Q1. What Is Managed SIEM for Healthcare and Why Does HIPAA Require It?
The Compliance-Security Gap Nobody Talks About
Healthcare organizations face a reality I see constantly: there’s a massive gap between “HIPAA compliant on paper” and “actually protected against breaches.” The HIPAA Security Rule (45 CFR §164.312) explicitly mandates audit controls and activity monitoring for any system containing electronic Protected Health Information (ePHI). Yet most healthcare IT teams are drowning, managing disconnected EHR systems, legacy infrastructure, cloud workloads, and medical devices without unified visibility into any of them.
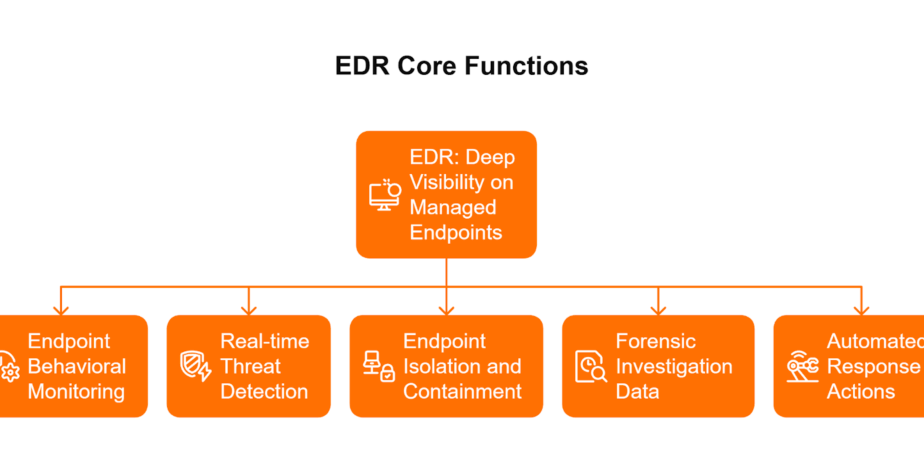
The typical healthcare security stack looks like this: Epic or Cerner for clinical records, Microsoft 365 for communication, a mix of on-premises and cloud infrastructure, and an EDR tool that nobody has time to tune properly. Alerts are everywhere. Understanding is nowhere.
Why Traditional Approaches Fail in Healthcare
Traditional MSSPs treat healthcare like any other industry, providing generic alerting without understanding EHR workflows, clinical access patterns, or what “normal” looks like when a physician accesses 200 patient records during morning rounds. Legacy SIEM deployments require 6 to 12-month implementations, dedicated analysts your team doesn’t have, and constant tuning that burns out whoever gets assigned to it.
⚠️ The result? Checkbox compliance that satisfies auditors but doesn’t stop ransomware at 2 AM.
The Shift from Alert Forwarding to Contextual Response
Managed SIEM for healthcare combines continuous security monitoring with compliance automation, correlating access logs across Epic, Cerner, cloud infrastructure, and endpoints into a single context-aware layer. The critical shift isn’t just collecting logs. It’s having a system that can reason across them and take action.
Detection without response is noise. Response without organizational context is risky. The question isn’t “did something suspicious happen?” but “is this Dr. Smith accessing patient records legitimately, or a compromised credential exfiltrating data?”
How UnderDefense Approaches Healthcare SIEM
We built UnderDefence MAXI specifically for this reality. Our platform delivers HIPAA-compliant managed SIEM with 24/7 monitoring, automated collection of audit evidence, and direct analyst response to PHI access anomalies. Here’s what matters:
- Vendor-agnostic integration: We work with your existing EHR investments, Epic, Cerner, and Meditech, without forcing replacement
- 96% MITRE ATT&CK coverage across healthcare-specific attack vectors
- Context-aware detection: Our analysts learn your clinical workflows, VIPs, and care team structures
- Compliance automation: Forever-free HIPAA compliance kits included, not a separate upsell
The 2025 IBM Cost of a Data Breach Report shows healthcare breaches average $7.42 million, still the highest of any industry for 15 consecutive years. U.S. healthcare organizations specifically face even higher costs at $10.22 million due to regulatory fines and OCR investigations.
We maintain a 100% ransomware prevention record across 500+ MDR clients over 6 years, including healthcare organizations where a single breach can trigger OCR audits lasting 18 to 24 months.
UnderDefense acts as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO, Mid-Market G2 Verified Review
Q2. What Are the Specific HIPAA Security Monitoring Requirements That SIEM Must Address?
The HIPAA Security Rule isn’t vague about what’s required. It’s specific, and auditors expect evidence, not promises. Understanding the exact requirements helps you evaluate whether your current monitoring actually satisfies compliance or just creates the appearance of it.
The Three Safeguard Categories
The HIPAA Security Rule (45 CFR Part 164) establishes three safeguard categories: Administrative, Physical, and Technical. For SIEM and security monitoring, Technical Safeguards under §164.312 are most relevant, but Administrative Safeguards around risk analysis and incident response also require documented monitoring evidence.
Implementation specifications fall into two categories:
45 CFR §164.312(b): Audit Controls Requirements
This is the core mandate for SIEM. The regulation requires covered entities to “implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI”.
What SIEM must capture and monitor:
- User identification: Who accessed the system (unique user IDs required)
- Event timestamp: Date, time, and timezone of activity
- Event type: Logon, logoff, record access, modification, deletion
- Patient/record identifiers: Which ePHI was accessed
- Source information: IP address, device, location
- Outcome: Success or failure of access attempt
HHS commentary explicitly supports risk-based audit intensity, but audit controls remain mandatory, not addressable.
⏰ The 6-Year Log Retention Mandate
Under 45 CFR §164.530(j), covered entities must retain documentation for six years from the date of creation or the date when it was last in effect, whichever is later. For audit logs, this means:
- Tamper-proof storage preventing unauthorized modification
- Integrity verification mechanisms
- Backup and disaster recovery procedures
- Chain of custody documentation for forensic validity
Most organizations underestimate storage and retrieval requirements until an OCR investigation requests three years of access logs, with 30 days to produce them.
HITECH Act: Automated Reporting Requirements
The HITECH Act extended HIPAA requirements to include:
- Accounting of disclosures: Patients can request records of who accessed their PHI
- Breach notification automation: Systems must support rapid identification of affected individuals
- Meaningful Use security measures: Attestation requires documented security monitoring evidence
Manual evidence gathering doesn’t scale. When auditors request “all access events for Patient X across all systems for the past 24 months,” you need automated retrieval, not a team manually pulling logs from six different platforms.
How UnderDefense Simplifies Compliance Evidence
Our UnderDefence MAXI Compliance module auto-maps security telemetry directly to HIPAA controls, providing auditors with verifiable evidence rather than theoretical policies. Every investigative step is observable and auditable; we show what we detected, why it mattered, and what action was taken.
Forever-free HIPAA compliance kits are included with MDR, eliminating the hidden costs of separate GRC tools that charge $30K+ annually just to organize the evidence your SIEM already generates.
Q3. How Does Managed SIEM Detect Threats to Protected Health Information Before They Become Breaches?
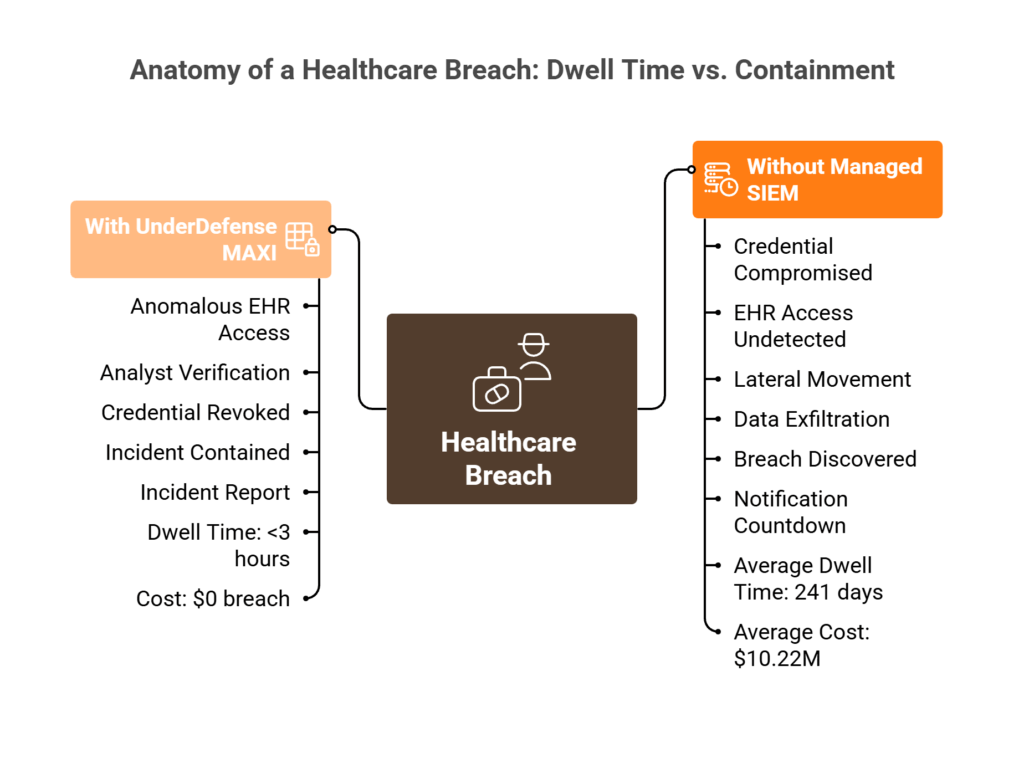
Scenario 1: The Midnight Credential Compromise
It’s 11:47 PM. A nurse’s credentials are compromised via phishing. The attacker begins accessing patient records outside normal clinical hours. Your EHR generates an alert. Your cloud SIEM flags unusual activity. But neither system knows if this is the actual nurse working late, or an attacker beginning data exfiltration.
Your security team is asleep. The attacker has hours to operate.
Scenario 2: Ransomware Through the Supply Chain
Ransomware enters through a compromised medical device vendor’s remote access portal. File encryption begins in the radiology department at 2:14 AM. Without IoMT monitoring correlated with network traffic analysis, the attack spreads to EHR backup systems before anyone notices. By morning, patient care is disrupted, and ransom demands arrive.
Scenario 3: The Insider Threat Nobody Sees
A billing specialist with legitimate PHI access begins exporting records of high-profile patients. Access is authorized. Intent is not. Without behavioral baseline analysis comparing this user’s normal patterns to current activity, the exfiltration appears completely normal in your logs.
Why These Detection Gaps Exist
The problem isn’t a lack of tools, it’s a lack of correlation:
- EHR systems see clinical access but not the authentication context
- Identity tools see login behavior but not patient data sensitivity
- EDR sees endpoint activity but not healthcare workflow legitimacy
- Network monitoring sees traffic but not the clinical context
Without correlation across all four, organizations rely on manual investigation, often discovering breaches 241 days after initial access, according to IBM’s 2025 report. That’s 241 days of attacker dwell time.
💰 The Hidden Costs of Delayed Detection
| Cost Category | Impact |
| Average healthcare breach | $7.42M (2025) |
| U.S. healthcare specifically | $10.22M |
| HIPAA penalty range | $100 to $50,000 per violation, up to $1.5M annually per category |
| OCR investigation duration | 18 to 24 months average |
| Patient trust erosion | Immeasurable but lasting |
How UnderDefence MAXI Correlates Across Your Healthcare Environment
We built a detection that actually understands healthcare workflows. UnderDefence MAXI correlates EHR access logs with identity behavior, endpoint telemetry, IoMT activity, and network patterns in real-time, 24/7.
When anomalies require context, “Did Nurse Jane actually access 47 patient records at midnight?”, our analysts verify directly via Slack or Teams with the affected user before escalating. Confirmed threats trigger immediate credential revocation and endpoint isolation while your team sleeps.
You wake up to: “Incident contained at 2:52 AM, here’s what happened and what we did.” Not 47 unread alerts to triage.
“The biggest win for me was getting actual control over our security alerts. Before the guys from UD stepped in, we were getting bombarded with alerts from all our security tools. Their team cleaned up our configurations and got the noise under control within the first week.”
— Verified User, Marketing and Advertising G2 Verified Review
In documented case studies, UnderDefense detected threats 2 days faster than CrowdStrike OverWatch, because AI-driven detection without human context still leaves gaps that only analysts communicating directly with users can close.
Q4. What Are the HIPAA Breach Notification Requirements and How Does SIEM Support Compliance?
When a breach occurs, the clock starts immediately. Understanding HIPAA’s notification requirements and how SIEM supports rapid compliance can mean the difference between a manageable incident and a regulatory catastrophe.
Defining “Breach” Under HIPAA
The HIPAA Breach Notification Rule (45 CFR §§164.400-414) defines breach as the unauthorized acquisition, access, use, or disclosure of unsecured PHI that compromises the security or privacy of such information. Three exceptions exist: unintentional access by authorized workforce members acting in good faith, inadvertent disclosure between authorized persons, and situations where the recipient couldn’t reasonably retain the information.
If none of these exceptions apply, you must conduct a risk assessment to determine breach probability and document it regardless of the conclusion.
⏰ Federal Notification Timeline Requirements
| Breach Size | Individual Notification | HHS/OCR Notification | Media Notification |
| 500+ individuals | Within 60 days of discovery | Within 60 days of discovery | Within 60 days (if 500+ in a single state) |
| Under 500 individuals | Within 60 days of discovery | Annual report, within 60 days of calendar year end | Not required |
The 60-day deadline runs from the breach discovery date, the first day you know, or by exercising reasonable diligence should know, that a breach occurred. “Unreasonable delay” before that 60-day maximum still triggers enforcement.
State-Specific Laws: The Overlooked Compliance Layer
HIPAA sets the floor, not the ceiling. State laws often impose stricter requirements:
- California (CCPA/CMIA): 15 business days for certain healthcare breaches
- Texas: 60 days, but 250+ threshold triggers AG notification
- New York (SHIELD Act): “Expedient” notification, no specific day count, but regulators interpret strictly
- Massachusetts: Requires certifying compliance to the Attorney General
- Florida: 30-day notification requirement, half the federal timeline
⚠️ A multi-state healthcare organization must track the strictest applicable timeline for each affected individual’s residence.
What SIEM Must Document for OCR Investigations
When OCR investigates, they expect forensic-quality evidence. SIEM must preserve:
- Forensic timeline: Exact sequence of events from initial compromise to detection
- Affected individual identification: Complete list of whose PHI was accessed or exfiltrated
- Attack vector documentation: How the breach occurred and through which systems
- Containment action records: What actions were taken, when, and by whom
- Risk assessment documentation: Analysis supporting breach determination
The difference between “we think 500 records were accessed” and “we have log evidence showing exactly 487 records were accessed by this credential from this IP between these timestamps” determines whether OCR views you as negligent or responsive.
How UnderDefense Supports Post-Breach Compliance
We provide instant forensic documentation with observable, auditable investigation workflows. Every action taken by AI and human analysts is recorded, creating the evidence trail OCR expects.
- Breach scope identification: Automated correlation identifies affected records within hours, not weeks
- Timeline reconstruction: Complete attack chain documentation for regulatory response
- Containment evidence: Documented proof of remediation actions and timing
- Risk assessment support: Evidence-based analysis for breach determination
Our incident response team has supported healthcare organizations through OCR investigations with zero compliance findings attributed to monitoring gaps. When you can show auditors exactly what happened, when you detected it, and how you responded, with timestamps and evidence, enforcement outcomes improve dramatically.
“They’ve also made our audit process much less painful. The reports from their platform give us clear evidence of our security controls and incident response capabilities. When auditors or clients ask questions about our security posture, we can pull up exactly what they need to see.”
— Verified User, Marketing and Advertising G2 Verified Review
Q5. What Business Associate Agreement Requirements Apply to Managed SIEM Vendors?
Any managed SIEM vendor with access to ePHI is a Business Associate under HIPAA. This isn’t optional; 45 CFR §164.502(e) requires written contracts (BAAs) before sharing PHI. Yet many healthcare organizations select SIEM vendors without verifying BAA readiness, exposing them to compliance risk from day one.
Required BAA Provisions Under HIPAA
The regulatory framework is explicit about what your BAA must contain. Under 45 CFR §164.504(e), these seven provisions are non-negotiable:
- Permitted uses and disclosures of PHI: Clearly define how the vendor can use ePHI (security monitoring only, not marketing or resale)
- Safeguards requirements, including administrative, physical, and technical safeguards, must be contractually mandated
- Reporting obligations, specify breach notification timelines (typically 10 to 30 days for security incidents)
- Subcontractor compliance, the vendor must ensure that any subcontractors agree to the same restrictions
- Access provision for HHS audits, make internal practices and records available to the Secretary
- Return or destruction of PHI, define what happens to ePHI-containing logs at contract termination
- Individual access rights support, enabling the covered entity to fulfill patient access requests
⚠️ Critical point: Beyond minimum requirements, consider adding indemnification clauses and risk-shifting provisions that clearly allocate breach responsibility.
Vendor Compliance Certifications to Verify
Don’t accept “HIPAA-compliant” marketing claims at face value. Require evidence of these certifications:
| Certification | What It Validates | Why Healthcare Organizations Need It |
| SOC 2 Type II | Security controls operating effectively for 3 to 12 months | Demonstrates sustained operational security, not just point-in-time compliance |
| HITRUST CSF | Healthcare-specific control framework aligned with HIPAA, HITECH | Recognized certification specifically designed for organizations handling PHI |
| ISO 27001 | Information security management system maturity | An international standard providing a systematic approach to security |
HITRUST provides certification against healthcare-specific standards, while SOC 2 Type II provides attestation that controls function as intended over time. Many healthcare organizations require HITRUST from vendors handling PHI directly, as it demonstrates higher control maturity and direct HIPAA alignment.
PHI Handling Specifications to Demand
Before signing, get specific answers to these questions:
- Where does telemetry data reside? Verify US data centers and specific geographic locations for PHI storage
- How is PHI encrypted? Require AES-256 encryption at rest and TLS 1.3 in transit
- What happens at contract termination? Define data retention, return, or destruction procedures explicitly
- Can the vendor access PHI content? Distinguish between metadata access and full PHI visibility
- Are subprocessors involved? Cloud-based SIEMs may use subcontractors requiring BAA amendments
✅ UnderDefense BAA Readiness
UnderDefense executes BAAs as standard practice, not upon request. We’re SOC 2 Type II certified, with customer-controlled data residency options across Azure, GCP, AWS, Oracle Cloud, and fully on-premises deployments. PHI-containing telemetry remains in your data lake; UnderDefence MAXI connects to your environment rather than extracting data to ours. Upon termination, all detection logic and configurations transfer to you, no vendor lock-in, no PHI retention concerns.
Q6. How Should Healthcare Organizations Evaluate and Select Managed SIEM Providers?
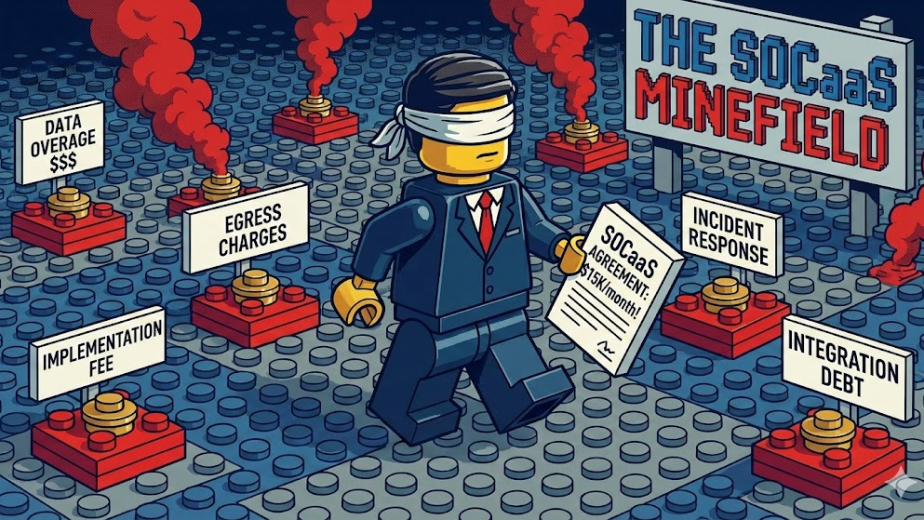
Choosing a managed SIEM provider for healthcare means committing to a security architecture that must satisfy both OCR auditors and actual threat prevention. Pick wrong, and you’re locked into proprietary tools that don’t understand EHR workflows, or left with alert noise your already-stretched team must investigate, or facing BAA compliance gaps that surface during your next audit.
The Wrong Way to Decide
Most healthcare security leaders choose based on brand recognition or “HIPAA-compliant” marketing claims. This ignores critical questions: Can they execute a BAA immediately? Have they integrated with your specific EHR platform? Can they contain threats, not just detect and escalate back to your team? Do they understand clinical workflows or treat healthcare like a generic enterprise?
The vendor evaluation process should start by identifying specific security needs, like protecting EHRs and improving HIPAA compliance. Yet most organizations skip rigorous assessment and compare solutions superficially.
📋 Healthcare SIEM Evaluation Framework (8 Criteria)
Score each potential vendor 0 to 2 on these criteria. Providers scoring 12+ represent a genuine operational partnership:
| Criteria | What to Evaluate | Discovery Question to Ask |
| 1. BAA Execution Readiness | Certifications (SOC 2 Type II, HITRUST), willingness to sign before pilot | “Will you sign our BAA before the pilot begins?” |
| 2. EHR Integration Experience | Documented deployments with Epic, Cerner, Meditech, athenahealth | “Show me an EHR integration you’ve deployed.” |
| 3. PHI Access Monitoring Depth | Clinical workflow understanding, not just infrastructure logs | “Can you correlate EHR access patterns with identity events?” |
| 4. Response Capability | Detection-only vs. containment/remediation | “What’s your documented MTTR for critical healthcare incidents?” |
| 5. User Verification Capability | ChatOps for alert context, direct communication with clinical staff | “Can your analysts communicate directly with our clinical staff to verify alerts?” |
| 6. Compliance Automation | HIPAA evidence generation built-in vs. separate tools | “Does your platform automatically generate audit documentation?” |
| 7. Pricing Transparency | Published rates vs. “contact sales.” | “What’s your per-endpoint monthly cost?” |
| 8. Onboarding Timeline | Months vs. weeks to operational | “What happens to our detection rules if we leave?” |
Key selection criteria include vendor financial stability, 24/7/365 support capability, and ability to handle critical issues within defined SLAs.
✅ UnderDefense Evaluation Scorecard
| Criterion | UnderDefense Score | Evidence |
| BAA-ready | ✅ 2 | Executed as standard practice, SOC 2 Type II certified |
| EHR integrations | ✅ 2 | Epic, Cerner, Meditech, athenahealth experience |
| Clinical PHI monitoring | ✅ 2 | Behavioral analytics across clinical applications |
| Full containment capability | ✅ 2 | 2-minute Alert-to-Triage and 15-minute escalation for critical incidents. |
| ChatOps user verification | ✅ 2 | Slack/Teams/Email direct verification with affected users |
| Forever-free HIPAA compliance kits | ✅ 2 | Included with MDR subscription |
| Published pricing | ✅ 2 | $11-15/endpoint/month, transparent |
| 30-day turnkey onboarding | ✅ 2 | No 6-month deployment cycles |
Total: 16/16
“UnderDefense MAXI helps us secure sensitive data and mitigate potential cyber threats, which improves the overall security of our business operations.”
— Arman N., CTO, Mid-Market G2 Verified Review
Q7. How Does Managed SIEM Integrate with EHR Systems and IoMT Medical Devices?
Healthcare SIEM effectiveness depends on visibility where ePHI actually lives, EHR systems and connected medical devices. Without ingesting Epic audit logs, Cerner access events, Meditech user activity, AND IoMT network traffic, threat detection operates blind to both clinical workflows and the fastest-growing attack surface in healthcare.
EHR Integration Mechanisms
API-based log collection from major EHR platforms enables meaningful security monitoring:
- Epic, Chronicles audit logs capturing user access, chart modifications, and PHI export events
- Cerner (Oracle Health), Millennium audit events with OAuth 2.0 authentication and comprehensive event tracking
- Meditech, User activity tracking across clinical modules
- athenahealth+, Cloud-based audit trails via API integration
Comprehensive audit logging is essential for Cerner integration; all significant events including API requests, logins, and data access must be logged for security monitoring, compliance reporting, and forensic analysis. Real-time monitoring using SIEM solutions helps detect threats before they escalate.
What EHR Events to Monitor
| Event Category | Examples | Why It Matters |
| Access patterns | Chart access outside care relationships, bulk record exports | Identifies potential insider threats or compromised accounts |
| Temporal anomalies | After-hours activity, unusual search patterns | Flags suspicious behavior requiring verification |
| Privilege changes | Escalation requests, role modifications | Detects unauthorized access attempts |
| PHI operations | Copy/print events, external transfers | Catches data exfiltration attempts |
RBAC and audit logging ensure only authorized personnel have access to sensitive patient data while maintaining accurate records of all access activities.
IoMT Security Monitoring: The Expanding Attack Surface
Connected medical devices (infusion pumps, imaging systems, patient monitors) average 10 to 15 per hospital bed, most running legacy OS with unencrypted protocols and default credentials. The risks are severe:
- Patient Harm: Attackers could modify drug dosages or disable life-supporting functions
- Data Breaches: PHI can be stolen or sold on the dark web
- Network Compromise: A compromised biomedical device becomes a foothold to pivot into EMR systems
FDA premarket cybersecurity guidance now requires manufacturer security documentation, but operational monitoring falls to healthcare IT. SIEM must extend to IoMT networks, correlating device behavior with clinical workflows and network segmentation policies.
Why Unified Visibility Matters
The difference between generic SIEM and healthcare-ready SIEM is understanding that Dr. Smith accessing 200 patient records during morning rounds is normal, but the billing clerk accessing the same records at midnight is a breach in progress. And knowing that an infusion pump communicating with an external IP at 3 AM is an attack, not a firmware update.
Device segmentation and isolation capabilities are critical; medical devices must be isolated when anomalous network behavior or a breach is detected, with programmatic alerting to enable clinical teams sufficient notice for contingency plans.
✅ UnderDefense Healthcare Integration
UnderDefence MAXI platform monitors EHR systems and IoMT networks alongside identity, cloud, and endpoint telemetry, correlating clinical workflows with security events. Our 96% MITRE ATT&CK coverage includes healthcare-specific techniques. We process 6TB of security telemetry daily across 500+ clients, including healthcare organizations with complex EHR and IoMT environments.
Q8. Should Healthcare Organizations Deploy Cloud-Based or On-Premises SIEM?
The cloud vs. on-premises decision for healthcare SIEM depends on PHI residency requirements, existing infrastructure investments, and compliance posture. Cloud SIEM offers faster deployment, automatic scaling, and reduced maintenance burden, but raises questions about PHI storage location and third-party access. On-premises SIEM provides maximum data control but requires significant infrastructure investment and specialized staffing. Most healthcare organizations benefit from hybrid approaches that keep PHI logs on-premises while leveraging cloud-based analysis and response capabilities.
☁️ Cloud SIEM: Advantages and Concerns
Advantages:
- 30-day deployment vs. 6 to 12 months for on-premises
- Automatic updates and elastic scaling during incidents
- Built-in redundancy with automatic data replication across availability zones
- Reduced infrastructure costs and maintenance burden
Concerns:
- PHI residency verification required, confirm US data centers and specific geographic locations
- BAA requirements for both cloud provider AND SIEM vendor
- Vendor access: The provider has the technical capability to access PHI
- Data portability challenges when switching providers (vendor lock-in risk)
🏢 On-Premises SIEM: Advantages and Challenges
Advantages:
- Complete data sovereignty, PHI never leaves your infrastructure
- Full visibility and control over how data is handled, processed, and stored
- No third-party PHI access without explicit permission
- Faster local access with minimized latency for bandwidth-intensive applications
Challenges:
- 💰 $500K to $2M+ first-year infrastructure investment (hardware, staff, infrastructure)
- 6 to 8 FTE required for 24/7 operations
- Must build disaster recovery and geographic redundancy yourself
- Responsible for all backup, maintenance, and upgrade burden
On-premises SIEM offers greater flexibility for meeting compliance standards since data stored locally gives organizations full visibility and control, particularly important for HIPAA, where data sovereignty and security are paramount.
🔄 Hybrid Architecture: The Practical Middle Ground
Many healthcare organizations implement hybrid approaches:
- The de-identification process removes/encrypts PHI before cloud transfer
- Secure connectivity via VPN or dedicated circuits
- On-premises for PHI storage, cloud for processing and analysis
- Both environments are verified HIPAA-compliant
✅ UnderDefense Deployment Flexibility
UnderDefense’s MAXI platform operates wherever your data lives, Azure, GCP, AWS, Oracle Cloud, or fully on-premises. PHI-containing logs stay in your data lake; our analysts access data where it resides rather than extracting it to external systems. This architecture satisfies the strictest PHI residency requirements while delivering cloud-native detection capabilities.
“Their team is proactive in identifying and addressing threats, providing 24/7 oversight. UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk.”
— Oleg K., Director of Information Security, Mid-Market G2 Verified Review
UnderDefense deploys healthcare organizations in 30 days regardless of architecture choice, because our vendor-agnostic approach means adapting to your environment rather than forcing infrastructure changes.
Q9. What Does Audit-Ready HIPAA Compliance Look Like with Managed SIEM?
Score your HIPAA audit readiness against these 8 criteria, then reference the HIPAA-to-SIEM capability mapping to understand exactly how managed SIEM addresses each compliance requirement.
📋 HIPAA Audit-Readiness Checklist
| ☐ | Criteria | What Auditors Verify |
| ☐ | 24/7/365 ePHI access monitoring with documented coverage | Continuous monitoring evidence, not business-hours-only |
| ☐ | 6-year tamper-proof log retention with integrity verification | Per 45 CFR §164.316(b)(2)(i), documentation retained from creation or last effective date |
| ☐ | Automated access control validation against role assignments | RBAC enforcement logs correlating user permissions to actual access |
| ☐ | Real-time alerting for unauthorized PHI access attempts | Anomaly detection with documented response times |
| ☐ | Documented incident response procedures with tested playbooks | IR plans with evidence of regular tabletop exercises |
| ☐ | Business Associate oversight evidence for all vendors with PHI access | BAA registry with compliance verification documentation |
| ☐ | Security awareness training records correlated with access privileges | Training completion tied to access provisioning |
| ☐ | Annual risk assessment with documented remediation tracking | Risk analysis per §164.308(a)(1) with closure evidence |
HIPAA-to-SIEM Capability Mapping
This mapping shows exactly how managed SIEM functions address specific HIPAA Security Rule requirements:
| HIPAA Requirement | CFR Citation | SIEM Capability | Evidence Generated |
| Audit Controls | §164.312(b) | Log collection & centralized analysis | Access audit reports, user activity logs |
| Integrity Controls | §164.312(c) | File integrity monitoring | Change detection logs, tamper alerts |
| Person/Entity Authentication | §164.312(d) | Identity correlation | Login activity reports, MFA verification |
| Risk Analysis | §164.308(a)(1) | Vulnerability correlation | Risk posture dashboards, gap analysis |
| Security Incident Procedures | §164.308(a)(6) | Alert triage & response workflows | Incident documentation, MTTR metrics |
| Access Control | §164.312(a) | Privilege monitoring | Access validation reports, anomaly alerts |
| Breach Notification Support | §164.400-414 | Detection within a 60-day window | Timeline documentation, notification evidence |
📊 Score Interpretation
✅ 6-8 checks: Audit-ready, maintain continuous monitoring and documentation
⚠️ 3-5 checks: Critical gaps exist, OCR findings likely without remediation
❌ 0-2 checks: Significant compliance exposure requiring immediate action
The most cautious strategy, as HHS guidance indicates, is maintaining all audit logs for a minimum of six years. Organizations often confuse the Security Rule’s logging requirement (§164.312(b)) with the documentation retention requirement (§164.316(b)(2)(i)), but treating audit logs as “activities” requiring six-year retention satisfies compliance objectives.
✅ UnderDefense Audit Readiness
UnderDefense transforms every unchecked box into continuous compliance. UnderDefence MAXI Compliance auto-collects evidence, maps controls to HIPAA requirements in real-time, and surfaces gaps before auditors find them. Clients achieve full regulatory compliance within 30 days, with forever-free HIPAA compliance kits eliminating hidden GRC tool costs.
“They’ve also made our audit process much less painful. The reports from their platform give us clear evidence of our security controls and incident response capabilities. When auditors or clients ask questions about our security posture, we can pull up exactly what they need to see.”
— Verified User, Marketing and Advertising G2 Verified Review
Q10. How Does Managed SIEM Compare to Building an In-House Healthcare SOC?
Healthcare security leaders face a fundamental architecture decision: build internal SOC capabilities with dedicated SIEM and compliance expertise, or partner with managed providers who specialize in healthcare security and regulatory requirements. Both approaches can achieve HIPAA compliance, but through fundamentally different resource models with dramatically different TCO.
In-House SOC: Strengths & Limitations
Building a healthcare SOC requires significant investment:
Strengths:
- Full operational control and institutional knowledge retention
- Career development paths for security talent
- Deep integration with clinical workflows over time
Limitations:
⏰ Setup time: 6 to 18 months before operational
💰 Upfront cost: $1M to $2M infrastructure and hiring
👥 Staffing burden: 6 to 12 analysts required for true 24/7 coverage
📉 Talent reality: 23% cybersecurity talent shortage; 18-month average analyst tenure due to burnout
❌ Healthcare expertise scarcity: HIPAA, HITECH, state laws require specialized compliance knowledge
Managed SIEM Approach
Managed SIEM eliminates staffing burden while preserving visibility through a concierge model. Analysts learn your organization, VIPs, clinical workflows, critical assets, care team structures, and provide context-aware responses without internal SOC investment. Healthcare compliance expertise comes included rather than requiring internal hiring.
💰 TCO Comparison Table
| Dimension | In-House SOC | UnderDefense Managed SIEM |
| Annual fully-loaded cost | $1.2M+ (staffing, tools, infrastructure) | $150K to $300K |
| Coverage hours | Requires shift coverage (6+ FTEs minimum) | 24/7/365 included |
| Response time | Variable (depends on staffing/availability) | 2-minute Alert-to-Triage and 15-minute escalation for critical incidents. |
| Compliance automation | Separate GRC tool ($50K to $150K/year) | Included (forever-free kits) |
| Healthcare expertise | Must hire specialized talent | Included |
| Scalability | Hire more analysts | Elastic, scales with your needs |
| Implementation | 6 to 18 months | 30-day turnkey |
| Vendor lock-in | Tool-dependent SIEM investment | Vendor-agnostic (250+ integrations) |
Who Should Choose What
Build in-house if: You have a $1.5M+ annual security budget, can hire and retain 6+ healthcare-specialized analysts, and want full operational control with long-term institutional knowledge building.
Choose managed SIEM if: You need 24/7 coverage without 24/7 headcount, want HIPAA compliance included rather than bolt-on, and prefer analysts who learn your clinical environment rather than rotating through generic ticket queues.
“Underdefense is a great choice for teams like ours that are short on resources. It automates many tasks, plus, with 24/7 monitoring, we know we’re always protected. The platform seamlessly integrates our existing security tools, simplifying management.”
— Inga M., CEO, Mid-Market G2 Verified Review
Q11. What Are the Best Managed SIEM Solutions for Healthcare Organizations?
The leading managed SIEM providers for healthcare organizations in 2026 include UnderDefense, Fortified Health Security, CyberMaxx, Arctic Wolf, and Secureworks, each with distinct approaches to HIPAA compliance, EHR integration, and response capabilities. Selection depends on existing security investments, compliance maturity, and whether you need detection-only or full response.
Why This Matters for Healthcare
Healthcare managed SIEM has evolved beyond basic log aggregation. The key differentiators now are:
- BAA readiness, Non-negotiable for any vendor touching ePHI
- EHR integration depth, Epic, Cerner, and Meditech compatibility
- PHI-specific threat detection, Clinical workflow understanding
- Response capability, Monitoring-only vs. full containment
- Compliance automation, Manual evidence gathering vs. continuous audit-readiness
Selection Criteria Preview
What separates top healthcare SIEM providers:
- BAA execution readiness and healthcare compliance certifications (SOC 2 Type II, HITRUST)
- EHR and IoMT integration capabilities with documented deployments
- Detection-only vs. full containment response (critical for ransomware)
- HIPAA compliance automation included vs. separate GRC tool purchase
- Pricing transparency and TCO predictability (published vs. “contact sales”)
- Deployment flexibility (cloud, on-premises, hybrid) for PHI residency requirements
The Right Choice Depends on Your Situation
Each provider excels in different scenarios: Fortified Health Security for healthcare-exclusive focus, UnderDefense for vendor-agnostic integration with existing security investments, Arctic Wolf for organizations preferring single-vendor simplicity. The right choice depends on your current security stack, compliance maturity, and operational model.
This analysis is based on documented response times, G2 Spring 2025 rankings (where UnderDefense earned 12 badges, including Best Support), and operational outcomes across 500+ MDR deployments.
Q12. Frequently Asked Questions: Managed SIEM for Healthcare and HIPAA Compliance
Does managed SIEM include compliance reporting for HIPAA?
Yes, modern managed SIEM solutions include HIPAA compliance reporting capabilities, though the depth varies significantly by provider. Core features typically include automated audit log generation, access control monitoring reports, and incident documentation. Advanced providers offer pre-built HIPAA report templates, automated evidence collection for audit preparation, and continuous compliance posture dashboards.
UnderDefense includes forever-free HIPAA compliance kits with MDR subscriptions, eliminating the need for separate GRC tool purchases that typically cost $50K to $150K annually.
How long must HIPAA audit logs be retained?
Per 45 CFR §164.316(b)(2)(i), documentation must be retained for six years from the date of creation or the date when it last was in effect, whichever is later. While the Security Rule doesn’t explicitly define audit log retention, HHS guidance indicates that treating audit trails as “activities” means six-year retention satisfies compliance objectives.
⚠️ Important: Some states have longer retention requirements. Healthcare organizations should verify state-specific laws and contractual obligations that may extend beyond the federal six-year minimum.
Can managed SIEM monitor medical devices (IoMT)?
Yes. Modern managed SIEM solutions can ingest telemetry data from Internet of Medical Things (IoMT) devices, enabling organizations to monitor device behavior, detect vulnerabilities or malicious activity, and ensure compliance with evolving FDA cybersecurity guidelines.
Key IoMT monitoring capabilities include:
- Network traffic analysis from infusion pumps, imaging systems, and patient monitors
- Anomaly detection for device communication patterns
- Integration with network segmentation policies
- Alerting when devices communicate with unauthorized external IPs
What is the HIPAA breach notification timeline?
HIPAA requires notification within 60 days of discovering a breach affecting individuals. For breaches affecting 500 or more individuals, organizations must notify HHS immediately (within 60 days) and local media. Breaches affecting fewer than 500 individuals can be reported to HHS annually.
SIEM platforms with SOAR capabilities automate breach detection and documentation, helping organizations meet these tight timelines while generating the evidence trail required for regulatory reporting.
Do managed SIEM vendors need to sign a BAA?
Yes, any vendor with access to ePHI is a Business Associate under HIPAA. Per 45 CFR §164.502(e), covered entities must obtain written assurance (BAA) before sharing PHI with vendors. This applies to managed SIEM providers who access, process, or store security telemetry containing ePHI.
Verify before engagement: BAA execution readiness, SOC 2 Type II certification, HITRUST certification (for healthcare-specific validation), and data residency options for PHI-containing logs.
What’s the difference between managed SIEM and MDR for healthcare?
The terminology often overlaps, creating confusion:
| Capability | Managed SIEM | MDR (Managed Detection & Response) |
| Log collection & correlation | ✅ Core function | ✅ Typically included |
| Compliance reporting | ✅ Primary focus | ⚠️ Varies by provider |
| Threat detection | ✅ Rule-based alerting | ✅ Advanced + threat hunting |
| Incident response | ❌ Detection only | ✅ Containment & remediation |
| Human analyst support | ⚠️ Varies | ✅ 24/7 analyst coverage |
The practical answer: Most healthcare organizations benefit from integrated approaches combining SIEM compliance capabilities with MDR response capabilities, detecting threats AND containing them before patient data is compromised.
1. What makes a SIEM solution HIPAA-compliant, and what specific security monitoring requirements must it address?
A HIPAA-compliant SIEM must address specific requirements under the HIPAA Security Rule (45 CFR Part 164). We see organizations mistakenly believe any SIEM qualifies, but true compliance requires addressing these core mandates:
- Audit Controls (§164.312(b)): The SIEM must record and examine all ePHI system activity, capturing user identification, timestamps, event types, patient/record identifiers, source information, and access outcomes
- Access Controls (§164.312(a)): Continuous monitoring of privilege assignments against actual access patterns
- Integrity Controls (§164.312(c)): File integrity monitoring with tamper detection
- Person/Entity Authentication (§164.312(d)): Identity correlation across login events and MFA verification
The SIEM must also support 6-year log retention per §164.316(b)(2)(i) and generate evidence for OCR audits. At UnderDefense, our managed SIEM service auto-maps security telemetry directly to HIPAA controls, providing auditors with verifiable evidence rather than theoretical policies.
2. How does managed SIEM detect threats to Protected Health Information before they escalate into reportable breaches?
We approach PHI threat detection through multi-layer correlation that traditional tools miss. The challenge is that healthcare threats often look legitimate; a compromised nurse credential accessing patient records appears normal without behavioral context.
Our detection methodology includes:
- EHR access pattern analysis: Correlating Epic, Cerner, or Meditech audit logs with identity behavior to identify anomalous PHI access
- Temporal anomaly detection: Flagging after-hours activity, unusual search patterns, or bulk record exports
- IoMT network monitoring: Detecting medical devices communicating with unauthorized external IPs
- Credential compromise indicators: Identifying impossible travel, failed authentication patterns, and privilege escalation attempts
The critical differentiator is response capability. Detection-only SIEM creates alert noise; we provide full incident response with documented 2-minute Alert-to-Triage and 15-minute escalation for critical incidents for critical healthcare incidents. When anomalies require context, our analysts verify directly with affected users via Slack or Teams before escalating, closing the gap that lets breaches progress undetected.
3. What Business Associate Agreement (BAA) requirements must managed SIEM vendors meet under HIPAA?
Any managed SIEM vendor with access to ePHI is classified as a Business Associate under 45 CFR §164.502(e), requiring a written BAA before any PHI sharing. We’ve seen organizations select vendors without verifying BAA readiness, creating compliance exposure from day one.
Your BAA must contain these seven non-negotiable provisions under §164.504(e):
- Permitted uses and disclosures of PHI (security monitoring only)
- Administrative, physical, and technical safeguards requirements
- Breach reporting obligations (typically 10 to 30 days for security incidents)
- Subcontractor compliance requirements
- HHS audit access provisions
- PHI return or destruction procedures at termination
- Individual access rights support
Beyond the BAA, verify vendor certifications: SOC 2 Type II demonstrates sustained operational security, while HITRUST CSF provides healthcare-specific validation. We execute BAAs as standard practice, not upon request, and our compliance services include forever-free HIPAA compliance kits to eliminate hidden GRC costs.
4. Should healthcare organizations choose cloud-based or on-premises SIEM for PHI protection?
This decision depends on PHI residency requirements, existing infrastructure investments, and compliance posture. We’ve helped healthcare organizations implement all three models, and each has distinct trade-offs.
Cloud SIEM advantages:
- 30-day deployment vs. 6 to 12 months for on-premises
- Automatic updates and elastic scaling
- Reduced infrastructure and maintenance burden
Cloud SIEM concerns:
- PHI residency verification required (confirm US data centers)
- BAA needed for both cloud provider AND SIEM vendor
- Vendor access to PHI-containing telemetry
On-premises advantages:
- Complete data sovereignty, PHI never leaves your infrastructure
- No third-party access without explicit permission
On-premises challenges:
- $500K to $2M+ first-year infrastructure investment
- 6 to 8 FTEs required for 24/7 operations
Most healthcare organizations benefit from hybrid approaches. Our UnderDefence MAXI platform operates wherever your data lives, Azure, GCP, AWS, Oracle Cloud, or fully on-premises. PHI-containing logs stay in your data lake while we provide cloud-native detection capabilities.
5. How much does managed SIEM cost compared to building an in-house healthcare SOC?
We’ve documented the TCO comparison extensively, and the difference is substantial. Building an in-house healthcare SOC requires $1M to $2M upfront infrastructure and hiring investment, with 6 to 18 months before becoming operational. Annual fully-loaded costs exceed $1.2M when including staffing, tools, and infrastructure.
The staffing reality is particularly challenging:
- True 24/7 coverage requires 6 to 12 analysts minimum
- 23% cybersecurity talent shortage makes hiring difficult
- 18-month average analyst tenure due to burnout creates a constant recruitment burden
- Healthcare-specific expertise (HIPAA, HITECH, state laws) narrows the talent pool further
Managed SIEM eliminates these challenges. Our MDR pricing ranges from $150K to $300K annually, including 24/7/365 coverage, compliance automation, and healthcare expertise. You get documented 2-minute Alert-to-Triage and 15-minute escalation for critical incidents, forever-free HIPAA compliance kits (eliminating $50K to $150K annual GRC tool costs), and 30-day turnkey implementation.
Choose managed SIEM if you need 24/7 coverage without a 24/7 headcount and want HIPAA compliance included rather than bolt-on.
6. How does managed SIEM integrate with Epic, Cerner, and other EHR systems? Answer:
Healthcare SIEM effectiveness depends on visibility of where ePHI actually lives. Without ingesting EHR audit logs, threat detection operates blindly to clinical workflows that distinguish legitimate access from breaches.
We integrate with major EHR platforms through API-based log collection:
- Epic: Chronicles audit logs capturing user access, chart modifications, and PHI export events
- Cerner (Oracle Health): Millennium audit events with OAuth 2.0 authentication and comprehensive event tracking
- Meditech: User activity tracking across clinical modules
- athenahealth: Cloud-based audit trails via API integration
Critical EHR events we monitor include:
- Access patterns (chart access outside care relationships, bulk record exports)
- Temporal anomalies (after-hours activity, unusual search patterns)
- Privilege changes (escalation requests, role modifications)
- PHI operations (copy/print events, external transfers)
The difference between generic SIEM and healthcare-ready SIEM is understanding that Dr. Smith accessing 200 patient records during morning rounds is normal, but the billing clerk accessing those same records at midnight is a breach in progress.
7.What is the HIPAA breach notification timeline, and how does SIEM help meet these requirements?
HIPAA requires notification within 60 days of discovering a breach affecting individuals. The timeline requirements are strict:
|
Breach Size |
Individual Notification |
HHS/OCR Notification |
Media Notification |
|
500+ individuals |
Within 60 days |
Within 60 days |
Within 60 days (if 500+ in a single state) |
|
Under 500 individuals |
Within 60 days |
Annual report |
Not required |
The 60-day deadline runs from the breach discovery date, the first day you know, or by exercising reasonable diligence should know, that a breach occurred. State laws often impose stricter timelines: California requires 15 business days for certain healthcare breaches, Florida mandates 30 days.
SIEM platforms with SOAR capabilities automate breach detection and documentation, helping meet these tight timelines. We provide instant forensic documentation with observable, auditable investigation workflows. When OCR investigates, they expect forensic-quality evidence. Our threat detection generates the complete timeline documentation, affected individual identification, and containment evidence that satisfies regulatory requirements.
8. How do we evaluate and score managed SIEM vendors for healthcare compliance?
We recommend scoring vendors 0 to 2 across eight criteria. Providers scoring 12+ represent a genuine operational partnership for healthcare organizations:
- BAA Execution Readiness: Will they sign before the pilot begins? (SOC 2 Type II, HITRUST certification)
- EHR Integration Experience: Documented deployments with Epic, Cerner, Meditech, athenahealth
- PHI Access Monitoring Depth: Clinical workflow understanding, not just infrastructure logs
- Response Capability: Detection-only vs. full containment/remediation (ask for documented MTTR)
- User Verification Capability: ChatOps for direct communication with clinical staff
- Compliance Automation: HIPAA evidence generation built-in vs. separate GRC tool purchase
- Pricing Transparency: Published rates vs. “contact sales.”
- Onboarding Timeline: Months vs. weeks to operational
Key discovery questions: “Show me an EHR integration you’ve deployed.” “What happens to our detection rules if we leave?” “Does your platform automatically generate audit documentation?”
Download our free SOC Provider Evaluation Checklist to systematically assess vendor capabilities against healthcare requirements.
The post Managed SIEM for Healthcare: HIPAA Compliance and PHI Threat Detection Guide appeared first on UnderDefense.