Q1. Your Portfolio Has Ten Different Security Problems, and They All Share One Structural Root Cause
You manage a portfolio of 10–20 companies. Company A just closed a healthcare acquisition and needs HIPAA compliance yesterday. Company B’s CISO left three months ago, and nobody’s watching the SIEM. Company C had a phishing incident last quarter, and the board wants answers. Company D is your fastest-growing SaaS play with 2,000 endpoints and a three-person IT team. Company E is 18 months from exit, and the buyer’s diligence team will scrutinize every security gap.
You already know each of these companies needs cybersecurity. The question is not “why” but “how do I standardize security across all of them without running 10 different programs?”
⚠️ The Root Cause: Missing Connection, Not Missing Tools
The root cause is not that portfolio companies lack security tools. Most have some combination of EDR, firewalls, maybe a SIEM. The problem is that none of it is connected, none of it reports into a unified view, and the Operating Partner has no way to compare Company A’s security posture against Company D’s. Each company is a separate island of risk.
During ownership transitions, portfolio companies often lack mature risk management, struggle with new IT governance, and face targeted social engineering attacks: fake PE emails, wire fraud attempts. Many PE firms now delay public announcements until weeks after closing just to avoid painting a target on their new acquisition. Attackers do not care which portfolio company is weakest; they just need one way in.
💸 Hidden Costs That Show Up Where PE Firms Already Track
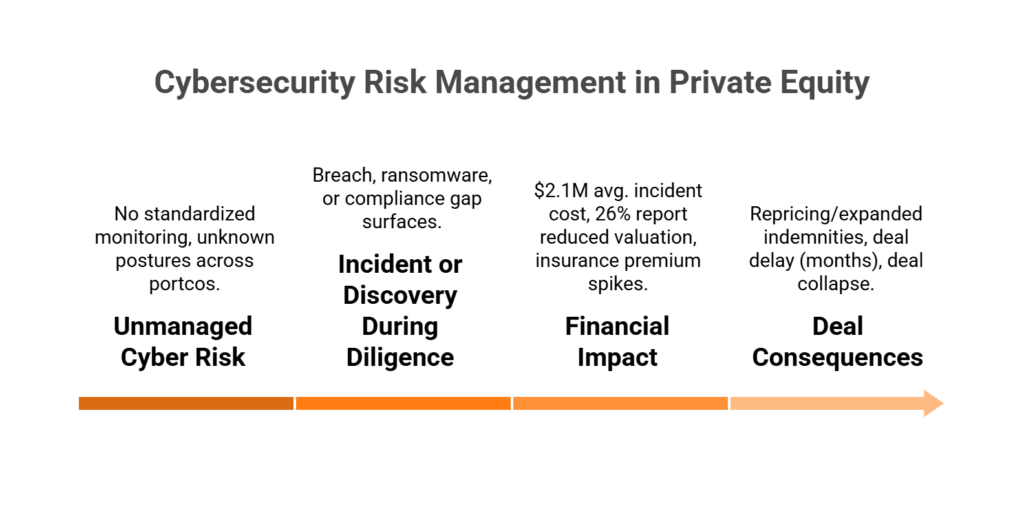
This fragmentation creates costs that surface in places PE firms already monitor:
- Incident remediation averaging $2.1M per event across PE portfolios (Kroll, 2026)
- Cyber insurance premiums rising 15–20% annually because underwriters see ungoverned risk
- Exit delays when buyers discover inconsistent security postures during diligence, with 62% of M&A deals experiencing cyber-related delays
- LP questions about fund-level cyber governance that the Operating Partner cannot answer with confidence
These are not IT problems. They are portfolio economics problems. And 96% of PE firms now expect the importance of portfolio cybersecurity to increase over the next 12 months.
✅ How the Firms Getting This Right Actually Operate
The firms getting this right are not running 10 separate security programs. They deploy a single AI SOC layer that integrates with whatever each portfolio company already runs, standardizing detection, response, and governance reporting across the entire fund without forcing any company to rip and replace its existing tools. The result: one dashboard, one SLA, one governance framework, and one insurance conversation across every portfolio company.
This article maps exactly how that model works: the financial case, the operational mechanics, the deployment timeline, and the governance output that buyers and LPs now expect. Not theory, but the specific architecture that turns fragmented portfolio cybersecurity into a standardized, measurable value creation lever.
Q2. The Financial Math: What Cyber Risk Costs Your Portfolio, and What Standardization Saves
If you are an Operating Partner or PE CFO, this is the section you will forward to your investment committee. The numbers below are not projections. They are reported outcomes from the past 12 months, drawn from Kroll’s global survey of 325 PE firm executives.
⏰ The Cost of Inaction: What Kroll’s 2026 Data Actually Shows
- 94% of PE firms experienced financial impact from cyber incidents, averaging $2.1M per event.
- 44% of sub-$500M AUM firms saw cyber risk directly reduce valuations at exit.
- 62% of M&A deals experienced cyber-related delays.
- 73% of buyers would renegotiate or walk away if undisclosed breaches surfaced during diligence.
- 53% believe the financial impact of cyberattacks will grow in the coming year, and 54% expect cyber incidents to be more challenging.
These are not edge cases. This is the new normal for PE-backed companies.
💰 Insurance Premium Dynamics: The Lever Most Firms Miss
Cyber insurance premiums are projected to rise 15–20% annually through 2026, driven by reinsurance costs and rising claim severities. Forrester Research predicts written cyber insurance premiums will rise 15% in 2026 as new AI threats and data demands emerge.
For a 15-company PE portfolio, aggregate premiums typically run $2.25M–$7.5M annually. Insurers now underwrite based on security posture: 24/7 monitoring, MFA enforcement, documented incident response, and compliance certifications. Companies demonstrating AI-driven security operations are negotiating meaningful premium reductions because insurers see measurably lower risk when detection and response happen in minutes, not hours.
📊 Portfolio-Scale ROI Model: The Math for a 15-Company Fund
Here is how the economics work at portfolio scale:
| Cost/Savings Category | Per Portfolio Company | Fund-Level (15 Companies) |
|---|---|---|
| AI SOC deployment ($11–15/endpoint/month, ~500 endpoints) | $66K–$90K/year | $990K–$1.35M |
| Insurance savings (15–20% premium reduction) | $22.5K–$100K | $337K–$1.5M |
| Incident avoidance (even one prevented $2.1M event) | — | $2.1M+ |
| Exit value protection (avoiding 8–15% valuation reduction) | Varies by deal size | Multiples of investment |
The AI SOC typically pays for itself through insurance savings alone, before counting incident prevention or exit value uplift. When 44% of sub-$500M AUM firms report valuation reductions from cyber risk, the ROI conversation shifts from “can we afford this?” to “can we afford not to?”
✅ The Standardization Dividend
The firms treating cybersecurity as a value creation lever, not just a cost center, are positioning portfolio companies more favorably for eventual exits while reducing the risk of value-destroying incidents during the holding period. That is the financial case for a standardized AI SOC approach.
Q3. Why Per-Company Security Fixes Do Not Scale: The Fragmentation Problem Across PE Portfolios
Here is what the Operating Partner actually sees on any given Monday morning: Company A runs CrowdStrike + Splunk with a 5-person security team. Company B has Microsoft Defender and no SIEM; their “security program” is the IT manager checking alerts when he has time. Company C uses a legacy MSSP that sends 500 unfiltered alerts daily that nobody reads. Company D just acquired a SaaS company running AWS GuardDuty with no endpoint protection.
The Operating Partner has no unified view, no way to compare maturity across companies, and no single number to report to LPs. This is not negligence. It is the natural result of acquiring companies that were built independently.
❌ Two Common Approaches, Both Structurally Limited
Approach 1: “Hands-off”, letting each portco manage its own security. Rational in theory (local teams know their environment), but it produces wildly inconsistent maturity and zero fund-level visibility. When Company B gets breached, the Operating Partner finds out from a journalist, not a dashboard.
Approach 2: “Single-vendor mandate”, deploying Arctic Wolf or CrowdStrike across all companies. Sounds standardized, but Arctic Wolf requires proprietary SIEM replacement (expensive, disruptive, 6+ month migration per company), and CrowdStrike only covers Falcon-native environments (what about Company D’s AWS stack?). You standardize the vendor, but not the coverage.
One Arctic Wolf reviewer captured this frustration directly:
“We received little value from Arctic Wolf. The product offered little visibility… Anything you want to look at or changes you need to make must go through their engineering team. As an MSP, this is a horrible way to do business.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
And from a CISO evaluating Arctic Wolf’s MDR:
“Started out well but over the years the service has consistently not met expectations. Log collectors show working, however when asked to provide logs for an investigation no logs could be provided. Analysts provide little context.”
— CISO, Manufacturing (3B–10B USD) Arctic Wolf – Gartner Review
✅ The Architectural Shift: Standardize the Layer, Not the Tool
What PE firms actually need is a layer that sits on top of whatever each portfolio company already runs, connecting CrowdStrike, Microsoft Defender, Splunk, AWS GuardDuty, Okta, and whatever else into a single detection and response fabric. No rip-and-replace. No 6-month migrations. The standardization happens at the orchestration layer, not the tool layer. This is what an AI SOC provides, and it is the only approach that scales to 10, 20, or 50 portfolio companies without forcing every acquisition through a security tool migration.
How UnderDefense Makes This Operational
We built the UnderDefense MAXI platform for exactly this scenario: vendor-agnostic integration with 250+ existing tools means every portfolio company keeps its current stack while gaining unified AI-driven detection, response, and governance. The Operating Partner gets a single dashboard showing security posture, incidents, and risk scores across the entire portfolio. Each portco CISO retains local control. Proactive threat hunting runs 24/7 with 96% MITRE ATT&CK coverage.
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight. With UnderDefense MAXI, we’ve reduced security breaches. As the Information Security Director, it lets me focus on strategy, knowing the day-to-day security is managed effectively.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
⏰ The Difference in Practice
When traditional MDR detects a suspicious login at Company C, it sends an alert to Company C’s overwhelmed IT manager who sees it 6 hours later. When we detect the same event, the analyst verifies directly with the employee via Slack within minutes, confirms it is unauthorized, isolates the endpoint, revokes the compromised credential, and logs the entire response in the fund-level governance dashboard before the IT manager’s morning coffee.
Q4. What Is an AI SOC, and How Does the Model Actually Work Across Your Existing Infrastructure?
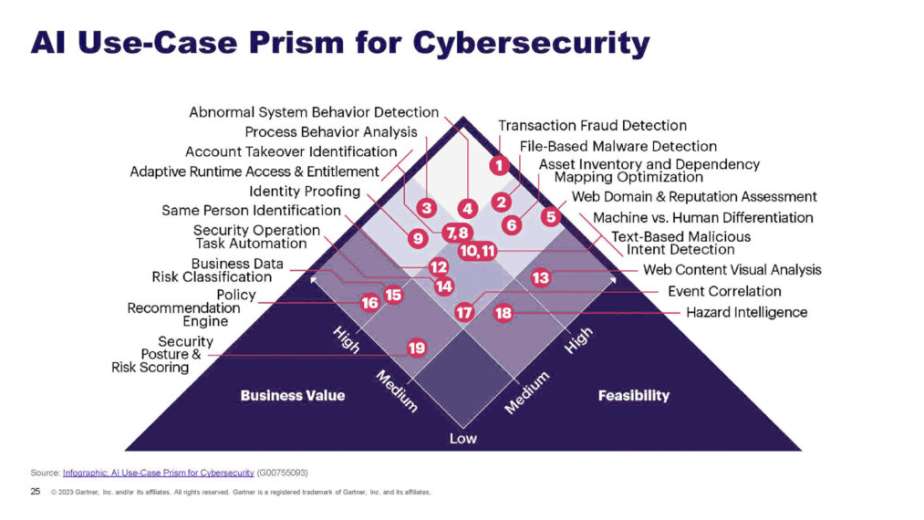
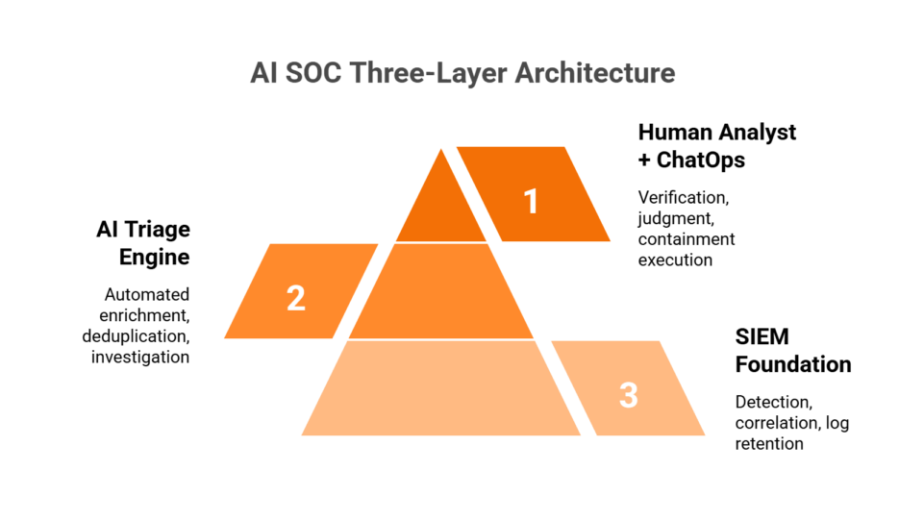
An AI SOC replaces the traditional model, where 20–30 analysts manually triage thousands of alerts, with an AI investigation layer that handles ~97% of alert analysis autonomously. Expert human analysts handle the ~3% that require judgment, context, and direct action. For PE firms, the critical distinction is that it deploys on top of existing infrastructure. Your portfolio companies do not need to change their security tools, hire SOC analysts, or build anything new.
How It Actually Works Under the Hood
The AI SOC connects to each portfolio company’s existing tools: whatever EDR they run (CrowdStrike, SentinelOne, Microsoft Defender), whatever SIEM (Splunk, Sentinel, Elastic), whatever cloud environment (AWS, Azure, GCP), and whatever identity provider (Okta, Azure AD). It ingests the telemetry these tools already generate and correlates it across sources.
When CrowdStrike flags suspicious PowerShell execution and Okta shows a login anomaly for the same user at the same time, the AI SOC connects those dots automatically. Of the thousands of daily signals, AI resolves ~97% autonomously (confirmed benign, known patterns, auto-remediated). The remaining ~3% that need human judgment, such as “Is this the real CFO logging in from an unusual country, or a compromised credential?”, go to a dedicated analyst who can verify directly with the user, contain the threat, and document the response. No ticket. No escalation back to the portco’s team.
What Each Portfolio Company Needs (and Does Not Need)
At minimum: an EDR on endpoints and some form of log collection. That is the baseline. The AI SOC does not require a specific vendor. It is vendor-agnostic across 250+ tools. Companies with more mature stacks (SIEM + EDR + identity + cloud) get deeper correlation. Companies with minimal tooling get immediate uplift just from having 24/7 AI-driven monitoring on their existing EDR. The UnderDefense MAXI platform adapts to each company’s maturity level while standardizing the detection, response, and reporting layer across all of them.
What the Operating Partner Gets
- ✅ Uniform detection coverage (96% MITRE ATT&CK) regardless of each portco’s individual tool stack
- ✅ Standardized SLAs (2-minute alert-to-triage, 15-minute escalation for critical incidents): same response speed whether it is the 5-person security team at Company A or the solo IT manager at Company B
- ✅ Centralized dashboard with fund-level and portco-level views
- ✅ Automated compliance evidence for SOC 2, ISO 27001, and HIPAA, with no separate GRC tool needed
- ✅ Normalized risk scoring so you can compare Company A’s posture to Company D’s in the same framework
⭐ The ERP Analogy That Makes This Click
Think of it as the “ERP of security operations.” PE firms standardized financial reporting across portfolio companies with NetSuite or SAP. The AI SOC does the same for cybersecurity, except deployment takes 30 days per company, not 12 months. The operating model is consistent, the governance output is uniform, and the cost structure is predictable: $11–15 per endpoint per month, published and transparent.
That is the shift: from fragmented, ungovernable portfolio cybersecurity to a standardized, measurable value creation lever that LPs, buyers, and insurers all recognize.
Q5. How One AI SOC Layer Serves Portfolio Companies With Completely Different Needs
The most common concern PE firms raise about portfolio-wide security is not cost but fit. “Our companies are so different. How can one solution work for a 50-person healthcare startup AND a 2,000-endpoint SaaS platform AND a manufacturing company with no security team?” The answer: a properly architected AI SOC standardizes the detection, response, and governance layer while adapting to each company’s unique infrastructure, regulatory context, and maturity level.
Here is what that looks like across five real portfolio archetypes:
⭐ The Compliance-Driven Portco
Healthcare or financial services company needing HIPAA, SOC 2, or PCI DSS. The AI SOC provides 24/7 monitoring that satisfies audit requirements, auto-generates compliance evidence, and gives the compliance officer a report instead of a project.
⭐ The Post-Breach Portco
Company that experienced a ransomware incident or phishing compromise. The AI SOC provides immediate containment capability, forensic documentation, and the demonstrated response maturity that prevents recurrence and reassures the board.
⭐ The Regulated-Industry Portco
Company facing SEC cyber disclosure mandates, DORA for EU financial exposure, or industry-specific regulations. The SEC now requires material cybersecurity incident disclosure within four business days. The AI SOC provides continuous monitoring and automated regulatory reporting that transforms compliance from a reactive fire drill into a background process.
⭐ The High-Growth Portco
Fast-scaling SaaS or tech company with 2,000+ endpoints and a 3-person IT team that cannot hire SOC analysts. The AI SOC provides the security operations team they cannot build, covering endpoint, cloud, and identity without adding headcount.
⭐ The Exit-Ready Portco
Company 12–18 months from sale where buyer diligence will scrutinize every security gap. The AI SOC provides documented security maturity, governance evidence, and incident response track record that protects valuation and accelerates the deal.
Why One Platform Serves All Five
UnderDefense’s UnderDefense MAXI platform serves all five archetypes simultaneously because the architecture is vendor-agnostic: it connects to whatever each company already runs. The analyst model is concierge-based, meaning our team learns each company’s context, users, and infrastructure. The reporting layer is standardized: same governance dashboard format across all portcos, with fund-level aggregation for the Operating Partner. One contract. One SLA. Five completely different companies getting exactly the coverage they need.
This is why we maintain a 100% ransomware prevention record across 500+ clients spanning healthcare, financial services, SaaS, government, and manufacturing, because the model was designed to flex across diverse environments, not force them into a single template.
“UnderDefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO UnderDefense – G2 Verified Review
“It’s reassuring to know they’re always watching for threats, and it doesn’t cost a fortune. The platform works really well with our other security tools, which makes things much simpler.”
— Serhii B., Chief Information Security Officer UnderDefense – G2 Verified Review
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., Enterprise (1000+ emp.) UnderDefense – G2 Verified Review
Q6. From Due Diligence to Day 100: Deploying AI SOC Across the Acquisition Lifecycle
Every PE acquisition follows the same security pattern: unknown risk before close, a dangerous monitoring gap during integration, and a slow ramp to standardized coverage. The firms that get this wrong face a documented 68% spike in cyber incidents during ownership transitions. Here is the lifecycle framework that eliminates that gap, from the first diligence call to Day 100 of ownership.
Pre-Acquisition Cyber Due Diligence: 7-Point Framework
Before signing, run every target through these seven checkpoints. These align with frameworks from the VCI Institute and are increasingly expected by sophisticated buyers and insurance underwriters alike:
- Security architecture review: What tools are in place (EDR, SIEM, IAM, cloud security)? What is missing or outdated? Map the full stack before you inherit it.
- Incident history: Past breaches, near-misses, ransomware exposure, and breach notification obligations. Request documented evidence, not verbal assurances.
- Regulatory exposure assessment: Which frameworks apply: SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS? The SEC now requires material cyber incident disclosure within four business days. DORA mandates ICT risk management for EU financial entities. These drive diligence scope directly.
- Third-party and supply chain risk: Vendor security assessments, SaaS dependency mapping, and fourth-party exposure. The SolarWinds breach demonstrated how supply chain risk cascades through acquisitions.
- Vulnerability posture: Last penetration test results, patch management cadence, and critical vulnerability backlog. If the last pentest was 18+ months ago, treat it as a red flag.
- Incident response maturity: Documented IR plan tested within 12 months, including tabletop exercises and response benchmarks. An untested plan is just a document sitting in SharePoint.
- Cyber insurance coverage and claims history: Active policies, exclusions, and whether past claims suggest systemic issues.
⏰ Days 1–30: Immediate Visibility
Deploy AI SOC with vendor-agnostic integration to existing tools. Establish 24/7 monitoring. Conduct initial threat assessment and vulnerability scan. Identify critical gaps: MFA gaps, unmanaged endpoints, patch debt. This closes the monitoring gap within 30 days, versus 6–12 months for traditional SOC buildouts.
⏰ Days 31–60: Standardization
Align detection rules to fund-level security policy. Deploy standardized incident response playbooks. Begin automated compliance evidence collection. Integrate portco into fund-level governance dashboard. AI-driven detection tuning typically reduces false positives by 90%+ within the first 60 days.
⏰ Days 61–90: Optimization
Tune detection to portco-specific context. Launch proactive threat hunting. Generate first quarterly cyber health report for Operating Partner and LP reporting. Benchmark against other portfolio companies to identify outliers and prioritize remediation spend.
Hold-Period Monitoring: Years 1–7
During the hold period, the AI SOC operates as continuous security infrastructure: ongoing threat detection, quarterly posture assessments, annual penetration testing coordination, regulatory change monitoring (SEC and DORA updates), and governance reporting cadence aligned to LP expectations. Each new acquisition gets folded into the same framework within 30 days of close, maintaining standardization as the portfolio grows.
How UnderDefense Simplifies This Lifecycle
UnderDefense’s 30-day turnkey deployment is specifically architected for PE post-acquisition scenarios: vendor-agnostic integration means no tool migration, concierge analysts learn the organization’s context within the first week, custom detection tuning starts immediately, and the governance dashboard goes live alongside monitoring, not months later as a separate project. Our documented case studies include avoiding $650K in potential losses and detecting threats 2 days faster than CrowdStrike OverWatch, while integrating with, not replacing, existing deployments.
Q7. Exit-Ready Governance: What Buyers, LPs, and Regulators Now Expect from Your Cyber Posture
Score your portfolio company’s exit-readiness against these 8 cybersecurity governance criteria that buyers, LPs, and regulators consistently scrutinize. These are not aspirational. They are the documented expectations from the past 24 months of PE exit diligence.
Exit Governance Readiness Checklist
- ✅ 24/7/365 security monitoring with documented SLAs and incident logs
- ✅ Incident response plan tested within the last 12 months (tabletop exercise + live drill)
- ✅ Current compliance certifications: SOC 2 Type II, ISO 27001, or industry-specific (HIPAA, PCI DSS)
- ✅ Board-level cybersecurity reporting with quantified risk metrics, not traffic-light dashboards
- ✅ Third-party risk management with documented vendor assessments
- ✅ Vulnerability management with <30-day critical patch SLA
- ✅ MFA enforced on all privileged accounts plus identity monitoring
- ✅ Documented cyber insurance coverage with clean claims history
⚠️ Regulatory Overlay You Cannot Ignore
The SEC requires material cyber incident disclosure within four business days of materiality determination. DORA mandates ICT risk management for EU financial entities effective January 2025. GDPR and CCPA require documented data protection controls with demonstrable compliance mechanisms. Buyers verify all of this during diligence, not after close, and gaps here trigger expanded indemnities or repricing.
Score Interpretation
| Score | Status | Deal Impact |
|---|---|---|
| 7–8 checked | ✅ Exit-ready | Cybersecurity adds value. Buyers see governance maturity as risk reduction, reflected in cleaner representations and warranties. |
| 4–6 checked | ⚠️ Material gaps | Sophisticated buyers will negotiate price reduction or expanded indemnities. Expect 60–90 day remediation timelines inserted into the deal. |
| 0–3 checked | ❌ High risk | Deal delay, repricing, or collapse. Aligns with the 44% of sub-$500M AUM firms reporting cyber-driven valuation impacts. |
What Buyers Actually Look For
Here is what I have learned working across PE exit processes: buyers do not just check boxes. They look for evidence of operational maturity. A 24/7 monitoring SLA means nothing without incident logs proving you actually detected and responded to threats. A compliance certification means nothing without continuous evidence collection proving controls are active today, not just when the auditor visited six months ago.
The difference between “exit-ready” and “price negotiation risk” is documentation. Can you show a buyer 12 months of continuous monitoring data? Can you produce incident response timelines with real response metrics, not just a written plan? Can you demonstrate that compliance controls are actively monitored, not passively assumed?
How AI SOC Closes the Gaps
UnderDefense’s AI SOC is engineered to turn unchecked boxes into checks: 24/7 monitoring with documented 2-minute alert-to-triage and 15-minute escalation for critical incidents (criteria 1), automated compliance evidence generation for SOC 2, ISO 27001, and HIPAA (criteria 3), board-ready quantified risk reports with fund-level aggregation (criteria 4), and vendor-agnostic integration that builds governance evidence from Day 1 of deployment, not retroactively before exit.
Start deployment 12–18 months before projected exit, and the buyer’s diligence team finds an auditable, continuously monitored security program, not a hasty pre-sale cleanup.
💰 Scored below 6 across your portfolio? The governance evidence buyers expect takes 12–18 months to build credibly. Starting now with UnderDefense MAXI deployment is the fastest path to exit-ready cybersecurity posture, and the insurance premium savings begin immediately.
Q8. Why Traditional MDR Providers and MSSPs Fall Short for PE Portfolio Standardization
If you are evaluating portfolio-wide security, you have probably already considered the major names: Arctic Wolf for its concierge model, CrowdStrike for endpoint dominance, ReliaQuest for its platform approach, or a legacy MSSP for cost efficiency. Each is strong for individual companies. The challenge surfaces when you try to standardize across 10–20 companies with different tools, different maturity levels, and different needs. That is where architectural differences become portfolio-level deal-breakers.
❌ Where Traditional Providers Hit Structural Limits
Arctic Wolf delivers comprehensive MDR with dedicated concierge teams but requires proprietary SIEM replacement. For 15 portfolio companies with different SIEMs (Splunk, Sentinel, Elastic, none), that means 15 parallel migrations, millions in switching costs, and 12–18 months before standardized coverage.
CrowdStrike Falcon Complete is best-in-class for Falcon-native environments but only covers Falcon endpoints. Portfolio companies running SentinelOne, Microsoft Defender, or no EDR get no coverage.
ReliaQuest connects disparate tools well but stops at detection and escalation. Detection without response at portfolio scale means 3-person IT teams become the bottleneck at 2 AM.
Legacy MSSPs offer the lowest cost but deliver monitoring without intelligence: rigid playbooks, no organizational context, and no actual response capability.
✅ UnderDefense’s Architecture for PE Portfolios
- Vendor-agnostic integration with 250+ tools, no migration required
- Full detection AND response: analysts contain threats, not just escalate
- ChatOps user verification: analysts reach employees directly via Slack/Teams
- Fund-level governance dashboard: standardized LP-ready reporting across portcos
- Transparent pricing ($11–15/endpoint/month): predictable budgeting
- 30-day deployment per company: new acquisitions covered within the first month
PE Portfolio Standardization Requirements
| Requirement | Arctic Wolf | CrowdStrike Falcon Complete | Legacy MSSP | UnderDefense |
|---|---|---|---|---|
| Works with existing tools | ❌ Proprietary stack | ❌ Falcon-only | ⚠️ Limited | ✅ 250+ integrations |
| Full response capability | ✅ Yes | ✅ Endpoint-only | ❌ Escalation only | ✅ Full containment |
| Cross-portfolio dashboard | ⚠️ Single-tenant | ❌ No | ❌ No | ✅ Fund-level view |
| 30-day deployment | ❌ 3–6 months | ⚠️ If Falcon exists | ✅ Fast setup | ✅ 30 days |
| Transparent pricing | ❌ Contact sales | ❌ Contact sales | ⚠️ Varies | ✅ $11–15/endpoint |
| Compliance evidence | ❌ Separate | ❌ Separate | ❌ No | ✅ Included |
| Direct user verification | ❌ No | ❌ No | ❌ No | ✅ ChatOps |
Who Should Choose What
Choose Arctic Wolf if you are building from scratch with budget for SIEM migration everywhere. Choose CrowdStrike if every portco already runs Falcon. Choose a legacy MSSP if cost is the only variable. Choose UnderDefense if your portfolio runs different tools, you need standardized governance without rip-and-replace, and you want analysts who contain threats, not escalate tickets.
“The pre-sales crew is great. Really make you think you’ll get high tier support… The scan engine doesn’t function. I’m unable to scan our IP ranges, and they’ve ignored requests to get this resolved.”
— Verified User, Mid-Market Rapid7 – G2 Verified Review
“There have been several instances where we expected RC to identify an issue and no alert was surfaced. Senior leadership feels, at times, that RC isn’t the right partner for us.”
— Mike S., Information Security Manager Red Canary – G2 Verified Review
“Their team is proactive in identifying and addressing threats, providing 24/7 oversight… Their adherence to SLAs gives me confidence in our infrastructure’s protection.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
Q9. Evaluating AI SOC Providers for Your Portfolio: What to Look For
If you are evaluating AI SOC providers for portfolio-wide deployment, five architectural criteria separate solutions built for PE scale from those retrofitted for it.
Not all AI SOC or MDR providers can serve PE portfolios. The core requirement, standardizing security across diverse companies with different tools, industries, and maturity levels, eliminates most solutions that were built for single-company deployment. Kroll’s February 2026 report confirms the stakes: 94% of PE firms suffered financial impact from cybersecurity risk, with $2.1 million average impact per incident and 26% reporting reduced valuation or exit price due to cyber incidents. Half of all portfolio companies face elevated or high cyber risk exposure, according to the ACA Vantage Benchmarking Report analyzing 300+ portfolio companies across 18 industries.
What Separates PE-Grade AI SOC Providers
- Vendor-agnostic integration: Must work with whatever each portco already runs (Splunk, Sentinel, CrowdStrike, SentinelOne, Elastic, none) without requiring tool replacement. If a provider needs you to rip out existing SIEM across 15 companies, that is not portfolio-ready but a migration project disguised as a security solution.
- Full response capability: Must contain and remediate threats, not just detect and escalate. Detection without response at portfolio scale means your 3-person IT teams become the 2 AM bottleneck. You need analysts who act on threats, not dashboards that generate notifications.
- Fund-level governance reporting: Must provide standardized dashboards across all portfolio companies with LP-ready cyber health metrics. If the Operating Partner cannot pull a single, consolidated view of portfolio-wide posture, governance does not exist at the fund level, and LP reporting becomes a quarterly scramble.
- Deployment speed: Must deploy within 30 days per company to close the post-acquisition risk window. The 80% of PE firms that experienced disruption during the hold period cannot afford 6-month rollouts per acquisition. Speed to coverage is a portfolio-level risk variable.
- Transparent, scalable pricing: Must offer predictable per-endpoint pricing that enables portfolio-wide budgeting. “Contact sales” for every portco is not a pricing model but a negotiation tax that makes fund-level cost modeling impossible and prevents the IC from forecasting total security spend.
Matching Providers to Your Portfolio
The right AI SOC provider depends on your current tool landscape, company count, and governance requirements. A fund with 5 portfolio companies all running Microsoft Sentinel has different needs than one with 20 companies across 8 different security stacks. Score providers against these five criteria before shortlisting, and use the resources below to model costs and compare providers in detail.
This evaluation framework is based on documented deployment outcomes, G2 Spring 2025 rankings, published pricing, and operational results across 500+ MDR engagements spanning healthcare, financial services, SaaS, government, and manufacturing environments.
Q10. Building the Business Case for Your Investment Committee
Getting cybersecurity standardization approved by the Investment Committee requires one thing: translating security into portfolio economics. The IC does not evaluate MITRE ATT&CK coverage. They evaluate risk-adjusted returns. Your business case needs four numbers: current aggregate cyber risk exposure in dollars, projected cost avoidance (incidents + insurance + compliance penalties), exit value protection, and implementation cost with clear per-company economics.
❌ Three Ways IC Presentations Fail
- Framing cybersecurity as a cost line to minimize rather than a value creation lever leads to cheapest-possible per-company solutions with no fund-level benefit. This is the “penny wise, pound foolish” approach that leaves portfolios exposed.
- Running security company-by-company with no portfolio coordination means each portco reinvents the wheel, and the Operating Partner cannot report fund-level posture to LPs or the board. You end up with 15 different security vendors, 15 different SLAs, and zero standardized governance.
- Deferring the investment until a breach forces reactive spending at 5–10x the proactive cost. The most expensive decision is no decision. Kroll’s 2026 data confirms this: 80% of PE firms experienced disruption during hold period, with $2.1M average financial impact per incident and 26% reporting reduced valuation or exit price.
✅ The Right Evaluation Framework
Score each AI SOC option (0–2) on five criteria:
- Portfolio coverage flexibility: Works across heterogeneous tool stacks without requiring migration?
- Response capability: Contains threats autonomously, or only detects and escalates back to your team?
- Governance output: Auto-generates LP-reportable metrics and compliance evidence?
- Insurance impact: Demonstrably lowers premiums? MDR services reduce cyber insurance claims by 97.5% vs. endpoint-only protection, per Sophos research across 282 claims.
5. Exit readiness: 12+ months of deployment creates the documented audit trail buyers demand during diligence?
Solutions scoring 8+ represent genuine portfolio-wide risk reduction. Below 5 means you are buying per-company alert feeds, not standardized security governance.
Where UnderDefense Stands
| Criterion | Score | Why |
|---|---|---|
| Portfolio coverage flexibility | ✅ 2 | 250+ integrations; works with whatever each portco runs |
| Response capability | ✅ 2 | Full containment and remediation; 2-minute alert-to-triage and 15-minute escalation for critical incidents documented |
| Governance output | ✅ 2 | Fund-level dashboard with LP-ready metrics and compliance evidence |
| Insurance impact | ✅ 2 | 100% ransomware prevention record; documented 830% ROI over 3 years |
| Exit readiness | ✅ 2 | 30-day deployment creates 12+ months of audit trail before exit |
| Total | 10/10 |
UnderDefense is purpose-built as the AI SOC standardization layer PE firms need: vendor-agnostic, response-capable, governance-ready, insurance-optimizing, and exit-enabling. The architecture was designed for portfolio scale from day one, not retrofitted for it.
Your Next Step
Request a portfolio-wide security posture assessment or schedule a technical demo to see how UnderDefense MAXI integrates with your existing tool stacks across multiple portfolio companies. 30 days to operational security, not 12 months. Start with one portfolio company, validate the model, then roll out across the fund.
💰 100% ransomware prevention record across 500+ clients over 6 years. Published $11–15/endpoint/month pricing. 30-day deployment. 2-minute alert-to-triage and 15-minute escalation for critical incidents. These are documented outcomes, not claims, and we expect you to validate every one of them before you commit.
1. How does an AI SOC standardize cybersecurity across portfolio companies with completely different tech stacks?
We built our UnderDefense MAXI platform to be vendor-agnostic by design, integrating with 250+ security tools. This means each portfolio company keeps whatever it already runs, whether that is Splunk, Microsoft Sentinel, CrowdStrike, SentinelOne, Elastic, or no SIEM at all.
The standardization happens at the detection, response, and governance layer, not at the tool layer. Our concierge analysts learn each company’s unique context, users, and infrastructure within the first week. The reporting layer outputs the same governance dashboard format across every portco, with fund-level aggregation for the Operating Partner.
This architecture lets us serve a 50-person healthcare startup, a 2,000-endpoint SaaS platform, and a manufacturing company with no security team, all under one contract and one SLA.
2. What cybersecurity due diligence should PE firms conduct before acquiring a company?
We recommend running every acquisition target through a 7-point pre-acquisition cyber due diligence framework:
-
Security architecture review to map the full stack
-
Incident history with documented evidence, not verbal assurances
-
Regulatory exposure assessment (SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS)
-
Third-party and supply chain risk evaluation
-
Vulnerability posture including last penetration test results
-
Incident response maturity with an IR plan tested within 12 months
-
Cyber insurance coverage and claims history
These checkpoints align with VCI Institute frameworks and are increasingly expected by sophisticated buyers and insurance underwriters. Skipping any of them means inheriting unknown risk that surfaces post-close, often at the worst possible time.
3. How does cybersecurity risk affect private equity deal valuations and exit pricing?
The financial impact is documented and significant. Kroll’s February 2026 report found that 94% of PE firms suffered financial impact from cybersecurity risk, with $2.1 million average impact per incident. More critically, 26% reported reduced valuation or exit price specifically due to cyber incidents.
Our exit-readiness checklist identifies 8 governance criteria that buyers, LPs, and regulators now scrutinize. Portfolio companies scoring below 4 on these criteria face deal delays, repricing, or outright collapse. This aligns with data showing 44% of sub-$500M AUM firms reporting cyber-driven valuation impacts.
We engineered our AI SOC service to build exactly the documented audit trail that protects valuations: 12+ months of continuous monitoring data, incident response timelines with real response metrics, and active compliance evidence collection.
4. How quickly can AI SOC be deployed across newly acquired portfolio companies?
We deploy within 30 days per company. Here is the timeline we follow:
-
Days 1–30: Vendor-agnostic integration to existing tools, 24/7 monitoring established, initial threat assessment and vulnerability scan, critical gap identification (MFA gaps, unmanaged endpoints, patch debt)
-
Days 31–60: Detection rules aligned to fund-level policy, standardized incident response playbooks deployed, automated compliance evidence collection begins, portco integrated into fund-level governance dashboard
-
Days 61–90: Detection tuned to portco-specific context, proactive threat hunting launched, first quarterly cyber health report generated
This closes the post-acquisition monitoring gap within 30 days versus 6–12 months for traditional SOC buildouts. The 80% of PE firms that experienced disruption during the hold period cannot afford longer rollouts.
5. How does portfolio-wide AI SOC deployment reduce cyber insurance premiums?
MDR services reduce cyber insurance claims by 97.5% compared to endpoint-only protection, per Sophos research across 282 claims. When underwriters evaluate portfolio companies and find standardized 24/7 monitoring with documented incident response capabilities, they price risk lower across the entire fund.
Our 100% ransomware prevention record across 500+ clients over 6 years provides the documented evidence underwriters require. The MDR service generates continuous compliance evidence and incident logs that demonstrate operational maturity, not just tool deployment.
We have documented 830% ROI over 3 years across our client base, and a significant portion of that return comes from insurance premium reductions alongside incident cost avoidance and compliance penalty prevention.
6. Why do traditional MDR providers and MSSPs fall short for PE portfolio standardization?
The challenge is architectural. Most MDR providers were built for single-company deployment and hit structural limits at portfolio scale:
-
Arctic Wolf requires proprietary SIEM replacement. For 15 portfolio companies with different SIEMs, that means 15 parallel migrations and 12–18 months before standardized coverage.
-
CrowdStrike Falcon Complete only covers Falcon-native endpoints. Portfolio companies running SentinelOne or Microsoft Defender get no coverage.
-
ReliaQuest connects tools well but stops at detection and escalation, with no actual containment.
-
Legacy MSSPs deliver monitoring without intelligence: rigid playbooks, no organizational context, no response capability.
The PE requirement, standardizing governance across 10–20 diverse companies under one contract, eliminates providers that cannot integrate with heterogeneous tool stacks or provide fund-level reporting.
7. What should an Investment Committee business case for portfolio-wide cybersecurity include?
The IC evaluates risk-adjusted returns, not MITRE ATT&CK coverage. Your business case needs four numbers:
-
Current aggregate cyber risk exposure in dollars
-
Projected cost avoidance (incidents + insurance + compliance penalties)
-
Exit value protection based on documented governance maturity
-
Implementation cost with clear per-company economics
We see IC presentations fail in three predictable ways: framing cybersecurity as a cost line to minimize, running security company-by-company with no portfolio coordination, and deferring the investment until a breach forces reactive spending at 5–10x the proactive cost.
Score each provider option (0–2) on portfolio coverage flexibility, response capability, governance output, insurance impact, and exit readiness. Solutions scoring 8+ represent genuine portfolio-wide risk reduction. Use our SOC cost calculator to model fund-level deployment costs and compare build vs. buy scenarios.
8. What does an exit-ready cybersecurity posture look like for PE-backed companies?
Buyers, LPs, and regulators now scrutinize 8 specific governance criteria during exit diligence:
-
24/7/365 security monitoring with documented SLAs and incident logs
-
Incident response plan tested within the last 12 months
-
Current compliance certifications (SOC 2 Type II, ISO 27001, HIPAA, PCI DSS)
-
Board-level cybersecurity reporting with quantified risk metrics
-
Third-party risk management with documented vendor assessments
-
Vulnerability management with less than 30-day critical patch SLA
-
MFA enforced on all privileged accounts plus identity monitoring
-
Documented cyber insurance coverage with clean claims history
Portfolio companies scoring 7–8 see cybersecurity add value at exit. Those scoring 4–6 face price reductions or expanded indemnities. Below 3 risks deal delay or collapse. The governance evidence buyers expect takes 12–18 months to build credibly, which is why we recommend starting AI SOC deployment well before projected exit.
The post AI SOC for PE Portfolios: One Platform, 15 Portfolio Companies, Zero Rip-and-Replace appeared first on UnderDefense.