Q1: You Spent Six Figures on Your SIEM, So Why Is Everyone Talking About AI SOC?
Here’s the uncomfortable truth most vendors won’t tell you: your SIEM investment is not failing, but incomplete. Organizations have poured $100K to $500K+ into platforms like Splunk, Elastic, and Microsoft Sentinel. These systems ingest terabytes of logs, satisfy compliance requirements, and power executive dashboards. By every procurement metric, the project succeeded.
⚠️ The Alert Factory Problem
But here’s what the dashboard doesn’t show you: the operational reality underneath. SOC teams receive upwards of 11,000 alerts daily, and research shows nearly one-third are false positives, with duplicates and redundant noise making up most of the rest. The Verizon 2024 DBIR found that in 74% of breaches, alerts were generated but ignored because analysts were simply overwhelmed by volume. Your six-figure investment created the world’s most expensive alert factory.
Traditional MDR providers and MSSPs haven’t solved this either. Arctic Wolf, ReliaQuest, and similar providers function as escalation layers on top of the noise. They receive your alerts, apply basic triage, and send tickets back to your team that say “please investigate.” That is not response, but delegation. MSSPs offer monitoring without actionable context: checkbox coverage based on rigid playbooks rather than real-time threat intelligence.
The Architectural Shift That Actually Matters
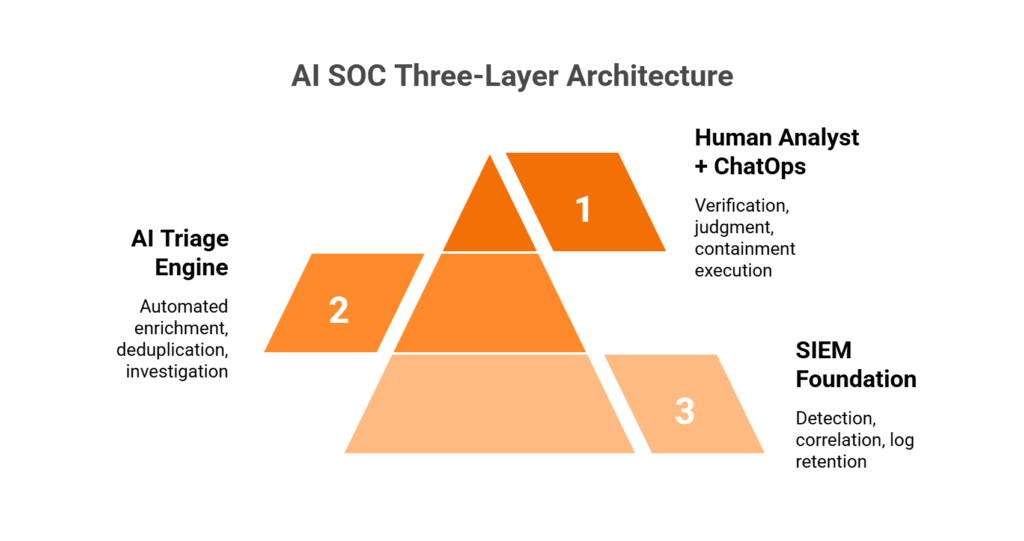
The industry is undergoing a structural transformation, and it is not about adding another tool to the stack. The competitive advantage in 2026 is not having security tools. It is having a system that can reason across them. Detection without response is noise. Response without context is risk. The organizations pulling ahead are the ones deploying systems that correlate alerts across endpoints, identity, cloud, and network, verify suspicious activity with the actual humans involved, and take containment action before an analyst opens a laptop.
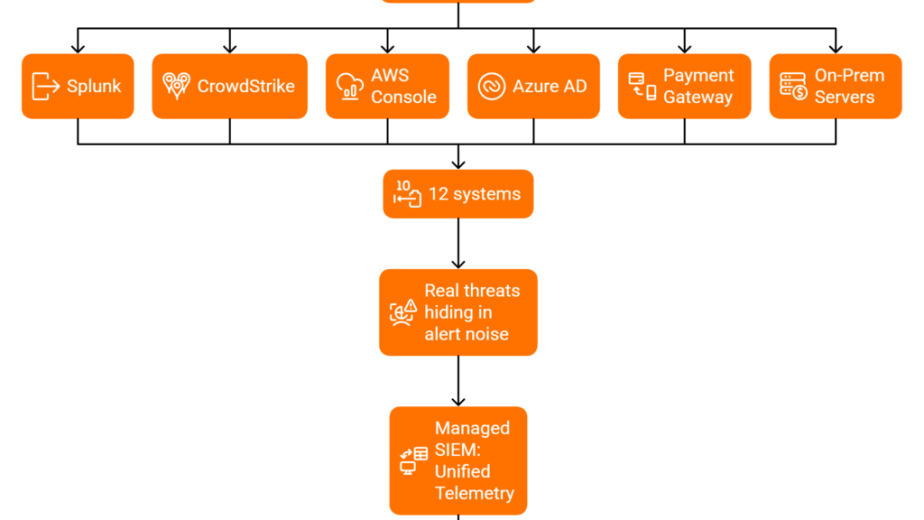
How MAXI Completes What Your SIEM Started
This is the architecture we built at UnderDefense. The UnderDefense MAXI platform sits on top of your existing SIEM, whether that’s Splunk, Elastic, Sentinel, or whatever you’re running, without vendor lock-in. It connects to 250+ security tools via native integrations, enriches alerts with threat intelligence and behavioral context, and drives alert-to-triage in under 2 minutes. When a suspicious login needs verification, our analysts reach out directly via Slack, Teams, or email through ChatOps. The SIEM keeps doing what it does. Your compliance stays intact. Your team stops drowning.
✅ The Results Speak Louder Than Claims
The proof is not in a marketing slide. It is in documented outcomes. UnderDefense maintains zero ransomware cases across all MDR customers over six years. In a head-to-head scenario, our team detected and contained a cyberthreat 2 days faster than CrowdStrike OverWatch while integrating with, not replacing, the customer’s existing CrowdStrike deployment. Enterprise SIEMs only cover 24% of MITRE ATT&CK techniques on average; MAXI delivers 96% coverage using a detection-as-code approach: Python-based, version-controlled, unit-tested, and CI/CD-deployed. Your SIEM was a solid foundation. The AI SOC + Human Ally model is what makes it operationally complete.
Q2: Do I Need an AI SOC If I Already Have Splunk, Elastic, or Sentinel?
“We already spent $200K on Splunk. Why would we add another platform on top of it?”
✅ Your Skepticism Is Good Security Leadership
Fair question. And honestly, if you’re asking it, that’s a sign of healthy security leadership. Tool fatigue is real: every vendor promises to “unify” your stack while adding one more console to manage. After years of procurement cycles, budget justifications, and team training, hesitation is not weakness. It is evidence that you’re protecting an investment that matters.
But here’s the operational reality that changes the equation: your SIEM was never designed to investigate, verify, or contain. It was built to aggregate logs, correlate events, and generate compliance reports, and it does those things exceptionally well. The problem is not what your SIEM does. It is what happens after the alert fires.
📌 The Camera System vs. Response Team Analogy
Think of it this way: your SIEM is a camera system. It captures everything, records it for evidence, and triggers when motion is detected. An AI SOC is the response team: the people who watch the feed, verify whether the person on camera is a delivery driver or an intruder, and act accordingly. You wouldn’t rip out the cameras because you hired a guard. And you wouldn’t expect the cameras to tackle an intruder.
How MAXI Works With, Not Against, Your SIEM
UnderDefense MAXI ingests alerts via your SIEM’s native API. It enriches them with threat intelligence, maps to MITRE ATT&CK, and either auto-resolves confirmed noise or escalates to our dedicated analysts for human verification and response without touching your log storage, your data lake, or your compliance reporting. Your Splunk/Elastic/Sentinel investment stays fully intact. MAXI completes the workflow that your SIEM was never architected to finish.
⏰ What Happens in the First 30 Days
During a 30-day onboarding, we remove 99% of alert noise through custom detection tuning calibrated to your specific environment. Your team goes from triaging thousands of “maybes” to reviewing only confirmed incidents that require their decision.
“Their team cleaned up our configurations and got the noise under control within the first week. Now when we get an alert, we know it’s something worth looking into. The platform pulls in data from all our existing security tools, so we didn’t have to rip and replace anything.”
— Verified User, Marketing and Advertising UnderDefense G2 – Verified Review
“UnderDefense also helped us navigate key compliance requirements, ensuring we met industry standards smoothly and efficiently. What stood out the most was their responsiveness and flexibility, no matter the issue, they tackled it quickly and professionally.”
— Arman N., CTO, Mid-Market UnderDefense G2 – Verified Review
Request a technical architecture walkthrough for your specific SIEM. We expect you to validate before you commit.
Q3: What Does Your SIEM Actually Do, and Why Was It Built to See, Not to Act?
It’s 2:47 AM on a Tuesday. Your phone buzzes with an impossible-travel alert from Splunk. Someone authenticated in Helsinki, then Lagos, eight minutes apart. You log in, pull up the raw logs, cross-reference with VPN configurations, and 45 minutes later confirm it’s a split-tunnel issue. A developer on a legitimate connection. You’ve been awake for an hour investigating what should’ve been auto-verified in seconds. Sound familiar?
What Your SIEM Does Well
Give your SIEM credit where it’s earned. These platforms are powerful for what they were designed to do:
| Capability | What It Delivers |
|---|---|
| Log ingestion & normalization | Aggregates data from endpoints, cloud, network, and identity into a central store |
| Rule-based & behavioral correlation | Matches events against detection logic to surface anomalies |
| Compliance reporting | Generates evidence for HIPAA, SOC 2, ISO 27001, and PCI-DSS audits |
| Threat intelligence integration | Enriches events with external IOC feeds |
| Dashboards & visualization | Provides operational and executive-level views of security posture |
❌ Where Your SIEM Stops
The gap becomes visible when you map what your SIEM does against what your security operations need:
| Your SIEM Does | Your SIEM Doesn’t |
|---|---|
| Detects anomalies | Investigate root cause |
| Fires alerts | Verify with affected users |
| Correlates across logs | Contain or isolate threats |
| Stores data for compliance | Orchestrate response actions |
| Sees everything | Act on anything |
This is not a product flaw. It is an architectural reality. SIEMs were born in the early 2000s as log management and compliance tools. The architecture was designed to aggregate and correlate, not investigate and respond. The gap between detection and action was meant to be filled by humans. But alert volume has outpaced human capacity by orders of magnitude.
💸 The Hidden Costs Nobody Budgeted For
- 10 to 15 hours/week per analyst spent on manual alert triage and investigation
- 74% of breaches had alerts that were generated but ignored due to volume
- 18-month average tenure before SOC analyst burnout and turnover
- Dwell time increases 3x when analysts are overwhelmed with noise
- Enterprise SIEMs only cover 24% of MITRE ATT&CK techniques on average, meaning three-quarters of adversary techniques have no detection rule at all
✅ From 45-Minute Investigations to Morning Summaries
Now reimagine that 2:47 AM scenario. The impossible-travel alert fires. Instead of waking you, the system pings the user via Slack at 2:48 AM: “Did you just authenticate from Lagos?” User responds “No.” Within seconds, the account is isolated, credentials revoked, and endpoint quarantined. By morning, you review a structured incident report: what happened, when, how it was contained, and what follow-up is recommended. That’s the shift from seeing to acting, and it’s exactly what UnderDefense MAXI’s ChatOps verification resolves for alerts that SIEMs generate but cannot close.
Q4: How Does an AI SOC Layer on Top of Your SIEM Without Replacing It?
MAXI operates as a unified SecOps layer on top of any SIEM, XDR, or EDR, with full customer data ownership and zero vendor lock-in.
⚙️ The 5-Step Integration Flow
Here’s exactly how it works, step by step:
- Alert Ingestion MAXI connects to your SIEM (Splunk, Elastic, Sentinel) via native alert API. No log duplication, no data re-routing. Your SIEM fires the alert; MAXI receives it.
- Automated Context Enrichment AI queries your logs, enriches with external threat intelligence, correlates across identity/endpoint/cloud/network telemetry, and maps every finding to the MITRE ATT&CK framework.
- ChatOps User Verification When behavioral alerts need human context (“Did you authorize this OAuth app at 2:41 AM?”), analysts reach out directly via Slack, Teams, email, or SMS. No ticket. No waiting. Direct verification.
- Structured Investigation Report Every investigation step is documented and auditable. Reports are generated in seconds, not hours, with full evidence chain, timeline, and analyst reasoning.
- Response & Containment Confirmed threats trigger immediate action through your existing tool APIs: credential revocation via Okta/Azure AD, endpoint isolation via CrowdStrike/SentinelOne, and network blocking via firewall integrations.
🔒 Why This Architecture Matters
Your SIEM is preserved. Logs stay in your data lake. Compliance reporting remains untouched. MAXI is available on-prem or in your cloud environment (AWS, Azure, GCP, or Oracle), so data sovereignty is never a question. You’re not migrating to a new platform. You’re adding a Tier-1/2 analyst team operating at machine speed, 24/7, that escalates only when real human decisions are needed.
Detection-as-Code: Show, Don’t Tell
Our detection logic is not a black box. Every detection rule is written in Python, version-controlled in Git, unit-tested, and deployed through CI/CD pipelines. If you want to see why an alert fired, you read the code. If you want to modify detection behavior, you submit a pull request. This is how we achieve 96% MITRE ATT&CK coverage compared to the enterprise SIEM average of 24%. The gap is not your SIEM’s fault. It is that most organizations can’t staff the engineering team needed to write, test, and maintain thousands of detection rules. That’s the engineering capacity MAXI provides.
“The biggest problem they solved was our 24/7 coverage gap. We needed round-the-clock monitoring for compliance reasons, but building our own SOC wasn’t realistic with our budget and the current hiring market. UnderDefense fills that gap without us having to hire a full team.”
— Verified User, Marketing and Advertising UnderDefense G2 – Verified Review
“We recently worked with UnderDefense on a penetration testing project, and the experience exceeded our expectations. Their team provided us with clear and detailed insights into security vulnerabilities, along with practical recommendations on how to fix them. This level of transparency made it easy for our team to take action.”
— Arman N., CTO, Mid-Market UnderDefense G2 – Verified Review
The question is not whether your SIEM works. It does. The question is whether you’ve operationalized it. MAXI doesn’t replace your security investments. It makes them do what you bought them to do.
Q5: What Does Integration Look Like Across Splunk, Elastic, and Sentinel?
One of the most common questions we hear from security leaders evaluating an AI SOC is: “Will it actually work with our SIEM, or do we need to rip and replace?” The answer depends entirely on the provider’s architecture. Here’s a breakdown of how UnderDefense MAXI integrates across the three dominant SIEMs: Splunk Enterprise Security, Elastic Security, and Microsoft Sentinel, along with how each compares to vendor-locked alternatives.
⚙️ Three-SIEM Integration Comparison
| Capability | Splunk ES | Elastic Security | Microsoft Sentinel |
|---|---|---|---|
| Alert Source Format | Notable events via REST API / HEC | Detection rules → Elasticsearch alerts | Incidents from analytics rules |
| API Method | REST API + HTTP Event Collector | Detection Engine API | Graph Security API + Sentinel Incident API |
| Data Residency | Data stays in your indexers | Data stays in your Elasticsearch cluster | Data stays in your Azure tenant |
| Response Actions | Splunk SOAR or direct APIs | Custom actions via Elastic API | Logic Apps / Entra ID / Defender |
| Onboarding Timeline | ~30 days | ~30 days | ~30 days |
| Compliance Ownership | Customer retains full ownership | Customer retains full ownership | Customer retains full ownership |
Splunk ES: Notable Events, Your Indexers
MAXI ingests Splunk notable events through the REST API and HTTP Event Collector. Your data never leaves your indexers: detection logic and correlation rules stay where you built them. This matters because, as Nazar has emphasized in practitioner conversations, “all of my business logic stays with me” if a vendor change ever becomes necessary. Providers like Deepwatch are tightly coupled to Splunk’s ecosystem, which can create expensive lock-in when your ingestion costs scale. UnderDefense works with your Splunk deployment: response actions route through Splunk SOAR or direct API calls, without requiring proprietary infrastructure on top.
Elastic Security: Detection Engine, No Premium Tier Required
For Elastic environments, MAXI connects via the Detection Engine API, pulling alerts generated by your custom detection rules directly from Elasticsearch. Elastic’s own EASE (Elastic AI Security for Endpoints) is vendor-locked to the premium tier. UnderDefense provides vendor-neutral triage and enrichment regardless of your Elastic license level, with no forced upgrade to access managed detection.
Microsoft Sentinel: Cross-Stack, Not Endpoint-Only
Sentinel incidents flow into MAXI through the Graph Security API and Sentinel Incident API. Response actions execute via Logic Apps, Entra ID, and Microsoft Defender. Where endpoint-focused providers like Red Canary stop at endpoint telemetry, UnderDefense correlates across identity, network, SaaS, and cloud, giving analysts the full context to verify and contain threats across your Microsoft ecosystem.
🔧 30-Day Onboarding: Validate Before You Commit
Every integration follows the same 30-day onboarding framework: toolset audit, custom detection tuning against your environment, and ransomware simulation using tools like MITRE Caldera and Infection Monkey. The goal is observable outcomes from day one, not a six-month deployment cycle that delays time-to-value.
Q6: What Changes When Alerts Get Triaged in Seconds Instead of Hours?
⏰ The Monday Morning You Already Know
It’s Monday at 8:47 AM. You open your laptop to 847 alerts that stacked up over the weekend. Your Tier 1 analyst starts triaging, manually, one by one. Three hours later, they’ve found two real issues and cleared 80% as false positives. But buried in the noise was a lateral movement attempt that started Saturday at 1:14 AM. By the time anyone notices, the attacker has been inside for 40+ hours.
Now picture the alternative: you open your laptop to three pre-investigated incident reports. Verification was completed directly with the affected users via Slack. Containment was executed at 3:12 AM Saturday. Your team reviews confirmed incidents over coffee instead of triaging raw alerts under pressure.
Why Manual Triage Breaks Down
The bottleneck was never detection speed but investigation bandwidth. Manual triage is linear: one analyst, one alert, 15 to 45 minutes per investigation. AI-driven triage runs in parallel, with thousands of alerts enriched, correlated, and deduplicated simultaneously. The SANS Institute reports that 64% of alerts are false positives, and SOC teams process only about 50% of their total alert volume. That means half your alerts go uninvestigated every single day.
💸 The Hidden Costs Nobody Budgets For
When triage is slow, the downstream costs compound fast:
- 200+ day average dwell time when investigation bandwidth is exhausted
- 83% analyst burnout rate, driving 18-month average tenure before turnover
- +$1.2M in breach costs when containment exceeds 200 days
- 25% of analyst time consumed by routine triage that could be redirected to threat hunting and strategic work
✅ What Changes with an AI SOC
With UnderDefense MAXI, the shift is measurable: 2-minute alert-to-triage, 15-minute critical escalation SLA, and a documented 830% ROI over three years. The team transitions from alert processors to threat hunters: the work they were hired to do.
“Before the guys from UD stepped in, we were getting bombarded with alerts from all our security tools. Their team cleaned up our configurations and got the noise under control within the first week. Now when we get an alert, we know it’s something worth looking into.”
— Verified User in Marketing and Advertising UnderDefense – G2 Verified Review
“Before MaxiMDR, we were slightly overwhelmed with alerts and often unsure of how to prioritize or respond to them. Now, not only do we get alerts, but we also get clear guidance on how to handle them. This has significantly reduced our response time.”
— Valeriia D., Marketing Specialist UnderDefense – G2 Verified Review
“UnderDefense MAXI has been a key player in helping us maintain a secure environment. It has significantly reduced the number of false positives, allowing our team to focus on real threats.”
— Darina I., Customer Success Manager UnderDefense – G2 Verified Review
847 alerts → 3 reports. That’s the shift from noise to managed outcomes, and UnderDefense customers report 95%+ alert noise reduction in month one.
Q7: If I Already Have SOAR Playbooks, Do I Still Need an AI SOC?
“We built 50+ SOAR playbooks in Phantom/XSOAR. Why add AI on top?”
Validate the Investment First
This is one of the smartest objections we hear, and it deserves a real answer. If you’ve built 50+ playbooks, you’re ahead of 80% of organizations. That represents months of engineering time, deep operational knowledge, and a genuine commitment to automation. The investment is real and valuable. Nobody should dismiss it.
⚠️ Where Deterministic Playbooks Hit a Ceiling
SOAR excels at known patterns: predefined decision trees that execute reliably when inputs match expectations. Disable an account when impossible travel is detected. Isolate a host when malware detonates. Block an IP when threat intel matches.
But here’s the operational reality: what happens when the alert requires judgment? Impossible travel: is it a VPN, a compromised credential, or an employee who actually flew to Tokyo? SOAR can’t ask the user. A new OAuth app was granted access at 2:41 AM: authorized by IT or by an attacker? SOAR can’t reason across novel patterns. It can’t adapt when the attacker does something your playbook didn’t anticipate.
Legacy SOAR platforms suffer from rigid, linear playbook execution, limited scalability across multi-cloud environments, integration gaps that fragment visibility, and high maintenance requirements for scripting and rule tuning. That 60 to 70% “gray zone” of alerts that fall outside clean playbook coverage? That’s where threats live, and where SOAR goes silent.
✅ SOAR + AI SOC: Complementary, Not Redundant
UnderDefense MAXI doesn’t replace your SOAR investment. It extends it. MAXI includes SOAR-as-a-Service with 85+ automation integrations, plus agentic AI for the gray zone, plus human analyst judgment for edge cases that neither playbooks nor algorithms should handle alone.
| Capability | SOAR Alone | SOAR + AI SOC |
|---|---|---|
| Known-pattern response | ✅ Excellent | ✅ Excellent |
| Adaptability to novel threats | ❌ Requires manual playbook updates | ✅ Agentic AI reasons across new patterns |
| User verification | ❌ Cannot contact affected users | ✅ ChatOps via Slack/Teams/Email |
| Gray-zone coverage | ❌ Silent on ambiguous alerts | ✅ AI enrichment + human triage |
| Maintenance overhead | ⚠️ High (manual scripting & tuning) | ✅ Continuous tuning by dedicated analysts |
The Practitioner’s Frame
Automation without intelligence is just faster noise. Your SOAR handles the 30% of alerts with clean, deterministic responses. An AI SOC handles the 70% that need context, verification, and judgment, then feeds those learnings back into your playbooks to make them smarter over time.
Q8: What Does an AI SOC Actually Cost vs. Scaling Your SIEM Team Alone?
💰 The Real Cost of “Just SIEM”
Scaling a SIEM-only SOC sounds straightforward until you run the numbers. Here’s what the line items actually look like for a mid-market organization:
- Additional Tier 1 analyst: $70K to $100K/year + benefits (total loaded cost: $85K to $120K)
- 24/7 coverage minimum: 4 to 5 FTEs to cover shifts = $400K to $600K/year in analyst labor alone
- SIEM license scaling: Splunk runs $50K to $90K/year at 50GB/day ingestion; enterprise deployments at 500GB/day reach $600K+ in licensing
- SOAR platform licensing: $50K to $150K/year for platforms like XSOAR or Splunk SOAR
- Analyst turnover replacement: $30K to $50K per hire in recruiting, onboarding, and ramp time, with 18-month average tenure driving constant churn
Total for a fully staffed, 24/7 in-house SOC with SIEM: $700K to $1.2M/year before you account for management overhead, training pipelines, or tool sprawl. UnderDefense’s SOC Cost Calculator lets you model these numbers against your specific environment.
💸 The AI SOC Layer Cost
UnderDefense publishes transparent pricing: $11 to $15 per endpoint per month. For a 1,000-endpoint organization, that’s approximately $132K to $180K/year for full 24/7 AI-powered detection, triage, and human analyst response, versus $600K+ for equivalent in-house capability.
Most competitors hide their pricing behind “contact sales” gates. Arctic Wolf’s median annual contract runs approximately $96K but requires proprietary SIEM replacement. CrowdStrike Falcon Complete pricing varies significantly and bundles EDR licensing. UnderDefense is the only provider in this tier that publishes per-endpoint rates and lets you calculate costs before a single sales call.
✅ ROI Framework: Three Numbers That Matter
| ROI Component | Calculation |
|---|---|
| FTE reduction | Reduce 4 to 5 Tier 1 FTEs to 1 senior analyst + AI SOC = ~$300K to $420K saved/year |
| Risk reduction value | Breach cost avoidance ($4.88M avg) × probability reduction from 24/7 coverage |
| Productivity recovery | 25% analyst time redirected from triage to threat hunting and strategic work |
UnderDefense documents 830% ROI over three years across its MDR client base, driven by FTE optimization, faster containment (reducing breach cost exposure), and the compounding value of proactive threat hunting.
The Math You Can Run Yourself
UnderDefense’s published pricing and SOC Cost Calculator let you model the exact math for your environment, with no “contact sales” required. Plug in your endpoint count, your current analyst headcount, and your SIEM spend. The breakeven point for most mid-market organizations lands within the first 90 days.
Q9: Where Does AI SOC Fall Short? Honest Limitations Every Buyer Should Know
Here’s something you won’t hear from most AI SOC vendors: their technology has real, measurable blind spots. AI-powered triage is not omniscient, and pretending otherwise is how vendors lose trust and customers lose data. Transparency about these limits is exactly what separates providers who protect you from providers who oversell you.
We tell every prospective customer this upfront at UnderDefense, because the fastest way to erode a security partnership is to overpromise what automation can actually do. Over a decade in this space has taught me that the vendors who hide their limitations are the ones who fail you at 2 AM when something novel hits your environment.
⚠️ Where AI Triage Hits Its Ceiling
There are four specific scenarios where AI SOC automation struggles, and where the human element becomes non-negotiable:
- Novel zero-day attack chains. AI models are trained on known patterns: MITRE ATT&CK TTPs, historical telemetry, and behavioral baselines. When a truly novel technique emerges (think a zero-day chained with living-off-the-land binaries in an unexpected sequence), AI detection can lag behind. This is exactly why we pair every AI investigation with Tier 3 to 4 human analysts, not AI-only triage. The AI catches the anomaly; the human confirms the novelty and determines the correct containment action.
- Ambiguous behavioral alerts without user verification. If ChatOps channels aren’t configured, or the affected user simply doesn’t respond to a verification prompt, the automated workflow stalls. A suspicious login from an unusual geography is flagged, but without the user confirming “that wasn’t me,” the AI can’t close the loop with confidence. Human escalation becomes the fallback, and that’s by design, not a failure.
- Complex multi-stage attacks spanning weeks. AI excels at real-time correlation: matching indicators across SIEM, EDR, and cloud logs within minutes. But sustained APT campaigns, where an attacker moves laterally over days or weeks while blending into normal traffic patterns, require human threat hunting across long timelines. No model replaces an experienced analyst who can stitch together a three-week narrative from fragmented breadcrumbs across disparate log sources.
- Compliance-specific judgment calls. AI can flag anomalies all day long, but regulatory interpretation (“Is this a reportable incident under HIPAA?” or “Does this trigger GDPR’s 72-hour notification window?”) requires human expertise and legal context every single time. Compliance is not a detection problem but fundamentally a judgment problem that no model can fully automate.
🔍 Why “AI SOC + Human Ally” Exists
This is exactly why we built the “AI SOC + Human Ally” model, not “AI SOC, period.” Every AI investigation inside UnderDefense MAXI is observable and auditable. Every escalation reaches a human analyst who knows your organization, your users, and your risk profile. The AI handles speed and scale; the human handles judgment and context.
Compare this to what happens when AI operates as a black box. ReliaQuest’s own documentation acknowledges that limited transparency in AI decision-making “erodes trust and makes it difficult to justify actions during audits or post-incident reviews.” When tickets come back without clear reasoning, security teams lose confidence in the system they’re paying to protect them.
Our 100% ransomware prevention record across 500+ clients exists precisely because we don’t trust AI alone. Our analysts override, escalate, and verify where automation can’t. That’s not a limitation of the model but the architecture working exactly as designed.
Q10: How Should You Evaluate an AI SOC That Protects Your Existing SIEM Investment?
Choosing the wrong AI SOC doesn’t just waste budget. It adds complexity without reducing workload, or worse, creates new vendor lock-in that undermines the SIEM investment you’ve already made. The evaluation mistake most teams make is filtering by integration count or brand recognition while ignoring the factors that actually determine operational outcomes.
❌ The Wrong Way to Evaluate
Most buyers evaluate AI SOC providers by checking a features matrix: “How many integrations? What’s the brand? Do they have AI?” This approach ignores what actually matters in day-to-day operations: data sovereignty, response capability beyond alert escalation, user verification workflows, investigation transparency, and whether the provider works with your existing stack or forces you to replace it.
A CISO who picks a provider based on logo recognition and ends up migrating off their existing SIEM six months later hasn’t gained security. They’ve gained a migration project with a bigger attack surface during the transition window.
✅ The 7-Criteria Evaluation Framework
Here’s the framework that separates AI SOC providers who protect your investment from those who quietly replace it:
| # | Evaluation Criterion | What to Look For | Max Score |
|---|---|---|---|
| 1 | SIEM Preservation | Works on top of your existing SIEM (Splunk, Sentinel, QRadar, and Elastic) without requiring replacement | /2 |
| 2 | Data Residency | Logs and AI processing stay in your data lake; no mandatory third-party cloud shipping | /2 |
| 3 | User Verification / ChatOps | Direct user communication (Slack, Teams) to validate suspicious activity before escalation | /2 |
| 4 | Response Capability | Full containment and remediation, not just “alert and escalate” | /2 |
| 5 | Investigation Transparency | Every AI decision is auditable with a complete investigation trail | /2 |
| 6 | Pricing Predictability | Published per-endpoint pricing; no hidden overage fees or “contact sales” black boxes | /2 |
| 7 | Onboarding Speed | Operational within 30 days on existing tools, not 90+ days with stack migration | /2 |
📊 How Top Providers Score
| Provider | SIEM Preservation | Data Residency | ChatOps | Response | Transparency | Pricing | Onboarding | Total |
|---|---|---|---|---|---|---|---|---|
| UnderDefense | ✅ 2 | ✅ 2 | ✅ 2 | ✅ 2 | ✅ 2 | ✅ 2 | ✅ 2 | 14/14 |
| Arctic Wolf | ❌ 0 | ❌ 1 | ❌ 0 | ✅ 2 | ❌ 1 | ❌ 1 | ❌ 1 | 6/14 |
| CrowdStrike Falcon Complete | ❌ 1 | ✅ 2 | ❌ 0 | ✅ 2 | ❌ 1 | ❌ 0 | ✅ 2 | 8/14 |
| ReliaQuest | ✅ 2 | ✅ 2 | ❌ 0 | ❌ 1 | ❌ 1 | ❌ 1 | ❌ 1 | 8/14 |
Arctic Wolf requires proprietary SIEM replacement: every customization, every alert tuning, and every change must route through their engineering team. CrowdStrike Falcon Complete delivers strong endpoint response but remains Falcon-native, missing organizational context beyond the endpoint. ReliaQuest preserves your SIEM but has documented transparency gaps where, as one CISO reviewing Arctic Wolf on Gartner noted, “Analysts provide little context, and when asked for more information in the investigation nothing is ever provided.”
💡 The Real Question
The real question is not which AI SOC has the most features but which one protects your existing investment while closing the detection-action gap. If your evaluation doesn’t weight these seven criteria, you’re optimizing for the wrong outcomes.
Q11: Looking for the Right AI SOC to Layer on Your SIEM?
The leading SOC-as-a-Service providers for organizations keeping their existing SIEM include UnderDefense, Arctic Wolf, CrowdStrike Falcon Complete, Expel, and Deepwatch, each with distinct integration philosophies, response models, and pricing structures.
🔄 How SOCaaS Has Evolved
SOCaaS has moved well beyond basic 24/7 monitoring into a market where the real differentiators are integration flexibility (vendor-agnostic vs. proprietary stack), response capability (detection-only vs. full containment), pricing transparency, and whether the provider works with your SIEM or forces replacement. Choosing the wrong model means paying for a service that adds another dashboard on top of your existing dashboards, without actually reducing your team’s operational workload or closing the detection-to-response gap.
The shift matters because organizations that already invested six or seven figures in a SIEM platform shouldn’t be forced to abandon that investment just to get 24/7 analyst coverage. The right SOCaaS layers on top, not instead of.
✅ What Separates Top Providers
When evaluating SOCaaS providers for an existing SIEM environment, focus on these operational differentiators:
- Vendor-agnostic integration vs. proprietary stack Does the provider connect to your Splunk, Sentinel, or Elastic instance, or require a full migration to their proprietary platform?
- Human analyst access Direct communication via Slack/Teams in a concierge model vs. ticket-based queues with multi-day response times and no direct analyst contact?
- Published response SLAs Are mean-time-to-detect and mean-time-to-respond numbers documented, contractually guaranteed, and independently verifiable?
- Transparent pricing vs. “contact sales” Can you find per-endpoint pricing published on the website, or do you need three discovery calls and an NDA to get a ballpark quote?
- Compliance support Is compliance reporting and audit-readiness documentation included in the base service, or sold as an expensive professional services add-on?
🔗 Which Provider Fits Your Scenario
Each provider excels in different operational scenarios. The right choice depends on your current SIEM investment, the integration depth you require, whether your team needs detection-only support or full incident response ownership, and your tolerance for vendor lock-in.
Analysis based on documented response times, G2 2025 rankings, and operational outcomes across 500+ MDR deployments.
Q12: FAQ: AI SOC + SIEM, Quick Answers
What happens to your SOC team after AI takes over Tier-1 triage?
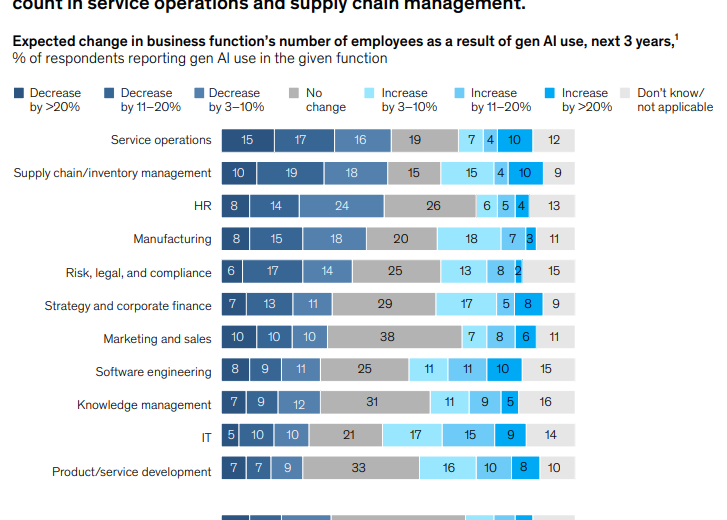
Your team doesn’t shrink. It levels up. AI eliminates the Tier-1 grunt work that burns out analysts fastest: alert triage, false-positive investigation, initial enrichment, and repetitive ticket routing. When that workload disappears, your people can finally do the work they were actually hired to do.
⏰ Where Recovered Time Goes
Here’s what the shift looks like in practice across organizations that have made this transition:
- ~25% of analyst time recovered and redirected toward proactive threat hunting and detection engineering.
- Analysts shift from “alert processor” to “incident commander,” owning outcomes instead of processing queues.
- Detection-as-code becomes possible: analysts write and version detection rules in Python/YAML via CI/CD pipelines, making your detection posture auditable, testable, and continuously improving.
- Retention improves significantly when the role becomes strategic rather than repetitive. Nobody quits a job where they’re hunting APTs; they quit when they’re closing 200 false positives a day.
⭐ The Proof
UnderDefense’s 1% customer churn and 113% net dollar retention tell the story clearly. Teams that make this shift don’t go back. As one G2 reviewer put it:
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., Enterprise CIO UnderDefense – G2 Verified Review
Can AI SOC work with on-premises SIEM deployments?
Yes, and this is a critical differentiator for regulated industries. UnderDefense MAXI can operate on-prem or within customer-specific cloud environments (AWS, Azure, GCP, and Oracle). Logs and AI-processed data stay in your data lake, not ours.
🔒 How On-Prem Deployment Works
- On-prem deployment preserves full data sovereignty for regulated industries: healthcare, financial services, government, and defense contractors where data residency is not optional but a legal requirement.
- No log data is shipped to third-party clouds unless the customer explicitly opts in and configures the data flow themselves.
- Integration uses the same API methods whether the SIEM is cloud-hosted or on-prem, so the detection and response workflow remains identical regardless of deployment architecture.
✅ Real-World Proof
UnderDefense helped a US Government organization reduce threat response time to 9 minutes, using on-prem infrastructure with full data residency compliance. That’s not a theoretical benchmark but a documented operational outcome on sovereign infrastructure.
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.” — Oleg K., Director of Information Security UnderDefense – G2 Verified Review
How long does it take to deploy AI SOC on top of an existing SIEM?
UnderDefense’s standard deployment is 30 days, including toolset audit, custom detection tuning, and validation testing. Not 90 days. Not “it depends.” Thirty days from contract signature to fully operational SOC coverage.
📋 The 30-Day Onboarding Timeline
- Week 1 to 2: Integration setup, log source mapping, and baseline alert profiling across your existing SIEM, EDR, and cloud tools.
- Week 2 to 3: Custom detection rules deployed, ChatOps configuration (Slack/Teams), and playbook alignment with your incident response procedures.
- Week 3 to 4: Ransomware simulation (using frameworks like Caldera or Infection Monkey), validation testing against real-world attack scenarios, and tuning to cut up to 99% of alert noise.
⚡ Why Competitors Take Longer
Compare this to Arctic Wolf, which requires proprietary SIEM replacement, meaning your “onboarding” is not deployment at all but a full-stack migration. Or ReliaQuest, which often requires extensive professional services engagements before reaching full operational status. UnderDefense’s 30-day onboarding works with your existing tools, not instead of them.
“The speed of onboarding was a delightful surprise. In times where integrating new systems can take weeks, UnderDefense had us up and running in no time.” — Valeriia D., Marketing Specialist UnderDefense – G2 Verified Review
Who audits the AI’s decisions? Is AI SOC transparent?
Every investigative step MAXI takes is observable and auditable. Unlike competitors that operate as black boxes, UnderDefense provides full transparency into AI reasoning, analyst actions, and the complete decision chain from initial detection through final resolution.
🔍 What Transparency Actually Looks Like
- Complete investigation audit trail for every alert, from initial detection through enrichment, correlation, and final disposition.
- AI decisions are reviewable, not opaque model outputs. Security teams can see exactly what data was used, how the conclusion was reached, and what triggered escalation.
- Detection logic managed as code: versioned in Git, testable in staging environments, and fully explainable to auditors. No “trust the algorithm” hand-waving.
- This contrasts sharply with documented issues at competitors. One CISO reviewing Arctic Wolf on Gartner noted: “Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated. Support incidents are not worked to completion and communication evaporates.”
✅ Why This Matters
Transparency is why UnderDefense maintains a 100% ransomware prevention record, because observable AI plus accountable humans catch what black-box automation misses. If you can’t audit your AI SOC’s decisions, you don’t have a security tool. You have a liability waiting to be exposed in your next compliance audit.
1. Can an AI SOC layer on top of my existing SIEM without replacing it?
Yes. An AI SOC is designed to layer on top of your existing SIEM, not replace it. Your SIEM handles what it was built for: log ingestion, correlation, and detection rule execution. The AI SOC adds what your SIEM cannot do alone, which is automated triage, enrichment, user verification, and response at machine speed.
We built UnderDefense MAXI to connect natively with Splunk Enterprise Security, Elastic Security, and Microsoft Sentinel through their existing APIs. Your data stays in your indexers, your Elasticsearch cluster, or your Azure tenant. No log shipping to third-party clouds. No mandatory platform migration.
This matters because your SIEM investment represents months of detection engineering, custom correlation rules, and deep institutional knowledge. Ripping that out to adopt a vendor-locked alternative means losing business logic you can’t rebuild overnight. An AI SOC preserves that investment and extends it with 24/7 automated investigation, ChatOps-based user verification, and human analyst judgment for edge cases.
The onboarding follows a 30-day framework that includes toolset audit, custom detection tuning, and ransomware simulation, so you see measurable outcomes from day one.
2. How does AI SOC integration work with Splunk, Elastic, and Microsoft Sentinel?
Each SIEM integration follows a different API pathway, but the principle is the same: the AI SOC connects to your existing environment without requiring proprietary infrastructure on top.
For Splunk, MAXI ingests notable events through the REST API and HTTP Event Collector. Detection logic and correlation rules stay in your indexers. Response actions route through Splunk SOAR or direct API calls.
For Elastic Security, MAXI connects via the Detection Engine API, pulling alerts generated by your custom detection rules directly from Elasticsearch. This works regardless of your Elastic license level, with no forced upgrade to access managed detection.
For Microsoft Sentinel, incidents flow through the Graph Security API and Sentinel Incident API. Response actions execute via Logic Apps, Entra ID, and Microsoft Defender. The AI SOC correlates across identity, network, SaaS, and cloud, giving analysts full cross-stack context.
All three integrations follow the same 30-day onboarding timeline and preserve full customer data residency and compliance ownership.
3. What is the real cost of an AI SOC vs. scaling an in-house SOC team?
A fully staffed, 24/7 in-house SOC with SIEM runs $700K to $1.2M per year for a mid-market organization. That includes 4 to 5 Tier 1 FTEs ($400K to $600K in analyst labor), SIEM license scaling ($50K to $600K+ depending on ingestion volume), SOAR platform licensing ($50K to $150K), and constant analyst turnover at $30K to $50K per replacement hire.
UnderDefense publishes transparent pricing at $11 to $15 per endpoint per month. For a 1,000-endpoint organization, that translates to approximately $132K to $180K per year for full 24/7 AI-powered detection, triage, and human analyst response. That is roughly 75% less than equivalent in-house capability.
We document 830% ROI over three years across our MDR client base, driven by FTE optimization, faster containment reducing breach cost exposure, and compounding value from proactive threat hunting. Our SOC Cost Calculator lets you model the exact math for your environment before a single sales call.
4. How does an AI SOC reduce SIEM alert fatigue?
SIEM alert fatigue happens because your SIEM generates alerts at scale, but your team investigates them one at a time. The SANS Institute reports that 64% of alerts are false positives, and SOC teams process only about 50% of their total alert volume. That means half your alerts go uninvestigated every single day.
An AI SOC breaks this bottleneck by running triage in parallel. UnderDefense MAXI enriches, correlates, and deduplicates thousands of alerts simultaneously, delivering 2-minute alert-to-triage and 15-minute critical escalation SLA. Customers report 95%+ alert noise reduction in month one.
The operational shift is dramatic. Instead of opening your laptop Monday morning to 847 raw alerts, your team reviews three pre-investigated incident reports. Verification was completed directly with affected users via Slack. Containment was executed automatically at 3 AM. Your analysts spend their time on threat hunting and detection engineering instead of clearing false positives under pressure.
5. Do I still need SOAR playbooks if I deploy an AI SOC?
Yes, and your SOAR investment becomes more valuable with an AI SOC, not less. If you have built 50+ playbooks, that represents months of engineering time and deep operational knowledge. We never recommend discarding that work.
SOAR handles the 30% of alerts with clean, deterministic responses: disable an account on impossible travel, isolate a host on malware detonation, block an IP on threat intel match. An AI SOC handles the 70% gray zone where alerts require judgment, context, and user verification that rigid playbooks cannot provide.
UnderDefense MAXI includes SOAR-as-a-Service with 85+ automation integrations, plus agentic AI for novel patterns, plus human analyst judgment for edge cases. The AI SOC also feeds learnings back into your existing playbooks, making them smarter over time.
The frame we use with practitioners: automation without intelligence is just faster noise. SOAR plus AI SOC is complementary, not redundant.
6. What are the honest limitations of an AI SOC?
We tell every prospective customer this upfront: AI SOC automation has real, measurable blind spots.
There are four specific scenarios where AI triage hits its ceiling. First, novel zero-day attack chains where AI models trained on known patterns lag behind truly unprecedented techniques. Second, ambiguous behavioral alerts without user verification, where the automated workflow stalls if ChatOps channels are not configured or the user does not respond. Third, complex multi-stage attacks spanning weeks, where sustained APT campaigns require human threat hunting across long timelines. Fourth, compliance-specific judgment calls where regulatory interpretation requires human expertise every single time.
This is exactly why we built the “AI SOC + Human Ally” model. Every AI investigation inside MAXI is observable and auditable. Every escalation reaches a human analyst who knows your organization, your users, and your risk profile. Our 100% ransomware prevention record across 500+ clients exists precisely because we do not trust AI alone.
7. How long does it take to deploy an AI SOC on top of an existing SIEM?
UnderDefense’s standard deployment is 30 days from contract signature to fully operational SOC coverage.
The timeline breaks down into three phases. Week 1 to 2 covers integration setup, log source mapping, and baseline alert profiling across your existing SIEM, EDR, and cloud tools. Week 2 to 3 includes custom detection rules deployment, ChatOps configuration via Slack or Teams, and playbook alignment with your incident response procedures. Week 3 to 4 involves ransomware simulation using frameworks like Caldera or Infection Monkey, validation testing against real-world attack scenarios, and tuning to cut up to 99% of alert noise.
Compare this to providers like Arctic Wolf, which require proprietary SIEM replacement, meaning your “onboarding” becomes a full-stack migration. Or ReliaQuest, which often requires extensive professional services engagements before reaching full operational status. We work with your existing tools, not instead of them. The goal is observable outcomes from day one, not a six-month deployment cycle.
8. How should I evaluate AI SOC providers to protect my existing SIEM investment?
We recommend a 7-criteria evaluation framework that separates AI SOC providers who protect your investment from those who quietly replace it.
The seven criteria are: SIEM preservation (works on top of your existing SIEM without replacement), data residency (logs stay in your data lake), user verification via ChatOps (Slack and Teams integration for validating suspicious activity), full response capability (containment and remediation, not just “alert and escalate”), investigation transparency (every AI decision is auditable), pricing predictability (published per-endpoint rates with no hidden fees), and onboarding speed (operational within 30 days on existing tools).
Score each provider on a 0 to 2 scale per criterion. UnderDefense scores 14/14 across all seven. Arctic Wolf scores 6/14 due to proprietary SIEM replacement requirements. CrowdStrike Falcon Complete scores 8/14 with strong endpoint response but Falcon-native limitations. Use our evaluation checklist to run this assessment against any provider on your shortlist.
The post Do I Need AI SOC If I Have SIEM? Keep Your Stack, Close the Response Gap appeared first on UnderDefense.