-in: Does the provider work with your CrowdStrike, Splunk, and Azure stack, or force replacement?
- Published response time SLAs and documented outcomes: Can they show you case studies with specific response time metrics, not just promises?
- Transparent per-endpoint pricing vs. opaque enterprise quotes: Is cost predictable at $11–15/endpoint/month, or hidden behind “contact sales”?
- Compliance evidence generation included vs. separate add-on: Do security operations automatically produce SOC 2, HIPAA, and ISO 27001 artifacts?
- Direct analyst access vs. ticket-based escalation: Can you reach Tier 3–4 analysts in minutes, or submit a support ticket and wait?
📋 Deep-Dive Resources for Serious Evaluators
Each resource below is built around the operational criteria covered in this article, including scored providers, published pricing, response time documentation, and integration capabilities:
This analysis is based on documented response times, G2 reviews, published pricing, and operational outcomes across 500+ MDR deployments.
Q11. How Does the AI SOC + Human Ally Model Change the Security Operations Equation?
The question was never “AI SOC vs. MDR vs. MSSP vs. SOAR” as a winner-take-all cage match. Each model was built for a different era and a different problem set. The real question, the one that actually determines whether your organization gets breached or not, is this: what operating philosophy matches the 2026 threat landscape?
The Limits of Every Model, Taken Alone
SOAR gave us automation but demanded constant playbook maintenance, and broke silently when environments changed. MSSPs gave us coverage but not context; you got checkbox monitoring based on rigid rules rather than real-time threat intelligence. MDR gave us human analysts but not machine-speed response; by the time a Tier 2 analyst investigated, the attacker had already moved laterally. XDR gave us unified telemetry but not unified action. Correlated data sitting in a dashboard is not the same as a contained threat.
AI SOC gives us reasoning at scale. But without human allies, it’s blind to business context, compliance nuance, and the judgment calls that separate a legitimate late-night admin session from credential theft.
The Unified Operating Philosophy
The answer isn’t choosing one model but building an operating philosophy where AI handles triage, investigation, and containment at machine speed while human analysts handle context, verification, and edge cases. This is the “AI SOC + Human Ally” paradigm: automation does what it does best (speed, pattern recognition, and correlation across thousands of signals), and humans do what they do best (judgment, organizational context, and direct communication with affected users).
As one CISO I work with put it during a recent conversation: “I just can’t automate everything. I can’t get to a fully lights-out automated security stack because we always run into situations that need human analysis.” That’s exactly right. You need both, and you need them working as a unified system, not separate tools stitched together with Jira tickets.
How UnderDefense Embodies This Model
We built UnderDefense MAXI for this paradigm. Vendor-agnostic integration with 250+ existing security tools means you don’t abandon your CrowdStrike, Splunk, or Azure investments. Agentic AI handles 80%+ of investigations at machine speed, including automated context collection, multi-system correlation, and structured investigation reports delivered in seconds. Concierge analysts handle the rest: the ambiguous alerts, the user verification through ChatOps, and the containment decisions that require organizational knowledge.
Transparent $11–15/endpoint/month pricing. Thirty-day onboarding. Not an MSSP. Not just MDR. The unified operating model this entire article describes.
“Before MAXI, constantly keeping an eye on our expanding cloud assets was the norm. With MAXI’s MDR, it’s like having a magnifying glass over every server, giving us confidence and continuous visibility. Since its integration and adopting UnderDefense team’s recommendations, we’ve witnessed major drop in cloud-related incidents.”
— Lesia P., Product Marketing Manager UnderDefense – G2 Verified Review
“Their team was flexible, and they arranged everything in quite a short time.”
— IT Administrator, Charitable Organization UnderDefense – Clutch Verified Review
The Organizations That Win in 2026
The organizations that get security right this year won’t have the most tools or the biggest SOC headcount. They’ll be the ones where AI and humans each do what they’re best at, together, in a system that’s observable, auditable, and fast enough to match the threat actors who are already using agentic AI against you.
1. What is the real difference between AI SOC, MDR, and MSSP for security operations?
We see these three models confused constantly, so here’s how we draw the line based on operational outcomes, not marketing labels.
An MSSP (Managed Security Service Provider) monitors your environment and generates alerts. In most cases, the MSSP sends you a ticket and waits for your team to investigate and respond. You’re paying for coverage, not resolution.
MDR (Managed Detection and Response) adds a human analyst layer. Providers like Arctic Wolf or Expel will investigate alerts, correlate signals, and escalate with recommendations. However, many MDRs still push containment responsibility back to your internal team.
AI SOC combines agentic AI for automated triage, investigation, and containment with dedicated human analysts for judgment calls, user verification, and edge cases. We built UnderDefense MAXI around this model, delivering 2-minute alert-to-triage, 15-minute escalation for critical incidents, and full containment authority so your team wakes up to a resolved incident report rather than a queue of unworked tickets.
The core differentiator: AI SOC doesn’t just detect or escalate, it responds with context at machine speed, backed by human oversight where automation falls short.
2. How does AI SOC differ from SOAR in handling automated incident response?
SOAR (Security Orchestration, Automation, and Response) relies on pre-built playbooks, essentially if/then logic trees written by your team or the vendor. If an alert matches a known pattern, the playbook fires. If it doesn’t match, the alert sits unhandled or gets escalated raw.
We’ve seen the failure mode firsthand. SOAR playbooks cover only what you anticipated. Novel attack chains, environment drift, and multi-stage threats that don’t fit a single rule fall through the cracks. One organization we worked with had 847 playbooks and still missed a lateral movement attack because no single playbook matched that specific CVE-to-privilege-escalation sequence.
AI SOC uses agentic reasoning rather than static playbooks. The AI investigates dynamically, correlating signals across EDR, SIEM, identity, and cloud telemetry without needing a pre-written rule for every scenario. When we built our SOC automation capabilities, we designed for adaptability, not just repeatability.
The practical result: SOAR works for known, repeatable scenarios. AI SOC handles the ambiguous, multi-step attacks that actually breach organizations.
3. Is AI SOC better than XDR for threat detection and response?
XDR (Extended Detection and Response) is a data unification layer. It correlates telemetry from endpoints, network, cloud, and identity into a single pane of glass, giving analysts a complete view of the kill chain. That’s genuinely valuable.
The gap is on the response side. XDR presents the correlated alert, but a human analyst still needs to execute containment actions. At 2:47 AM on a Tuesday, staffing is the variable that determines whether XDR’s excellent detection translates into actual threat containment or a ticket that waits until morning.
AI SOC takes XDR’s correlated telemetry and adds automated response plus human analyst judgment. We integrate with your existing EDR and detection tools rather than replacing them. UnderDefense MAXI ingests XDR signals and acts on them at machine speed, with Tier 3–4 analysts verifying containment decisions that require business context.
Think of it this way: XDR tells you the full story of an attack. AI SOC tells you the story and resolves it before your team reads chapter one.
4. When should you NOT use an AI SOC?
We believe in being transparent about where AI SOC falls short. Here are the scenarios where we tell prospects to look elsewhere:
-
OT/ICS air-gapped environments: Proprietary protocols like Modbus, DNP3, and BACnet in operational technology networks aren’t what cloud-based AI models are trained on. Specialized OT security tools (Dragos, Claroty, Nozomi) are the right fit.
-
Forensic investigations requiring chain-of-custody evidence: AI-generated summaries don’t hold up in court proceedings. You need certified human forensic examiners.
-
Organizations with fewer than 50 endpoints: The cost-per-alert math doesn’t justify AI SOC at this scale. A well-configured managed EDR handles the volume.
-
Adversarial AI attacks targeting the AI SOC itself: Model poisoning and prompt injection require human analysts who can recognize when the AI’s reasoning engine is compromised.
-
Executive/board communication during active incidents: Translating technical findings into business-impact language for your board requires a human who understands regulatory exposure and stakeholder dynamics.
Knowing these boundaries informed why we built the “AI SOC + Human Ally” model rather than betting everything on automation alone.
5. Can you actually replace your MSSP with an AI SOC?
Yes, but only under specific conditions. We recommend replacing your MSSP if you’re paying over $100K/yr for alert-only monitoring, your team triages more than 40% of alerts manually, your MSSP can’t integrate your existing security stack, or compliance evidence generation remains a separate manual process.
We recommend augmenting (not replacing) if your MSSP handles broad IT operations beyond security, if your regulated industry requires specific vendor attestations, or if physical security monitoring is bundled in the contract.
The migration path we’ve refined across 500+ deployments follows four steps: parallel deployment for 30 days alongside your MSSP, alert comparison to quantify noise reduction, compliance cutover to migrate audit evidence generation, and contract sunset at your next renewal with documented coverage proof.
We designed UnderDefense MAXI’s 30-day onboarding specifically for migration scenarios. Published pricing at $11–15/endpoint/month eliminates the renewal ambiguity that keeps teams locked into underperforming MSSPs. If you want to model your costs before committing, our SOC cost calculator provides a real-time budget comparison.
6. How much does AI SOC cost compared to MSSP and MDR?
Based on our operational data and market analysis, here’s how total cost of ownership (TCO) compares across models:
-
Traditional MSSP: ~$150K–$300K/yr, which includes the contract plus internal investigation labor because your team still handles triage and response.
-
Traditional MDR: ~$80K–$200K/yr for detection plus partial response. Containment often falls back to your internal staff.
-
AI SOC + Human Ally: ~$40K–$100K/yr. Higher automation offsets FTE costs, and integrated compliance evidence generation eliminates separate tooling expenses.
The critical factor most TCO comparisons miss is the hidden internal labor cost. When your MSSP sends 200 alerts per day and your team manually triages 40% of them, that’s 2–3 FTEs worth of work buried in your security budget that never appears on the MSSP invoice.
We publish our pricing transparently at $11–15/endpoint/month. No opaque enterprise quotes, no “contact sales” barriers. You can forecast costs precisely using our SOC cost calculator before any sales conversation.
7. What does managed SIEM vendor lock-in mean, and how does it affect your security model choice?
Managed SIEM vendor lock-in occurs when your detection rules, correlation logic, dashboards, and compliance workflows are built inside a vendor’s proprietary system rather than your own. We’ve seen CISOs lose years of custom correlation rules overnight when switching SIEM vendors because those rules were stored in the vendor’s environment, not exported to the customer.
This lock-in affects your AI SOC, MDR, or MSSP decision directly. If your current MSSP requires their proprietary SIEM, switching providers means starting detection engineering from scratch, creating a dangerous coverage gap during migration.
The solution is choosing providers that integrate with your existing stack rather than forcing replacement. UnderDefense MAXI supports 250+ tool integrations, including Splunk, Microsoft Sentinel, and Elastic, so your detection logic stays portable. We also integrate natively with your existing SIEM deployment rather than demanding rip-and-replace.
When evaluating any security model, ask one question: “If we leave, what do we keep?” If the answer is “nothing,” you’re already locked in.
8. How do you assess if your organization is ready for an AI SOC?
We use an 8-point readiness audit that we’ve refined across dozens of CISO engagements. Score your current operations against these criteria, checking only boxes where you have documented evidence:
-
24/7/365 threat monitoring (not business-hours coverage with an ignored on-call rotation)
-
Critical threat containment within 30 minutes from first detection signal
-
EDR, SIEM, cloud, and identity alerts correlated in a unified view
-
Suspicious activity verified directly with users before escalation
-
Ability to handle 1,000+ alerts/day without manual triage bottlenecks
-
Security monitoring auto-generates compliance evidence (SOC 2, HIPAA, ISO 27001)
-
Direct access to Tier 3–4 analysts in minutes, not hours
-
Team focuses on threat hunting and strategy rather than alert noise
If you score 6–8, AI SOC will optimize what’s already working. At 3–5, you have critical gaps that AI SOC plus human analysts closes fast. At 0–2, start with managed detection and response as your foundation before layering AI SOC capabilities.
Most teams we onboard go from 2–3 checks to 8/8 within 30 days, a documented outcome across 500+ MDR deployments.
The post AI SOC vs MDR vs MSSP: Scoring Table, Pricing Data, Response Proof appeared first on UnderDefense.