Q1: What Is Managed SIEM for Hybrid and On-Premise Environments, and Why Does It Matter Now?
The Hybrid Reality No One Can Ignore
Let me cut straight to what most vendor pitches skip: managed SIEM for hybrid infrastructure is not a “deployment option.” It is a vendor-operated service that collects, normalizes, correlates, and responds to security events across both cloud and on-premise environments from a single, unified platform. And this is not some niche edge case. Healthcare systems still run on-prem EHR platforms. Manufacturers depend on OT/SCADA networks. Financial services maintain data-residency-bound infrastructure. Scaling tech companies straddle AWS alongside legacy data centers. Five reasons hybrid persists and will keep persisting:
- Regulatory mandates (HIPAA, PCI DSS, GDPR) requiring on-prem data controls
- Legacy systems and proprietary applications that cannot be cloud-migrated
- OT/SCADA and manufacturing environments with air-gapped or protocol-specific requirements
- Data sovereignty and jurisdiction-specific storage mandates
- Sunk infrastructure investments not yet at end-of-life
The result is a “hybrid by default” reality, with organizations straddling 2–4 environments simultaneously. Pretending otherwise is the first mistake most security vendors make.
The “Cloud-First Assumption” Trap
Here’s the operational problem: most managed SIEM and MDR providers architect primarily for cloud-native environments and treat on-prem as an afterthought. Arctic Wolf, for instance, is “cloud-native and monitors cloud applications in addition to networks, endpoints, and identities,” but their own documentation reveals a design philosophy that starts in the cloud and bolts on-prem later. Users validate this gap:
“Log collectors show working, however when asked to provide logs for an investigation no logs could be provided. Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing [$3B–$10B] Arctic Wolf – Gartner Verified Review
Expel takes a different approach, as their MDR augments customer SIEM investments, but their integration scope has documented limits around firewalls, WAFs, and certain cloud platforms like GCP. Traditional MSSPs? They provide checkbox monitoring with rigid playbooks, offering no intelligence, no cross-environment correlation, and no organizational context. The result: blind spots where on-prem logs are either uncollected, delayed, or stripped of context.
✅ Unified Visibility as the New Standard
Detection across half your infrastructure is not detection. It is a false sense of security. In hybrid environments, the competitive advantage is a managed SIEM that reasons across cloud identity events, on-prem network logs, endpoint telemetry, and SaaS activity simultaneously. The “AI SOC + Human Ally” model represents the architectural shift the industry needs, a system that does not just ingest logs but understands the causal chain across environments and responds with organizational context.
How We Built MAXI for Hybrid From Day One
We built the UnderDefense MAXI platform for cloud, hybrid, and on-premise environments from the ground up, not as an add-on. It works on-prem, in customer-specific cloud environments (Azure, GCP, AWS, Oracle), and keeps logs and AI data in the customer’s data lake. We integrate with customer-owned SIEM (Elastic, Splunk, others) without forcing vendor lock, with 250+ integrations across endpoints, cloud, identity, network, and SaaS. Our analysts provide 24/7 concierge response with organizational context, and our detection logic is code, versioned, unit-tested, and CI/CD deployed.
“Their team cleaned up our configurations and got the noise under control within the first week. The platform itself is straightforward, it pulls in data from all our existing security tools, so we didn’t have to rip and replace anything.”
— Verified User, Marketing & Advertising UnderDefense – G2 Verified Review
“UnderDefense integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
⭐ UnderDefense maintains zero ransomware cases across all MDR clients in 6 years, including organizations running complex hybrid environments with both cloud and on-prem infrastructure, because unified visibility without response is just expensive logging.
Q2: How Does Managed SIEM Log Collection Work Across Cloud and On-Premise Environments?
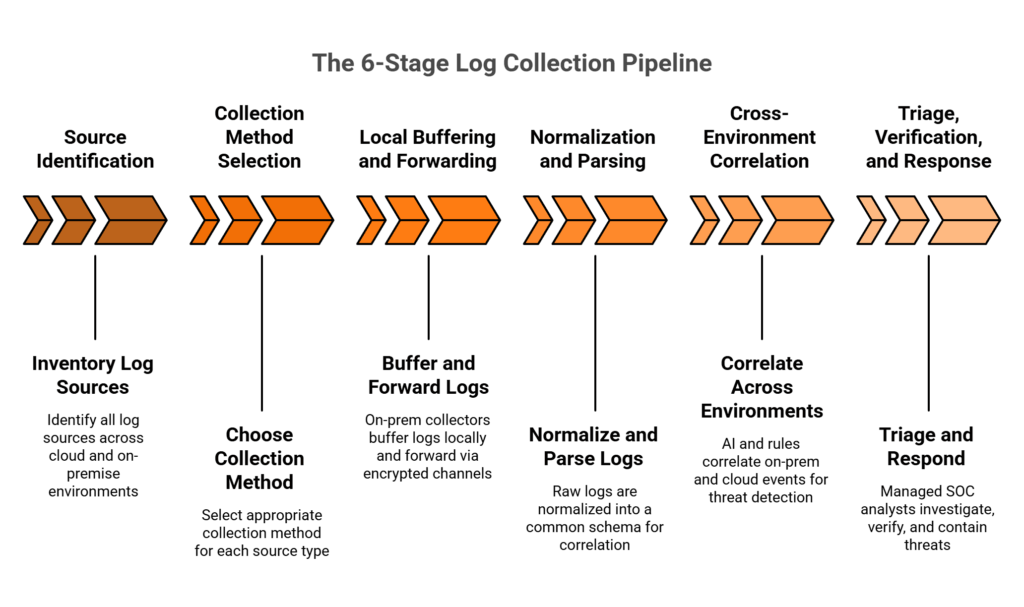
Managed SIEM log collection in hybrid environments works through a six-stage pipeline that bridges on-premise and cloud telemetry into a unified detection layer. Here’s the end-to-end process:
The 6-Stage Log Collection Pipeline
- Source Identification — Inventory all log sources: firewalls, servers, endpoints, cloud services, SaaS applications, OT/SCADA systems, and identity providers
- Collection Method Selection — Agent-based for servers/endpoints; agentless via Syslog/SNMP for network devices; API-based for cloud/SaaS; local forwarders for on-prem aggregation
- Local Buffering and Forwarding — On-prem collectors store events locally to protect against connectivity loss, then forward via encrypted channels
- Normalization and Parsing — Raw logs from diverse sources normalized into a common schema for cross-platform correlation
- Cross-Environment Correlation — AI-driven and rule-based correlation linking on-prem Active Directory events with cloud IAM anomalies and endpoint behavior
- Triage, Verification, and Response — Managed SOC analysts investigate, verify via ChatOps, and contain threats with organizational context
📊 Log Flow Architecture
The end-to-end pipeline flows as follows:
[On-Prem Sources] (servers, firewalls, OT) → [Local Collector/Forwarder] (with buffer) → [Encrypted Forwarding] → [Cloud Analytics Engine] (normalize, correlate, detect) → [Managed SOC Analysts] → [Response: contain, verify, remediate]
This architecture ensures no logs are lost during internet outages, no proprietary protocols go unmonitored, and no alert lacks cross-environment context.
Log Collection Methods by Source Type
| Source Type | Collection Method | Examples |
|---|---|---|
| On-prem servers | Agent-based | Elastic Agent, Splunk Forwarder |
| Network devices / Firewalls | Agentless Syslog/SNMP | Palo Alto, Fortinet, Cisco ASA |
| Cloud platforms | Native API connectors | AWS CloudTrail, Azure Monitor, GCP Logs |
| SaaS applications | API/webhook ingestion | O365, Okta, Google Workspace |
| OT/SCADA systems | Protocol-specific collectors | Modbus, BACnet gateways |
| Endpoints | EDR telemetry forwarding | CrowdStrike, SentinelOne, Defender |
Integration Requirements That Actually Matter
Beyond raw log collection, the pipeline must support:
- SOAR integration for automated response playbooks
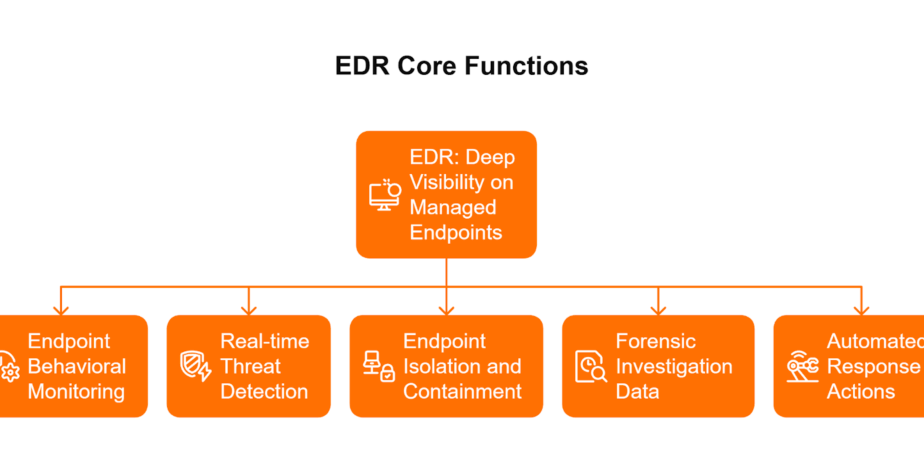
- EDR telemetry correlation to connect endpoint behavior with network and cloud events
- Firewall log ingestion for perimeter visibility
- IAM/identity provider event collection to track privilege escalation and lateral movement
- Legacy system support, including mainframes and proprietary protocols via custom parsers
Each integration point is a potential blind spot if your managed SIEM provider doesn’t support it natively. This is where the “250 integrations” claim on a vendor’s website matters less than which specific 250 integrations they support.
How MAXI Handles This Natively
UnderDefense MAXI handles this entire pipeline natively, deploying on-prem collectors that buffer locally and forward securely, connecting via API to cloud/SaaS sources, and correlating cross-environment events through agentic AI with 96% MITRE ATT&CK coverage. Customers retain full ownership of their SIEM data lake. MAXI supports 250+ integrations including SOAR orchestration, EDR platforms, firewalls, IAM systems, and legacy/proprietary sources.
Q3: How Do On-Premise, Cloud, and Hybrid SIEM Deployments Compare?
The right SIEM deployment model depends on your infrastructure reality, but for organizations running both cloud and on-premise environments, only hybrid managed SIEM provides unified visibility without forcing infrastructure migration.
Side-by-Side Deployment Comparison
| Dimension | On-Premise SIEM | Cloud-Only SIEM | Hybrid Managed SIEM |
|---|---|---|---|
| Deployment Location | Customer data center | Vendor’s multi-tenant cloud | Customer’s environment (on-prem + cloud) |
| Log Collection Scope | On-prem only; limited cloud API support | Cloud-native; limited on-prem agent support | Full coverage: on-prem, cloud, SaaS, OT |
| Scalability Model | Hardware-bound; manual capacity planning | Elastic; pay-per-ingestion | Elastic with local buffering for on-prem |
| Cost Structure | High CapEx; perpetual licensing + hardware | OpEx; ingestion-based (can spike unpredictably) | Predictable per-endpoint pricing |
| Staffing Requirements | 4–8 FTE security engineers minimum | 1–3 FTE for tuning/integration | Fully managed; 0 additional FTE required |
| Compliance / Data Residency | ✅ Full control | ⚠️ Data leaves your environment | ✅ Data stays in your controlled environment |
| Correlation Capability | Single-environment only | Cloud-centric; on-prem gaps | Cross-environment: cloud + on-prem + SaaS |
| Incident Response | Manual; your team investigates | Alert escalation; limited remediation | Concierge response: detect, verify, contain |
| Vendor Lock-In Risk | Moderate (SIEM vendor lock) | ❌ High (proprietary data formats) | ✅ Low (vendor-agnostic, data ownership) |
| Best Suited For | Air-gapped government / classified environments | 100% cloud-native startups | Organizations with mixed infrastructure |
⚠️ When Pure Models Fit
Be fair: if you’re a 100% cloud-native startup with zero on-prem assets, a cloud-only SIEM might work fine. If you’re running a fully air-gapped classified government system, on-prem SIEM is the only option. But the vast majority of mid-market and enterprise organizations fall squarely in the hybrid zone, and they need a managed SIEM that meets them where they are, not where a vendor wishes they were.
How MAXI Operates as Hybrid Managed SIEM
UnderDefense MAXI operates as hybrid managed SIEM, deployed on-prem in your environment, in your chosen cloud (Azure, GCP, AWS, Oracle), or both, with the flexibility to support organizations at every stage of cloud migration. Published pricing at $11–15/endpoint/month vs. opaque “contact sales” quotes from competitors. We onboard hybrid environments in 30 days, compared to 6-month-to-one-year deployment timelines typical of legacy SIEM implementations, because turnkey deployment should not require rearchitecting your infrastructure.
Q4: Where Do Cloud-Only Managed SIEM Providers Fall Short for On-Premise Environments?
⏰ The 3:17 AM Blind Spot
Your cloud SIEM dashboard shows green across the board, with 100% of cloud workloads monitored and all API connectors active. But at 3:17 AM, an attacker moves laterally from a compromised on-prem domain controller to a cloud admin account. Your cloud-only managed SIEM sees the cloud side, an anomalous login, but has zero visibility into the on-prem reconnaissance that preceded it. The alert reads “suspicious cloud login” with no context. Your team starts investigating from the middle of the kill chain.
This scenario is not hypothetical, but an operational reality for organizations running hybrid infrastructure with cloud-only SIEM coverage.
❌ 6 Specific Failure Modes of Cloud-Only SIEM in On-Prem Environments
- Internet-dependent log ingestion — On-prem Syslog forwarding to cloud SIEM fails during connectivity interruptions. Logs are lost, not buffered.
- No local collection infrastructure — Cloud-only providers don’t deploy on-prem collectors/forwarders, leaving legacy servers, network devices, and OT systems unmonitored.
- Proprietary protocol blind spots — Industrial systems (SCADA, Modbus, BACnet) generate logs in formats cloud SIEM parsers don’t support.
- Latency in on-prem event correlation — Forwarding all on-prem logs to cloud introduces delay critical for time-sensitive lateral movement detection.
- Data residency violations — Forwarding regulated on-prem data to a vendor’s multi-tenant cloud may violate HIPAA, PCI DSS, or jurisdiction-specific mandates.
- Loss of forensic context — Without local log retention, post-incident forensics requires manual on-prem evidence collection.
Arctic Wolf’s own architecture starts cloud-native by design, and users report the gap:
“We received little value from ArcticWolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“This is not an extension of our security team as was originally sold. Still not quite there with the remediation side of things. We receive alerts, but not necessarily a clear path to resolution.”
— Sr Cybersecurity Engineer, Manufacturing [$500M–$1B] Arctic Wolf – Gartner Verified Review
💸 The Hidden Costs No One Budgets For
- 10–15 hours/week manually correlating on-prem events the SIEM missed
- Extended dwell time from undetected on-prem-to-cloud lateral movement
- Compliance audit failures from on-prem log gaps
- Average breach cost amplified by incomplete visibility across environments
✅ How It Should Actually Work
The right managed SIEM deploys local collectors on-prem, buffers logs during outages, normalizes proprietary protocols, and correlates across environments in real time, all while keeping data in your controlled environment. We built UnderDefense MAXI to do exactly this: deploying on-prem where data lives, operating in customer-specific environments, and keeping SIEM data in your data lake. Our analysts correlate the full kill chain with 2-minute alert-to-triage and concierge response that verifies directly with affected users.
“At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it. Now, with their security monitoring and incident response we know our endpoints are well-protected.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
UnderDefense detected threats 2 days faster than CrowdStrike OverWatch in documented case studies, because AI-driven cloud-only detection without on-prem context still leaves the first half of the kill chain invisible.
Q5: How Does Managed SIEM for Hybrid Infrastructure Work in Healthcare, Manufacturing, and Financial Services?
Most managed SIEM marketing stays abstract: “we cover all industries.” That tells a CISO in healthcare, a plant security manager in manufacturing, or a compliance officer at a regional bank exactly nothing useful. Here’s how hybrid managed SIEM actually maps to three industries where the rubber meets the road.
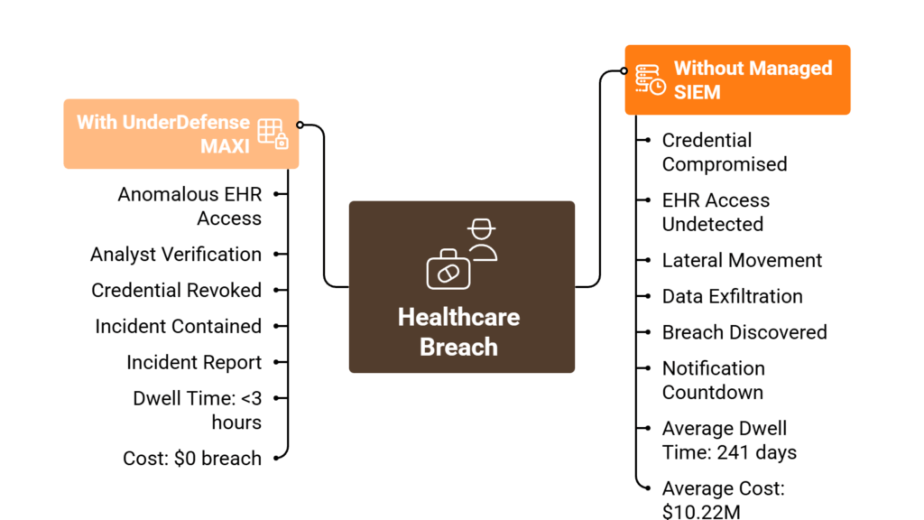
🏥 Healthcare: On-Prem EHR Systems and HIPAA Log Residency
Healthcare organizations run on-prem EHR platforms, such as Epic, Cerner, and MEDITECH, that generate authentication and access logs containing ePHI (electronic Protected Health Information). These logs must remain within controlled environments per HIPAA’s Security Rule. Cloud-only SIEM either can’t collect these logs or creates compliance exposure by forwarding ePHI to a multi-tenant cloud environment outside the organization’s control.
The operational reality: hybrid managed SIEM deploys local collectors that monitor EHR access events on-prem, correlate them with cloud identity events (Okta, Azure AD), and alert on anomalous patient record access, all while keeping ePHI logs in the hospital’s own data lake. Without this, you’re blind to the most common healthcare attack vector: insiders accessing records they shouldn’t.
🏭 Manufacturing / OT: Bridging Air-Gapped Networks
Industrial control systems, including SCADA, PLCs, and HMIs, live on air-gapped or semi-isolated OT networks and generate logs via proprietary protocols (Modbus, BACnet, OPC UA) that cloud-only SIEM simply cannot ingest. The convergence of IT and OT networks is where attackers move laterally, and it’s exactly the blind spot cloud-only providers leave open.
Hybrid managed SIEM deploys protocol-specific collectors in the OT environment, monitors for lateral movement between IT and OT networks, and correlates industrial anomalies with IT security events. The managed SOC provides 24/7 coverage that manufacturing security teams, often 1–2 people, cannot staff alone.
💰 Financial Services: Data Residency Meets PCI DSS
Banking and fintech organizations face data-residency mandates requiring transaction logs, authentication events, and audit trails to remain within specific jurisdictions. Cloud-only SIEM with multi-tenant architecture creates scope expansion for PCI DSS 4.0 compliance: if cardholder-environment logs leave your controlled data lake, your compliance surface grows significantly.
Hybrid managed SIEM keeps financial logs in the organization’s controlled data lake within the required jurisdiction, correlates across on-prem core banking systems and cloud payment platforms, and generates automated compliance evidence for PCI DSS, SOC 2, and regulatory audits.
How We Approach Vertical-Specific Hybrid SIEM
We serve healthcare, manufacturing, and financial services organizations with hybrid managed SIEM tailored to each vertical’s regulatory and infrastructure reality. From monitoring on-prem EHR systems to securing OT/IT convergence zones to maintaining data-residency compliance for financial regulators, UnderDefense MAXI deploys where your industry demands, not where the vendor prefers.
“UnderDefense impressed us with their ability to tailor their services to our unique needs and challenges. They didn’t simply provide a one-size-fits-all solution, but instead took the time to understand our specific environment and requirements.”
— Serhii Bozhok, CIO of Security, ARX Insurance Company UnderDefense – Clutch Verified Review
Q6: What Compliance and Integration Risks Does a Cloud-Only SIEM Create for Regulated Hybrid Environments?
Forwarding on-premise security logs to a cloud-only managed SIEM creates regulatory exposure across multiple frameworks while simultaneously breaking integration chains with on-prem security tools. When log data containing PHI, cardholder data, or PII traverses to a multi-tenant cloud environment outside your control, you inherit the provider’s compliance posture, and their integration limitations.
⚠️ Compliance Risks by Framework
HIPAA: ePHI in security logs forwarded to cloud SIEM requires BAA coverage, encryption controls, and data-residency guarantees many cloud-only providers don’t offer.
PCI DSS 4.0 (Req 10): Forwarding cardholder-environment logs to third-party cloud introduces scope expansion and shared-responsibility complexity. Your QSA will have questions.
GDPR / Data Sovereignty: EU organizations forwarding on-prem logs containing personal data to non-EU cloud SIEM regions risk adequacy violations.
ISO 27001 / SOC 2: Auditors require evidence of log data custody and retention controls. “Logs in our multi-tenant cloud” is harder to audit than “logs in your controlled data lake.”
❌ Integration Risks That Break Response Workflows
SOAR/playbook breaks when on-prem firewall and IAM logs aren’t ingested, because automated response workflows can’t trigger across the full environment.
EDR correlation gaps when on-prem endpoint telemetry doesn’t reach the cloud SIEM, meaning you see endpoints but miss network context.
Legacy system blind spots when proprietary protocols (mainframe, custom apps) have no cloud-SIEM parser support.
Expel users report exactly this gap in practice:
“Despite the capabilities of the technical platform, there is still a limit to the environmental/organizational knowledge inherent in the service. This leads to a fairly frequent need for engagement with our internal team to get clarification and verification.”
— Verified User, Computer Software Expel – G2 Verified Review
✅ How UnderDefense Solves Both
We keep logs and AI data in the customer’s own data lake, whether on-prem, private cloud, or chosen region. UnderDefense MAXI’s 250+ integrations include SOAR orchestration, EDR platforms (CrowdStrike, SentinelOne, Defender), firewalls, IAM systems, and legacy/proprietary sources. Compliance automation generates audit-ready evidence mapped to SOC 2, ISO 27001, HIPAA, PCI DSS, and GDPR, with forever-free compliance kits included.
UnderDefense has achieved full regulatory compliance across ISO 27001, SOC 2 Type 1 & 2 for its own operations, because compliance built on actual security operations beats compliance built on checkbox tools.
Q7: What Should You Look for in a Managed SIEM Vendor That Truly Supports Hybrid Infrastructure?
The Decision Most Security Leaders Get Wrong
Choosing a managed SIEM vendor for hybrid infrastructure means committing to a security architecture that must see everything, including on-prem servers, cloud workloads, OT systems, and SaaS applications, through a single detection-and-response layer. Pick a vendor that only covers half your environment, and you’re paying for a false sense of security.
Most security leaders choose managed SIEM based on brand recognition or total integration count. This ignores the critical question: Can they collect, correlate, and respond across your on-prem AND cloud infrastructure, or do they only cover the cloud side and escalate “please investigate” tickets for everything else?
✅ 7 Evaluation Criteria for Hybrid Managed SIEM
- On-Prem Collection Infrastructure — Does the vendor deploy local collectors/forwarders with local buffering for connectivity resilience?
- Cross-Environment Correlation — Can the SIEM correlate events across on-prem, cloud, and SaaS in real time, not just ingest cloud APIs?
- Data Residency and Log Ownership — Do logs stay in your data lake, or get forwarded to the vendor’s multi-tenant environment?
- Legacy/OT Protocol Support — Can they parse from SCADA, mainframes, custom applications, and non-standard sources?
- Vendor-Agnostic Integration — Works with your existing SIEM (Elastic, Splunk, Sentinel) or forces proprietary replacement?
- Response Capability Beyond Detection — Can the managed team contain threats (isolate endpoints, revoke credentials) or just escalate?
- Compliance Evidence Generation — Does the platform map security telemetry to regulatory controls automatically?
Score each vendor 0–2 on all 7 criteria. Providers scoring 11+ represent genuine hybrid partners. Below 8 means you’re buying cloud monitoring repackaged as hybrid coverage.
⭐ UnderDefense Scorecard
| Criterion | Score | Evidence |
|---|---|---|
| On-Prem Collection | ✅ 2 | Deploys on-prem collectors with local buffering |
| Cross-Environment Correlation | ✅ 2 | Agentic AI with 96% MITRE ATT&CK coverage |
| Data Residency / Log Ownership | ✅ 2 | Customer-owned data lake (on-prem or chosen cloud) |
| Legacy/OT Protocol Support | ✅ 2 | 250+ integrations including OT/proprietary sources |
| Vendor-Agnostic Integration | ✅ 2 | Works with Elastic, Splunk, Sentinel, with no replacement |
| Response Beyond Detection | ✅ 2 | Full containment, 2-minute alert-to-triage, ChatOps verification |
| Compliance Evidence | ✅ 2 | Forever-free compliance kits (SOC 2, ISO 27001, HIPAA) |
| Total | 14/14 |
UnderDefense MAXI scores 14/14 because it was designed from the ground up for hybrid infrastructure, not retrofitted from a cloud-only platform. 830% ROI over 3 years documented.
“Their expert management of our SIEM has added to the value of our security investments and tools.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
“Arctic Wolf provides solid detection and response capabilities, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology, Services Arctic Wolf – Gartner Verified Review
Q8: How Does Co-Managed SIEM Compare to Fully Managed SIEM for Hybrid Environments?
Why This Choice Matters More in Hybrid
Organizations with hybrid infrastructure face a unique operational-model decision. Some have internal security teams with SIEM expertise who want to retain control of detection rules and on-prem infrastructure but need 24/7 monitoring support. Others want to fully offload SOC operations because they lack resources to manage a hybrid SIEM stack.
A former CISO of Micron put it best during a conversation about this exact tradeoff: separate SIEM ownership from MDR vendor to protect business logic and avoid vendor lock-in when switching providers. When your business logic, correlation rules, and automation stay in the vendor’s system, switching means starting over from scratch.
Co-Managed Model: Retain Control, Add Coverage
The customer retains SIEM platform ownership (Elastic, Splunk), manages detection engineering and tuning, and the managed provider handles 24/7 monitoring, triage, and escalation. This model fits organizations with mature teams (5+ analysts) who want to preserve detection IP and business logic.
⚠️ The critical requirement: the managed provider must log into your SIEM directly, not extract data to their proprietary platform. Many providers refuse this. When business logic, correlation rules, and automation stay in the vendor’s system, switching means starting over.
Fully Managed Model: Turnkey 24/7 SOC
The provider handles the entire pipeline: tool deployment, detection engineering, 24/7 monitoring, and incident response. This suits organizations without dedicated SOC teams, including startups, scaling companies, and PE portfolio companies.
Side-by-Side Comparison
| Dimension | Co-Managed | Fully Managed |
|---|---|---|
| SIEM Ownership | Customer retains platform (Elastic, Splunk) | Provider includes SIEM in managed service |
| Detection Engineering | Customer manages rules and tuning | Provider handles detection-as-code |
| On-Prem Access Model | Provider logs into customer’s SIEM directly | Provider deploys own collectors on-prem |
| Ideal Organization | 5+ security analysts; preserving detection IP | No dedicated SOC; needs turnkey coverage |
| Vendor Lock-In Risk | ✅ Low, business logic stays with customer | ⚠️ Medium, depends on portability of detection logic |
| UnderDefense Support | Analysts log into YOUR SIEM; your rules, your data | UnderDefense MAXI provides turnkey SOC deployed in 30 days |
Choose co-managed if you have 5+ security analysts and want to preserve detection IP. Choose fully managed if you need turnkey 24/7 SOC coverage and your team focuses on strategic security initiatives.
Why We Support Both, and Transitions Between Them
We operate both models: for co-managed, our analysts log into your SIEM; for fully managed, UnderDefense MAXI provides turnkey 24/7 SOC deployed in 30 days with SIEM included. Detection logic as code (written, versioned, unit-tested, CI/CD) means your business logic is portable even in fully managed mode, a critical difference from providers who lock your rules into their proprietary platform.
“UnderDefense has changed our approach to cybersecurity. At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
“UnderDefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO UnderDefense – G2 Verified Review
Q9: How Does UnderDefense Deliver Managed SIEM Across Your Full Hybrid Infrastructure?
UnderDefense MAXI delivers managed SIEM as a unified detection-and-response layer across cloud, hybrid, and on-premise environments, operating where your data lives, integrating with tools you already own, and keeping full log ownership in your hands.
How the Technical Architecture Works
Here’s what happens under the hood. UnderDefense MAXI deploys on-prem in customer-specific environments or in your chosen cloud: Azure, GCP, AWS, or Oracle. It integrates with your existing SIEM (Elastic, Splunk, Microsoft Sentinel), and our analysts log directly into your system. This matters more than most people realize. As I’ve discussed with CISOs who’ve been burned by vendor switches, when business logic, correlation rules, and automation rules live in the vendor’s environment, you lose them the moment you part ways. We keep all of that with you.
Local collectors buffer and forward on-prem logs, so connectivity interruptions don’t create blind spots. API connectors ingest cloud and SaaS telemetry. Agentic AI correlates across all environments with 96% MITRE ATT&CK coverage. Detection logic is written as code, Python-based, versioned, unit-tested, and deployed via CI/CD, giving you governance over every rule the SOC runs.
What It Covers Across Hybrid Environments
- On-prem AD + domain controller monitoring correlated with cloud identity events
- OT/SCADA and industrial network log collection alongside cloud workload security
- Legacy SIEM augmentation, layering on top of existing Elastic/Splunk deployments without rip-and-replace
- Cross-environment kill chain detection: on-prem compromise → cloud lateral movement → SaaS data exfiltration
- ChatOps user verification for both on-prem and cloud incidents via Slack, Teams, email, and SMS
⏰ Why This Matters for Business Outcomes
The difference between a cloud-only vendor and UnderDefense is monitoring half your attack surface vs. defending all of it. We deliver 2-minute alert-to-triage, 15-minute escalation for critical incidents, 99% alert noise reduction through custom detection tuning, and 100% ransomware prevention across 500+ clients. At $11–15/endpoint/month vs. $500K+ annual cost of building this in-house, the math is straightforward.
Think of it as a dedicated SOC that knows your hybrid architecture as intimately as your own team, at a fraction of the cost.
What Security Leaders Are Saying
“Their team provided us with clear and detailed insights into security vulnerabilities, along with practical recommendations on how to fix them. This level of transparency made it easy for our team to take action.”
— Arman N., CTO UnderDefense – G2 Verified Review
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
“Log collectors show working, however when asked to provide logs for an investigation no logs could be provided. Analysts provide little context.”
— CISO, Manufacturing ($3B–$10B) Arctic Wolf – Gartner Verified Review
Q10: Which Managed Security Resources Help You Evaluate Hybrid SIEM Providers?
Evaluating managed SIEM providers for hybrid infrastructure requires comparing real operational outcomes, including response times, integration breadth, on-prem deployment capabilities, and compliance support, not just feature checklists. The most valuable resources are provider-neutral comparisons, documented case studies, and hands-on SOC cost calculators.
What to Look for in Evaluation Resources
- Documented response time comparisons across providers, not marketing claims, but published SLAs with case study evidence
- Published pricing vs. “contact sales” opacity, because transparent per-endpoint rates tell you a provider has nothing to hide
- Integration compatibility with your specific hybrid stack (SIEM platform, EDR vendor, cloud providers), verifying the vendor works with your tools, not instead of them
- Real case studies showing hybrid environment outcomes, not just cloud-only deployments, but on-prem + cloud + SaaS across the kill chain
- SOC cost analysis comparing build vs. buy for your organization size, because the math changes dramatically between 100 and 5,000 endpoints
💰 The Most Efficient Next Step
For organizations evaluating managed SOC providers that support hybrid infrastructure, a comprehensive provider comparison, with pricing, response times, integration capabilities, and deployment models for each, is the most efficient path forward. Rather than spending weeks assembling vendor data sheets, start with resources that have already done the analysis.
This analysis is based on documented response times, G2 reviews, published pricing, and operational outcomes across 500+ MDR deployments protecting hybrid cloud and on-premise environments.
Q11: Hybrid Managed SIEM Readiness: Is Your Organization Fully Covered?
Score your current managed SIEM coverage against these 8 criteria to identify critical hybrid infrastructure gaps:
Self-Assessment Checklist
☐ Does your managed SIEM collect logs from ALL on-premise infrastructure (servers, network devices, OT systems, and legacy applications), not just cloud workloads?
☐ Are on-prem logs buffered locally before forwarding, so connectivity interruptions don’t create log gaps?
☐ Can your SIEM correlate events across on-prem, cloud, and SaaS environments in a single detection layer?
☐ Do your security logs remain in your controlled data lake (not the vendor’s multi-tenant cloud)?
☐ Does your managed provider have direct visibility into your on-prem SIEM, or do they only see cloud-forwarded data?
☐ Can your provider contain threats across both on-prem and cloud (isolate endpoints, revoke credentials, and block lateral movement)?
☐ Does your monitoring generate compliance evidence covering BOTH on-prem and cloud controls (SOC 2, HIPAA, PCI DSS, and ISO 27001)?
☐ Can your provider verify suspicious user activity directly via ChatOps for both on-prem and cloud incidents?
⭐ Score Interpretation
| Score | Assessment | Recommendation |
|---|---|---|
| 7–8 ✅ | Hybrid SIEM coverage is mature | Focus on optimization and proactive threat hunting |
| 4–6 ⚠️ | Critical gaps exist | Your on-prem environment likely has blind spots increasing dwell time and compliance risk |
| 0–3 ❌ | Effectively cloud-only | On-prem infrastructure is exposed. Most of your attack surface is unmonitored |
How UnderDefense Closes Every Gap
UnderDefense is designed to turn every unchecked box into ✅ across your full hybrid infrastructure. On-prem collection with local buffering, cross-environment AI correlation, customer-owned data residency, concierge analyst response, and automated compliance evidence, deployed in 30 days. Most organizations go from 2–3 checks to 8/8 within the first month.
Scored below 5? Book a 15-minute hybrid SIEM gap assessment to see exactly where your on-prem blind spots are.
Proven Outcomes Across Hybrid Environments
UnderDefense clients achieve 99% alert noise reduction and 96% MITRE ATT&CK coverage within the first month across hybrid environments, because comprehensive protection shouldn’t require your team to stitch together cloud and on-prem visibility manually.
“At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it. Now, with their security monitoring and incident response we know our endpoints are well-protected.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
1. What is managed SIEM for hybrid infrastructure, and how does it differ from cloud-only SIEM?
Managed SIEM for hybrid infrastructure is a vendor-operated service that collects, normalizes, correlates, and responds to security events across both cloud and on-premise environments from a single, unified detection layer. Unlike cloud-only SIEM, which architects primarily for cloud-native workloads and treats on-prem as an afterthought, hybrid managed SIEM deploys local collectors on-prem, buffers logs during connectivity interruptions, and correlates events across on-prem Active Directory, cloud IAM, endpoint telemetry, and SaaS activity simultaneously.
The distinction matters operationally. Cloud-only providers lack local collection infrastructure, cannot parse proprietary OT/SCADA protocols, and introduce latency when forwarding on-prem logs to cloud analytics engines. Hybrid managed SIEM addresses all three gaps by operating where data lives rather than requiring all telemetry to traverse to the vendor’s multi-tenant cloud.
For organizations straddling 2–4 environments, including healthcare systems running on-prem EHR platforms, manufacturers with OT networks, and financial services with data-residency mandates, hybrid managed SIEM is not a deployment preference but an operational requirement.
2. How does managed SIEM log collection work across cloud and on-premise environments?
Managed SIEM log collection in hybrid environments works through a six-stage pipeline that bridges on-premise and cloud telemetry into a unified detection layer:
-
Source identification inventories all log sources: firewalls, servers, endpoints, cloud services, SaaS applications, OT/SCADA systems, and identity providers.
-
Collection method selection deploys agent-based collection for servers/endpoints, agentless Syslog/SNMP for network devices, API connectors for cloud/SaaS, and local forwarders for on-prem aggregation.
-
Local buffering and forwarding ensures on-prem collectors store events locally to protect against connectivity loss, then forward via encrypted channels.
-
Normalization and parsing converts raw logs from diverse sources into a common schema for cross-platform correlation.
-
Cross-environment correlation links on-prem Active Directory events with cloud IAM anomalies and endpoint behavior using AI-driven and rule-based logic.
-
Triage, verification, and response means managed SOC analysts investigate, verify via ChatOps, and contain threats with organizational context.
This architecture ensures no logs are lost during internet outages, no proprietary protocols go unmonitored, and no alert lacks cross-environment context.
3. Where do cloud-only managed SIEM providers fall short for on-premise environments?
Cloud-only managed SIEM providers fail across six specific operational areas when applied to on-premise environments:
-
Internet-dependent log ingestion means on-prem Syslog forwarding fails during connectivity interruptions, and logs are lost rather than buffered.
-
No local collection infrastructure leaves legacy servers, network devices, and OT systems unmonitored because cloud-only providers don’t deploy on-prem collectors.
-
Proprietary protocol blind spots affect industrial systems like SCADA and Modbus that generate logs in formats cloud SIEM parsers don’t support.
-
Latency in on-prem event correlation introduces delay when forwarding all on-prem logs to cloud, which is critical for time-sensitive lateral movement detection.
-
Data residency violations occur when forwarding regulated on-prem data to a vendor’s multi-tenant cloud, potentially violating HIPAA, PCI DSS, or jurisdiction-specific mandates.
-
Loss of forensic context means post-incident forensics requires manual on-prem evidence collection without local log retention.
The right managed SIEM provider deploys local collectors on-prem, buffers logs during outages, normalizes proprietary protocols, and correlates across environments in real time while keeping data in your controlled environment.
4. What compliance risks does a cloud-only SIEM create for regulated hybrid environments?
Forwarding on-premise security logs to a cloud-only managed SIEM creates regulatory exposure across multiple compliance frameworks:
-
HIPAA: ePHI in security logs forwarded to cloud SIEM requires BAA coverage, encryption controls, and data-residency guarantees that many cloud-only providers don’t offer.
-
PCI DSS 4.0 (Req 10): Forwarding cardholder-environment logs to a third-party cloud introduces scope expansion and shared-responsibility complexity.
-
GDPR / Data Sovereignty: EU organizations forwarding on-prem logs containing personal data to non-EU cloud SIEM regions risk adequacy violations.
-
ISO 27001 / SOC 2: Auditors require evidence of log data custody and retention controls, and “logs in our multi-tenant cloud” is harder to audit than “logs in your controlled data lake.”
Beyond compliance, integration risks compound the problem. SOAR playbooks break when on-prem firewall and IAM logs aren’t ingested. EDR correlation gaps emerge when on-prem endpoint telemetry doesn’t reach the cloud SIEM. The solution is keeping logs in the customer’s own data lake and using compliance automation to generate audit-ready evidence mapped to each framework.
5. How does managed SIEM for hybrid infrastructure work in healthcare, manufacturing, and financial services?
Each industry faces unique hybrid SIEM requirements based on regulatory mandates and infrastructure realities:
Healthcare organizations run on-prem EHR platforms (Epic, Cerner, MEDITECH) generating ePHI logs that must remain in controlled environments per HIPAA. Hybrid managed SIEM deploys local collectors to monitor EHR access events on-prem, correlates them with cloud identity events, and alerts on anomalous patient record access while keeping ePHI in the hospital’s own data lake.
Manufacturing environments run SCADA, PLCs, and HMIs on air-gapped or semi-isolated OT networks generating logs via proprietary protocols that cloud-only SIEM cannot ingest. Hybrid managed SIEM deploys protocol-specific collectors in the OT environment, monitors for lateral movement between IT and OT networks, and provides 24/7 managed SOC coverage that manufacturing security teams of 1–2 people cannot staff alone.
Financial services face data-residency mandates requiring transaction logs and authentication events to remain within specific jurisdictions. Hybrid managed SIEM keeps financial logs in the organization’s controlled data lake, correlates across on-prem core banking systems and cloud payment platforms, and generates automated compliance evidence for PCI DSS, SOC 2, and regulatory audits.
6. What should you look for in a managed SIEM vendor that truly supports hybrid infrastructure?
We recommend evaluating managed SIEM vendors for hybrid infrastructure across seven criteria:
-
On-prem collection infrastructure: Does the vendor deploy local collectors/forwarders with local buffering for connectivity resilience?
-
Cross-environment correlation: Can the SIEM correlate events across on-prem, cloud, and SaaS in real time, not just ingest cloud APIs?
-
Data residency and log ownership: Do logs stay in your data lake, or get forwarded to the vendor’s multi-tenant environment?
-
Legacy/OT protocol support: Can they parse from SCADA, mainframes, custom applications, and non-standard sources?
-
Vendor-agnostic integration: Works with your existing SIEM (Elastic, Splunk, Sentinel) or forces proprietary replacement?
-
Response capability beyond detection: Can the managed team contain threats or just escalate?
-
Compliance evidence generation: Does the platform map security telemetry to regulatory controls automatically?
Score each vendor 0–2 on all seven criteria. Providers scoring 11+ represent genuine hybrid partners. Below 8 means you’re buying cloud monitoring repackaged as hybrid coverage. We built UnderDefense MAXI to score 14/14 because it was designed from the ground up for hybrid environments.
7. How does co-managed SIEM compare to fully managed SIEM for hybrid environments?
The choice depends on your internal team’s maturity and desire for control:
Co-managed SIEM means the customer retains SIEM platform ownership (Elastic, Splunk), manages detection engineering and tuning, and the managed provider handles 24/7 monitoring, triage, and escalation. This model fits organizations with mature teams (5+ analysts) who want to preserve detection IP and business logic. The critical requirement is that the managed provider logs into your SIEM directly, not extracts data to their proprietary platform.
Fully managed SIEM means the provider handles the entire pipeline: tool deployment, detection engineering, 24/7 monitoring, and incident response. This suits organizations without dedicated SOC teams, including startups, scaling companies, and PE portfolio companies.
We support both models and transitions between them. For co-managed, our analysts log into your SIEM. For fully managed, UnderDefense MAXI provides turnkey 24/7 SOC deployed in 30 days. Detection logic as code (written, versioned, unit-tested, CI/CD) means your business logic is portable even in fully managed mode, a critical difference from providers who lock your rules into their proprietary platform.
8. How much does managed SIEM for hybrid environments cost, and what pricing model should you expect?
Managed SIEM pricing for hybrid environments varies significantly by provider model. The three primary structures are:
-
On-premise SIEM: High CapEx with perpetual licensing + hardware costs. Requires 4–8 FTE security engineers minimum, making total cost of ownership $500K+ annually for mid-market organizations.
-
Cloud-only SIEM: OpEx with ingestion-based pricing that can spike unpredictably as on-prem log volumes increase. Many providers use opaque “contact sales” quotes.
-
Hybrid managed SIEM: Predictable per-endpoint pricing with fully managed operations, requiring 0 additional FTE.
We publish our managed SIEM pricing transparently at $11–15/endpoint/month. This includes on-prem collector deployment, cross-environment correlation, 24/7 analyst coverage, and compliance automation. Compare this to building equivalent capability in-house, which requires a minimum 4-person SOC team ($400K–$600K in salaries alone), plus SIEM licensing, infrastructure, and ongoing tuning.
We onboard hybrid environments in 30 days compared to 6-month-to-one-year deployment timelines typical of legacy SIEM implementations, with documented 830% ROI over 3 years across our client base.
The post Managed SIEM for Hybrid and On-Premise Environments Explained appeared first on UnderDefense.