Q1: Do You Actually Need Managed SIEM If You Already Have EDR?
The Short Answer: Yes, But Not for the Reasons Vendors Tell You
Here’s the direct answer: if you’re running CrowdStrike, SentinelOne, or Microsoft Defender, you already have excellent endpoint detection. That’s not the question. The question is whether endpoints are your only attack surface and they’re not. Network traffic, cloud APIs, identity logs, and compliance requirements all exist beyond what any EDR agent can architecturally see. The real question isn’t “EDR or SIEM” it’s “what visibility gaps remain after EDR?”
I’ve watched this play out dozens of times. A security leader deploys world-class EDR, feels confident, then gets blindsided by an attack that moved laterally through network protocols or exploited identity federation things their endpoint agents never saw because they couldn’t see them.
What Your EDR Sees vs. What It Misses
Your EDR excels at endpoint behavioral analysis process execution, file system changes, memory forensics. But here’s what it’s architecturally blind to:
- ❌ East-west network lateral movement attackers pivoting between systems via SMB, RDP, or WMI that EDR agents can’t monitor
- ❌ Cloud control plane activity AWS/Azure/GCP administrative actions happen outside endpoint scope entirely
- ❌ Identity federation events Okta, Azure AD, Active Directory authentication anomalies
- ❌ SaaS application access patterns OAuth grants, suspicious data exports through sanctioned apps
- ❌ IoT/OT and unmanaged devices you can’t install agents on printers, cameras, or industrial controllers
- ❌ Compliance log aggregation SOC 2, HIPAA, and PCI-DSS require centralized retention EDR doesn’t provide
These aren’t EDR failures, they’re scope limitations. CrowdStrike can’t see what happens on your network switches. SentinelOne can’t monitor your identity provider. Microsoft Defender can’t track cloud API calls in AWS.
How We Approach This at UnderDefense
At UnderDefense, we built the MAXI platform to unify your existing EDR telemetry with network, cloud, and identity data into one correlation layer. We don’t ask you to replace CrowdStrike or SentinelOne we work with your investment. The 250+ integrations mean your EDR alerts become one data source among many, correlated with the context that endpoints alone can’t provide.
The result? You stop asking “do I need both?” and start seeing the complete picture without tool sprawl or vendor lock-in.
“UnderDefense MAXI helps us secure sensitive data and mitigate potential cyber threats, which improves the overall security of our business operations.”
— Arman N., CTO, Mid-Market G2 Verified Review
Q2: What Are SIEM and EDR? Functional Definitions That Actually Matter
Why Definitions Matter Before You Spend Budget
Before evaluating “do I need both,” you need to understand what each technology architecturally delivers not what vendor marketing claims it delivers. I’ve seen too many organizations buy overlapping tools because sales decks conflate capabilities. Here’s what SIEM and EDR actually do in practice.
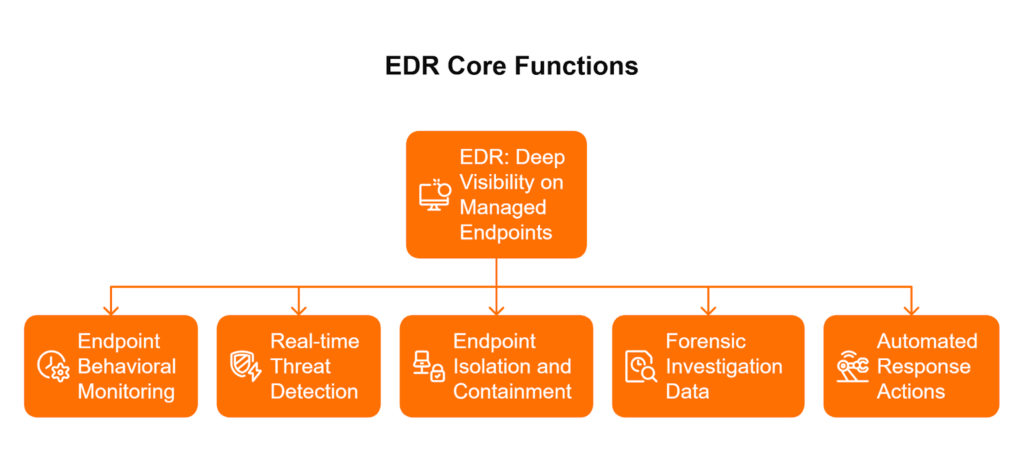
EDR: Deep Visibility on Managed Endpoints
Endpoint Detection and Response (EDR) monitors devices where you’ve installed agents. Its core functions:
- Endpoint behavioral monitoring tracks process execution, file system changes, registry modifications, and memory analysis on individual devices
- Real-time threat detection identifies malicious activity through behavioral signatures and machine learning on endpoints
- Endpoint isolation and containment quarantines compromised devices to prevent spread
- Forensic investigation data provides detailed timeline and artifact analysis for endpoint-specific incidents
- Automated response actions executes predefined playbooks, but only within endpoint scope
EDR sees deep but narrow. It knows everything happening on a laptop or server with an agent installed. It knows nothing about what’s happening between those devices or in systems without agents.
SIEM: Broad Visibility Across Infrastructure
Security Information and Event Management (SIEM) aggregates logs from everywhere. Its core functions:
- Log aggregation collects events from network devices, cloud platforms, identity providers, applications, and endpoints into one repository
- Cross-source event correlation connects related events across disparate systems to identify attack patterns
- Long-term log retention stores historical data for compliance audits and forensic investigations (often 90 days to 1+ year)
- Centralized alerting normalizes alerts from multiple security tools into unified incident queues
- Compliance evidence generation produces audit trails and reports required by SOC 2, HIPAA, PCI-DSS, and ISO 27001
SIEM sees wide but depends entirely on what log sources you connect. It can correlate a phishing email with a suspicious login with lateral movement but only if those data sources are feeding it.
The Architectural Truth
Here’s the key distinction: EDR provides depth on managed endpoints. SIEM provides breadth across all infrastructure. Neither alone provides complete visibility.
At UnderDefense, our managed SIEM service combines both data streams with 24/7 analyst correlation. We ingest your EDR alerts alongside network, cloud, and identity logs then our analysts connect the dots that neither tool can see independently. That’s the difference between owning tools and owning outcomes.
Q3: What Visibility Gaps Does EDR Actually Leave Exposed?
Understanding EDR’s Architectural Boundaries
EDR is designed for endpoint behavioral analysis and it excels at exactly that. But modern attack surfaces extend far beyond managed endpoints, and sophisticated attackers know precisely where EDR can’t see. These aren’t theoretical gaps; they’re the entry points I see exploited in incident response engagements regularly.
The 7 Critical Visibility Gaps
1. Network Lateral Movement Detection
Once attackers establish initial access, they pivot between systems using network protocols SMB, WMI, RDP, SSH. EDR agents monitor individual endpoints but can’t see the traffic between them. An attacker moving from your finance server to your domain controller via pass-the-hash? Your endpoint sees the login; it doesn’t see the network reconnaissance that preceded it.
2. Cloud API and Control Plane Activity
AWS CloudTrail, Azure Activity Logs, GCP Audit Logs these capture administrative actions that happen entirely outside endpoint scope. When someone creates a new IAM user with admin privileges at 3 AM, that’s a cloud control plane event. No EDR agent sees it because there’s no endpoint involved.
3. Identity and Authentication Logs
Active Directory, Okta, Azure AD federation events identity-based attacks increasingly bypass endpoints entirely. Credential stuffing, token theft, and federation abuse happen in identity systems. Your EDR sees the endpoint login result; it doesn’t see the authentication anomaly that should have blocked it.
4. SaaS Application Access Patterns
OAuth grants, mailbox forwarding rules, data exports through sanctioned applications these happen within SaaS platforms your EDR can’t monitor. An attacker granting themselves persistent access via a malicious OAuth app? That’s a SaaS event, invisible to endpoint detection.
5. IoT/OT and Unmanaged Devices
You can’t install agents on network printers, security cameras, HVAC controllers, or industrial systems. These devices connect to your network, often with default credentials, and serve as pivot points attackers love. No agent means no EDR visibility.
6. Email Gateway Threats
Phishing, business email compromise, malicious attachments email threats exist before they reach endpoints. Your EDR might catch the malware when it executes, but it doesn’t see the 47 phishing attempts that preceded the one employee who clicked.
7. DNS and Web Proxy Logs
Command-and-control communication patterns, data exfiltration via DNS tunneling, connections to known malicious domains network-level visibility that endpoints lack.
Why These Gaps Exist
EDR agents monitor kernel and user space activity on devices where they’re installed. They architecturally cannot be installed on network switches, cloud APIs, identity providers, or SaaS platforms. These aren’t failures they’re scope boundaries inherent to the technology.
At UnderDefense, we address every gap through MAXI’s 250+ integrations spanning endpoint, network, cloud, identity, and SaaS providing the unified visibility your EDR alone cannot deliver.
Q4: What’s Actually Overlapping Between EDR and SIEM And What’s Complementary?
The Uncomfortable Truth About Tool Overlap
The security industry profits from “you need everything” advice. Vendors rarely admit overlap exists CrowdStrike wants Falcon LogScale sales, Splunk wants endpoint visibility add-ons. Neither has incentive for honest architectural assessment. But here’s reality: some EDR and SIEM capabilities genuinely overlap, while others are irreplaceable. Understanding the difference prevents wasted budget and ensures actual coverage.
The “Buy Everything” Trap
I’ve audited environments where organizations pay twice for duplicate endpoint alerting while missing network and identity gaps entirely. The problem? Vendors position their products as comprehensive when they’re architecturally specialized. When CrowdStrike tells you Falcon LogScale handles everything, they’re selling their ecosystem not solving your visibility problem. When Splunk pushes endpoint add-ons, they’re expanding their footprint not optimizing your architecture.
The result? Alert fatigue from duplicate detections, budget drain from overlapping tools, and still blind spots where it matters.
The Overlap Reality
| Category | What’s Actually Duplicated |
| ✅ True Overlap | Endpoint process alerts, file-based malware detection, endpoint-specific IOCs, basic endpoint behavioral alerts |
| 🔄 Complementary | Network traffic analysis + endpoint correlation, identity events + endpoint behavior, cloud audit logs + endpoint access patterns |
| 🔒 SIEM-Only | Compliance log retention, cross-source correlation, non-endpoint device visibility, long-term forensic archives |
The overlap is real but narrow mostly limited to endpoint-generated alerts appearing in both systems. The complementary value is where the magic happens: correlating a suspicious Azure AD login with a CrowdStrike process alert with network lateral movement creates context neither tool provides alone.
How We Eliminate Duplicate Spend
At UnderDefense, MAXI eliminates duplicate alerting through intelligent correlation. We ingest your EDR alerts as one data source among many, deduplicate overlapping detections, and correlate unique signals across endpoint, network, cloud, and identity. You get unified visibility without paying twice for the same detection.
“The platform works really well with our other security tools, which makes things much simpler.”
— Serhii B., CISO, Mid-Market G2 Verified Review
What This Looks Like in Practice
Here’s a real scenario: CrowdStrike flags suspicious PowerShell execution on an endpoint. Azure AD shows a risky sign-in from an unusual location 3 minutes earlier. Network logs reveal SMB traffic to a file server that same endpoint never previously accessed. Three tools saw fragments. Without correlation, you have three separate alerts your team triages independently. With proper integration, you have one incident timeline showing credential compromise → endpoint access → lateral movement.
That’s the difference between alert noise and actionable intelligence and it’s what we deliver through managed detection and response that works with your existing EDR investment.
Q5: Why Does ‘Managed’ Matter When Evaluating SIEM Options?
⏰ The 3 AM Reality Check
It’s 3:17 AM on a Tuesday. Your SIEM flagged 52 alerts overnight. Your CrowdStrike console shows 14 “high severity” detections. You spend the next 3 hours triaging 38 false positives, 9 duplicates across tools, 4 legitimate but low-priority, 1 actual incident you almost missed in the noise. Your flight to a board meeting leaves in 4 hours. You haven’t slept.
This scenario isn’t hypothetical it’s the operational reality for most security teams running SIEM without dedicated 24/7 analyst coverage. The technology works. The human layer doesn’t scale.
Why SIEM Without Analysts Becomes an Expensive Log Aggregator
SIEM technology collects and correlates beautifully. But someone still needs to investigate alerts, tune detection rules, verify suspicious activity with users, and actually respond. Most organizations lack true 24/7 SOC coverage and the specialized expertise SIEM operation demands. The result? Expensive infrastructure that generates work rather than outcomes.
The hidden costs compound quickly:
- ⏰ Analyst time drain 15-20 hours weekly on manual triage that should be automated or handled by specialists
- 😓 Burnout epidemic Security analysts average 18-month tenure before turnover; alert fatigue is the primary driver
- ❌ Coverage gaps 70% of teams admit critical alerts get ignored due to volume
- 💸 Breach exposure Average dwell time increases 3x when analysts are overwhelmed
“Started out well but over the years the service has consistently not met expectations. Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing, 3B-10B USD Gartner Review
What “Managed” Should Actually Mean
Managed SIEM means waking up to “Incident contained at 3:22 AM here’s what happened and what we did” instead of “52 alerts to triage before your flight.” The difference isn’t the technology it’s the humans operating it around the clock.
At UnderDefense, our analysts become your 24/7 SOC extension. They triage, investigate, verify with users directly via Slack or Teams, and respond so your team reviews confirmed incidents, not raw alerts. We’ve documented 99% alert noise reduction across 500+ clients because that’s what “managed” should deliver.
“The biggest problem they solved was our 24/7 coverage gap. We needed round-the-clock monitoring for compliance reasons, but building our own SOC wasn’t realistic with our budget and the current hiring market.”
— Verified User, Marketing and Advertising G2 Verified Review
Q6: How Should EDR and Managed SIEM Actually Work Together?
Integration Isn’t “Connect Everything and Hope”
Poor integration makes both EDR and SIEM worse. I’ve seen environments where organizations forward all EDR telemetry to SIEM, creating duplicate alerts, storage cost explosions, and analysts drowning in noise. The goal isn’t maximum data it’s maximum signal.
Effective integration requires intentional architecture: knowing what telemetry to forward, what to summarize, and how to correlate without creating alert multiplication.
Integration Best Practices
- ✅ Forward EDR alerts (not raw telemetry) to SIEM for cross-source correlation you want the detection, not every process execution
- ✅ Use SIEM for data EDR doesn’t capture network flows, cloud audit logs, identity events, SaaS activity
- ✅ Establish unified severity scoring don’t let CrowdStrike “Critical” and SIEM “High” mean different things to different analysts
- ✅ Configure bidirectional enrichment SIEM context should inform EDR response automation
- ✅ Define single investigation workflow analysts shouldn’t toggle between 4 consoles for one incident
- ✅ Align retention policies EDR for short-term forensic detail, SIEM for long-term compliance archive
What NOT to Do
Common integration mistakes that create more problems than they solve:
- ❌ Forwarding all EDR raw telemetry to SIEM creates noise, balloons storage costs, generates duplicate detections
- ❌ Treating SIEM as EDR backup wastes SIEM’s correlation strength on data EDR already handles
- ❌ Maintaining separate investigation queues fragments response, increases MTTR, burns out analysts
- ❌ Ignoring tuning generic out-of-box rules create alert fatigue; every environment needs customization
How MAXI Simplifies This
At UnderDefense, MAXI handles integration architecture automatically. We ingest your CrowdStrike, SentinelOne, or Defender alerts alongside network, cloud, and identity data. We correlate across sources, deduplicate overlapping detections, and present unified incidents. No integration engineering required from your team we’ve done this across 500+ environments and know what works.
The outcome: your EDR investment stays intact while gaining the cross-source visibility and 24/7 analyst coverage that transforms alerts into outcomes.
Q7: Vendor-Specific Guidance: CrowdStrike, SentinelOne, and Microsoft Defender Users
Your EDR Investment Deserves Complementary Not Competing Coverage
Your EDR choice reflects significant investment and operational commitment. The managed SIEM question isn’t about replacing that investment it’s about complementing it with visibility your endpoint platform architecturally can’t provide. Here’s vendor-specific guidance for the three dominant EDR platforms.
CrowdStrike Falcon Users
✅ Strengths: Falcon excels at endpoint detection with industry-leading threat intelligence and OverWatch hunting capabilities. The platform’s behavioral analytics catch sophisticated attacks other EDRs miss.
❌ Gaps remain: Falcon LogScale adds significant cost without 24/7 analyst coverage included. Visibility stays at the endpoint-centric limited network, cloud API, and identity correlation. The proprietary ecosystem creates lock-in that complicates future flexibility.
UnderDefense approach: MAXI ingests Falcon alerts as one telemetry source among many. We add network, cloud, and identity correlation your Falcon deployment can’t see, plus included analyst coverage that OverWatch doesn’t provide at the same depth.
“This is not an extension of our security team as was originally sold. Still not quite there with the remediation side of things. We receive alerts, but not necessarily a clear path to resolution.” — Sr Cybersecurity Engineer, Manufacturing Gartner Review
SentinelOne Users
✅ Strengths: SentinelOne delivers autonomous endpoint response with strong automated remediation. The Storyline feature provides excellent attack visualization on endpoints.
❌ Gaps remain: Singularity platform is expanding but remains endpoint-centric. Limited native identity and cloud coverage. Requires internal SOC for cross-source correlation automation handles endpoint, but who handles everything else?
UnderDefense approach: MAXI integrates SentinelOne telemetry alongside your cloud and identity infrastructure. Our analysts provide the 24/7 correlation and contextual response that SentinelOne’s automation can’t deliver for non-endpoint threats.
Microsoft Defender Users
✅ Strengths: Defender provides cost-effective endpoint protection tightly integrated with M365 and Azure ecosystem. For Microsoft-native environments, the integration is seamless.
❌ Gaps remain: Sentinel SIEM adds significant licensing complexity and requires Azure commitment. Microsoft-centric visibility leaves gaps for multi-cloud or hybrid environments. AWS, GCP, and non-Microsoft identity providers become second-class citizens.
UnderDefense approach: MAXI works with Defender AND your non-Microsoft infrastructure AWS, GCP, Okta, on-prem systems. We provide vendor-neutral visibility that Microsoft’s ecosystem architecturally can’t match.
“The seamless integration and optimization of the EDR platform, CrowdStrike, has been impressive. Despite the complexity involved, they delivered the deployment to 1200 endpoints in just 23 business days.”— Oleksii M., Mid-Market G2 Verified Review
Q8: When Does Managed SIEM Add Value Beyond What EDR Provides? [toc=When SIEM Adds Value]
The Six Scenarios Where SIEM Isn’t Optional
Managed SIEM adds clear, measurable value in six scenarios that represent gaps your EDR regardless of vendor cannot architecturally address. If any apply to your organization, SIEM isn’t optional overhead; it’s required coverage.
Use Cases Where EDR Alone Falls Short
- Multi-cloud environments AWS + Azure + GCP activity requires log aggregation and correlation that no endpoint agent can provide. Cloud control plane attacks happen outside endpoint scope entirely.
- Compliance mandates SOC 2, HIPAA, PCI-DSS require centralized log retention (90 days to 1+ year) and audit trails across all systems, not just endpoints. EDR doesn’t satisfy these compliance requirements.
- Identity-based attacks Credential theft, privilege escalation, and federation abuse happen in identity systems (Active Directory, Okta, Azure AD), not on endpoints. Your EDR sees the result; SIEM sees the attack.
- Insider threat detection Behavioral baselines across applications, data access patterns, and communication channels require cross-source correlation. Endpoint activity alone misses the context.
- Network-based threats Command-and-control communication, lateral movement via network protocols, data exfiltration through DNS tunneling all invisible to endpoint agents.
- M&A and multi-environment visibility Acquiring companies with different EDR platforms? You need unified correlation across heterogeneous security stacks. SIEM provides that common layer.
How MAXI Addresses Every Scenario
At UnderDefense, MAXI addresses every use case through unified visibility across endpoint, network, cloud, identity, and SaaS with 24/7 analyst coverage that makes the data actionable. Your EDR handles endpoint threats; we handle everything else.
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.” — Oleg K., Director Information Security G2 Verified Review
Q9: How Do Compliance Requirements Factor Into the EDR vs. SIEM Decision? [toc=Compliance Requirements]
Here’s something I see constantly in conversations with CISOs and IT Directors: they come to us thinking they need better threat detection, but what actually forces the SIEM investment is a compliance audit finding or a cyber insurance renewal questionnaire. EDR is fantastic at what it does catching malicious behavior on endpoints. But compliance frameworks don’t care about your detection capabilities in isolation. They care about evidence, retention, and centralized audit trails.
⚠️ The Compliance Gap EDR Can’t Close
Many organizations discover this the hard way. They’ve deployed CrowdStrike, SentinelOne, or Microsoft Defender for Endpoint, and they believe their security telemetry needs are covered. Then the auditor arrives, and the questions start: “Show me 90 days of access logs for all systems touching cardholder data.” “Where’s your centralized audit trail for PHI access?” “How do you correlate authentication events across your identity provider, VPN, and cloud infrastructure?”
EDR can answer the endpoint portion of these questions. Everything else? That’s beyond its architectural scope.
📋 Framework-by-Framework Requirements
SOC 2 Type II requires centralized logging across all in-scope systems not just endpoints, but network devices, applications, cloud infrastructure, and databases. Auditors expect 90+ days of retention with access audit trails demonstrating who accessed what data and when.
HIPAA mandates audit controls to “record and examine activity related to protected health information” (45 CFR §164.312(b)). PHI flows through EHR systems, databases, cloud storage, and network paths all beyond what endpoint telemetry captures. HIPAA also requires six-year log retention for certain audit trails.
PCI-DSS Requirement 10 specifies one-year log retention with 90-day immediate access for all cardholder data environment systems. This includes firewalls, routers, servers, databases, and security tools a scope that exceeds any EDR’s data collection architecture.
ISO 27001 Control A.12.4 requires log management controls with aggregation from network, application, and security events. The emphasis is on correlation and centralized analysis, not point-tool telemetry.
Cyber Insurance Underwriting has shifted dramatically. Carriers increasingly require evidence of centralized logging, 24/7 monitoring, and incident response capabilities. “Do you have a SIEM?” is now a standard questionnaire item affecting premium calculations and coverage eligibility.
❌ What EDR Provides vs. What Compliance Requires
EDR meets endpoint logging requirements effectively process execution, file modifications, network connections from managed devices. That’s valuable, but compliance frameworks require aggregation across network devices, applications, databases, cloud infrastructure, and identity systems. Auditors want centralized evidence repositories, not console-by-console screenshots pieced together during audit week.
The forensic depth issue compounds this gap. Most EDR platforms focus on telemetry and alerting rather than forensic-grade evidence collection. They rarely provide tamper-proof logs, chain-of-custody integrity, or court-defensible reporting that regulators and legal teams require.
✅ How UnderDefense Simplifies Compliance
This is where our approach differs fundamentally. MAXI includes compliance automation built into the MDR subscription not sold as separate compliance modules. Our forever-free compliance kits generate audit evidence automatically from your unified security data. SOC 2, HIPAA, ISO 27001 readiness comes included, pulling from the same telemetry that powers your threat detection.
The result: when auditors ask for evidence, you’re not scrambling across five different consoles. You’re exporting pre-formatted reports from a single platform that already correlates your endpoint, network, cloud, and identity data.
Q10: SIEM vs. EDR: Side-by-Side Comparison Table [toc=SIEM EDR Comparison]
This comparison clarifies what each technology delivers and where they complement rather than compete. Use this as evaluation criteria when assessing your current coverage gaps the table reveals architectural differences that matter for both security outcomes and operational requirements.
📊 Comprehensive Comparison Across 10 Dimensions
| Dimension | EDR | SIEM |
| Scope | Endpoints only (workstations, servers, laptops) | All infrastructure (network, cloud, identity, applications) |
| Data Sources | Endpoint telemetry (process, file, network from device) | Logs from all systems firewalls, identity providers, cloud APIs, databases |
| Detection Focus | Endpoint behavior analysis and anomaly detection | Cross-source correlation and pattern recognition |
| Response Capability | Endpoint isolation, process termination, file quarantine | Alert generation, workflow orchestration, integration triggers |
| Compliance Support | Endpoint audit logs only | Centralized retention, audit-ready evidence, compliance reporting |
| Visibility Depth | Deep forensics on managed endpoints | Broad infrastructure overview with correlation context |
| Agent Requirement | Yes installed on every monitored device | No log-based collection from existing systems |
| Cloud Coverage | Cloud endpoint agents (if deployed) | Cloud API logs, audit trails, configuration events |
| Identity Visibility | Endpoint authentication events only | Identity provider logs, SSO events, privilege changes |
| Operational Requirement | Security team for alert triage and response | SOC team or managed service for correlation and analysis |
🔑 Key Insight: Complementary Architectures
The table reveals complementary architectures, not competing products. EDR provides depth on managed endpoints detailed process trees, memory forensics, and real-time containment capabilities. SIEM provides breadth across all infrastructure correlating authentication events with network flows with cloud API calls.
Organizations choosing “one or the other” leave predictable gaps attackers exploit. Lateral movement detection requires network visibility. Credential theft identification requires identity log correlation. Cloud workload compromise requires API audit trails. None of these are EDR’s job not because EDR is inadequate, but because its architecture wasn’t designed for these data sources.
⏰ When Each Technology Leads
EDR leads when: rapid endpoint containment matters, deep process forensics are required, or you’re investigating a known compromised device.
SIEM leads when: you’re correlating activity across multiple systems, meeting compliance log retention mandates, or detecting threats that span network boundaries.
Both required when: you need complete visibility into attack chains that start with a phishing email (identity), move through network reconnaissance (firewall/network logs), and execute on endpoints (EDR).
✅ UnderDefense Positioning
MAXI unifies both data streams your existing EDR’s endpoint depth combined with network, cloud, and identity breadth with 24/7 analyst coverage that makes correlation actionable. We don’t ask you to replace your EDR investment. We integrate with CrowdStrike, SentinelOne, Microsoft Defender, and 250+ other tools to fill the visibility gaps your current stack leaves open.
The operational difference: instead of your team manually correlating alerts across consoles, our analysts see the complete picture and respond with context. Endpoint isolation informed by network activity. User verification through ChatOps. Response that understands your organizational reality.
Q11: How Do You Evaluate Whether Managed SIEM Is Worth the Investment? [toc=Evaluating SIEM Investment]
Adding managed SIEM to your existing EDR stack is a significant budget decision. Choose wrong and you’ve created duplicate coverage with wasted spend. Choose right and you’ve closed visibility gaps that currently leave your organization exposed. Here’s the framework I use when helping security leaders make this decision.
❌ Wrong Way to Decide
Vendor bundling logic: “CrowdStrike offers LogScale, so we should use it.” This ignores whether the bundled solution actually addresses your gaps or just consolidates billing.
Feature count comparison: “They have 1,000 integrations.” Integration count means nothing if the integrations you need aren’t deep or maintained.
Analyst quadrant position alone: Quadrant placement reflects vendor marketing investment as much as operational fit. Your environment is specific; rankings are generic.
✅ Right Evaluation Framework: 7 Criteria
Score each provider 0-2 on these criteria. This isn’t theoretical it’s what separates partners who own outcomes from vendors who sell alert feeds.
1. Integration with existing EDR (0-2): Does it work with your current EDR or require replacement? Replacement means migration risk, retraining, and lost institutional knowledge.
2. Coverage scope (0-2): Does it address the network, cloud, and identity gaps your EDR misses? Or does it just add another endpoint-focused layer?
3. Analyst inclusion (0-2): Does pricing include 24/7 SOC coverage, or just the technology platform? Technology without analysts creates more work, not less.
4. Response capability (0-2): Can they contain and remediate, or just detect and notify? Notification without action means your team remains the bottleneck at 2 AM.
5. User verification (0-2): Can they communicate with affected users directly, or do they escalate back to you for verification? Direct verification cuts MTTR dramatically.
6. Compliance automation (0-2): Does it generate audit evidence automatically, or require manual report building? Manual compliance work is a hidden cost.
7. Pricing transparency (0-2): Is cost published and predictable, or does it require custom quotes and hidden overages? Unpredictable pricing creates budget risk.
📋 Applying the Framework
Score 10+ (out of 14): Genuine operational partnership that closes gaps and reduces your team’s burden. Worth the investment.
Score 7-9: Technology value exists, but operational gaps remain. Carefully evaluate whether your team can fill those gaps internally.
Below 7: You’re buying an alert feed that creates more work. The “managed” label is marketing, not operational reality.
✅ UnderDefense Scorecard
| Criterion | Score | Evidence |
| Integration | 2/2 | 250+ integrations; works with existing CrowdStrike, SentinelOne, Defender |
| Coverage scope | 2/2 | Network, cloud, identity, and endpoint unified in MAXI |
| Analyst inclusion | 2/2 | 24/7 SOC analysts included in MDR pricing |
| Response capability | 2/2 | 0.5h MTTR with containment and remediation authority |
| User verification | 2/2 | ChatOps-driven direct communication with affected users |
| Compliance automation | 2/2 | Forever-free compliance kits for SOC 2, HIPAA, ISO 27001 |
| Pricing transparency | 2/2 | Published $11-15/endpoint/month pricing |
| Total | 14/14 |
“UnderDefense’s ease of integration into our existing tech stack mirrors the positive aspects, enhancing our security without disrupting workflow.”
— CEO, Mid-Market Company G2 Verified Review
“They’re basically my security team since I can’t build one myself. They respond to problems so quickly.”
— Verified User, Mid-Market G2 Verified Review
Q12: What’s the Real Cost of Incomplete Visibility vs. Managed SIEM Investment? [toc=Cost of Visibility Gaps]
The budget question isn’t “Can we afford managed SIEM?” The real question is “Can we afford the gaps?” Incomplete visibility has quantifiable costs extended dwell time, breach impact amplification, analyst turnover, and compliance failures. These costs are real; the question is whether you’re tracking them or ignoring them until they materialize.
❌ Critiquing the “EDR Is Enough” Assumption
Organizations telling themselves that CrowdStrike, SentinelOne, or Microsoft Defender provides sufficient coverage are making an architectural bet. That bet has documented failure modes:
Missed lateral movement: Network visibility gap means attackers moving between systems go undetected until they hit another endpoint with your agent installed.
Undetected credential theft: Identity visibility gap means compromised credentials harvested from memory dumps or phishing get used across systems without correlation.
Compliance audit findings: Retention and centralization gaps mean auditors document deficiencies, requiring remediation budgets and management attention.
Analyst burnout: Operational gap means your team manually correlates alerts across disconnected consoles, creating context-switching fatigue and turnover risk.
💰 The Cost Synthesis
Breach cost probability calculation: Average breach cost reached $4.45M in 2023. Visibility gaps increase breach probability and extend dwell time, amplifying impact. Even a 10-20% reduction in breach likelihood from unified visibility represents significant risk reduction.
Security analyst replacement: Fully-loaded replacement cost for experienced security analysts exceeds $150K when factoring recruiting, onboarding, and productivity ramp. Alert fatigue and manual correlation work drive turnover. Reducing that burden through managed services protects your team investment.
Compliance penalty exposure: HIPAA penalties reach up to $1.5M per violation category. PCI-DSS non-compliance can result in fines, increased transaction fees, and loss of card processing privileges. SOC 2 audit failures delay customer deals and damage reputation.
Insurance premium impact: Organizations without centralized logging face higher premiums and coverage limitations. The delta between “adequate” and “insufficient” security posture directly impacts policy cost.
💸 UnderDefense’s Transparent ROI Calculation
Published pricing ($11-15/endpoint/month) makes this calculation straightforward. For a 500-endpoint organization:
Annual investment: $66,000-$90,000 for unified visibility, 24/7 analyst coverage, and compliance automation.
Compare against:
- Single breach average cost: $4.45M
- One analyst replacement: $150K+
- One compliance finding remediation: $50K-500K depending on scope
- Insurance premium increase for insufficient coverage: Variable but material
The math favors coverage. You’re not buying technology you’re buying risk transfer and operational capacity.
✅ Proof Point: Customer Outcomes
“UnderDefense MAXI helped us save money on security by automating tasks and making things run smoother. Their network tools helped us see what’s happening on our network better, which has helped us stop threats before they become big problems.”
— Julia K., Marketing Manager, Mid-Market G2 Verified Review
“Reduction in the number of successful cyberattacks or security incidents. Decreased time to detect and respond to threats. Improved vulnerability management metrics. Time savings for the in-house security team due to automation and 24/7 monitoring.”
— Serhii Bozhok, CIO of Security, ARX Insurance Company Clutch Review
The investment decision becomes clear when you stop asking “What does managed SIEM cost?” and start asking “What does the gap cost?” Every organization has a different risk profile, but the architectural gaps from EDR-only deployments are predictable and so are the consequences.
The post EDR vs. Managed SIEM: What You Actually Need for Full Visibility (And What’s Just Overlap) appeared first on UnderDefense.