Q1. What Are Managed SIEM, MDR, MSSP, and SOCaaS, and Why Do Security Leaders Confuse Them?
⚠️ The Acronym Maze Is Costing You Real Money
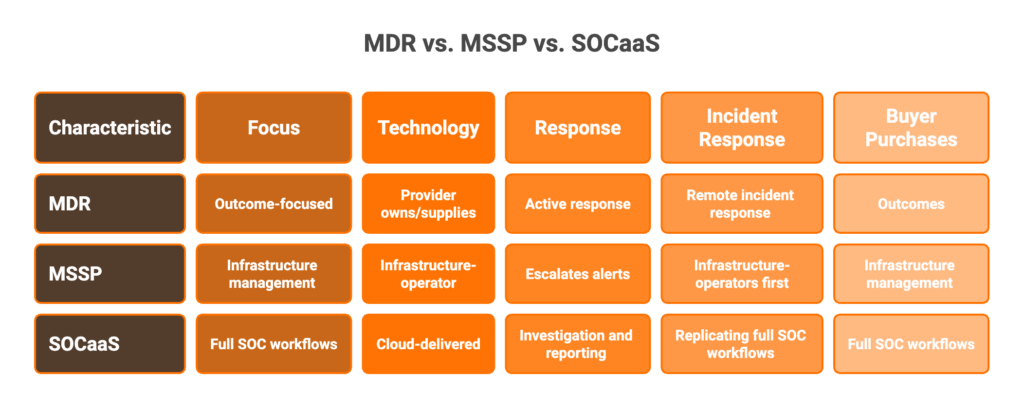
Here’s the problem: vendors use these four terms interchangeably to sell fundamentally different things. Gartner projected that 50% of organizations would be using MDR services by 2025, with the market generating $2.15 billion in revenue that year alone. The MDR market has since ballooned past $9.6 billion in 2025. Meanwhile, MSSPs rebrand as MDR providers or SOCaaS vendors without actually changing their delivery model. This confusion has real procurement consequences, because buying the wrong model means coverage gaps your team inherits or budget burned on overlapping services.
I’ve seen it firsthand: a CISO signs what they think is an MDR contract, only to discover they’ve purchased managed SIEM with a fancy dashboard. Six months in, the team is still triaging alerts at 2 AM. Let’s fix the definitions.
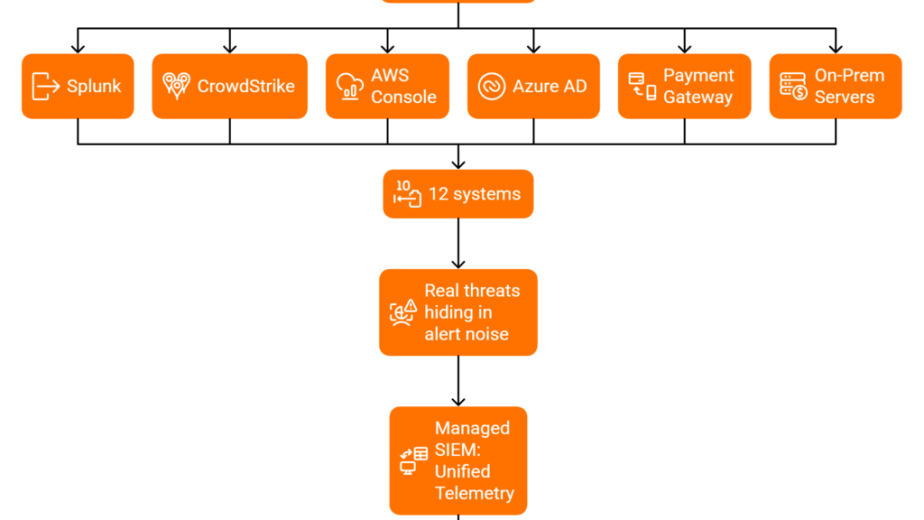
📋 Managed SIEM: You Own the Platform, They Run It
A Managed SIEM service means a third-party provider operates, tunes, and monitors your SIEM platform, whether that’s Splunk, Elastic, or Microsoft Sentinel. You own the SIEM instance; they manage it. Core deliverables include:
- Log ingestion and normalization across your environment
- Correlation rule tuning and alert threshold management
- Dashboard maintenance and compliance reporting from logs
- Alert triage and ticket creation for your team
The critical limitation: Managed SIEM is detection-heavy, response-light. Your team still investigates and responds. The provider creates a ticket, but they don’t contain the threat.
🔍 MDR: You’re Buying Outcomes, Not Tool Management
Managed Detection and Response (MDR) is a turnkey, outcome-focused service combining technology, threat intelligence, and human analysts to detect AND respond to threats 24/7. Unlike managed SIEM, the MDR provider typically owns or supplies detection technology and performs active response, including isolation, containment, and remediation. Gartner distinguishes MDR from MSSPs primarily through incident response capability: MDR providers offer remote incident response as part of the standard package. The buyer purchases outcomes, “threats stopped,” not tool management.
🛡️ MSSP: The Broadest and Oldest Category
Managed Security Services Providers (MSSPs) deliver the broadest service scope: monitoring, device management (firewalls, VPN, IDS/IPS), vulnerability scanning, patch management, and compliance support. MSSPs are infrastructure-operators first, threat-responders second. They monitor your environment and escalate alerts, but typically do not perform containment or remediation. As one industry analysis puts it: “An MSSP will perform no investigation into the alerts that they send.” Think of it as outsourced security infrastructure management.
☁️ SOCaaS: Full SOC Workflows Without Building One
SOC-as-a-Service (SOCaaS) is a cloud-delivered, subscription-based security operations center function, providing 24/7 monitoring, detection, triage, investigation, and reporting without building a physical SOC or hiring Tier 1-3 analysts. SOCaaS overlaps with MDR and managed SIEM but is distinguished by its emphasis on replicating full SOC workflows (multi-tier triage, investigation narratives, escalation procedures) rather than just detection+response or log management. Gartner increasingly views SOCaaS as a delivery mechanism for MDR rather than a separate category.
UnderDefense MAXI platform unifies these capabilities, combining managed SIEM log operations, MDR-grade response, and SOCaaS-level analyst workflows, into a single “AI SOC + Human Ally” model that eliminates the need to parse these distinctions during procurement.
Q2. How Do These Four Models Differ in Scope, Response, and Performance Benchmarks?
📊 Why Most Comparison Articles Miss What Matters
Most competitor articles compare two or three models superficially and skip the operational dimensions that matter during contract negotiations. The table below maps all four models across 10 critical dimensions, covering what each model actually delivers day-to-day, how fast they perform, and where your team’s responsibilities begin and end.
The overlaps are real, as all four provide some form of 24/7 monitoring and alert triage. The differences emerge in response depth, proactive posture, and measurable performance.
📋 The Definitive 10-Dimension Comparison
| Dimension | Managed SIEM | MDR | MSSP | SOCaaS |
|---|---|---|---|---|
| Core Function | SIEM platform operations & log management | Threat detection + active response | Infrastructure monitoring & device management | Full SOC workflow replication |
| Detection Approach | Log correlation & rule-based alerting | Multi-signal (endpoint, network, cloud, identity) | Signature-based & device-log monitoring | Multi-tier triage with investigation narratives |
| Incident Response Scope | Detect → Create ticket | Detect → Respond → Contain → Remediate | Detect → Escalate via email/portal | Detect → Investigate → Recommend action |
| Proactive vs. Reactive | Reactive (alert-driven) | Proactive (threat hunting + TI-driven) | Reactive (signature/device alerting) | Mixed (depends on provider) |
| Typical MTTD Range | Minutes to hours (tuning-dependent) | Minutes (leading providers: 2 min) | Hours to days | Hours (analyst-dependent) |
| Typical MTTR Range | N/A, customer responds | 6 min to 1 hour (top providers) | N/A, customer responds | Hours (recommendation-based) |
| Monitoring Depth | Logs only (SIEM-ingested) | Full-stack: endpoint + network + cloud + identity | Device-level: firewalls, IDS/IPS, VPN | Logs + endpoint + cloud (varies) |
| Staffing Model | Vendor: tunes SIEM; Customer: investigates & responds | Vendor: detects, triages, contains; Customer: reviews | Vendor: monitors devices; Customer: investigates & responds | Vendor: Tier 1-2 triage; Customer: Tier 3 decisions |
| Technology Ownership | Customer owns SIEM | Vendor often owns/supplies detection tech | Customer owns infrastructure | Varies, often vendor-supplied |
| Typical Buyer Profile | Orgs with SIEM investment needing operational help | Mid-market teams needing turnkey 24/7 security | Enterprises needing infrastructure management | Orgs needing SOC function without building one |
Leading MDR providers can reduce MTTD from the industry average of 207 days to hours or minutes, with top providers reporting MTTR between 6 and 22 minutes for critical threats.
🔄 Where They All Overlap
All four models share three core capabilities: 24/7 monitoring, alert prioritization, and some form of compliance reporting. This overlap is real, because each model evolved from the same root problem: organizations can’t staff security operations internally, especially with the 3.4M cybersecurity talent shortage.
The critical differentiator is what happens AFTER an alert fires: managed SIEM creates a ticket, MSSPs send you an email, SOCaaS investigates then recommends action, and MDR contains the threat.
✅ Where UnderDefense Benchmarks
UnderDefense MAXI delivers 2-minute Alert-to-Triage with enrichment, 15-minute escalation for critical incidents, and 96% MITRE ATT&CK coverage. These benchmarks collapse the performance gap between “monitoring service” and “security operations partner.”
Q3. Who Owns What? The Accountability Matrix Competitors Won’t Show You
⏰ The Question That Matters at Contract Renewal
Most comparison articles stop at “what each model detects.” But the questions that matter at contract renewal, or termination, are about ownership. Who owns the SIEM instance? Who owns the detection rules and correlation logic your vendor spent 12 months tuning? If you switch providers, do those custom detections come with you, or do you start from zero?
In a recent podcast discussion, a former CISO of Micron and DarkTrace (now at Aura) described exactly this scenario: when switching MDR providers who owned the SIEM, he lost all custom correlation rules, insider threat integrations, and business-context configurations. Months of tuning, gone overnight. As he put it: “When I switch to another vendor, I get to start all over on that tuning process.”
📋 The Ownership & Accountability Matrix
| Ownership Dimension | Managed SIEM | MDR | MSSP | SOCaaS |
|---|---|---|---|---|
| SIEM/Platform Ownership | ✅ Customer owns | ❌ Vendor typically owns | ✅ Customer owns infrastructure | ❌ Vendor-supplied |
| Detection Rules & Logic | ✅ Customer owns (but must maintain) | ❌ Vendor owns (proprietary) | ⚠️ Mixed, basic rules with customer | ❌ Vendor owns |
| Playbook/Runbook Ownership | ✅ Customer-defined | ❌ Vendor-defined & controlled | ⚠️ Shared, customer input, vendor execution | ❌ Vendor-controlled |
| Log Data Storage & Access | ✅ Customer retains all logs | ⚠️ Varies, some vendors restrict access | ✅ Customer retains logs | ⚠️ Varies by provider |
| Threat Intelligence Feeds | ⚠️ Often vendor-supplied, non-portable | ❌ Vendor proprietary | ⚠️ Basic feeds, non-portable | ❌ Vendor proprietary |
| Compliance Evidence & Audit Trails | ✅ Accessible via SIEM | ⚠️ Vendor-generated, may not transfer | ✅ Device-level logs retained | ⚠️ Vendor-generated reports |
| Data Portability at Termination | ✅ Full, SIEM stays with you | ❌ Limited, detection logic stays with vendor | ✅ Infrastructure stays | ❌ Platform and logic stay with vendor |
💸 The Vendor Lock-In Trap
Arctic Wolf requires proprietary SIEM replacement, forcing you to abandon your existing stack. ReliaQuest positions its own Gray Matter platform and locks customers to it. CrowdStrike Falcon Complete works only within the Falcon ecosystem. When these contracts end, your detection logic, tuning, and business context stay with the vendor.
The operational cost is staggering. That former Micron CISO shared a specific example: a non-standard integration connecting a project management system to the MDR team (to contextualize insider threat anomalies) disappeared entirely when switching SIEM vendors. Every unique business workflow, “gone overnight.”
“We received little value from ArcticWolf. The product offered little visibility… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated. Support incidents are not worked to completion.”
— CISO, Manufacturing ($3B-$10B) Arctic Wolf – Gartner Peer Review
“Their team provided us with clear and detailed insights into security vulnerabilities, along with practical recommendations on how to fix them. This level of transparency made it easy for our team to take action.”
— Arman N., CTO UnderDefense – G2 Verified Review
✅ UnderDefense’s “You Own Everything” Architecture
UnderDefense’s architecture is designed to prevent lock-in. Analysts log into YOUR SIEM (Splunk, Elastic, Sentinel), detection rules are written in open languages (Python, SIGMA), versioned, and belong to you. If you leave, every custom detection, playbook, and correlation rule stays in your environment. As the Aura CISO recommended: “I look for an MDR partner that will access the data where it lives and I want to control where that data lives,” which is precisely how UnderDefense operates.
Q4. Can Managed SIEM Replace an MSSP, or Do You Need Both?
⚠️ The Decision Dilemma
Security leaders who already run a managed SIEM face a real question: do they still need an MSSP for broader operations (firewall management, vulnerability scanning, device administration), or has managed SIEM made the MSSP redundant? The stakes are clear, because over-buying means wasted budget on overlapping monitoring, while under-buying means blind spots in infrastructure management your team inherits.
❌ The Wrong Way to Decide
Most teams answer by comparing feature lists. “Our managed SIEM already does monitoring, so why pay an MSSP for monitoring too?” This logic ignores the critical difference: managed SIEM optimizes detection from log data, while MSSPs manage the infrastructure that generates that data. Dropping one without replacing its unique function creates gaps. And as one experienced CISO framed it during a budget conversation: “I want a list of vendors and then I want to visualize it by security controls… that one-page visual can be really enlightening.”
✅ The Right Evaluation Framework
Score your situation against these five criteria before making the call:
- Do you need infrastructure management (firewall, VPN, endpoint device administration), or just log-based detection? If infrastructure: MSSP still relevant.
- Does your team handle incident response, or do you need a provider to contain threats? If response needed: neither managed SIEM nor MSSP alone suffices, and you need MDR.
- Are compliance requirements met by log evidence alone, or do you need policy enforcement and audit support?
- Can your internal team manage the security stack operationally, or do you need hands-on device support?
- Is your primary goal noise reduction (managed SIEM strength) or full security operations offload (MSSP/MDR territory)?
🎯 Applying the Framework
If you scored “detection + response + compliance” as primary needs, you don’t need separate managed SIEM + MSSP. You need an MDR with managed SIEM capabilities built in. If your primary need is infrastructure administration (device management, patching), the MSSP still has a role, but that role is shrinking as MDR providers absorb MSSP functions.
📋 Where UnderDefense Eliminates the Dilemma
| Capability | Traditional Managed SIEM | Traditional MSSP | UnderDefense MAXI |
|---|---|---|---|
| Detection | ✅ Log-based correlation | ⚠️ Basic device alerting | ✅ Full-stack AI detection across 250+ tools |
| Response | ❌ Creates tickets only | ❌ Escalates via email | ✅ Active containment, 15-min escalation for critical incidents |
| Infrastructure Mgmt | ❌ Not included | ✅ Firewalls, VPN, devices | ⚠️ Not device management, focuses on security operations |
| Compliance | ⚠️ Log evidence only | ⚠️ Separate engagement | ✅ Forever-free compliance kits bundled |
| Pricing Model | 💰 SIEM license + management fee | 💰 Opaque retainers | 💰 $11-15/endpoint/month, published |
| Data Ownership | ✅ Customer owns SIEM | ✅ Customer owns devices | ✅ Customer owns SIEM, rules, and data |
UnderDefense MAXI eliminates the “managed SIEM vs. MSSP” dilemma by combining managed SIEM log operations (on your existing SIEM), MDR-grade response (15-minute escalation for critical incidents), and compliance automation, without the infrastructure management overhead that justifies a traditional MSSP. Published $11-15/endpoint/month pricing with 30-day onboarding.
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
“The biggest problem they solved was our 24/7 coverage gap. We needed round-the-clock monitoring for compliance reasons, but building our own SOC wasn’t realistic with our budget and the current hiring market.”
— Verified User, Marketing & Advertising UnderDefense – G2 Verified Review
“We’ve had a pretty terrible experience with Alert Logic. The product was oversold and underdelivered.”
— Information Security Officer, Banking ($3B-$10B) Alert Logic – Gartner Peer Review
The real question here is not “managed SIEM or MSSP?” but “which provider can own security outcomes the way a dedicated internal team would, without forcing me to replace what I already have?” That’s the shift UnderDefense represents.
Q5. Is SOCaaS the Same as MDR, or a Different Model Entirely?
No, SOCaaS and MDR solve related but structurally different problems. SOCaaS replicates full SOC workflows (Tier 1-3 triage, investigation, escalation, reporting) as a cloud-delivered subscription service. MDR is outcome-focused: detect threats and respond to them, period. SOCaaS gives you a SOC team; MDR gives you threat containment. Here’s how to tell them apart:
🔍 Five Distinctions That Matter
- SOCaaS delivers the people + process layer: analysts who triage, investigate, and report. It mirrors what an internal SOC does, but outsourced. The emphasis is on replicating multi-tier workflows and producing investigation narratives.
- MDR delivers the outcome layer: threats detected, contained, and remediated, regardless of internal workflow. The buyer purchases “threats stopped,” not SOC operations.
- ⚠️ SOCaaS may or may not include active response (containment, isolation). MDR always does, because active containment is the defining feature that separates MDR from every other model.
- SOCaaS typically works across your existing tooling and produces investigation narratives; MDR providers may supply their own detection stack, which can introduce vendor lock-in.
- Gartner increasingly views SOCaaS as a delivery mechanism for MDR, not a separate category. The lines are converging rapidly in 2026 as security services spending grows at 11.1%, the fastest rate in the services segment.
✅ Where the Two Models Converge
UnderDefense’s “AI SOC + Human Ally” model is the convergence point, combining dedicated Tier 3-4 analysts who learn your organization (SOCaaS-level relationship depth) with automated detection + containment that stops threats in minutes (MDR-level outcomes). The result: SOC-grade investigation depth with MDR-grade response speed. Zero ransomware cases across 500+ MDR clients in 6 years, because detection without human-driven response is just expensive alerting.
Q6. What Does Each Model Cost, and Which Compliance Frameworks Does It Best Support?
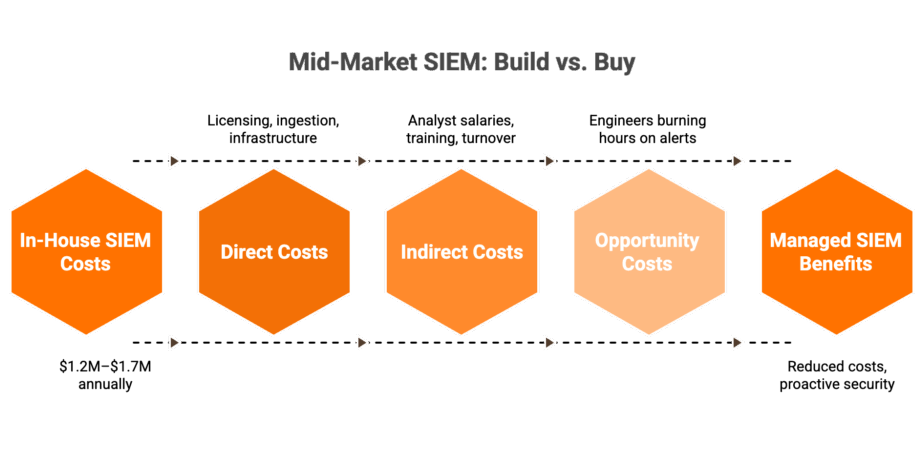
💰 Why True Cost Is Harder to Calculate Than You Think
Cost comparison across these four models is deliberately opaque. Most providers hide pricing behind “contact sales,” making apples-to-apples comparison nearly impossible. But the total cost extends beyond the contract price: it includes the internal staffing required to operationalize the service. A managed SIEM at $8K/month that requires 2 FTE analysts to investigate alerts has a very different true cost than an MDR at $12K/month that requires zero internal investigation. Security services spending is growing at 11.1% in 2026, the fastest-growing segment in Gartner’s $244 billion security forecast, precisely because organizations are buying outside expertise they cannot build internally.
📋 Cost & Staffing Comparison
| Dimension | Managed SIEM | MDR | MSSP | SOCaaS |
|---|---|---|---|---|
| Typical Annual Contract | $60K-$120K | $50K-$200K+ | $80K-$300K | $60K-$180K |
| Internal Staff Required | 2-3 FTEs (investigate + respond) | 0-1 FTE (review + strategic decisions) | 1-2 FTEs (investigate escalations) | 1 FTE (Tier 3 decisions) |
| Hidden Costs | SIEM licensing, log storage overage | Tool replacement (vendor-locked MDR), onboarding fees | Scope creep per-device charges | Platform fees, per-alert costs |
| Pricing Model | Per-log-volume or flat fee | Per-endpoint or flat | Per-device or retainer | Per-user or per-endpoint |
Key insight: managed SIEM is cheapest on paper but most expensive in total staff burden. MDR costs more upfront but offloads the most internal work. MSSPs vary wildly based on scope. SOCaaS falls between managed SIEM and MDR.
✅ Compliance Framework Support Matrix
| Framework | Managed SIEM | MDR | MSSP | SOCaaS |
|---|---|---|---|---|
| SOC 2 Type II | ✅ Strong log evidence | ⚠️ Varies by provider | ⚠️ Partial, device-level logs | ✅ Investigation audit trails |
| HIPAA | ⚠️ Log monitoring only | ✅ IR evidence for breach notification | ⚠️ Monitoring without enforcement | ⚠️ Depends on scope |
| PCI DSS | ✅ Log retention + review | ⚠️ Partial, response-focused | ✅ Device policy enforcement | ⚠️ Partial coverage |
| ISO 27001 | ⚠️ Log evidence only | ⚠️ Requires compliance add-on | ✅ Policy management support | ⚠️ Investigation evidence |
| NIS2/DORA | ❌ No incident reporting built-in | ✅ Rapid IR for regulatory reporting | ⚠️ Limited response capability | ⚠️ Reporting varies |
Managed SIEM generates log evidence (strong for SOC 2, PCI DSS) but doesn’t enforce controls. MDR provides incident response evidence critical for HIPAA breach notification and NIS2 reporting. MSSPs provide policy enforcement. SOCaaS provides investigation audit trails.
✅ Where UnderDefense Simplifies the Math
UnderDefense publishes transparent $11-15/endpoint/month pricing, zero hidden professional services fees, 30-day onboarding included, and forever-free compliance kits (SOC 2, HIPAA, ISO 27001, PCI DSS) bundled with MDR, not sold as a separate product. 830% ROI over 3 years documented across the customer base.
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User, Program Development UnderDefense – G2 Verified Review
“The pre-sales crew is great. Really make you think you’ll get high tier support… The scan engine doesn’t function. I’m unable to scan our IP ranges, and they’ve ignored requests to get this resolved.”
— Verified User, Farming Rapid7 – G2 Verified Review
Q7. What Does Each Model Look Like in Practice? Three Real-World Scenarios
⏰ The Setup: 2:47 AM, Tuesday
It’s 2:47 AM. A behavioral alert fires: a senior engineer’s account authenticated from an unfamiliar location and initiated a privileged configuration change in your cloud environment. What happens next depends entirely on your organization’s profile and which security model you’ve chosen. Here’s the same incident through three different lenses.
Persona A: Lean SaaS Startup (40 employees, 0 security staff, SOC 2 deadline in 90 days)
- With Managed SIEM: The alert sits in Splunk until your CTO checks the dashboard tomorrow morning, an 8+ hour gap. No investigation, no response, no containment.
- With MSSP: You receive an email ticket at 3:01 AM: “suspicious authentication, please investigate.” Your CTO is the “security team.” That email sits unread until 7 AM.
✅ With MDR (UnderDefense): UnderDefense MAXI detects, correlates identity + cloud telemetry, and an analyst messages the engineer via Slack within minutes. Confirmed legitimate? Closed with audit trail. Compromised? Account contained, session terminated, incident report ready by morning. SOC 2 evidence auto-generated.
Persona B: Mid-Market Fintech (500 employees, 3-person security team, existing Splunk + CrowdStrike)
- With Managed SIEM: Alert triaged, prioritized as “high.” Your Tier 1 analyst starts investigating at 6 AM. Three hours of manual correlation across Splunk and CrowdStrike before anyone understands what happened.
- With SOCaaS: Outsourced Tier 1 triages and escalates to your Tier 2 with an investigation narrative, but containment still requires your analyst to act.
✅ With MDR (UnderDefense): UnderDefense MAXI integrates with your existing Splunk + CrowdStrike, correlates the alert, analyst verifies directly with the engineer via Teams, contains if necessary. Your 3-person team reviews a completed incident report, not raw alerts. Their time stays on strategic projects.
Persona C: Enterprise with Partial SOC (2,000 employees, 8-person security team, Microsoft Sentinel)
- With MSSP: Infrastructure team monitors Sentinel, firewall logs, and VPN, but the behavioral alert lands in the SOC queue behind 200 other alerts. Dwell time: hours.
- With SOCaaS + Internal Tier 2: Outsourced Tier 1 triages, your internal Tier 2 investigates and decides. Faster, but still requires your senior analyst to act at 3 AM.
✅ With MDR (UnderDefense): UnderDefense MAXI augments your existing SOC, handles Tier 1-2 triage and user verification, escalates confirmed critical incidents to your Tier 3 team with full context and recommended actions. Your SOC scales without hiring.
Same alert. Three organizations. Radically different outcomes based on model choice.
“Underdefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO UnderDefense – G2 Verified Review
“Despite the capabilities of the technical platform and the strength of the analysts providing the service, there is still a limit to the environmental/organizational knowledge inherent in the service. This leads to a fairly frequent need for engagement with our internal team.”
— Verified User, Computer Software Expel – G2 Verified Review
Q8. Co-Managed Models, Hybrid Approaches, and the 2026 Convergence: Where Are These Categories Heading?
🔄 The Blended Model Reality
Few organizations fit neatly into one model. The fastest-growing deployment pattern in 2026 is the hybrid/co-managed approach: enterprises keeping internal Tier 2-3 analysts for business-context decisions while outsourcing Tier 1 triage and 24/7 coverage. Co-managed SIEM, where the customer owns the platform and an external partner manages operations, has moved from a tactical outsourcing option to a strategic operating model.
A former CISO described this hybrid model precisely: “If I can offshore or have a partner take on the level one work, that work tends to be very commoditized, very documented, easy to bring somebody on and train them up. People are frequently moving on in their career path. So it might make sense for me to ask a vendor to manage that turnover. But I still keep a level two or level three team in-house.”
❌ Why Category Boundaries Are Breaking
Traditional MSSPs now offer “MDR capabilities.” MDR vendors bundle SIEM management. SOCaaS providers add automated response. The category labels increasingly describe legacy vendor packaging, not actual delivery models. Buyers who choose based on vendor category rather than operational deliverables end up with coverage gaps disguised by marketing language.
Arctic Wolf calls itself MDR but requires proprietary SIEM replacement. ReliaQuest positions as MDR but escalates tickets without context back to customer teams. Red Canary focuses heavily on endpoint via CrowdStrike, with reviewers noting detections “could be more proactive” beyond the endpoint layer.
“This is not an extension of our security team as was originally sold.”
— Sr Cybersecurity Engineer, Manufacturing Arctic Wolf – Gartner Peer Review
🚀 The Convergence Thesis
The winning model in 2026 is not managed SIEM or MDR or SOCaaS but an integrated security operations platform that delivers all three: log management + detection + human-led response + compliance automation. Gartner projects $244 billion in total security spending for 2026, with managed security services growing at 11.1%, the fastest rate in the services segment. The market is voting with dollars for unified delivery, not fragmented categories. Detection without response is noise. Response without context is risk.
✅ UnderDefense’s Position in the Convergence
UnderDefense built MAXI for this convergence. The platform supports full co-managed deployment: analysts log into your SIEM, work alongside your internal team, and handle Tier 1-2 while your team owns strategic decisions. Simultaneously, it delivers MDR-grade containment (96% MITRE ATT&CK coverage, 15-minute escalation for critical incidents), SOCaaS-level relationship depth (concierge teams who learn your org structure, VIPs, and critical assets), and compliance automation, all vendor-agnostic across 250+ tools. One contract replaces 3-4 fragmented vendor relationships.
“Their experienced SOC engineers work closely with our team, providing continuous monitoring and threat detection. They delivered CrowdStrike deployment to 1,200 endpoints in just 23 business days.”
— Oleksii M., Mid-Market UnderDefense – G2 Verified Review
“Red Canary is perhaps too reliant on CrowdStrike and less on our other sources which are important, Cloud, Identity, Email, etc. We also find that Red Canary detections could be more proactive.”
— Verified User, Computer Software Red Canary – G2 Verified Review
UnderDefense maintains 113% net dollar retention, because concierge teams that learn each customer’s org structure, executives, and critical assets don’t just monitor environments but become an extension of your security team. Zero ransomware cases across all MDR clients in 6 years.
Q9. Which Model Fits Your Security Team? A Decision Framework by Team Size, Maturity, and Budget
You’ve read the definitions, comparisons, and real-world scenarios. The operational question remains: which model fits your organization right now? The answer depends on five variables: internal team size, existing tool investments, compliance requirements, budget model preference, and whether you need detection-only or detection + response + containment.
❌ The Wrong Way to Decide
Choosing based on vendor category (“we need an MSSP”) or brand recognition (“CrowdStrike is the biggest”) ignores operational reality. A 3-person security team choosing a managed SIEM still has to investigate every alert, and that’s not “managed” but “monitored.” A 500-person enterprise choosing basic MDR might be paying for response capabilities they can handle internally. As one Reddit user put it:
“The majority of MDR services tend to offer similar solutions, with only slight variations. Ultimately, the choice often hinges on factors like cost and the quality of customer support.”
— u/sprite3nthusiast, r/cybersecurity Reddit Thread
✅ The Right Framework: Decision Matrix
Map your profile to the model that actually fits your operational reality:
| Profile | Team Size | Existing Tools | Recommended Model |
|---|---|---|---|
| A: No dedicated security staff | 0-2 | No SIEM, compliance-driven | MDR with bundled SIEM + compliance |
| B: Small security team, existing investments | 3-5 | Existing SIEM, want to keep tools | Vendor-agnostic MDR or co-managed SIEM + MDR overlay |
| C: Partial SOC, need augmentation | 5-10+ | Partial SOC built | SOCaaS or co-managed MDR |
| D: Large enterprise, full SOC | 10+ | Full SOC, infrastructure management needed | MSSP for infrastructure + MDR for threat operations |
📋 8 Questions to Ask Before Signing Any Contract
Before committing budget, score each provider on these criteria:
- ☐ Can they work with your existing tools, or do they require proprietary replacement?
- ☐ Do they perform active containment, or just detect + notify?
- ☐ Can they verify suspicious activity directly with affected users?
- ☐ Is pricing published and predictable?
- ☐ What is documented response time for critical incidents?
- ☐ Is compliance automation included, or is it a separate add-on?
- ☐ What happens to detection rules and data at contract termination?
- ☐ What’s the onboarding timeline?
⚖️ How to Score and Interpret
Score each provider 0-2 on these 8 criteria. Providers scoring 12+ represent genuine security operations partners. Below 8: you’re buying an alert feed, not managed detection and response. This checklist deliberately tests for the gaps most vendors hope you won’t ask about: data portability, user verification, and pricing transparency.
“We received little value from Arctic Wolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
Where UnderDefense Stands: 16/16
| Criterion | Score | Justification |
|---|---|---|
| Vendor-agnostic | ✅ 2 | 250+ integrations, works with your existing stack |
| Active containment | ✅ 2 | 15-minute escalation for critical incidents, documented |
| User verification | ✅ 2 | ChatOps via Slack/Teams/Email, contacts users directly |
| Published pricing | ✅ 2 | $11-15/endpoint/month, transparent |
| Documented response time | ✅ 2 | 2-minute alert-to-triage, 15-minute escalation for critical incidents |
| Compliance included | ✅ 2 | Forever-free compliance kits (SOC 2, ISO 27001, HIPAA) |
| Data portability | ✅ 2 | You own everything: SIEM, detection rules, and telemetry |
| Onboarding | ✅ 2 | 30-day turnkey deployment with custom detection tuning |
UnderDefense scores 16/16 because we designed UnderDefense MAXI from the ground up as an AI SOC with Human Ally, not retrofitted from a monitoring tool or proprietary SIEM.
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
Q10. Ready to Evaluate Providers? Here’s Where to Start
Now that you understand what each model delivers, the next step is evaluating specific providers against the framework above. The managed security market includes hundreds of vendors, but only a handful deliver genuine detection + response + compliance under transparent pricing.
What Separates Top Managed Security Providers from Alert Factories
- Vendor-agnostic integration vs. proprietary stack replacement: does the provider work with your CrowdStrike, Splunk, or SentinelOne, or force you to rip and replace?
- Human analyst access: direct Tier 3-4 communication vs. ticket-based escalation that leaves your team waiting hours for context.
- Published response time SLAs with documented case study evidence, not marketing claims, but reproducible outcomes.
- Transparent per-endpoint pricing vs. opaque enterprise quotes that hide true cost until you’re deep in a sales cycle.
- Compliance support bundled vs. sold as a separate product that inflates total cost of ownership.
⏰ The Right Next Step for Serious Evaluators
Each provider excels in different scenarios. The right choice depends on your current security investments, team size, and operational model. We’ve evaluated the top managed cybersecurity services providers head-to-head, including pricing, response times, integration capabilities, and compliance support.
💰 Want to calculate what building vs. buying a SOC actually costs for your organization? Use the SOC Cost Calculator →
This analysis is based on documented response times, G2 reviews, published pricing, and operational outcomes across 500+ MDR deployments over 6 years.
Q11. The Bottom Line: Stop Buying Categories, Start Buying Outcomes
The managed security market has spent a decade splitting into increasingly narrow categories. But threats don’t respect vendor categories. When a credential is compromised at 2 AM, the contract label doesn’t matter, whether it says “managed SIEM” or “MDR.” What matters: Did someone detect it, verify it, and contain it?
What Each Model Actually Delivers
✅ Managed SIEM optimizes detection from logs, but your team still investigates and responds.
✅ MSSPs manage infrastructure, but don’t hunt threats or contain breaches.
✅ MDR detects and responds, but many vendors lock you into proprietary tools.
✅ SOCaaS replicates SOC workflows, but response depth varies wildly by provider.
The real question here is not “which category?” but rather: can my provider detect, verify, and contain with the speed and context of a dedicated security team, without vendor lock-in?
Where We Stand
We built UnderDefense MAXI to answer that question with yes, across your existing stack, at transparent pricing, with analysts who know your organization. Zero ransomware cases across 500+ clients in 6 years. 2-minute alert-to-triage. 830% ROI over 3 years.
Request a technical demo or start a 30-day proof of value to validate these claims with your own data.
1. What is the main difference between managed SIEM and MDR?
The core difference comes down to who responds when a threat is detected.
With managed SIEM, a third-party provider operates and tunes your SIEM platform (Splunk, Elastic, Sentinel), handling log ingestion, correlation rule tuning, and alert prioritization. However, when an alert fires, your internal team still investigates and responds. The provider creates a ticket; they don’t contain the threat.
MDR flips that model entirely. We, as an MDR provider, own the full detection-to-response lifecycle: detect, verify, contain, and remediate. We supply the detection technology, the 24/7 analysts, and the active containment capability.
The practical test is simple: at 2 AM, does the provider stop the threat, or do they send your team a ticket? Managed SIEM sends tickets. MDR stops threats. That distinction drives every downstream difference in staffing requirements, response time, and operational cost.
2. Can managed SIEM replace an MSSP, or do we need both?
It depends on whether your primary gap is detection or infrastructure management.
Managed SIEM optimizes detection from log data: correlation rules, alert tuning, and compliance reporting. MSSPs manage the infrastructure that generates that data: firewalls, VPNs, IDS/IPS devices, and patch management.
We recommend scoring your situation against five criteria:
-
Do you need device administration (firewall, VPN, endpoint management)?
-
Does your team handle incident response, or do you need a provider to contain threats?
-
Are compliance requirements met by log evidence alone?
-
Can your internal team manage the security stack operationally?
-
Is your primary goal noise reduction or full security operations offload?
If you scored detection + response + compliance as primary needs, you don’t need separate managed SIEM + MSSP. You need an MDR with managed SIEM capabilities built in. If infrastructure administration (device management, patching) is your primary gap, the MSSP still has a role, but that role is shrinking as MDR providers absorb MSSP functions.
3. Is SOCaaS the same as MDR, or are they different models?
They solve related but structurally different problems.
SOCaaS replicates full SOC workflows as a cloud-delivered subscription: Tier 1-3 triage, investigation narratives, escalation procedures, and reporting. We think of it as outsourcing your SOC team. MDR is outcome-focused: threats detected, contained, and remediated, regardless of internal workflow.
Five distinctions that matter:
-
SOCaaS delivers people + process (analysts who triage and report). MDR delivers outcomes (threats stopped).
-
SOCaaS may or may not include active response. MDR always includes active containment.
-
SOCaaS typically works across your existing tooling. MDR providers may supply proprietary detection stacks.
-
Gartner increasingly views SOCaaS as a delivery mechanism for MDR, not a separate category.
-
The lines are converging rapidly as security services spending grows at 11.1% in 2026.
We built UnderDefense MAXI as the convergence point: SOCaaS-level analyst depth combined with MDR-grade containment speed.
4. What does each managed security model cost, and what are the hidden expenses?
True cost extends far beyond the contract price. We map it across four dimensions: contract cost, internal staffing burden, hidden fees, and pricing model.
-
Managed SIEM: $60K-$120K/year, but requires 2-3 FTEs to investigate and respond. Hidden costs include SIEM licensing and log storage overage.
-
MDR: $50K-$200K+/year, requiring 0-1 FTE. Hidden costs include tool replacement fees if the vendor locks you into proprietary detection stacks.
-
MSSP: $80K-$300K/year, requiring 1-2 FTEs. Hidden costs include scope creep and per-device charges.
-
SOCaaS: $60K-$180K/year, requiring 1 FTE. Hidden costs include platform fees and per-alert pricing.
The key insight: managed SIEM is cheapest on paper but most expensive in total staff burden. We publish transparent $11-15/endpoint/month MDR pricing with zero hidden professional services fees and 30-day onboarding included.
5. Who owns the detection rules and data if we switch managed security providers?
This is the question most vendors hope you won’t ask during procurement.
The ownership split varies dramatically by model:
-
Managed SIEM: You own the SIEM instance, detection rules, log data, and playbooks. Full portability at termination.
-
MDR: The vendor typically owns detection logic, threat intelligence feeds, and playbooks. If you leave, those custom detections stay with them.
-
MSSP: You own infrastructure. Detection rules are mixed, with basic rules staying with you.
-
SOCaaS: The vendor typically owns the platform, detection logic, and investigation workflows.
We’ve seen CISOs lose months of custom correlation rules, insider threat integrations, and business-context configurations overnight when switching providers. We designed our architecture to prevent this: detection rules written in open languages (Python, SIGMA), versioned, and fully owned by you.
6. Which managed security model best supports SOC 2, HIPAA, and ISO 27001 compliance?
Each model supports different compliance frameworks through different evidence types:
-
Managed SIEM: Strong for SOC 2 and PCI DSS (log retention, review evidence). Weak for HIPAA and NIS2 because it generates log evidence but doesn’t enforce controls or provide incident response documentation.
-
MDR: Strong for HIPAA breach notification and NIS2/DORA regulatory reporting because it provides incident response evidence. Partial for SOC 2 and ISO 27001, which often need separate compliance add-ons.
-
MSSP: Strong for PCI DSS device policy enforcement and ISO 27001 policy management. Weak for incident reporting.
-
SOCaaS: Strong for SOC 2 investigation audit trails. Variable for everything else depending on provider scope.
We bundle forever-free compliance kits (SOC 2, HIPAA, ISO 27001, PCI DSS) with our MDR service, not as a separate product. This eliminates the need to purchase compliance automation from a third vendor.
7. How do we choose between managed SIEM, MDR, MSSP, and SOCaaS for our team size?
We recommend mapping your profile against four organizational archetypes:
-
0-2 security staff, no SIEM, compliance-driven: MDR with bundled SIEM + compliance. You need turnkey coverage, not tool management.
-
3-5 person team, existing SIEM investments: Vendor-agnostic MDR or co-managed SIEM + MDR overlay. Keep your tools; add detection + response.
-
5-10+ person team, partial SOC built: SOCaaS or co-managed MDR. Outsource Tier 1 triage while your team handles strategic decisions.
-
10+ person team, full SOC, infrastructure management needed: MSSP for infrastructure + MDR for threat operations.
Before signing any contract, score each provider on 8 criteria: vendor-agnostic integration, active containment, user verification, published pricing, documented response time, compliance inclusion, data portability, and onboarding timeline. Providers scoring 12+ out of 16 represent genuine security operations partners.
8. What is a co-managed security model, and is it better than choosing one service?
A co-managed model is the fastest-growing deployment pattern in 2026. It means your organization keeps internal Tier 2-3 analysts for business-context decisions while outsourcing Tier 1 triage and 24/7 monitoring coverage to an external partner.
This hybrid approach works because:
-
Tier 1 triage is commoditized, well-documented, and high-turnover work. Outsourcing it eliminates hiring and retention burden.
-
Tier 2-3 decisions require business context (VIP users, critical assets, organizational workflows) that internal teams understand best.
-
Co-managed SIEM, where you own the platform and a partner manages operations, has moved from tactical outsourcing to a strategic operating model.
We built UnderDefense MAXI for this convergence. Our analysts log into your SIEM, work alongside your internal team, handle Tier 1-2 triage, and escalate confirmed critical incidents to your Tier 3 team with full context. One contract replaces 3-4 fragmented vendor relationships.
The post Managed SIEM vs MDR vs MSSP vs SOCaaS: Which Model Fits? appeared first on UnderDefense.