Q1. What Is Managed SIEM Integration and Why Does It Matter for Your Security Stack?
Managed SIEM integration is a service model where an external provider operates, monitors, and optimizes your Security Information and Event Management platform, connecting it with your existing security tools to deliver unified threat detection and response without requiring you to build an in-house 24/7 SOC.
The Integration Chaos Problem
Here’s the operational reality: most organizations run 45+ security tools, CrowdStrike on endpoints, Splunk collecting logs, Okta handling identity, and separate consoles for AWS and Azure. Each tool generates alerts. None of them talks to each other in a meaningful way. Your security team becomes the manual correlation layer, spending nights piecing together whether that “suspicious login” alert actually connects to the “unusual process execution” on an endpoint.
This isn’t a tool’s problem. It’s an integration problem. And it’s exactly why managed SIEM integration matters more than raw detection capabilities.
Why Traditional Approaches Fall Short
❌ Legacy MSSPs offer monitoring but force you onto their proprietary platforms, meaning you abandon your Splunk investment and the detection rules you’ve spent years tuning. They forward alerts without organizational context, which just shifts the investigation burden back to you.
❌ Pure MDR providers like Arctic Wolf see threats but require you to replace your existing stack. One G2 reviewer described their experience:
“Anything you want to look at or changes you need to make in the product must go through their engineering team. As an MSP, this is a horrible way to do business for us.”
— Matt C., Manager, Cybersecurity Services Artic Wolf G2 Verified Review
The fundamental issue? Alert forwarding without AI-powered correlation creates more work, not less.
What True Integration Looks Like
True managed SIEM integration means the provider operates within your environment, not pulling data into their black box, but working inside your Splunk, your Elastic, your Microsoft Sentinel. They correlate alerts from your existing tools using AI-driven detection while providing 24/7 expert analysis.
The goal isn’t replacing your stack. It’s making it operationally effective.
This requires:
- Native connectors to your EDR, identity, and cloud platforms
- Detection rules written in portable formats (Sigma, YARA)
- Analysts who understand your business context, not just generic playbooks
- Response capabilities, not just escalation emails at 3 AM
How UnderDefense Approaches This
We built UnderDefence MAXI to be vendor-agnostic from day one. Our platform integrates with 250+ existing security tools, including Splunk, Elastic, Microsoft Sentinel, and every major EDR, providing unified AI-driven detection and human-led response without forcing tool replacement.
Our analysts operate directly in your SIEM environment. When we write detection rules, they’re yours. When we tune out false positives, those configurations stay with you. If you ever leave, you keep everything we built together.
“Their team was proactive in identifying and addressing threats, providing 24/7 oversight… UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk.”
— Oleg K., Director, Information Security G2 Verified Review
The Measurable Difference
Organizations using vendor-agnostic managed SIEM with AI-driven correlation report 40% faster threat detection versus proprietary-stack providers. The reason is straightforward: analysts can correlate across all existing telemetry sources rather than limited vendor-specific data. When you see the full picture, you catch threats faster and respond before damage spreads.
Q2. How Does Managed SIEM Splunk Compatibility Actually Work?
If you’ve invested in Splunk, whether Enterprise, Cloud, or Enterprise Security, the last thing you want is a managed provider who can’t work with it directly. The technical details of how providers integrate with Splunk matter enormously for your licensing costs, detection latency, and long-term flexibility.
Understanding Splunk Integration Paths
Splunk offers three primary deployment models, each with different integration requirements:
- Splunk Enterprise (on-prem): Full control over indexers and search heads, but you manage the infrastructure
- Splunk Cloud Platform: Splunk manages infrastructure; you manage configurations
- Splunk Enterprise Security (ES): Premium security layer with risk-based alerting and threat intelligence
Your managed SIEM provider needs to support whichever path you’re on, without forcing data egress that triggers additional Splunk licensing fees.
Technical Integration Methods
Most managed SIEM providers connect to Splunk through one of these methods:
| Method | Use Case | Latency | License Impact |
| HTTP Event Collector (HEC) API | Log ingestion from external sources | Low | Minimal |
| Splunk REST API | Alert forwarding, saved search triggers | Low | Minimal |
| Splunk SOAR Webhooks | Automated response orchestration | Very Low | Requires SOAR license |
| Direct Indexer Access | Advanced correlation, custom detection | Lowest | Requires analyst training |
The critical question: Does the provider operate in your Splunk, or do they require data export to their platform?
⚠️ Expert Tip
“Always validate whether the provider operates IN your Splunk or requires data EXPORT; the licensing and latency implications are significant. Exporting data externally can trigger Splunk’s data forwarding fees and add 30-60 seconds of detection latency that matters during active incidents.”
— UnderDefense SOC Team
Deployment Architecture Options
Option A: Provider-Hosted SIEM with Splunk Data Forwarding
- Your Splunk forwards events to the provider’s platform
- Potential licensing cost increases
- Added latency for detection
- Provider handles infrastructure
Option B: Provider Analysts Operating Within Your Splunk
- Analysts use your Splunk interface directly
- No data egress, no license surprises
- Real-time detection in your environment
- All configurations and rules remain yours
Common Compatibility Pitfalls
Before signing with any managed SIEM provider, verify these technical details:
- License implications: Does forwarding data trigger Splunk workload pricing?
- Latency considerations: How quickly do alerts reach analysts for triage?
- Rule compatibility: Do provider detection rules work alongside your existing Splunk correlation searches?
- ES integration: Can they leverage Splunk ES risk scores and notable events?
How UnderDefense Integrates with Splunk
We operate directly within your existing Splunk deployment. Our SOC analysts use your Splunk interface, configure custom detection rules in your environment, and provide a response without data egress or additional licensing complexity.
“Their expert management of our SIEM has added to the value of our security investments and tools.”
— Yaroslava K., IT Project Manager G2 Verified Review
This means:
- Detection rules written directly in Splunk SPL
- No forwarding fees or workload pricing surprises
- Sub-second detection latency
- Full rule ownership, everything we create stays with you
Q3. What Elastic SIEM Managed Service Options Exist Today?
Organizations choosing Elastic SIEM face three distinct paths: self-managed open-source with third-party SOC support, Elastic Cloud with separate security services, or fully managed Elastic through a specialized provider. Each model carries different costs, operational, and capability trade-offs that determine whether Elastic becomes an asset or a burden.
The Three Elastic Deployment Models
Model 1: Self-Managed Elastic (Open-Source)
You deploy and maintain Elastic Security on your infrastructure. This offers maximum flexibility and zero licensing costs, but requires significant internal expertise for detection engineering, rule tuning, and 24/7 monitoring.
⚠️ The hidden cost: most organizations underestimate the operational burden. A Reddit user considering Elastic SIEM noted the challenge: you need skilled engineers who understand both Elastic internals and detection engineering. Without that, you’re running infrastructure without effective security coverage.
Model 2: Elastic Cloud (Managed Infrastructure)
Elastic manages the infrastructure; you manage security operations. This reduces deployment complexity but doesn’t solve the core problem: you still need analysts watching alerts 24/7.
Model 3: Third-Party Managed Elastic SIEM
A specialized provider deploys, tunes, and operates Elastic Security within your environment with full analyst coverage. You get Elastic’s flexibility with enterprise-grade managed operations.
Side-by-Side Comparison
| Factor | Self-Managed | Elastic Cloud | Third-Party Managed |
| Infrastructure Cost | Hardware + maintenance | Elastic Cloud fees | Included in service |
| Operational Burden | High (24/7 coverage needed) | Medium (still need SOC) | Low (provider handles) |
| Detection Quality | Depends on the team’s skill | Depends on the team’s skill | 96% MITRE ATT&CK coverage |
| Response Capability | Your team responds | Your team responds | Provider contains threats |
| Compliance Support | Build your own reports | Build your own reports | Automated evidence collection |
| Time to Value | 3-6 months | 1-2 months | 30 days |
What Users Say About MDR Integration Challenges
The integration quality varies dramatically across providers. One Expel user described a common frustration:
“There is still a limit to the environmental/organizational knowledge inherent in the service. This leads to a fairly frequent need for engagement with our internal team to get clarification and verification.”
— Verified User, Computer Software Expel G2 Verified Review
This highlights why provider choice matters; generic MDR bolted onto Elastic doesn’t deliver the same value as purpose-built managed Elastic services.
UnderDefense’s Approach to Managed Elastic SIEM
We provide fully managed SIEM services, deploying, tuning, and operating Elastic Security within your environment with 24/7 analyst coverage, AI-driven threat hunting, and incident response included.
“The platform seamlessly integrates our existing security tools, simplifying management. Plus, it’s incredibly easy to deploy. I used to work with many MDR solutions in the past, and so far Underdefense is the best one!”
— Inga M., CEO G2 Verified Review
Who Should Choose What
- Self-managed: Large enterprises with 5+ dedicated security engineers and existing Elastic expertise
- Elastic Cloud: Organizations wanting infrastructure simplicity but maintaining an internal SOC team
- Third-Party Managed (UnderDefense): Teams wanting Elastic’s flexibility with full managed operations, without hiring a 24/7 analyst team
Q4. What API and Log Source Connections Should Your Managed SIEM Provider Support?
Integration capability isn’t a checkbox; it’s the difference between 30-day onboarding and 6-month delays. Before signing with any managed SIEM provider, audit their connector catalog against your actual environment. If they can’t ingest your critical log sources natively, you’ll face coverage gaps during the transition window when you’re most vulnerable.
Integration Capability Checklist
Score potential providers against these criteria. Each checkbox represents a critical integration category:
Endpoint Detection & Response (EDR)
- CrowdStrike Falcon
- SentinelOne
- Microsoft Defender for Endpoint
- Carbon Black
- Palo Alto Cortex XDR
Cloud Platforms
- AWS CloudTrail + GuardDuty
- Azure Activity Logs + Sentinel
- GCP Cloud Audit Logs
- Kubernetes audit logs
Identity Providers
- Okta
- Azure AD / Entra ID
- Ping Identity
- CyberArk
Network Security
- Palo Alto Networks
- Fortinet
- Cisco (ASA, Firepower)
- Zscaler
Log Format Flexibility
- CEF (Common Event Format)
- LEEF (Log Extended Event Format)
- Syslog (RFC 3164, RFC 5424)
- JSON
- Windows Event Logs
- CSV
Operational Requirements
- Custom log source onboarding within 30 days
- Bi-directional API for response actions (not just ingestion)
Score Interpretation
| Score | Assessment |
| 80%+ native support | ✅ Onboarding in weeks; minimal custom work |
| 60-80% support | ⚠️ Some custom connectors needed; 4-6 week delays possible |
| Below 60% | ❌ Significant development required; potential coverage gaps |
A Gartner reviewer flagged this exact issue with Alert Logic:
“Very limited compatibility/integration with other security tools… Everything is a very manual process, and the documentation is horrible.”
— IT InfoSec Manager Alert Logic Gartner Review
The Response Action Gap
⚠️ Most providers focus on ingestion, getting logs in. Fewer support bi-directional APIs that enable response actions: isolating endpoints, revoking credentials, and blocking IPs. Ask specifically: “Can you take containment actions through our existing tools, or do you just send us alerts to action ourselves?”
UnderDefense Integration Coverage
We maintain 250+ pre-built integrations with automatic log parsing and normalization across all major formats. Our dedicated onboarding engineers build custom connectors for any proprietary log source within your 30-day deployment window.
“It automates many tasks, plus, with 24/7 monitoring, we know we’re always protected. The platform seamlessly integrates our existing security tools, simplifying management.”
— Inga M., CEO G2 Verified Review
💡 Verification Step
Before signing any contract, request the provider’s full integration catalog and confirm connector status for your top 10 critical log sources. Ask specifically:
- Native connector or custom development required?
- Expected onboarding timeline for each source?
- Are response actions supported, or ingestion only?
Q5. How Do You Avoid SIEM Vendor Lock-In with Managed Providers?
Committing to a managed SIEM provider isn’t a quarterly purchase; it’s a multi-year architectural decision. Choose wrong, and you’re locked into proprietary tools with painful migrations ahead if you need to switch. I’ve seen organizations trapped with providers who no longer fit their security program maturity, unable to extract their detection logic or historical data.
❌ The Wrong Way to Evaluate
Most organizations choose based on brand recognition or “most integrations” claims without asking the hard questions: Can I export my detection rules in portable formats like Sigma or YARA? Do I own my historical data? What happens to my security posture if I leave? These questions determine your long-term flexibility, not feature checklists.
Many traditional MDR providers operate as black boxes. One G2 reviewer described Arctic Wolf as “an expensive black box” where “anything you want to look at or changes you need to make in the product must go through their engineering team”. That’s the opposite of transparency and ownership.
✅ Seven Criteria for Lock-In Avoidance
| Criteria | What to Ask | Red Flag |
| Data ownership | Can you export logs in standard formats? | “Data stored in proprietary format” |
| Detection rule portability | Are rules in Sigma/YARA or proprietary syntax? | “Rules only work in our platform.” |
| Integration approach | Do they work with your tools or require their stack? | “Replace your existing SIEM.” |
| Contract flexibility | What are exit terms and data transfer provisions? | 60-day auto-renewal traps |
| Historical retention | What happens to data if you terminate? | “Data deleted upon termination.” |
| SIEM platform choice | Can you change platforms without changing providers? | “We only support our SIEM.” |
| Response automation | Do playbooks transfer if you leave? | “Automations are proprietary.” |
⚠️ Real-World Lock-In Pain
A Gartner reviewer noted that their MDR provider’s analysts “provide little context, and when asked for more information in the investigation, nothing is ever provided”. When you can’t see inside the detection logic, you can’t learn, improve, or take it with you.
Another reviewer warned about contract traps: “Beware, they add a 60-day renewal notice instead of the typical 30-day notice. If you don’t give notice of cancelling any services before 60 days, you will automatically renew everything”.
Where UnderDefense Stands
We operate within your environment using your SIEM, Splunk, Elastic, and Microsoft Sentinel. All detection rules written in portable Sigma format, historical data, and configurations remain yours. We provide the analysts and expertise; you keep the platform and all intellectual property.
“UnderDefense deployed their MDR solution for 24/7 threat monitoring and integrated all our existing security tools into one easy-to-manage platform.”
— Inga Miller, CEO, Network Security Company Clutch Verified Review“The seamless integration of our existing tools, the 24/7 monitoring, the rapid AI-driven threat response… it all added up to a truly impressive solution.”
— Inga Miller, CEO, Network Security Company Clutch Verified Review
💡 The Meta-Insight
The real question isn’t “Which managed SIEM has the best lock-in terms?” It’s “Which provider operates within my environment rather than forcing me into theirs?” That architectural difference eliminates lock-in entirely. When your provider is vendor-agnostic and works with your existing stack, switching becomes a staffing decision, not a migration project.
Q6. What’s the Difference Between Managed SIEM and Co-Managed SIEM?
Organizations evaluating managed SIEM face a fundamental choice: fully managed (provider handles everything) or co-managed (shared responsibilities). The right model depends on your internal team size, expertise level, and desired control over detection rules and response actions.
Fully Managed: Outsource the Operations
In a fully managed model, the provider handles all SIEM operations, log ingestion, detection rule development, alert triage, threat hunting, and incident response. Your team receives confirmed incidents and response recommendations.
Best for:
- Organizations with fewer than 3 security FTEs
- Teams wanting to redirect internal resources to strategic initiatives
- Companies lacking 24/7 coverage capability
As one experienced CISO explained: “For smaller companies and smaller organizations may not have the luxury or the ability to hire in-house staff… a fully outsourced team starts to be a real solution there for folks that can’t build their own”.
Co-Managed: Shared Responsibility
Responsibilities are split between the provider and internal team. Typically, the provider handles 24/7 monitoring and initial triage while your team manages detection rule customization, investigation escalations, and response decisions.
Best for:
- Organizations with existing SOC teams (3-10 FTEs)
- Teams needing coverage extension, not replacement
- Companies wanting to maintain detection engineering control
“If I can offshore or have a contractor or a partner take on the level one work, that work tends to be very commoditized, very documented, easy to bring somebody on and train them up… So it might make sense for me to ask a vendor to manage that turnover. But I still keep a level two or level three team in-house”.
📊 Responsibility Matrix
| Function | Fully Managed | Co-Managed |
| Log source management | Provider | Shared |
| Detection engineering | Provider | Customer-led |
| Alert triage (24/7) | Provider | Provider |
| Threat hunting | Provider | Shared |
| Incident response decisions | Provider recommends | Customer decides |
| Compliance reporting | Provider | Shared |
| Strategic security planning | Shared | Customer-led |
| Cost differential | Higher | 20-30% lower |
⏰ The Hybrid Sweet Spot
The strategic value of co-managed comes from the business context. “I want a senior security analyst who understands how the business works on the inside; they’re in a much better place to make judgments on risk”.
In a hybrid model, you can offload the labor management aspects of level one work while keeping business-critical judgment internal. When tier-one flags something requiring deeper analysis, it escalates to your tier-two team with organizational knowledge.
UnderDefense Flexibility
UnderDefense offers both models with seamless transition paths. Start fully managed during initial deployment, then shift to co-managed as your internal team matures. Our UnderDefence MAXI platform supports both operating models without re-implementation.
The key insight: “Knowledge management stays within the team, but now they’re able to focus that on a particular customer. And so as an organization that needs help funding or sourcing labor for their security program, the fully outsourced model makes sense in a lot of ways and starts to get multiplier effects”.
💰 Cost Considerations
Co-managed typically runs 20-30% lower than fully managed, but requires internal investment in senior security talent. The calculation: Is the cost of maintaining tier-two/three analysts lower than the premium for fully managed services?
Q7. How Should Managed SIEM Integrate with Your EDR, SOAR, Identity Tools, and Microsoft Sentinel?
True managed SIEM integration means correlating across your entire security stack, not just ingesting logs. The difference between “we support 250 tools” and “we correlate 250 tools in real-time” is the difference between alert noise and actionable intelligence.
🔗 How Cross-Stack Correlation Works
EDR Integration: Pulls endpoint context, process trees, file hashes, and network connections to enrich SIEM alerts. When your SIEM detects suspicious PowerShell execution, the EDR context shows whether it’s a legitimate admin script or malware staging.
Identity Integration: Adds user context, role, department, location, and behavior baseline. A login from an unusual location means something different for a traveling executive than for a data center engineer.
SOAR Integration: Enables automated response playbooks. Detection triggers containment actions without waiting for analyst intervention at 2 AM.
Microsoft Sentinel Integration: For organizations invested in Azure, managed providers should operate within Sentinel’s KQL-based detection framework while adding 24/7 analyst coverage. You shouldn’t need to forward data elsewhere; analysts should work inside your existing Sentinel environment.
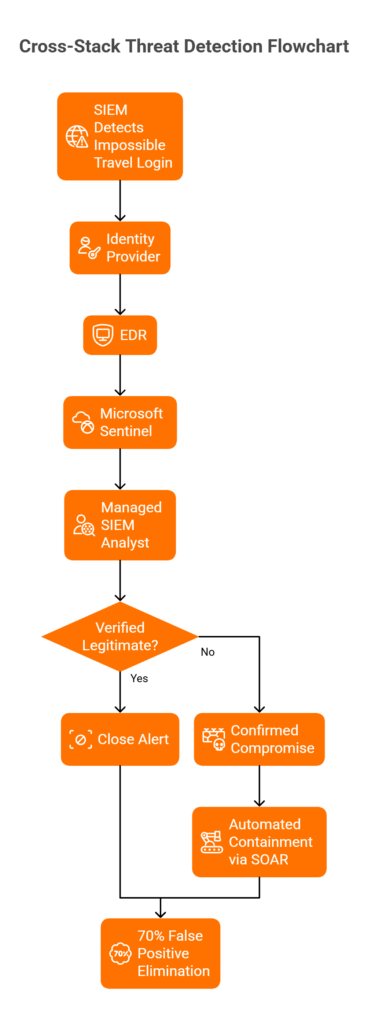
Scenario: Cross-Stack Detection in Action
When SIEM detects an impossible travel login:
- Identity provider confirms first-time device
- EDR shows no endpoint compromise indicators
- Microsoft Sentinel correlates the Azure AD sign-in risk score
- Managed SIEM contacts user directly for verification
This cross-stack correlation eliminates 70% of false positives that single-source detection creates. Without it, you’re escalating every anomaly and burning analyst hours on noise.
⚠️ Common Integration Failures
Many providers claim extensive integration lists but deliver shallow connections. A Gartner reviewer noted: “Missing integrations with key products like CyberArk… This is not an extension of our security team as was originally sold”.
Another warned about documentation gaps: “Some of the articles are fantastic and provide great details about the topics, while others feel outdated as a result of changes outside of [the provider’s] control, e.g., when Google makes changes to how logging works, there is a lag to when documentation is updated”.
Why Multi-Platform Architecture Matters
Organizations with integrated managed SIEM (EDR + Identity + Cloud + existing SIEM correlated) report significantly faster MTTR than those with siloed monitoring, because context eliminates noise.
EXPERT TIP: “The biggest ROI comes from correlating identity + endpoint + cloud in real-time. Most providers do log collection; few do cross-stack reasoning.” — UnderDefense Detection Engineering Team
UnderDefense Multi-Platform Architecture
The UnderDefence MAXI platform ingests from 250+ tools and correlates alerts across:
- EDR: CrowdStrike, SentinelOne, Microsoft Defender
- Identity: Okta, Azure AD, Ping
- Cloud: AWS, Azure, GCP native logs
- Existing SIEM: Splunk, Elastic, Microsoft Sentinel
We don’t replace your stack; we make it work together. Analysts understand cross-stack attack patterns because they see the full picture, not fragmented alerts from disconnected tools.
“They integrated all our existing security tools into one easy-to-manage platform… We now have 24/7 threat detection and response, which we were looking for, and centralized management of our security tools.”
— Inga Miller, CEO, Network Security Company Clutch Verified Review
Q8. What Questions Should You Ask When Evaluating Managed SIEM Providers?
Evaluating managed SIEM providers requires specific validation questions, not feature comparisons. The right questions expose operational reality versus sales promises.
📋 Integration & Detection Questions (1-4)
1. What percentage of our current stack do you support with native connectors?
Native connectors matter more than total integration count. A provider supporting 500 tools but requiring custom development for your core stack creates deployment delays.
2. How long does custom log source onboarding take?
Benchmark: 2-4 weeks for standard sources, 6-8 weeks for custom. Longer timelines indicate operational immaturity.
3. Do you operate within our SIEM or require data forwarding to your platform?
This question reveals lock-in risk. Providers requiring data forwarding create dependency; those operating within your environment maintain your control.
4. What’s your MITRE ATT&CK technique coverage percentage, and can you document it?
Ask for coverage maps, not marketing claims. Mature providers track detection coverage against ATT&CK and identify gaps transparently.
⚡ Response & Operations Questions (5-7)
5. What is your documented MTTR for critical incidents, with case study evidence?
Sales teams quote best-case numbers. Ask for documented case studies showing actual response timelines across different incident types.
6. Do you contain threats or only escalate?
Critical distinction. A Gartner reviewer noted their provider “overly relies on the client’s team for remediation, which really hurts the value of the service”. True MDR takes action, not just alerts.
7. How do you verify suspicious activity? Do you contact users directly or escalate back to our team?
User verification is operationally critical. If providers escalate every “unusual login” to your team for verification, you’re paying for alert forwarding, not managed detection.
💸 Pricing & Contract Questions (8-10)
8. Is pricing published or “contact sales”? What’s included vs. add-on?
Transparent pricing signals confidence. Hidden pricing often hides complexity and upsells.
9. What are exit terms and data portability provisions? Are detection rules exportable?
Review contract language carefully. One reviewer warned: “60-day renewal notice instead of the typical 30-day notice. If you don’t give notice… you will automatically renew”.
10. Are there hidden costs for log volume, alert counts, or compliance reporting?
Ask specifically about overage charges. One user noted their provider had “a 50GB a day cap on log collection, which was not brought to our attention during the whole buying phase”.
✅ UnderDefense Transparency
UnderDefense publishes pricing ($11-15/endpoint/month), provides documented MTTR with case studies, and offers a 30-day trial period, so you can validate answers rather than trust sales claims.
“We appreciated that they offered multiple alternative solutions that suited our budget.”
— Denis Volokh, CTO, Noviscient Pte Ltd Clutch Verified Review
Q9. What Does Managed SIEM Onboarding Look Like And How Do You Measure Success?
Onboarding a managed SIEM provider is where promises meet reality. I’ve seen deployments drag on for months because vendors weren’t upfront about what’s involved, and I’ve seen others go live in under 30 days with full detection coverage. The difference comes down to process discipline and clear milestones you can actually verify.
The Four Phases That Matter
A well-structured onboarding follows predictable phases, each with deliverables you should validate:
- Discovery & Scoping (Week 1): Environment assessment, log source inventory, integration prioritization, and baseline threat landscape review. If your provider can’t articulate which log sources are critical by day 5, that’s a red flag.
- Technical Integration (Weeks 2-3): API connections established, log forwarding validated, initial data normalization confirmed. This is where most vendors stall, particularly those requiring proprietary data forwarding versus those who work within your existing SIEM.
- Detection Tuning (Weeks 3-4): False positive reduction targeting 90%+ noise elimination, custom detection rules deployed for your environment, and baseline behavior models established.
- Operational Handoff (Week 4+): Runbook documentation, escalation procedures, and communication channels (Slack/Teams) configured.
⚠️ Red Flags During Onboarding
Watch for these warning signs:
- Providers requiring 3-6 month deployments should be 30-60 days maximum for standard environments
- Inability to integrate your critical log sources in the initial phase
- Detection tuning not included in standard onboarding (expect ongoing noise)
- No dedicated onboarding engineer assigned to your account
- “We’ll figure it out as we go,” instead of documented milestones
90-Day Success Scorecard
Here’s how to measure whether your integration actually worked:
| Metric | Target | Indicates |
| MTTR for critical incidents | Below 1 hour | Response capability |
| Alert noise reduction | 90%+ vs. baseline | Tuning effectiveness |
| MITRE ATT&CK coverage | Above 90% | Detection breadth |
| Analyst hours recovered | Measurable weekly | Operational value |
| Compliance evidence automation | Functional | GRC integration |
| Missed high-severity incidents | Zero | Reliability |
Meeting 5-6 of these indicates successful integration. Below 3 suggests fundamental issues requiring escalation.
What Real Customers Experience
“The speed of onboarding was a delightful surprise. In times where integrating new systems can take weeks, UnderDefense had us up and running in no time.”
— Valeriia D., Marketing Specialist G2 Verified Review“Getting all our logs and stuff flowing took longer than I expected.”
— Andriy H., Co-Founder and CTO G2 Verified Review
These experiences reflect reality: onboarding complexity varies by environment, but timeline expectations should be clear upfront.
✅ UnderDefense Benchmarks
We complete full integration within 30 days, including all log source connections, custom detection tuning, achieving 99% noise reduction, and dedicated analyst assignment. Clients achieve 0.5-hour MTTR and 96% MITRE ATT&CK coverage with metrics visible in the UnderDefence MAXI dashboard from day one. The key difference: we work within your existing SIEM rather than requiring migration, which eliminates the longest phase of most onboarding projects.
Q10. How Does Managed SIEM Support Compliance Requirements (HIPAA, PCI DSS, ISO 27001)?
Compliance and security monitoring shouldn’t be separate workstreams. When they are, you’re duplicating effort, manual evidence collection, scattered audit trails, and the inevitable scramble before assessments. The right managed SIEM integration eliminates this by making security operations generate compliance documentation automatically.
The Compliance Intersection
Managed SIEM directly supports multiple frameworks by providing continuous monitoring, audit log retention, incident detection/response documentation, and automated evidence collection. The operational activities your SOC performs daily, alert triage, incident investigation, and access monitoring, are precisely what auditors want to see documented.
HIPAA Requirements Addressed
45 CFR § 164.312 requires audit controls and monitoring of PHI access. Here’s how managed SIEM maps:
- Continuous monitoring of EHR access patterns and anomaly detection
- Automated alerting on unauthorized PHI access attempts
- Audit trail retention meeting 6-year requirements
- Incident response documentation for breach notification compliance
Healthcare organizations running managed SIEM for healthcare can demonstrate “reasonable and appropriate safeguards” with actual operational evidence rather than policy documents alone.
PCI DSS 4.0 Requirements Addressed
Requirements 10.x mandate logging and monitoring of cardholder data environments:
| PCI DSS Requirement | Managed SIEM Capability |
| 10.4 (Real-time monitoring) | Continuous CDE access monitoring |
| 10.5 (Log integrity) | Log integrity verification and tamper detection |
| 10.6 (Security event review) | Automated review with analyst escalation |
| 10.7 (Retention) | 12-month accessibility requirements met |
The shift from PCI DSS 3.2.1 to 4.0 emphasizes continuous monitoring over point-in-time assessments, exactly what managed SIEM delivers.
ISO 27001 / SOC 2 Alignment
A.12.4 (Logging and Monitoring) and CC7.x (System Monitoring) controls map directly to managed SIEM capabilities:
- Continuous security event monitoring with documented detection logic
- Incident response procedures with timestamped evidence trails
- Automated compliance reporting for audit readiness
- Access control monitoring across identity systems
For SOC 2 Type II specifically, the continuous nature of managed SIEM operations demonstrates control effectiveness over time, not just design adequacy.
⏰ The Evidence Generation Problem
Most compliance failures aren’t security failures; they’re documentation failures. Security teams detect and respond to threats, but don’t capture the evidence trail auditors require. Managed SIEM with proper compliance integration solves this by generating audit artifacts as a byproduct of operational work.
✅ UnderDefense Compliance Integration
We include forever-free compliance kits with MDR service, automated evidence collection, pre-built compliance dashboards, and audit-ready reporting for HIPAA, PCI DSS, SOC 2, and ISO 27001. Security monitoring generates compliance documentation automatically, eliminating dual workstreams.
“UnderDefense also helped us navigate key compliance requirements, ensuring we met industry standards smoothly and efficiently.”
— Arman N., CTO G2 Verified Review
Q11. Why Do Organizations Choose Vendor-Agnostic Managed SIEM Over Single-Vendor Solutions?
This is one of the most important architectural decisions you’ll make, and it’s often glossed over during sales conversations. The choice between vendor-agnostic providers who work with your existing Splunk/Elastic/Sentinel stack versus single-vendor solutions requiring proprietary platform adoption has lasting consequences for flexibility, cost, and institutional knowledge.
The Single-Vendor Approach
Providers like Arctic Wolf offer comprehensive coverage but require adopting their proprietary SIEM. The pitch is simple: one vendor, one platform, one throat to choke. The reality:
- Existing investments abandoned: Your Splunk or Elastic deployment (often $100K+ annually for enterprise licenses) becomes sunk cost
- Detection rules left behind: The correlation logic and custom rules you’ve built over the years don’t transfer
- Migration timeline: Typically 3-6 months before full operational capability
- Lock-in established: Switching providers later means repeating the entire process
“The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services G2 Review
The Vendor-Agnostic Approach
Providers like UnderDefense operate within your existing environment, protecting your tool investments while adding 24/7 expert operations and AI-driven detection:
- Existing tools preserved: Your Splunk, Elastic, or Sentinel deployment continues operating
- Detection rule ownership: All correlation logic stays with you, portable if you change providers
- Faster integration: No platform migration required, typically 30 days to operational
- Exit strategy viable: Switch managed providers without rebuilding detection capabilities
💰 Side-by-Side Comparison
| Factor | Single-Vendor (Arctic Wolf) | Vendor-Agnostic (UnderDefense) |
| Existing tool preservation | ❌ Requires abandonment | ✅ Works within your stack |
| Migration effort | 3-6 months typical | 30 days typical |
| Detection rule ownership | ❌ Stays with provider | ✅ You retain ownership |
| Long-term flexibility | ❌ Platform lock-in | ✅ Provider-independent |
| Sunk cost impact | 💸 Write off existing investment | ✅ Protects existing investment |
| Pricing transparency | Contact sales | $11-15/endpoint/month |
Decision Criteria
Choose single-vendor if:
- Starting fresh with no existing SIEM investment
- Prefer one-vendor simplicity over flexibility
- Don’t anticipate needing to change platforms
Choose vendor-agnostic if:
- An established Splunk/Elastic/Sentinel deployment exists
- Want to protect existing investments ($100K+ annually)
- Need flexibility to change SIEM platforms without changing managed providers
- Value detection rule portability
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk.”
— Oleg K., Director, Information Security G2 Verified Review
The lesson from experience: all your business logic, correlation rules, automation playbooks, and tuning decisions should stay with you. When you partner with a SIEM vendor, control where that data lives and ask your MDR partner to log in to your system, not the other way around.
Q12. Which Managed SIEM and SOC Providers Lead the Market for Integration Flexibility?
The managed SIEM market has bifurcated. On one side: vendor-agnostic providers who enhance your existing investments. On the other hand, platform providers who replace them. Understanding which approach each vendor takes is essential before any conversation.
Market Leaders for Integration Flexibility
The leading managed SIEM providers for integration flexibility in 2026:
- UnderDefense: 250+ integrations, operates within your existing SIEM (Splunk, Elastic, Sentinel), transparent pricing ($11-15/endpoint/month)
- Expel: Strong API-first approach, good documentation, though organizational knowledge retention can be inconsistent
- Select boutique providers: Various regional players with genuine integration depth
Platform-replacement providers (require proprietary adoption):
- Arctic Wolf, ReliaQuest, and several traditional MSSPs
Selection Criteria to Evaluate
When comparing providers, validate these factors:
✅ Vendor-agnostic integration vs. proprietary stack requirements, does the provider work within your existing SIEM or require migration?
✅ Native Splunk/Elastic/Sentinel support depth, not just “we integrate” but actual operational capability within these platforms
✅ Human analyst access model, direct communication (Slack/Teams) versus ticket-based escalation
✅ Published response time SLAs with case study evidence; claims without verification are marketing
✅ Transparent per-endpoint pricing, contact-sales models often hide true costs
The Integration Approach Matters
Providers claiming “250+ integrations” may mean data forwarding to their platform or actual operation within your environment. The distinction is critical:
- Data forwarding: Your logs leave your environment; business logic builds in their system
- In-environment operation: Provider analysts work within your SIEM; you retain all configuration and detection rules
📚 Where to Go Deeper
1. What is managed SIEM integration, and how does it differ from traditional MSSP monitoring?
Managed SIEM integration is a service model where an external provider operates, monitors, and optimizes your Security Information and Event Management platform while connecting it with your existing security tools. The critical difference from traditional MSSP monitoring lies in where the work happens.
Traditional MSSPs typically pull your data into their proprietary platforms, forcing you to abandon existing investments and the detection rules you’ve built over the years. We take a fundamentally different approach with our managed SIEM service. Our analysts operate directly within your environment, whether that’s Splunk, Elastic, or Microsoft Sentinel. This means:
- No data egress or additional licensing fees
- All detection rules and configurations remain yours
- Sub-second detection latency versus 30-60 second delays with data forwarding
- Complete visibility into detection logic (no black boxes)
The operational reality is that most organizations run 45+ security tools that don’t communicate effectively. Managed SIEM integration solves the correlation problem by making your existing stack work together rather than replacing it entirely.
2. How do managed SIEM providers integrate with Splunk without triggering additional licensing costs?
The integration method determines whether you face licensing surprises. There are two fundamental approaches:
Data forwarding (problematic): Your Splunk forwards events to the provider’s platform. This can trigger Splunk’s workload pricing tiers and data forwarding fees, adding 20-40% to your annual Splunk costs while introducing 30-60 seconds of detection latency.
In-environment operation (preferred): The provider’s analysts work directly within your Splunk interface using native APIs. No data leaves your environment, so there are no additional licensing implications.
We operate using the second approach with our MDR for Splunk service. Our SOC analysts use your Splunk interface, configure custom detection rules in your environment using native SPL, and provide response capabilities without data egress.
Key questions to ask any provider:
- Do you require data forwarding to your platform?
- Will integration trigger Splunk workload pricing changes?
- Are detection rules written in portable formats or proprietary syntax?
The licensing implications are significant enough that this should be verified in writing before contract signing.
3. What are the key criteria for avoiding SIEM vendor lock-in with managed providers?
Vendor lock-in risk should be evaluated across seven specific criteria before committing to any managed SIEM provider:
|
Criteria |
What to Verify |
Red Flag |
|
Data ownership |
Can you export logs in standard formats? |
“Data stored in proprietary format” |
|
Detection rule portability |
Are rules in Sigma/YARA or proprietary syntax? |
“Rules only work on our platform.” |
|
Integration approach |
Do they work within your tools? |
“Replace your existing SIEM.” |
|
Contract flexibility |
Exit terms and data transfer provisions |
60-day auto-renewal traps |
|
Historical retention |
What happens to data if you terminate? |
“Data deleted upon termination.” |
|
SIEM platform choice |
Can you change SIEMs without changing providers? |
“We only support our SIEM.” |
|
Response automation |
Do playbooks transfer if you leave? |
“Automations are proprietary. |
We designed our UnderDefence MAXI platform to eliminate these lock-in risks. All detection rules are written in portable Sigma format, historical data remains yours, and we operate within your existing environment rather than forcing migration to our platform.
4. What's the difference between fully managed SIEM and co-managed SIEM services?
The choice depends on your internal team size, expertise level, and desired control over detection engineering.
Fully Managed SIEM:
- Provider handles all operations: log ingestion, detection rules, alert triage, threat hunting, and incident response
- Your team receives confirmed incidents and response recommendations
- Best for organizations with fewer than 3 security FTEs or lacking 24/7 coverage capability
- Higher cost, lower internal resource requirement
Co-Managed SIEM:
- Responsibilities are split between the provider and the internal team
- Provider handles 24/7 monitoring and initial triage
- Your team manages detection rule customization and response decisions
- Best for organizations with existing SOC teams (3-10 FTEs) wanting coverage extension
- 20-30% lower cost than fully managed
We offer both models through our Security Operations Center service with seamless transition paths. Many clients start fully managed during initial deployment, then shift to co-managed as their internal team matures.
The strategic value of co-managed comes from the business context. Your internal analysts understand organizational risk better than any external provider. The hybrid sweet spot is offloading tier-one labor management while keeping business-critical judgment internal.
5. How long does managed SIEM onboarding take, and what milestones indicate success?
A well-structured onboarding should be completed within 30-60 days for standard environments. Any provider requiring 3-6 months is a red flag.
The Four Phases:
- Discovery & Scoping (Week 1): Environment assessment, log source inventory, integration prioritization
- Technical Integration (Weeks 2-3): API connections established, log forwarding validated, data normalization confirmed
- Detection Tuning (Weeks 3-4): False positive reduction targeting 90%+ noise elimination, custom detection rules deployed
- Operational Handoff (Week 4+): Runbook documentation, escalation procedures, and communication channels configured
90-Day Success Metrics:
- MTTR for critical incidents below 1 hour
- Alert noise reduction of 90%+ versus baseline
- MITRE ATT&CK coverage above 90%
- Analyst hours recovered (measurable weekly)
- Zero missed high-severity incidents
We complete full integration within 30 days, achieving 99% noise reduction and 0.5-hour MTTR with metrics visible in your dashboard from day one. Review our case studies for documented onboarding timelines across different environments.
6. How does managed SIEM support compliance requirements like HIPAA, PCI DSS, and ISO 27001?
Managed SIEM directly supports multiple compliance frameworks by making security operations generate audit documentation automatically, eliminating the dual workstream problem where security and compliance teams duplicate effort.
HIPAA (45 CFR § 164.312):
- Continuous monitoring of EHR access patterns
- Automated alerting on unauthorized PHI access attempts
- Audit trail retention meeting 6-year requirements
- Incident response documentation for breach notification
PCI DSS 4.0 (Requirements 10.x):
- Real-time CDE access monitoring (Req 10.4)
- Log integrity verification (Req 10.5)
- Automated security event review (Req 10.6)
- 12-month retention accessibility (Req 10.7)
ISO 27001/SOC 2:
- A.12.4 Logging and Monitoring controls
- CC7.x System Monitoring requirements
- Timestamped incident response evidence trails
We include forever-free compliance kits with our MDR service through cybersecurity compliance services. Security monitoring generates compliance documentation automatically, including pre-built dashboards and audit-ready reporting.
7. Why should organizations choose vendor-agnostic managed SIEM over single-vendor solutions like Arctic Wolf?
The architectural difference has lasting consequences for flexibility, cost, and institutional knowledge retention.
Single-Vendor Approach (Arctic Wolf model):
- Requires adopting a proprietary SIEM platform
- Existing Splunk/Elastic investments (often $100K+ annually) become sunk costs
- Detection rules and correlation logic don’t transfer
- A 3-6 month migration timeline is typical
- Switching providers later means repeating the entire process
Vendor-Agnostic Approach (UnderDefense model):
- Operates within your existing SIEM environment
- Protects your tool investments
- All detection rules remain yours in portable formats
- 30-day integration is typical (no migration required)
- Switch managed providers without rebuilding detection capabilities
The choice is clear if you have established Splunk, Elastic, or Sentinel deployments. You’ve invested years building correlation logic and tuning detection rules. A vendor-agnostic provider like us preserves that institutional knowledge.
We publish
($11-15/endpoint/month) versus the “contact sales” opacity common with single-vendor providers. Our approach means your business logic stays with you regardless of your managed provider relationship.
8. What questions should we ask when evaluating managed SIEM providers?
We recommend validating answers across ten specific questions before signing any contract:
Integration & Detection:
- What percentage of our current stack do you support with native connectors?
- How long does custom log source onboarding take? (Benchmark: 2-4 weeks)
- Do you operate within our SIEM or require data forwarding?
- What’s your documented MITRE ATT&CK technique coverage percentage?
Response & Operations:
5. What is your documented MTTR for critical incidents with case study evidence?
6. Do you contain threats or only escalate?
7. How do you verify suspicious activity with affected users?
Pricing & Contract:
8. Is pricing published or “contact sales”? What’s included vs. add-on?
9. What are exit terms and data portability provisions?
10. Are there hidden costs for log volume, alert counts, or compliance reporting?
Use our SOC Provider Evaluation Checklist as a scoring template. We answer all ten questions with documented evidence, published pricing, and a 30-day trial period so you can validate claims rather than trust sales promises.
The post Managed SIEM Integration: Splunk, Elastic, Sentinel Compatibility Without Lock-In appeared first on UnderDefense.