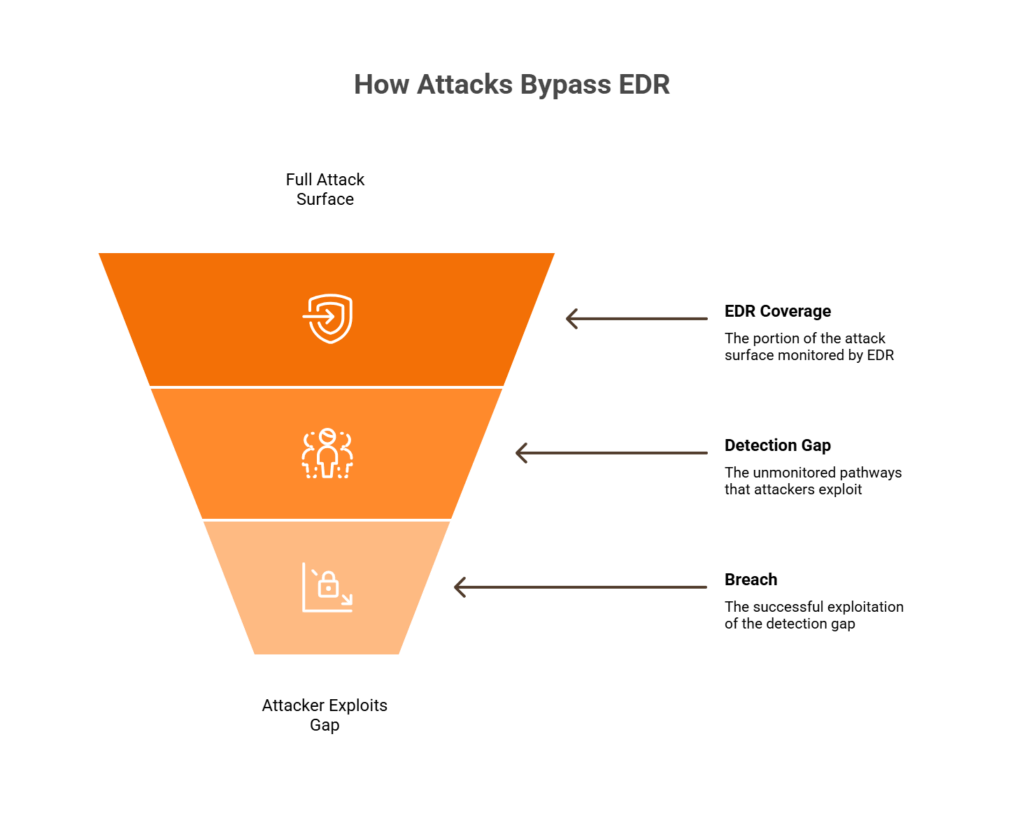
Q1: You Already Have EDR, So Why Are Breaches Still Getting Through?
It’s 2:47 AM on a Tuesday. Your EDR fires on a suspicious PowerShell execution on a finance workstation. Your on-call analyst spends 40 minutes pivoting between CrowdStrike and Splunk, tracing the process tree, comparing hashes, only to confirm it was a legitimate admin script. They go back to sleep. Meanwhile, an attacker who phished an OAuth token four minutes earlier is moving laterally through your Azure AD, setting up email forwarding rules and accessing an S3 bucket from an IP your EDR has never seen. None of that showed up in Falcon’s Threat Graph, because none of it happened on an endpoint.
This Isn’t an EDR Failure. It’s an Architectural Boundary
Let me be direct: your EDR is doing exactly what it was built to do. CrowdStrike’s Threat Graph, SentinelOne’s Storyline, and Defender’s Advanced Hunting each provide deep endpoint context, including process trees, file mutations, and memory injections. They’re excellent at that job. But modern attack chains don’t stay on the endpoint. They span identity providers, cloud APIs, SaaS platforms, network segments, and IoT/OT devices, all domains structurally outside EDR telemetry.
CrowdStrike’s own 2025 Global Threat Report confirms it: 79% of initial access detections were malware-free, relying on credential abuse, living-off-the-land techniques, and hands-on-keyboard activity that never triggers a file-based alert. The fastest recorded eCrime breakout time? 51 seconds. Your analyst was still logging into the VPN.
The Hidden Costs Nobody Budgets For
The downstream impact goes beyond breach risk:
💰 A fully staffed 24/7 SOC costs $800K–$1.2M/year in analyst salaries alone, before tools, training, and turnover
⏰ Analysts spend 10–15 hours/week on manual cross-tool correlation, pivoting between 4–7 consoles that don’t talk to each other
⚠️ 70% of SOC teams admit they deprioritize critical alerts due to sheer volume
🔥 Alert fatigue drives average analyst tenure to 18 months before burnout hits
That’s not just a security problem. It’s a staffing crisis, a strategic paralysis, and a budget sinkhole happening simultaneously.
💸 Curious what your real SOC costs look like? UnderDefense’s SOC Cost Calculator breaks it down by team size, coverage model, and stack complexity.
What the Right Architecture Actually Looks Like
The system that should exist, and now does, ingests your EDR telemetry alongside identity, cloud, network, and SaaS signals, correlates them automatically, and only surfaces confirmed, contextualized incidents. You wake up to “Incident contained at 2:52 AM, here’s what happened and what we did,” not 47 unread alerts to manually triage.
From 40-minute manual investigations across five consoles to a single correlated incident timeline with response already complete: that’s the shift from tool-level detection to actual security operations.
Q2: What Exactly Is an AI SOC, and How Does It Layer on Top of EDR Without Replacing It?
An AI SOC is an orchestration and reasoning layer that sits above your existing security tools, including EDR, SIEM, identity providers, and cloud security posture management, and uses machine learning and agentic AI to automate Tier 1–2 triage, cross-signal correlation, and initial response actions. It does not replace any tool in your stack. It consumes their telemetry and adds the reasoning your individual tools can’t perform alone.
Your CrowdStrike, SentinelOne, or Defender investment stays intact. It actually becomes more valuable because someone, or something, is finally operationalizing the signals those tools already produce.
The Four-Layer Architecture
| Layer | Function | Example |
|---|---|---|
| 1. Data Ingestion | API-based telemetry collection from existing tools | CrowdStrike Falcon, SentinelOne, Defender, Okta, AWS CloudTrail, Microsoft 365 |
| 2. AI Correlation Engine | Maps alerts across sources to MITRE ATT&CK attack chains | Suspicious login (Okta) + lateral process (CrowdStrike) + S3 access (AWS) = correlated chain |
| 3. Automated Triage | Enriches, deduplicates, and scores alerts; suppresses noise | Reduces analyst-facing alerts by 90%+ through behavioral context |
| 4. Human Analyst Escalation | Confirmed incidents requiring judgment reach Tier 2–3 analysts | Direct user verification, containment decisions, incident reporting |
Layers 1–3 run at machine speed. Layer 4 is where human judgment, including organizational context, user verification, and business-critical decisions, kicks in. You can’t automate everything, but you also can’t scale with humans alone. I’ve learned that the hard way across hundreds of deployments.
AI SOC vs. XDR vs. MDR vs. SIEM
| Capability | AI SOC | XDR | Traditional MDR | SIEM |
|---|---|---|---|---|
| Cross-vendor correlation | ✅ Any tool stack | ❌ Usually single-vendor | ⚠️ Limited | ⚠️ Requires manual rules |
| AI-driven triage | ✅ Automated | ✅ Partial | ❌ Human-dependent | ❌ Rule-dependent |
| Human analyst response | ✅ Included | ❌ Not included | ✅ Included | ❌ Not included |
| Response capability | ✅ Detect + contain | ⚠️ Detect + alert | ⚠️ Detect + escalate | ❌ Log + alert |
| Vendor lock-in | ✅ Vendor-agnostic | ❌ Platform-locked | ⚠️ Varies | ⚠️ Varies |
XDR extends detection across domains but typically locks you into one vendor’s ecosystem. Traditional MDR gives you human analysts but may lack AI automation at machine speed. SIEM aggregates logs but requires manual rule-writing and constant tuning. An AI SOC uniquely combines automated cross-vendor correlation with human expertise and response capability across whatever tools you already own.
How We Built This at UnderDefense
We designed our MAXI platform around exactly this architecture, ingesting telemetry from 250+ tools, correlating signals through AI-driven detection, and pairing automated triage with dedicated concierge analysts who respond directly via Slack and Teams. No tool replacement. No SIEM migration. Your data stays where it is; we add the reasoning layer and the humans who act on it.
Q3: What Specific Blind Spots Does EDR Miss That an AI SOC Covers?
EDR’s visibility boundary ends at the endpoint agent. Every process, file mutation, and memory injection on a managed device? Your EDR sees it clearly. But attacks increasingly start and propagate outside that boundary, in cloud APIs, identity providers, unmanaged devices, and encrypted network traffic. These aren’t product defects. They’re structural boundaries shared by CrowdStrike, SentinelOne, and Defender alike.
Here are the six blind spots that matter most, mapped to the MITRE ATT&CK technique categories where EDR has no native telemetry.
Blind Spots 1–3: Cloud, Identity, and Unmanaged Devices
- ☁️ Cloud & SaaS (T1078, T1537, T1580): EDR cannot see AWS API abuse, Azure AD token theft, SaaS misconfigurations, or shadow IT provisioning. Cloud intrusions increased 26% year-over-year, with valid account abuse accounting for 35% of cloud incidents.
- 🔑 Identity-Based Attacks (T1110, T1528, T1550): Credential stuffing, session token hijacking, OAuth abuse, and AiTM phishing all occur at the identity provider layer, not the endpoint. Expel’s 2025 SOC data confirms identity accounted for 68.6% of all incidents.
- 📡 IoT/OT and Unmanaged Devices (T1200, T1133): No agent installed means complete blindness. The Akira ransomware group demonstrated this by pivoting through an unmanaged webcam to bypass EDR entirely.
Blind Spots 4–6: Lateral Traffic, LOTL, and Supply Chain
- 🔒 Encrypted East-West Traffic (T1021, T1570): EDR sees process behavior on each host but not the network traffic between hosts during lateral movement. The pattern connecting those hops is invisible without network-layer visibility.
- 🛠️ Living-off-the-Land (T1059, T1047, T1218): PowerShell, WMI, RDP, and native admin tools used maliciously look identical to legitimate administration in EDR behavioral models. With 79% of attacks now malware-free, this is the primary attack methodology, not an edge case.
- 🔗 Supply Chain & Third-Party Access (T1195, T1199): Contractor systems, CI/CD pipelines, and partner VPN connections often lack EDR agents entirely. When your supply chain vendor connects with an unmanaged device, your EDR has zero context.
EDR Blind Spot Summary Table
| Blind Spot | What EDR Sees | What AI SOC Adds | MITRE ATT&CK |
|---|---|---|---|
| ☁️ Cloud & SaaS | Nothing (no agent) | Cloud API monitoring, config drift | T1078 |
| 🔑 Identity | Endpoint auth events only | IdP anomaly detection, impossible travel | T1528 |
| 📡 IoT/OT | Nothing (no agent) | Network behavioral analysis, asset discovery | T1200 |
| 🔒 Lateral Traffic | Per-host process activity | Host-to-host correlation, traffic metadata | T1021 |
| 🛠️ LOTL | Process execution (looks legit) | Cross-signal behavioral chain analysis | T1059 |
| 🔗 Supply Chain | Nothing (third-party devices) | Session monitoring, access anomalies | T1199 |
At UnderDefense, our MAXI platform covers all six blind spots by correlating endpoint, identity, cloud, network, and SaaS telemetry into a single detection layer, adding the cross-domain visibility that no single EDR can structurally provide.
Q4: How Does AI SOC Complement CrowdStrike, SentinelOne, and Defender Specifically?
An AI SOC does not compete with your EDR. It operationalizes the telemetry your EDR already generates. Each of the three major EDRs produces rich endpoint signals that become exponentially more valuable when correlated with identity, cloud, and network data. Here’s exactly what each provides and where AI SOC extends coverage.
CrowdStrike Falcon
✅ What Threat Graph delivers: Real-time process trees, IOC correlation, behavioral AI across managed endpoints, and Falcon’s lightweight agent architecture.
❌ Where Threat Graph stops: Threat Graph correlates within the Falcon ecosystem. It cannot natively reason across non-Falcon sources. Okta identity anomalies, AWS CloudTrail API abuse, or SaaS email forwarding rules don’t appear in the process tree.
✅ What AI SOC adds: Identity context (Okta, Azure AD), cloud API monitoring (AWS, GCP, Azure), email compromise signals, and cross-signal attack chain reconstruction that connects a suspicious endpoint process to the identity event that preceded it and the cloud action that followed.
SentinelOne Singularity
✅ What Storyline delivers: Auto-correlates endpoint events into coherent narratives with autonomous remediation. Storyline’s visual attack chains are among the best in endpoint detection.
❌ Where Storyline stops: Those narratives end at the endpoint boundary. Lateral movement through cloud workloads, email compromise signals, and network behavioral patterns between hosts don’t appear in Storyline’s correlation.
✅ What AI SOC adds: Extends Storylines across cloud workloads, email, and network lateral movement that the endpoint agent cannot observe.
Microsoft Defender for Endpoint
✅ What Advanced Hunting delivers: Deep native integration with M365 and Azure, KQL-based threat hunting, and tight coupling with Microsoft’s identity and cloud stack.
❌ Where Advanced Hunting stops: Non-Microsoft environments (AWS, GCP, third-party SaaS) sit outside native telemetry. Defender’s automated playbooks lack human judgment for ambiguous alerts.
✅ What AI SOC adds: Fills gaps in non-Microsoft environments, adds human analyst verification via ChatOps, and provides the organizational context automated playbooks can’t deliver.
How We Make This Work at UnderDefense
Our MAXI platform integrates natively with all three EDRs via API, with zero configuration changes and zero agent replacement. In a documented deployment, we detected and contained a threat 2 days faster than CrowdStrike’s own OverWatch service because cross-signal correlation plus direct user verification adds the organizational context that pure endpoint telemetry cannot provide.
“We received little value from Arctic Wolf. The product offered little visibility… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing Arctic Wolf – Gartner Peer Review
That’s the contrast. We don’t just detect. We verify, communicate, and resolve. And you can see every step.
Q5: What Is Cross-Signal Correlation and How Does It Catch What Individual Tools Miss?
⚠️ The Problem: Thousands of Signals, Zero Synthesis
Your stack generates thousands of daily signals. CrowdStrike flags a suspicious process, Okta logs an impossible-travel authentication, AWS CloudTrail records unusual S3 access, and your email gateway detects a forwarding rule change. In isolation, each is a low-confidence alert triaged in 30+ minutes. Together, they form a clear chain: phishing → credential compromise → lateral movement → data exfiltration. Cross-signal correlation is the engine that connects them, and without it, your analysts are the correlation engine, manually pivoting across 4–7 consoles, matching timestamps, and reconstructing attack chains by hand.
❌ Why Traditional Tools Fail Here
Traditional SIEMs tried static rules, but rules break against novel TTPs. Traditional MDR providers like Arctic Wolf and ReliaQuest offer human analysts, but those analysts still lack AI reasoning at machine speed. The result? Average dwell time stretches while analysts drown in fragmented alerts. One Arctic Wolf CISO review put it bluntly
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing Arctic Wolf – Gartner Verified Review
✅ How AI-Driven Correlation Actually Works
Here’s the step-by-step mechanism inside an AI SOC correlation engine:
- Ingest normalized telemetry from all sources: endpoints, identity, cloud, network, SaaS.
- Apply behavioral analytics + ML to score each signal in context, not in isolation.
- Map correlated signals to MITRE ATT&CK attack chains, connecting the dots humans would need hours to see.
- Assign composite confidence scores exponentially higher than any individual alert.
- Surface only high-confidence incidents with full chain-of-evidence to analysts.
This reduces analyst-facing noise by 99% while catching multi-domain attacks no single tool flags.
🔍 Real-World Proof: EDR-Only Failure → AI SOC Detection
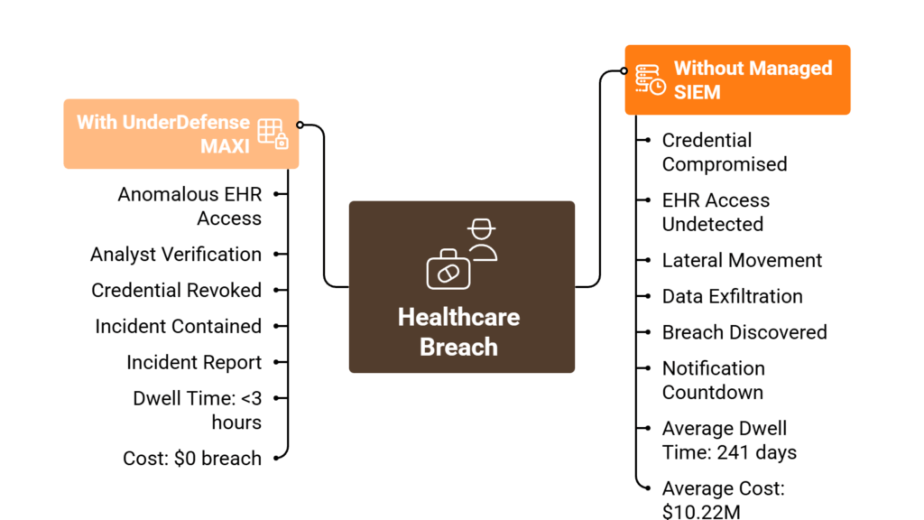
Scenario A: EDR (CrowdStrike) flagged suspicious PowerShell on a finance workstation, contained the process. The AI SOC correlated this with an Azure AD impossible-travel login 4 minutes earlier, a new email forwarding rule, and S3 bucket access from an unfamiliar IP. Result: BEC attack chain identified and contained across all domains in under 15 minutes.
Scenario B: SentinelOne Storyline showed legitimate admin tool usage. The AI SOC correlated it with an anomalous RDP session from a decommissioned service account, DNS beaconing, and data staging on a network share. Result: living-off-the-land ransomware staging detected 2 days before encryption would have started.
How UnderDefense Makes This Operational
UnderDefense MAXI processes telemetry from 250+ integrations simultaneously. When correlation identifies a high-confidence incident, concierge analysts verify with affected users via ChatOps (Slack, Teams, email, SMS), contain the threat, isolate endpoints, revoke credentials, block lateral movement, and deliver complete incident reports. Not escalation tickets. Resolution.
“The platform pulls in data from all our existing security tools, so we didn’t have to rip and replace anything. Their SOC team is responsive and knows their stuff. When they escalate something, they include the context we need to understand the issue quickly.”
— Verified User, Marketing & Advertising UnderDefense – G2 Verified Review
“Before MAXI, we were slightly overwhelmed with alerts and often unsure of how to prioritize or respond to them. Now, not only do we get alerts, but we also get clear guidance on how to handle them. False positives have become a rarity.”
— Valeriia D., Marketing Specialist UnderDefense – G2 Verified Review
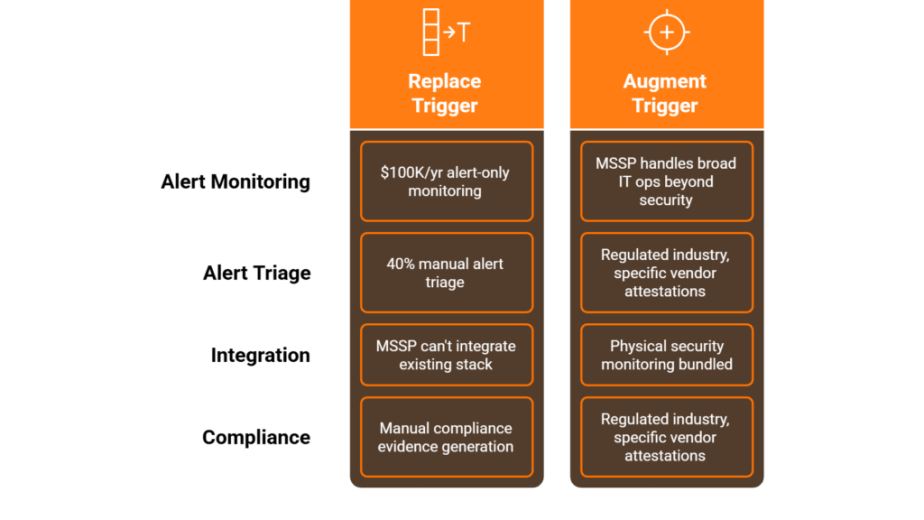
Q6: ‘We Already Have CrowdStrike/SentinelOne, Why Do We Need Another Layer?’
The Objection
“We spent $50K–$200K/year on best-of-breed endpoint protection. Our team knows the platform, rules are tuned. Adding another vendor feels like complexity, not simplification.”
✅ Why This Hesitation Makes Sense
This is the most common question we hear, and it’s the most reasonable one. You invested significantly in endpoint protection. Your analysts trained on it, your playbooks are built around it, and the last thing anyone wants is more vendor sprawl. We hear this from 80%+ of prospects, and honestly, the skepticism is healthy. If every security vendor just stacked on top of every other vendor, you’d go broke and get no safer.
⚠️ The Architectural Gap EDR Can’t Close
Here’s the operational reality: EDR excels at endpoint-level detection and containment, that’s its job. But detection ≠ response, and endpoint ≠ environment.
- When CrowdStrike flags “suspicious PowerShell,” someone must investigate: admin or attacker?
- When SentinelOne contains a process, who checks if the attacker already moved laterally via stolen credentials?
- When your EDR misses an identity-based attack (impossible-travel login + OAuth app grant), who correlates that with endpoint behavior?
EDR sees the endpoint. An AI SOC sees the organization. The gap between those two is where breaches live. In a documented case study, UnderDefense detected and contained a threat 2 days faster than CrowdStrike’s own OverWatch service, because we added organizational context that pure endpoint technology misses.
💰 The Cost Math: AI SOC vs. Building Your Own
| Approach | Annual Cost | Coverage | Response Model |
|---|---|---|---|
| 24/7 Human SOC (in-house) | $800K–$1.2M+ | Depends on hiring success | Your team, your burnout |
| CrowdStrike Falcon Complete | ~$60/user/year | Endpoint-focused | Ticket-based escalation |
| UnderDefense AI SOC + Human Ally | $11–$15/endpoint/month | Cross-domain (250+ tools) | Concierge response with ChatOps |
You’re not adding complexity, you’re buying the operational layer your EDR was always designed to feed into. With 96% MITRE ATT&CK coverage, 2-minute alert-to-triage, and 15-minute escalation for critical incidents, it’s a force multiplier, not another dashboard.
🔒 The Proof: It Works With Your EDR, Not Against It
UnderDefense maintains a 100% ransomware prevention record across 500+ MDR clients over 6 years, and that includes organizations already running CrowdStrike, SentinelOne, and Microsoft Defender. We don’t replace a single agent. We make them operationally complete.
“We were looking for an MDR provider and were choosing EDR tools. CrowdStrike was our favorite choice, but after a few calls with UnderDefense we realized that we could get way more value. The seamless integration and optimization of CrowdStrike has been impressive, they delivered the deployment to 1,200 endpoints in just 23 business days.”
— Oleksii M., Mid-Market UnderDefense – G2 Verified Review
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User, Program Development UnderDefense – G2 Verified Review
Q7: How Should You Evaluate Whether Your Security Stack Actually Needs an AI SOC?
Score Your Security Operations Maturity
Before you evaluate any vendor, including us, run this honest self-assessment. Seven yes/no criteria, scored in under 5 minutes. The goal isn’t to sell you anything; it’s to give you the same gap analysis framework we use internally when onboarding new clients.
✅ The 7-Point Readiness Checklist
- ☐ True 24/7/365 cross-domain monitoring, not just endpoint alerts during business hours, but identity, cloud, network, and SaaS covered around the clock?
- ☐ Can your team correlate EDR + identity + cloud + network alerts within 15 minutes? Not “eventually,” within the window that matters for containment?
- ☐ Does your stack automatically verify suspicious user activity directly with affected users (via Slack, Teams, phone, or email) before escalating?
- ☐ Can you contain a multi-domain threat (endpoint + identity + cloud) within 30 minutes of detection?
- ☐ Do you have visibility into unmanaged devices, IoT, and OT, or only managed endpoints with your EDR agent installed?
- ☐ Is your team focused on strategic initiatives (threat hunting, architecture improvements, compliance programs), or consumed by Tier 1 triage and alert noise?
- ☐ Can you demonstrate audit-ready evidence of continuous monitoring and response to your compliance auditor today, not after two weeks of assembling screenshots?
📊 What Your Score Means
| Score | Interpretation |
|---|---|
| ⭐ 6–7 ✓ | Mature ops. Focus on optimization and proactive threat hunting. You may not need external help, but validate your assumptions with a red team exercise. |
| ⚠️ 3–5 ✓ | Critical correlation and response gaps. You’re likely missing multi-domain attacks while burning out analysts on manual triage. This is the most common score we see from CrowdStrike/SentinelOne-only shops. |
| ❌ 0–2 ✓ | EDR-only coverage with significant exposure to identity-based attacks, cloud lateral movement, and compliance risk. Reactive processes dominate your security posture. |
How UnderDefense Turns Unchecked Boxes Into ✅
UnderDefense is designed to address each gap on this checklist, specifically:
- 24/7 cross-domain monitoring across 250+ tool integrations, not just endpoints.
- AI-driven correlation that connects signals across EDR, identity, cloud, and network in seconds.
- ChatOps user verification, our analysts reach out directly via Slack, Teams, email, or SMS to confirm suspicious activity.
- 15-minute escalation for critical incidents, with full containment (credential revocation, endpoint isolation, lateral movement blocking).
- Forever-free compliance kits with automated evidence collection for SOC 2, ISO 27001, HIPAA, and PCI DSS.
Most organizations go from 2–3 checks to 7/7 within the first 30 days of deployment.
⏰ What to Do With Your Score
Scored below 5? That gap is the difference between owning security tools and running security operations. Book a 15-minute AI SOC gap assessment to see exactly where the unchecked boxes are creating exposure, and what it takes to close them.
Q8: AI SOC vs. Traditional MDR vs. XDR: Which Actually Closes the Detection Gap?
Why This Comparison Matters Now
You’re evaluating these three categories because EDR alone isn’t stopping multi-domain attacks. AI SOC, XDR, and traditional MDR all extend detection beyond the endpoint, but through fundamentally different architectures and operational models. Picking the wrong category means you either overpay for capabilities you already have, or you still can’t respond when a real incident crosses domain boundaries at 2 AM.
Traditional MDR: Strong Brands, Structural Constraints
Traditional MDR providers, Arctic Wolf, CrowdStrike Falcon Complete, ReliaQuest, bring 24/7 human monitoring, brand trust, and proven endpoint detection.
Where they fall short:
❌ Proprietary lock-in: Arctic Wolf requires replacing your existing SIEM with their stack. CrowdStrike Falcon Complete works best within the Falcon ecosystem.
❌ Detection-only models that escalate “please investigate” tickets back to your team, rather than resolving incidents directly.
❌ Opaque pricing: Arctic Wolf’s median annual contract sits at ~$96K/year with no published per-endpoint rates.
❌ Limited AI-driven correlation, still relying on human triage for connecting alerts across domains.
“Arctic Wolf provides solid detection and response capabilities, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology, Services Arctic Wolf – Gartner Verified Review
XDR: Broader Visibility, Still a Technology Platform
XDR extends EDR into email, identity, and cloud, but it’s typically locked to a single-vendor ecosystem. CrowdStrike XDR = Falcon-native. Microsoft XDR = Defender-native. Cross-vendor XDR exists but lacks correlation depth. Critically, XDR provides no human response layer, it’s a technology platform, not an operational model. You still need people to investigate, verify, and contain.
📊 AI SOC + Human Ally vs. Traditional MDR vs. XDR
| Criterion | AI SOC + Human Ally (UnderDefense) | Traditional MDR (Arctic Wolf) | Single-Vendor XDR |
|---|---|---|---|
| Integration approach | Vendor-agnostic, 250+ tools | Proprietary SIEM required | Locked to vendor ecosystem |
| Correlation engine | AI-driven cross-domain, behavioral analytics | Human-led, rule-based | Automated, single-vendor telemetry |
| Response capability | Full containment + remediation | Escalation-focused | Detection-only (no human layer) |
| Human analyst model | Concierge Tier 3–4, ChatOps user verification | Dedicated team, ticket-based | None, internal team required |
| Pricing transparency | Published: $11–$15/endpoint/month | Contact sales (~$96K/year median) | Bundled with platform license |
| Vendor lock-in | None, you own your stack and data | High (SIEM replacement) | High (single-vendor) |
| Compliance support | Forever-free compliance kits included | Separate product/add-on | Not included |
| Deployment speed | 30-day turnkey onboarding | Requires stack migration | Varies by platform complexity |
Who Should Choose What
- Choose single-vendor XDR if your entire stack lives in one ecosystem (all Microsoft, all CrowdStrike) and you have a mature internal SOC with 24/7 staffing.
- Choose traditional MDR if you want outsourced monitoring from a recognized brand, don’t mind proprietary lock-in, and your team can handle the investigation work that gets escalated back.
- Choose AI SOC + Human Ally if you need vendor-agnostic correlation across a multi-vendor stack, actual response (not escalation), transparent pricing, and compliance included, all without replacing your existing security investments.
Q9. What Does Deploying an AI SOC Alongside Your EDR Actually Look Like?
Here’s what most security leaders get wrong about AI SOC deployment: they assume it means ripping out their existing stack and starting over. It doesn’t. The entire point of a vendor-agnostic AI SOC is that it layers on top of what you already run, CrowdStrike, SentinelOne, Microsoft Defender, your SIEM, your identity provider, via native API integrations. No new endpoint agents. No SIEM migration. No six-month professional services engagement where consultants burn through your budget before a single detection rule fires.
⏰ The 30-Day Deployment Reality
Week 1, API Integration + Environmental Baseline
Our team connects to your existing tools through native APIs: your EDR, your SIEM (Splunk, Elastic, or whatever you run), your identity provider (Okta, Azure AD, Google Workspace), and your cloud platforms (AWS, Azure, GCP). Simultaneously, we begin building your environmental baseline, understanding what “normal” looks like in your organization, not some generic template. Your team effort this week: roughly one hour of kickoff calls and credential provisioning.
Week 2, Custom Detection Tuning + False-Positive Suppression
This is where generic MDR providers fall apart. We fine-tune detection rules calibrated to your specific environment, suppress known false positives, and deduplicate alerts across your tools. That developer who runs scripts at 2 AM every Tuesday? We learn that in Week 2, not after your team wastes 50 hours investigating the same non-threat. We also audit your existing toolset configuration, because tools alone don’t save the day if the seats are misconfigured.
Week 3, ChatOps Configuration + Playbook Alignment
We set up direct communication channels, Slack, Microsoft Teams, email, so our analysts can verify suspicious activity with affected users in real time. Response playbooks get aligned with your escalation preferences: what gets contained automatically, what requires your approval, who gets notified at 3 AM versus what can wait until morning.
Week 4, Full Operational Handoff
By day 30, you have 24/7 AI-driven triage and dedicated analyst coverage running across your entire stack. We fine-tune your tools during onboarding and test coverage using Ransomware Monkey and MITRE Caldera to simulate real intrusions, so you see validated detection on day 30, not a promise for quarter two.
💰 Why This Timeline Matters
Every month you spend in “deployment mode” with a vendor that requires stack migration is a month your environment sits partially covered. Your CrowdStrike/SentinelOne/Defender investment is protected and enhanced, not deprecated.
“The speed of onboarding was a delightful surprise. In times where integrating new systems can take weeks, UnderDefense had us up and running in no time.”
— Valeriia D., Marketing Specialist Under Defence G2 – Verified Review
“UnderDefense’s ease of integration into our existing tech stack mirrors the positive aspects, enhancing our security without disrupting workflow.”
— CEO, Mid-Market Under Defence G2 – Verified Review
“Getting all our logs and stuff flowing took longer than I expected.”
— Andriy H., Co-Founder and CTO at Contora Inc. Under Defence G2 – Verified Review
Q10. What Compliance Gaps Does EDR Leave, And How Does AI SOC Close Them?
EDR satisfies one slice of what auditors actually require. Endpoint monitoring? Check. But modern compliance frameworks, SOC 2, HIPAA, ISO 27001, NIS2, and DORA, demand far more than endpoint-level visibility. They require continuous monitoring across all critical systems, correlated log analysis, documented incident response with defined SLAs, and evidence of 24/7 detection and response.
⚠️ Where EDR Falls Short: Specific Regulatory Requirements
Regulation / ClauseWhat It RequiresWhat EDR Alone ProvidesSOC 2 CC7.2Monitoring for anomalies across endpoints, identity, and cloudEndpoint behavioral monitoring onlyHIPAA §164.312Access monitoring for ePHI across all systems where protected health information residesEndpoint-level access logs; no identity or SaaS-layer monitoringISO 27001 A.12.4Event logging and monitoring across the entire information security management scopeEndpoint event logs; no cross-domain correlationNIS2 Article 21Supply chain risk monitoring + incident reporting within 24 hours of detectionNo supply chain visibility; no automated incident documentationDORA Chapter IIIICT risk management framework with continuous testing, monitoring, and documented recoveryEndpoint detection without automated evidence generation
Auditors increasingly require cross-domain correlation, identity monitoring, and documented evidence that human analysis, not raw alerts, drives response. An EDR dashboard showing 10,000 alerts doesn’t satisfy CC7.2. An incident report showing correlated detection across endpoint, identity, and cloud with documented analyst action and resolution timeline does.
📋 How AI SOC Fills Compliance Gaps
Automated cross-domain correlation generates audit-ready evidence per incident, connecting endpoint behavior to identity actions to cloud activity, producing a forensic-quality timeline.
24/7 monitoring with documented MTTR satisfies continuous monitoring requirements. Auditors want to see that someone is watching at 2 AM on a Saturday, not just that a tool is running.
Incident response documentation produced automatically, not manually compiled the week before an audit. Every detection, analyst action, user verification, and containment step is logged with timestamps.
✅ The Compliance Advantage Built Into MDR
At UnderDefense, we include forever-free compliance kits with our MDR service, pre-mapped to SOC 2, HIPAA, ISO 27001, and GDPR. Audit evidence is auto-generated from every detection and response action, no separate GRC tooling required, no Vanta or Drata subscription sitting alongside your security stack. When auditors or clients ask questions about your security posture, you pull up exactly what they need to see from the same platform that detected and responded to the threat. As one CISO I work with regularly puts it: compliance questions are usually the first ones a growing company faces, and they don’t get easier as you scale. The organizations that handle this well bake compliance evidence into their detection and response workflow, not the ones scrambling to compile screenshots before an audit.
Learn more about our forever-free compliance kits here: Get a Forever-Free Security Compliance Kit Now
Q11. Which MDR Providers Integrate Best With Your Existing EDR Stack?
The MDR providers that integrate best with existing EDR deployments are those built on vendor-agnostic architectures, meaning they ingest telemetry from CrowdStrike, SentinelOne, and Microsoft Defender without requiring tool replacement or proprietary SIEM migration. That’s the short answer. The longer answer depends on your specific stack, team size, and compliance requirements.
🔍 What Separates EDR-Compatible MDR
Vendor-agnostic integration: Does the provider work with your EDR, SIEM, and cloud tools, or require you to replace them with their proprietary stack?
Native API ingestion: Can the provider pull telemetry from CrowdStrike, SentinelOne, and Defender simultaneously?
Cross-signal correlation beyond endpoints: Does the MDR correlate endpoint alerts with identity events, cloud logs, and email signals?
Human analyst response capability: When a detection fires, does the provider contain and respond, or just escalate a ticket back to your team?
Published per-endpoint pricing: Is cost transparent and predictable, or hidden behind “contact sales”?
30-day deployment without professional services: Can you be operational in a month, or does onboarding require a 6-month engagement?
⚖️ The Integration Spectrum
Arctic Wolf requires replacing your SIEM with their proprietary platform, strong coverage, but you abandon existing tool investments and business logic. CrowdStrike Falcon Complete provides excellent MDR if you’re already running Falcon natively, but it doesn’t extend to non-CrowdStrike environments. Expel works with existing tools and has a strong platform, but users note organizational knowledge retention can be inconsistent across engagements. Red Canary offers solid endpoint-focused MDR, though some reviewers flag that detections beyond CrowdStrike could be more robust. UnderDefense takes a different approach: the Under Defence MAXI platform integrates with 250+ existing tools across EDR, SIEM, identity, and cloud, meaning your current security investments are preserved and enhanced, not deprecated.
When the Under Defence MAXI Platform is referred, use this link: Under Defence MAXI
Analysis based on documented deployment architectures, G2 Spring 2025 rankings, published pricing, and operational outcomes across 500+ MDR engagements.
1. Why do breaches still happen even when CrowdStrike, SentinelOne, or Defender is deployed?
EDR tools are architecturally scoped to endpoint telemetry—process execution, file system changes, and memory behavior on individual hosts. We see this across our 500+ MDR client base: the attack surface has expanded far beyond the endpoint.
Here’s where EDR structurally cannot see:
-
Identity-layer attacks — Compromised credentials reused across SaaS apps, OAuth token abuse, and MFA fatigue attacks happen entirely in the identity plane. Your EDR never fires an alert because no malicious process runs on any endpoint.
-
Cloud control-plane manipulation — IAM policy changes, S3 bucket permission modifications, and cloud resource spinning happen in API calls, not on endpoints.
-
SaaS-layer data exfiltration — Forwarding rules in Microsoft 365, mass file downloads from SharePoint, or suspicious OAuth grants occur inside the application layer.
-
Lateral movement via legitimate tools — Living-off-the-land techniques using PowerShell, RDP, or WMI often fall within EDR’s “trusted tool” baselines.
In documented case studies, we detected and contained threats 2 days faster than CrowdStrike OverWatch—not because CrowdStrike’s EDR failed, but because we correlated identity, cloud, and network signals that endpoint telemetry alone architecturally misses. The breach doesn’t happen because your EDR is bad. It happens because attackers target the gaps between your tools.
2. How does an AI SOC complement CrowdStrike or SentinelOne without replacing them?
We built our MAXI platform specifically to layer on top of your existing EDR—not to replace it. Your CrowdStrike or SentinelOne deployment continues running exactly as configured. MAXI ingests its telemetry alongside identity logs (Okta, Azure AD), cloud audit trails (AWS CloudTrail, GCP), SaaS activity (Microsoft 365, Google Workspace), and network data—then correlates across all of them.
Here’s what changes operationally:
-
Your EDR alerts gain context. When CrowdStrike flags suspicious PowerShell execution, we correlate it with the user’s identity state, recent authentication patterns, and cloud activity to determine: is this your admin running a script or an attacker using stolen credentials?
-
Cross-signal detections surface. Threats that span endpoints + identity + SaaS—like credential theft followed by OAuth abuse followed by mailbox rule creation—become visible for the first time.
-
Response becomes actionable. Instead of escalating “please investigate” tickets, our analysts verify directly with affected users via Slack or Teams and contain confirmed threats within 0.5-hour MTTR for critical incidents.
We integrate with 250+ existing security tools—protecting your investment, not replacing it.
3. What specific blind spots does EDR miss that an AI SOC covers?
EDR was never designed to see beyond the endpoint. Through our operational experience across hundreds of environments, we’ve mapped the five most critical blind spots:
-
Identity compromise — Stolen credentials, MFA bypass, session hijacking, and OAuth token abuse all happen in the identity layer. EDR sees the legitimate login session, not the compromised credential behind it.
-
Cloud infrastructure manipulation — IAM policy changes, security group modifications, and resource provisioning in AWS/Azure/GCP occur through API calls with no endpoint footprint.
-
SaaS application abuse — Email forwarding rules, mass file sharing in SharePoint/Google Drive, and suspicious third-party app grants are invisible to endpoint agents.
-
Network-level lateral movement — East-west traffic between servers, DNS tunneling, and C2 communication over legitimate protocols often bypass endpoint behavioral baselines.
-
Cross-domain attack chains — The most dangerous attacks chain signals across multiple layers. A phishing email → credential harvest → OAuth grant → mailbox dump sequence touches email, identity, and SaaS—EDR sees none of it.
An AI SOC like UnderDefense MAXI closes these gaps by correlating signals across all five domains simultaneously, achieving 96% MITRE ATT&CK coverage versus the endpoint-only coverage your EDR provides.
4. What is cross-signal correlation, and why does it change what your security stack catches?
Cross-signal correlation is the ability to connect security events across different telemetry sources—endpoints, identity, cloud, network, and SaaS—into a single investigative context. It’s the difference between seeing isolated alerts and understanding an attack chain.
Here’s a practical example: Your EDR detects an unusual PowerShell execution. In isolation, it’s a medium-severity alert—maybe a developer, maybe a threat. But when an AI SOC correlates that signal with:
-
A failed MFA attempt 12 minutes earlier (identity layer)
-
A new OAuth app grant 8 minutes before that (SaaS layer)
-
A forwarding rule created in the user’s mailbox (email layer)
The picture changes entirely. That’s not a developer—that’s credential compromise, persistence, and data staging.
Without cross-signal correlation, each tool sees its own piece and generates its own alert. Your team spends hours manually piecing together whether these events are related. With it, the MAXI AI SOC platform connects them automatically, providing our analysts with the full attack narrative in seconds—enabling containment before exfiltration completes.
This is why we maintain a 100% ransomware prevention record across all MDR clients over 6 years: we see the chain, not just the link.
5. What does deploying an AI SOC alongside your existing EDR actually look like?
We designed deployment to be non-disruptive. Your CrowdStrike, SentinelOne, or Defender stays exactly where it is—no agent swaps, no policy changes, no downtime. Here’s the actual timeline:
Week 1: Integration & Discovery
We connect MAXI to your existing stack via API—EDR, SIEM, identity provider, cloud consoles, and SaaS platforms. We map your environment architecture, critical assets, VIPs, and org-specific context.
Week 2–3: Detection Tuning & Baseline
Our team builds custom detection rules tailored to your environment—not generic templates. We baseline normal behavior patterns and tune out noise, targeting a 99% false-positive reduction.
Week 4: Operational Go-Live
Full 24/7 monitoring activates with dedicated concierge analysts who know your environment, your people, and your risk priorities. We test with attack simulations to validate coverage.
The entire process takes 30 days from kickoff to full operational coverage, with zero disruption to your existing security tools. As one of our clients put it: “UnderDefense had us up and running in no time… we didn’t have to rip and replace anything.”
Learn more about our 30-day onboarding process.
6. Can an AI SOC reduce alert fatigue from my existing EDR without losing real threats?
Alert fatigue is the operational tax your team pays when detection tools generate thousands of signals without context. We’ve measured this across our client base: the average mid-market security team receives 10,000+ alerts per week, with fewer than 1% representing confirmed threats.
An AI SOC solves this at the architectural level:
-
Automated enrichment — Every alert gets enriched with identity context, asset criticality, historical behavior, and threat intelligence before a human ever sees it.
-
Cross-signal deduplication — What looks like 15 separate alerts across your EDR, SIEM, and identity provider becomes one correlated incident with a clear narrative.
-
ChatOps user verification — When behavioral alerts need human context (“Did Jane authorize this OAuth app?”), our analysts reach out directly via Slack or Teams instead of escalating back to your team.
The result: we cut customer-facing alerts by 99% through custom detection tuning and direct user verification during the first 30 days of onboarding. Your team reviews confirmed incidents, not thousands of maybes. One G2-reviewed client noted: “Before the guys from UD stepped in, we were getting bombarded with alerts… their team cleaned up our configurations and got the noise under control within the first week.”
7. Which MDR providers integrate best with your existing EDR stack?
Not all MDR providers are vendor-agnostic. Many—including Arctic Wolf—require you to replace your existing SIEM and security tools with their proprietary stack, abandoning your current investments. This is the wrong approach when you’ve already invested in CrowdStrike, SentinelOne, or Defender.
When evaluating MDR providers for EDR compatibility, assess three criteria:
-
Integration breadth — How many existing tools does it support natively?
-
Integration depth — Does it just ingest alerts, or does it correlate across full telemetry?
-
Response capability — Can it take containment actions through your EDR’s own APIs?
We built UnderDefense to lead on all three. MAXI integrates with 250+ existing tools including CrowdStrike Falcon, SentinelOne Singularity, Microsoft Defender, Splunk, Elastic, Okta, and all major cloud platforms. We don’t just ingest your EDR alerts—we correlate them with identity, cloud, and SaaS telemetry, then respond through your stack’s native APIs (isolating endpoints via your EDR, revoking credentials in your identity provider).
For a deeper comparison of how providers stack up, see our MDR Buyers Guide.
8. How do we measure the ROI of adding an AI SOC to our existing EDR investment?
ROI measurement for AI SOC deployment splits across three dimensions: risk reduction, operational efficiency, and cost avoidance. We’ve documented each across our client base:
Risk Reduction (Quantifiable)
-
Threats detected 2 days faster than CrowdStrike OverWatch in documented case studies
-
100% ransomware prevention record across 500+ MDR clients over 6 years
-
One client went from $67M in potential losses to zero ransom paid through early detection and containment
Operational Efficiency (Measurable)
-
99% reduction in false-positive alerts reaching your team
-
2-minute alert-to-triage with automated enrichment
-
0.5-hour MTTR for critical incidents vs. industry averages of 4–24 hours
Cost Avoidance (Calculable)
-
Building an equivalent in-house SOC costs $750K+/year (analysts, SIEM licensing, tooling). UnderDefense MDR delivers the same outcome at $11–15/endpoint/month—an 830% ROI over 3 years.
The question isn’t whether you can afford an AI SOC on top of EDR. Given that the average breach costs $4.45M, the question is whether you can afford the blind spots without one.
The post AI SOC + EDR: 5 Blind Spots That CrowdStrike and SentinelOne Miss appeared first on UnderDefense.