Q1: What Is Managed SIEM Vendor Lock-In, and Why Is It Worse Than Self-Managed Lock-In?
Vendor lock-in in the SIEM context means you have built so much dependency on one platform, through proprietary data formats, custom integrations, specialized skills, and long-term contracts, that switching becomes technically painful and financially punishing. But here is what most articles on this topic miss entirely:
Managed SIEM vendor lock-in is a compounded, three-layer trap where your MSSP intermediary adds data access, detection IP, and institutional knowledge risks on top of the platform lock-in you would already face with a self-managed SIEM.
That distinction matters. When you manage your own Splunk or Sentinel instance, at least you control the keys. You see your data, you own your correlation rules, you know where the bodies are buried. With a managed SIEM arrangement, a third party holds those keys, and you may not realize how much you have handed over until you try to leave.
⚠️ The Three Compounding Layers
| Lock-In Layer | What It Means | Why It’s Worse in Managed SIEM |
|---|---|---|
| Platform Lock-In | Proprietary data schemas, query languages (SPL, KQL, AQL), and normalized formats | Same as self-managed, but you may lack direct access to even see the raw data |
| Provider Lock-In | MSSP controls access, tuning, operational knowledge, and environment baselines | Your team loses hands-on familiarity; the MSSP becomes the only entity that understands your environment |
| Contractual Lock-In | Termination penalties, auto-renewal traps, data export restrictions, notice period landmines | One MDR provider’s contract includes a 60-day renewal notice. Miss it, and you auto-renew everything |
🔍 SIEM Market Consolidation Makes This Urgent
The escape routes are shrinking. Cisco completed its $28 billion acquisition of Splunk in March 2024. Palo Alto Networks absorbed IBM’s QRadar SaaS assets, pivoting those customers toward Cortex XSIAM. LogRhythm and Exabeam merged under Thoma Bravo’s ownership. CrowdStrike has been acquiring adjacent capabilities aggressively. Fewer independent SIEM vendors means fewer alternatives when your managed SIEM contract comes up for renewal, and your MSSP knows it.
✅ How We Built UnderDefense to Prevent All Three Layers
This is exactly why we designed our MDR model to be vendor-agnostic from the ground up. Your data stays in your SIEM. We never hold raw logs in a proprietary data store. Detection logic is documented and portable. And our contracts include explicit data ownership and exit provisions, because a vendor that is confident in its value does not need to trap you.
As I have said many times: the right MDR partner should access the data where it lives, and you should control where that data lives. Some providers will refuse that model. Fine, but that is a red flag, not a feature.
Q2: How Does Managed SIEM Lock-In Develop Gradually, Even When You Don’t See It Coming?
It is contract renewal season. Your managed SIEM provider just sent a 22% price increase. You consider switching, then realize your team can’t access raw log data, your 300+ custom correlation rules are written in a proprietary query language, and the only person who understands your detection tuning works for the MSSP, not for you. You are locked in, and you didn’t even see it happen.
This scenario is not hypothetical but an operational reality I have watched unfold across dozens of organizations. I have heard it directly from CISOs who came to us after years of compounding dependency.
⏰ Why This Creeps Up Over 12–36 Months
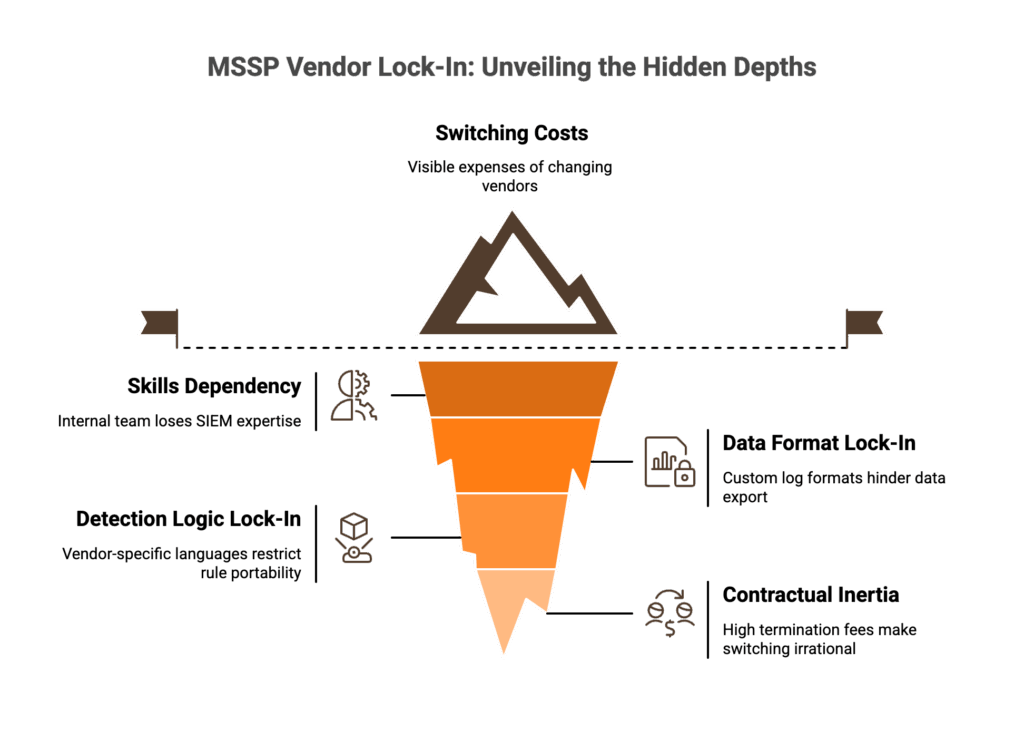
The MSSP gradually absorbs institutional knowledge: environment baselines, exception lists, user behavior context. Detection rules get written in proprietary syntax (SPL, KQL, AQL). Logs get normalized into proprietary schemas. Over time, switching costs compound silently across four dimensions:
- Skills dependency: your internal team stops touching the SIEM; tribal knowledge migrates to the provider
- Data format lock-in: custom log formats make export painful; some vendors prefer proprietary formats over open standards like CEF or Syslog
- Detection logic lock-in: correlation rules, automation playbooks, and SOAR integrations are built in vendor-specific languages
- Contractual inertia: long-term contracts with high termination fees (some with 50% penalties for early cancellation) make switching economically irrational
As one CISO I spoke with on our podcast put it plainly: when you make a vendor switch, “the business logic, the correlation rules, the automation rules, that does not come with you. And so when I switch to another vendor, I get to start all over on that tuning process.”
💸 The Hidden Costs Nobody Quotes You
- Staff hours for rule migration: 2–4 hours per complex rule × 200+ rules = 400–800+ engineering hours minimum
- Dual-licensing overlap: 3–6 months of running both platforms simultaneously
- Detection gap risk window: average 47 days to reach detection parity on a new platform
- Institutional knowledge loss: undocumented tuning decisions, exception lists, false positive suppression logic, all living in your MSSP’s heads, not yours
✅ The Ideal State vs. The Trap
The ideal state is simple: you retain data ownership in open formats, detection logic is documented in vendor-neutral syntax (like Sigma), and your MSSP provides a transition package as a contractual obligation. That is not aspirational. That is how we operate at UnderDefense by design. Your data never leaves your environment, detection rules are always documented and exportable, and we access your SIEM directly rather than pulling data into our proprietary platform.
From discovering you are trapped at renewal to knowing you can walk away any day with your data, rules, and institutional knowledge intact, that is the difference between a vendor and a partner.
“Anything you want to look at or changes you need to make in the product must go through their engineering team. As an MSP, this is a horrible way to do business for us.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
Q3: Who Actually Owns Your Data in a Managed SIEM Arrangement?
The honest answer for most organizations: you don’t actually know. And that ambiguity is the single biggest leverage point your MSSP holds over you at renewal time.
Data in a managed SIEM is not one monolithic thing. There are four distinct layers, and most managed SIEM contracts are vague about which layers the customer actually owns:
📑 The Four Data Layers
| Data Layer | Description | Typical Ownership Clarity |
|---|---|---|
| Raw Log Data | Original logs from your endpoints, firewalls, cloud services, identity providers | Usually yours, but can you access it directly? In what format? |
| Normalized/Enriched Data | Data transformed by the SIEM platform: parsed, enriched, indexed | Gray area. The MSSP’s platform created the enrichment; who owns the derivative? |
| Derived Insights | Alerts, incident reports, threat intelligence correlations, risk scores | Often treated as MSSP intellectual property |
| Historical Archives | Retention data, compliance-mandated log archives, forensic evidence | Yours in theory, but post-termination access timelines and egress fees can make retrieval impractical |
✅ Data Ownership Clarity Checklist
Before signing (or renewing) any managed SIEM contract, ask these seven questions:
- Can you export raw logs in standard formats (CEF, Syslog, JSON) on demand, not just at termination?
- What happens to your data post-termination? Is there a guaranteed access window (30/60/90 days)?
- Is there a data deletion certification after contract end?
- Who owns enrichment metadata and normalized data derivatives?
- What is the maximum data export timeline, and is it in the MSA, not just the SLA addendum?
- Is data accessible during dispute resolution, or does the MSSP hold it hostage?
- Are data egress fees capped or waived at termination?
⚖️ Legal Anchors You Should Reference
GDPR’s data portability requirements (Article 20) and CCPA provisions both establish precedent for customer data access and export rights. SaaS exit clause best practices also recommend explicit data ownership language in the Master Service Agreement (MSA), not buried in an SLA addendum that can be unilaterally modified. If your contract does not explicitly address all four data layers, silence favors the provider.
“Log collectors show working, however when asked to provide logs for an investigation no logs could be provided. Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing, $3B–$10B Arctic Wolf – Gartner Peer Review
How We Handle This at UnderDefense
Data stays in your SIEM instance, period. We never hold raw logs in a proprietary data store. Every engagement includes documented data ownership provisions in the contract. We log into your environment and work where your data lives, which means when the engagement ends, there is nothing to “export.” It was always yours.
“Their expert management of our SIEM has added to the value of our security investments and tools.”
— Yaroslava K., IT Project Manager UnderDefense G2 – Verified Review
Q4: Who Owns the Detection Rules Your MSSP Creates, and How Do Open Standards Make Them Portable?
Your MSSP has written 200+ custom correlation rules, tuned thresholds, built MITRE ATT&CK-mapped detection coverage, and created incident response playbooks. If you leave, can you take these with you? In most cases, the contract is silent on detection IP ownership, and silence favors the provider.
🔍 Three Categories of Detection Rules
Not all rules are equal when it comes to portability:
- Generic/community rules (Sigma, YARA): universally portable, vendor-neutral by design
- MSSP-developed rules in proprietary syntax (SPL, KQL, AQL): vendor-specific, require translation to migrate
- Custom rules with organizational context (environment baselines, exception lists, user behavior patterns): uniquely yours in substance, but the MSSP wrote them and may claim ownership
That third category is where disputes happen. As one CISO shared with me: he had built a non-standard integration connecting a project management system to his MDR team so analysts understood why certain employees worked odd hours. When he considered switching providers, that integration, and all the institutional context behind it, would vanish.
📋 Detection IP Protection Framework
Contract provisions you should negotiate before signing:
- Work-for-hire designation on all custom rules created for your environment
- Export rights in vendor-neutral formats (Sigma, YARA, human-readable logic descriptions)
- Documentation requirements: every rule should have a logic description, MITRE ATT&CK mapping, and tuning rationale
- Transition assistance obligations: the MSSP must provide a detection handover package as part of contract termination
⭐ How Open Standards Solve the Technical Portability Problem
Even with good contracts, you need technical portability. This is where open standards become your insurance policy:
| Capability | Proprietary Approach | Open Standard |
|---|---|---|
| Log Export | Vendor-specific normalized format; export requires professional services engagement | CEF, ECS, Syslog, JSON: export on demand |
| Detection Rule Migration | SPL/KQL/AQL rules must be manually rewritten for new platform | Sigma rules: “write once, run anywhere” detection logic |
| Enrichment Metadata | Locked in vendor’s enrichment engine | OCSF (Open Cybersecurity Schema Framework): vendor-agnostic core schema supported by AWS, Splunk, IBM, CrowdStrike |
| Schema Normalization | Platform-specific field names, enumerations, data types | OCSF enables stable field names across SIEM/XDR backends; detection logic authored once runs across different analytics engines |
OCSF is the big development here. It is an open-source project delivering an extensible, vendor-agnostic core security schema, and it is backed by AWS, Splunk, IBM, CrowdStrike, and others. Combined with Sigma for detection logic portability, organizations finally have a realistic path to “write once, detect anywhere.”
✅ How We Approach This at UnderDefense
All detection rules we create for clients are documented in human-readable format with MITRE ATT&CK mappings and exportable logic descriptions in vendor-neutral format. Our UnderDefense MAXI platform integrates with 250+ tools using open APIs and standard formats, ensuring portability regardless of the underlying SIEM.
The principle is straightforward: I want my MDR partner to log into my system. The business logic stays with me. If I change MDR providers, I keep my correlation rules, my automation, my institutional knowledge. That is not a feature request. That is a design philosophy.
“This is not an extension of our security team as was originally sold.”
— Sr. Cybersecurity Engineer, Manufacturing, $500M–$1B Arctic Wolf – Gartner Peer Review
“The platform itself is straightforward – it pulls in data from all our existing security tools, so we didn’t have to rip and replace anything.”
— Verified User in Marketing and Advertising UnderDefense G2 – Verified Review
Q5: What Are the Red Flags in Managed SIEM Contracts That Signal Future Lock-In?
Most security leaders don’t read their managed SIEM contract like a threat model, but they should. The lock-in doesn’t start when you try to leave. It starts the day you sign. And by the time you feel the friction, you’re already paying for it in lost flexibility, delayed migrations, and six-figure switching costs.
🔍 Score Your Managed SIEM Contract Now
Run your current (or prospective) managed SIEM agreement through these 8 criteria. Be honest: partial credit doesn’t count here.
☐ Data export formats and timelines specified: Does the contract name exact formats (CEF, JSON, OCSF) and guarantee export within 30 days post-termination?
☐ Detection rules designated as customer-owned IP: Are the rules your team built (or were built for you) classified as work-for-hire? Or does the provider claim ownership of the logic running on your data?
☐ Defined transition assistance period: Is there a minimum 90-day parallel-run obligation with documented knowledge transfer, or does service just… stop?
☐ Independent raw log access: Can you pull raw logs directly, without routing through the MSSP’s portal or ticketing system?
☐ Termination notice periods ≤60 days: Or are you locked into auto-renewal traps with narrow cancellation windows?
☐ Data egress/export costs explicitly capped or waived: Some providers charge per-GB egress fees that make leaving financially punitive.
☐ Data deletion certification post-exit: Will the provider confirm in writing (SOC 2-compliant) that your data is purged within 30 days?
☐ Auto-renewal terms clearly disclosed: No buried 60-day notice windows that silently extend multi-year commitments.
⚠️ Score Interpretation
| Score | Risk Level | Action |
|---|---|---|
| ✅ 6–8 | Low lock-in risk | Well-protected. Review annually |
| ⚠️ 3–5 | Moderate risk | Renegotiate before your next renewal cycle |
| ❌ 0–2 | High lock-in risk | Begin exit planning now |
This is not theoretical. The 60-day auto-renewal trap alone catches more teams than any zero-day.
“Beware they add a 60 day renewal notice instead of the typical 30 day notice. If you don’t give notice of cancelling any services before 60 days, you will automatically renew everything.”
— Verified User, Electrical/Electronic Manufacturing Arctic Wolf – G2 Verified Review
“We received little value from ArcticWolf. The product offered little visibility… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
✅ How UnderDefense Scores: 8/8 by Default
We built our contracts to pass this audit on day one, not because customers demanded it, but because that is how a confident provider operates.
- Transparent exit provisions with 30-day notice periods (not 60-day traps)
- Customer-owned detection IP: every rule, playbook, and integration documented in vendor-neutral formats
- Zero data egress fees: your data leaves when you do, at no extra cost
- Documented transition assistance baked into every MSA, not sold as a professional services add-on
If your current provider wouldn’t pass this checklist, that tells you something about how they plan to retain you: through value, or through friction.
Q6: What Should a SIEM Exit Strategy Contract Include? Five Non-Negotiable Clauses
The best time to negotiate exit terms is before you sign. These five clauses should be non-negotiable in every managed SIEM contract, yet fewer than 20% of agreements include all five. Here is what to demand, clause by clause.
Clause 1: Data Export Rights
Your contract must specify exact export formats (CEF, JSON, OCSF), guarantee delivery within 30 days of termination, and explicitly cap, or waive, data egress fees. Vague language like “data will be made available” is a red flag. If the format is not named, assume it will arrive in a proprietary dump that takes weeks of engineering to parse.
Clause 2: Detection Logic Ownership
Every detection rule, correlation logic, and playbook created for your environment should be classified as work-for-hire, meaning you own the intellectual property. Demand export in vendor-neutral formats (Sigma, YARA) with full documentation. If a provider won’t let you take the detection rules that were built on your data, for your threat landscape, that is not partnership but leverage.
Clause 3: Transition Assistance Obligation
Require a minimum 90-day parallel-run support period. This includes structured knowledge transfer sessions, environment documentation handover, and access to the provider’s analysts during the transition window. Without this, you are flying blind during the most vulnerable phase of any migration.
“Log collectors show working, however when asked to provide logs for an investigation no logs could be provided. Analysts provide little context, and when asked for more information… nothing is ever provided or even communicated.”
— CISO, Manufacturing ($3B–$10B) Arctic Wolf – Gartner Peer Review
When your current provider can’t even produce logs during active service, imagine what the transition looks like without contractual obligations.
Clause 4: Termination Without Cause
You need a 60-day maximum notice period with no punitive early termination fees beyond prorated costs. Multi-year contracts with vague termination language are designed to make leaving expensive, not to deliver value.
Clause 5: Data Deletion Certification
Demand written confirmation that all your data is purged within 30 days post-exit, following a SOC 2-compliant deletion process. This is not optional for regulated industries. It is a compliance requirement that should be standard everywhere.
Why UnderDefense Includes All Five by Default
We include every one of these clauses as standard contract terms, not because clients demand them, but because a provider confident in its value doesn’t need contractual handcuffs to retain customers. When your MDR partner competes on outcomes rather than lock-in, exit clauses are not a risk but a statement of confidence.
Q7: What Does a 90-Day Managed SIEM Exit Playbook Look Like, and What Will It Cost? [toc=90-Day Exit Playbook & Costs]
Switching managed SIEM providers is not just a procurement decision but an operational project with hard costs and real risk windows. Here is the phased playbook, with effort estimates and cost benchmarks.
Phase 1: Audit & Inventory (Weeks 1–2)
Catalog every log source, detection rule, dashboard, playbook, and integration currently running. Document which assets are customer-owned vs. MSSP-created. Identify data export format requirements and review contractual obligations from Q6 above. Estimated effort: 40–60 staff hours.
Phase 2: Parallel Environment & Rule Translation (Weeks 3–6)
Stand up the new SIEM/MDR environment while maintaining the old one. Implement dual-routing so logs feed both platforms simultaneously. Translate detection rules from proprietary syntax to vendor-neutral (Sigma), then to the new platform’s format. This is where the real cost hits. Estimated effort: 400–800 engineering hours for rule migration, plus dual-licensing overlap costs for 3–6 months.
“This is not an extension of our security team as was originally sold.”
— Sr. Cybersecurity Engineer, Manufacturing ($500M–$1B) Arctic Wolf – Gartner Peer Review
That gap between what is sold and what is delivered gets magnified tenfold during a migration, when you discover which rules were proprietary, which logs were accessible, and which documentation never existed.
Phase 3: Detection Parity Testing (Weeks 7–10)
Run both environments side by side. Compare alert volumes, MITRE ATT&CK detection coverage, and false positive rates. Validate that translated rules produce equivalent outcomes. Document gaps and remediate. Estimated effort: 80–120 staff hours; average 47 days to reach full detection parity.
Phase 4: Cutover & Decommission (Weeks 11–13)
Staged cutover: non-critical log sources first, then production. Confirm data export completeness. Request data deletion certification from the departing provider. Complete knowledge transfer documentation.
💰 Total Estimated Migration Cost (Mid-Market: 500–5,000 Endpoints)
| Cost Component | Estimate |
|---|---|
| Rule migration (400–800 hrs) | $40K–$80K |
| Dual licensing overlap (3–6 mo.) | $15K–$60K |
| Integration re-engineering (20–40 sources × 4–8 hrs) | $10K–$40K |
| Data egress fees | $0–$30K (provider-dependent) |
| Knowledge transfer sessions (40–80 hrs) | $5K–$20K |
| Total | $50K–$250K |
✅ How UnderDefense Compresses This Timeline
Our 30-day onboarding with vendor-agnostic integration reduces transition cost by 40–60%, because when your MDR partner works with your existing SIEM (not a proprietary replacement), migration means adding a partner, not rebuilding from scratch. You keep your log sources, your data stays where it is, and our AI SOC starts detecting on day one while analysts handle the context-building in parallel.
Q8: How Do You Evaluate a Managed SIEM Provider That Won’t Lock You In?
Switching managed SIEM providers is expensive. Choosing the wrong replacement means trading one lock-in for another. The question is not just “who has the best detection?” but “can I leave with my data, my rules, and my dignity intact?”
❌ Flawed Evaluation Criteria
Most teams default to the wrong filters: brand recognition (“they’re the biggest”), integration count on a marketing page (“they support our SIEM”), or cheapest sticker price. None of these answer the questions that matter. Can you leave with your data? Do you own your detection rules? Is pricing transparent, or designed to escalate after year one?
🔍 7 Lock-In Prevention Criteria
Rate each criterion 0 (not met), 1 (partial), or 2 (fully met):
- Vendor-agnostic integration: Works with your existing stack without requiring proprietary tool replacement
- Data ownership: Explicit contractual language guaranteeing your data stays yours, no proprietary data stores
- Detection rule portability: Rules documented in vendor-neutral format (Sigma/YARA), customer-owned IP
- Exit clause transparency: All 5 non-negotiable clauses from Q6 present in the MSA
- Pricing transparency: Published rates, no hidden egress fees, no usage-based surprises
- Onboarding speed: 30-day deployment, or 6-month professional services engagement?
- Human analyst access: Direct communication (ChatOps, Slack, phone), or ticket-based escalation queues?
Scoring: Providers scoring 10+ represent genuine operational partnership with low lock-in risk. Below 7 means you are trading one cage for another.
✅ Provider Comparison Scorecard
| Criterion | UnderDefense | Arctic Wolf | CrowdStrike |
|---|---|---|---|
| Vendor-agnostic integration | 2 | 0 | 1 |
| Data ownership | 2 | 1 | 1 |
| Detection rule portability | 2 | 0 | 1 |
| Exit clause transparency | 2 | 1 | 1 |
| Pricing transparency | 2 | 1 | 0 |
| Onboarding speed | 2 | 1 | 1 |
| Human analyst access | 2 | 1 | 1 |
| Total | 14/14 | 5/14 | 6/14 |
“Lack of true remediation in the response, costing us significantly in resources and introducing risks in security.”
— VP of Technology, Services ($50M+) Arctic Wolf – Gartner Peer Review
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated. Support incidents are not worked to completion and communication evaporates.”
— CISO, Manufacturing ($3B–$10B) Arctic Wolf – Gartner Peer Review
Why UnderDefense Scores 14/14
UnderDefense MAXI is purpose-built to meet every criterion because we designed an AI SOC with Human Ally support, not a proprietary platform that needs contractual leverage to retain customers. Vendor-agnostic integration across 250+ tools, transparent pricing at $11–15/endpoint/month, and direct analyst access via ChatOps mean the value is observable, auditable, and reproducible.
We maintain a 100% ransomware prevention record across 500+ MDR clients over 6 years, because we compete on outcomes, not on lock-in.
Q9: Which Managed Security Providers Offer the Best Lock-In-Free Experience?
The managed security providers with the strongest data portability, transparent contracts, and vendor-agnostic architectures include UnderDefense, Expel, and Red Canary, each with fundamentally different approaches to preventing lock-in.
⚠️ Why Lock-In Prevention Matters More Than Feature Lists
Managed security has evolved well beyond monitoring-only. The real differentiators for lock-in prevention sit at the architectural level: integration flexibility (vendor-agnostic vs. proprietary), data ownership provisions (explicit vs. vague), detection rule portability (open format vs. proprietary syntax), and exit clause transparency (published vs. hidden). If you can’t take your detection logic and log data with you when you leave, you don’t own your security posture. You’re renting it.
✅ Selection Criteria That Actually Prevent Lock-In
Here’s what separates providers that respect your independence from those that create dependency:
- Vendor-agnostic integration vs. proprietary stack requirements: Does the provider work with your existing SIEM, EDR, and cloud tools, or force you onto their platform?
- Explicit data ownership and export provisions vs. ambiguous contract language: Can you export your logs, detection rules, and incident data in standard formats at any time?
- Detection rules in open formats (Sigma, YARA) vs. proprietary syntax lock-in: If you leave, do your custom detections come with you or stay behind a paywall?
- Published pricing and exit terms vs. opaque “contact sales”: Are costs predictable, and can you cancel without a 60-day auto-renewal trap?
- Compliance and transition support included vs. separate add-on: Does migration assistance come standard, or is it an upsell when you try to leave?
🔍 Finding the Right Fit for Your Stack
Each provider excels in different scenarios. Your choice depends on your current stack, contract requirements, and whether you need pure SIEM management or full detection and response. UnderDefense integrates with 250+ existing tools without replacement. Expel works across select integrations but limits firewall and SaaS log support. Red Canary leans heavily on CrowdStrike as a primary telemetry source, which narrows flexibility for organizations running diverse stacks. For a comprehensive provider-by-provider comparison with pricing, response times, and integration capabilities, see our full breakdown:
This analysis is based on documented contract terms, G2 reviews, published pricing, and operational outcomes across 500+ MDR deployments.
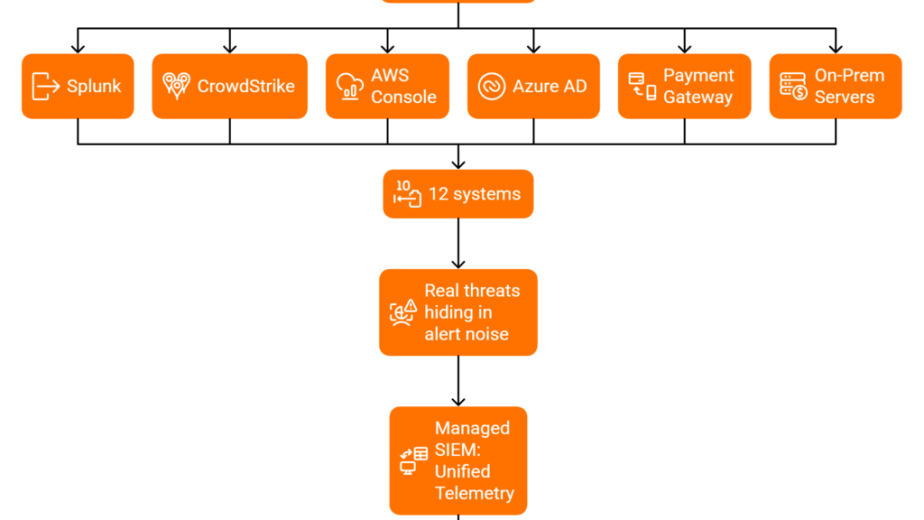
Q10: How Does UnderDefense’s Vendor-Agnostic MDR Model Eliminate SIEM Lock-In by Design?
The fundamental architectural flaw behind managed SIEM lock-in is deceptively simple: traditional MSSPs and MDR providers force you onto their proprietary platform, replacing your SIEM, ingesting data into their data store, and writing detections in their syntax. You don’t own the environment. You rent access to it. The moment you try to leave, your detection logic, historical logs, and operational context stay behind. That’s not a partnership but a hostage situation with a monthly invoice.
❌ How Competitors Build the Dependency Trap
Arctic Wolf requires proprietary SIEM replacement. Every customization, every alert tuning, every change must route through their engineering team. One G2 reviewer put it bluntly:
“Anything you want to look at or changes you need to make in the product must go through their engineering team. As an MSP, this is a horrible way to do business for us.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
Add the documented 60-day auto-renewal traps, and leaving becomes a logistical nightmare. CrowdStrike Falcon LogScale locks detection into its own ecosystem. ReliaQuest’s GreyMatter creates dependency on their correlation engine. The pattern is consistent across the industry: the more value the provider adds, the harder it becomes to leave.
🔑 The Architectural Shift: MDR on Top, Not Instead Of
True managed SIEM freedom requires the MDR layer to sit on top of the customer’s existing SIEM, not replace it. Detection logic should be documented in vendor-neutral formats. Data should never leave the customer’s environment. The provider’s value comes from expertise and response speed, not from holding your data hostage. This is how you build a security operations model where you stay because the outcomes are good, not because leaving is too expensive.
✅ How UnderDefense Is Built Differently
We designed the UnderDefense MAXI platform around a non-negotiable principle: your tools, your data, your rules. Here’s what that looks like operationally:
- 250+ existing tool integrations, including CrowdStrike, Splunk, SentinelOne, Elastic, and Microsoft Defender, with no platform replacement required
- Detection rules documented with MITRE ATT&CK mappings and exportable logic: you take your detections if you leave
- Concierge analysts verify threats via Slack/Teams, providing real context, not ticket escalation
- Published pricing ($11–15/endpoint/month), with no opaque “contact sales” surprises
- 30-day onboarding, not 6-month migrations that create switching-cost gravity
One IT Project Manager captured the difference after switching to UnderDefense:
“Their expert management of our SIEM has added to the value of our security investments and tools.”
— Yaroslava K., IT Project Manager UnderDefense G2 – Verified Review
And from a marketing team that needed integration without disruption:
“The platform itself is straightforward – it pulls in data from all our existing security tools, so we didn’t have to rip and replace anything.”
— Verified User in Marketing and Advertising UnderDefense G2 – Verified Review
⭐ Competing on Value, Not Contractual Leverage
UnderDefense maintains a 100% ransomware prevention record across 500+ MDR clients over 6 years, not because we lock customers in, but because we make it easy to stay and easy to leave. Every contract includes data portability, detection rule export, and transparent exit terms as standard. That’s the confidence of a partner who competes on outcomes, not contractual leverage.
1. What is managed SIEM vendor lock-in, and how does it differ from self-managed SIEM lock-in?
Managed SIEM vendor lock-in is a three-layer dependency trap that compounds platform lock-in, provider lock-in, and contractual lock-in into a single, escalating risk. With a self-managed SIEM, you face platform-level lock-in through proprietary query languages like SPL, KQL, or AQL and normalized data formats. That is painful enough. But when an MSSP manages your SIEM, the provider adds two additional layers on top.
First, your team loses hands-on familiarity with the environment. The MSSP becomes the only entity that understands your baselines, tuning decisions, and exception lists. Second, contractual mechanisms like auto-renewal windows, data egress fees, and termination penalties make leaving financially punitive.
We built our managed SIEM service to eliminate all three layers. We never hold raw logs in a proprietary data store, detection logic is documented and portable, and our contracts include explicit data ownership and exit provisions. The result: you stay because outcomes are good, not because leaving is too expensive.
2. How does managed SIEM lock-in develop gradually over 12 to 36 months?
Lock-in compounds silently across four dimensions over 12 to 36 months. Skills dependency grows as your internal team stops touching the SIEM and tribal knowledge migrates to the provider. Data format lock-in deepens as logs get normalized into proprietary schemas. Detection logic lock-in hardens as correlation rules, automation playbooks, and SOAR integrations are written in vendor-specific languages. Contractual inertia solidifies through long-term agreements with high termination fees.
The hidden costs are substantial: 400 to 800+ engineering hours for rule migration, 3 to 6 months of dual-licensing overlap, and an average 47-day detection gap before reaching parity on a new platform. Most teams only discover these costs at renewal, when a 22% price increase forces a switching analysis they are not prepared for.
We address this at UnderDefense by keeping detection rules always documented and exportable, accessing your SIEM directly rather than pulling data into our proprietary platform, and providing transition packages as a contractual obligation.
3. Who actually owns the data in a managed SIEM arrangement?
Data in a managed SIEM spans four distinct layers, and most contracts are vague about which the customer actually owns. Raw log data is usually yours, but direct access and export format matter. Normalized and enriched data sits in a gray area because the MSSP’s platform created the derivatives. Derived insights like alerts, incident reports, and risk scores are often treated as MSSP intellectual property. Historical archives are yours in theory, but post-termination egress fees and access timelines can make retrieval impractical.
Before signing or renewing, ask whether you can export raw logs in standard formats (CEF, Syslog, JSON) on demand, what happens to data post-termination, whether egress fees are capped or waived, and whether data is accessible during dispute resolution.
At UnderDefense, data stays in your SIEM instance, period. We log into your environment and work where your data lives, so when the engagement ends there is nothing to “export.” We also recommend referencing GDPR Article 20 and CCPA data portability provisions as legal anchors during contract negotiations.
4. Can I take my detection rules with me when I switch managed SIEM providers?
In most cases, the contract is silent on detection IP ownership, and silence favors the provider. Detection rules fall into three categories with very different portability profiles.
Generic and community rules written in Sigma or YARA are universally portable by design. MSSP-developed rules in proprietary syntax (SPL, KQL, AQL) require translation to migrate. Custom rules with organizational context, such as environment baselines, exception lists, and user behavior patterns, are uniquely yours in substance, but the MSSP wrote them and may claim ownership.
To protect yourself, negotiate work-for-hire designation on all custom rules, export rights in vendor-neutral formats, documentation requirements with MITRE ATT&CK mappings, and transition assistance obligations. Open standards like Sigma for detection logic and OCSF for schema normalization now provide a realistic path to “write once, detect anywhere.”
We document all detection rules we create for clients in human-readable format with exportable logic descriptions. Our SIEM correlation rules approach ensures your detection IP stays with you regardless of provider changes.
5. What red flags in a managed SIEM contract signal future vendor lock-in?
We recommend scoring your managed SIEM contract against eight criteria. Failing more than half should trigger immediate renegotiation or exit planning.
The eight criteria are: data export formats and timelines specified in the contract, detection rules designated as customer-owned IP, a defined transition assistance period of at least 90 days, independent raw log access without routing through the MSSP’s portal, termination notice periods of 60 days or fewer, data egress and export costs explicitly capped or waived, data deletion certification post-exit following SOC 2 compliance, and auto-renewal terms clearly disclosed without buried notice windows.
Scoring 6 to 8 means low lock-in risk. Scoring 3 to 5 means moderate risk that requires renegotiation before renewal. Scoring 0 to 2 means high lock-in risk, and you should begin exit planning now.
We built our contracts to score 8/8 by default. Our SOC provider evaluation checklist can help you audit your current provider against these benchmarks.
6. What does a SIEM exit strategy contract need to include?
Every managed SIEM contract should include five non-negotiable exit clauses, yet fewer than 20% of agreements contain all five.
Clause 1 is Data Export Rights: specify exact formats (CEF, JSON, OCSF), guarantee delivery within 30 days of termination, and cap or waive data egress fees. Clause 2 is Detection Logic Ownership: classify all custom rules as work-for-hire with export in vendor-neutral formats. Clause 3 is Transition Assistance Obligation: require a minimum 90-day parallel-run support period with structured knowledge transfer. Clause 4 is Termination Without Cause: 60-day maximum notice period with no punitive early termination fees beyond prorated costs. Clause 5 is Data Deletion Certification: written confirmation of data purging within 30 days post-exit following SOC 2-compliant processes.
We include every one of these clauses as standard contract terms in our managed detection and response agreements, not because clients demand them, but because a provider confident in its value does not need contractual handcuffs.
7. How much does it cost to switch managed SIEM providers?
For mid-market organizations with 500 to 5,000 endpoints, total migration costs typically range from $50K to $250K across five cost components.
Rule migration accounts for 400 to 800 engineering hours at $40K to $80K. Dual-licensing overlap runs 3 to 6 months at $15K to $60K. Integration re-engineering across 20 to 40 sources at 4 to 8 hours each costs $10K to $40K. Data egress fees range from $0 to $30K depending on the provider. Knowledge transfer sessions over 40 to 80 hours cost $5K to $20K.
The full migration follows a 90-day phased playbook: audit and inventory (weeks 1 to 2), parallel environment and rule translation (weeks 3 to 6), detection parity testing (weeks 7 to 10), and cutover and decommission (weeks 11 to 13). Average time to detection parity is 47 days.
Our vendor-agnostic onboarding at UnderDefense reduces transition cost by 40 to 60% because we work with your existing SIEM rather than replacing it. For a complete guide on the switching process, see our step-by-step provider switching guide.
8. Which managed security providers offer a vendor-agnostic, lock-in-free experience?
The providers with the strongest lock-in prevention architectures include UnderDefense, Expel, and Red Canary, but each takes a fundamentally different approach.
UnderDefense integrates with 250+ existing tools without replacement, keeps data in the customer’s SIEM, documents all detection rules in vendor-neutral formats, publishes pricing at $11 to $15 per endpoint per month, and includes all five exit clauses as standard contract terms. Expel works across select integrations but limits firewall and SaaS log support. Red Canary leans heavily on CrowdStrike as a primary telemetry source, which narrows flexibility for organizations running diverse stacks.
When evaluating providers, rate them on seven criteria: vendor-agnostic integration, data ownership, detection rule portability, exit clause transparency, pricing transparency, onboarding speed, and human analyst access. Providers scoring 10 or above out of 14 represent genuine operational partnership with low lock-in risk.
For a detailed provider-by-provider comparison, see our 12 best MSSP providers breakdown with pricing, response SLAs, and integration capabilities.
The post Managed SIEM Lock-In: Data Ownership, Exit Clauses, and Switching Costs Explained appeared first on UnderDefense.