Q1: What Is Managed SIEM for Financial Services and Why Does It Matter Now?
The Compliance Chaos Reality
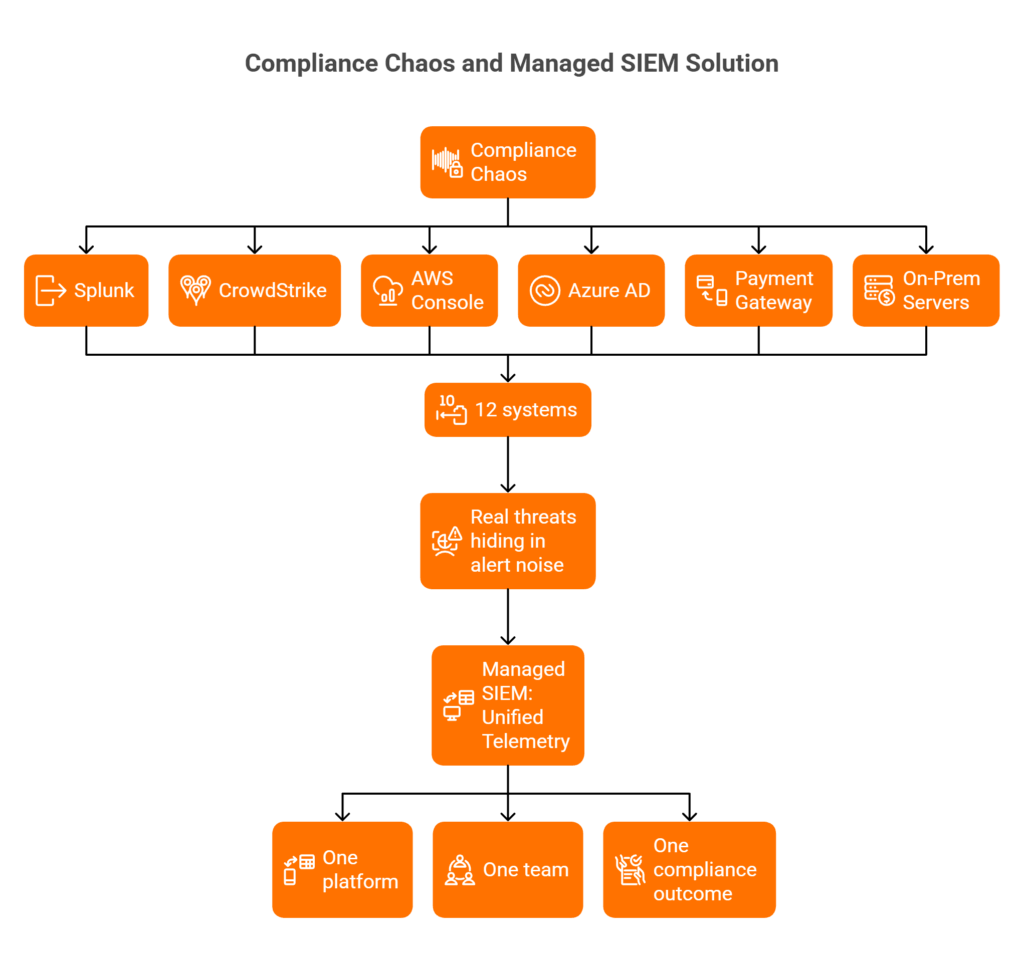
Financial services organisations operate under relentless regulatory pressure: PCI-DSS, SOX, GLBA, and GDPR, each demanding specific logging, monitoring, and audit evidence. The operational reality? Most institutions run fragmented security stacks: Splunk for logs, CrowdStrike for endpoints, separate cloud consoles for AWS and Azure, and disconnected identity systems. This creates what I call “compliance chaos”: audit evidence scattered across twelve systems while real threats hide in alert noise nobody has time to investigate.
The math doesn’t work. PCI-DSS Requirement 10 alone mandates daily log reviews, yet most security teams spend their days translating raw data for auditors instead of hunting threats.
Why Traditional Approaches Keep Failing
Legacy on-premise SIEM requires dedicated teams of 5-7 analysts just to keep rules tuned and false positives manageable. Traditional MSSPs provide “checkbox monitoring”: they’ll confirm your logs exist but won’t tell you if someone’s exfiltrating cardholder data at 2 AM. DIY SIEM creates technical debt without improving security posture; you’ve built expensive log storage, not detection capability.
⚠️ The false economy here is real. Organisations invest $500K+ in SIEM platforms, then discover they need another $1M+ annually in staff to make it operational.
The Managed SIEM Evolution
Financial services need systems that correlate events across payment processing, identity systems, and cloud infrastructure while generating compliance evidence automatically. Detection without compliance automation is just expensive logging. The industry is shifting toward managed models because the alternative: building and staffing a 24/7 SOC, isn’t realistic for most organisations.
How the AI SOC + Human Ally Model Changes This
At UnderDefense, we built UnderDefence MAXI specifically for this problem. Our platform connects to 250+ existing tools: your Splunk, your CrowdStrike, your Azure AD, without forcing replacement. We correlate across your entire cardholder data environment in real-time, generating PCI-DSS Requirement 10 evidence as a byproduct of threat detection.
The difference is human expertise that understands financial services. When our platform flags suspicious activity on a payment processing server at 3 AM, our analysts don’t just escalate: they verify, contain, and document. You wake up to an incident report, not 47 unread alerts.
✅ Unified telemetry from your existing stack
✅ 24/7 analyst oversight with financial services expertise
✅ Automated compliance evidence for PCI-DSS, SOX, GLBA
❌ No tool replacement required
❌ No 6-month implementation projects
Why March 2025 Creates Urgency
PCI-DSS v4.0’s new requirements hit enforcement on March 31, 2025. Requirement 10.4.1.1 mandates automated mechanisms for daily log reviews: manual spot-checks no longer satisfy auditors. Financial institutions without continuous automated monitoring will face compliance gaps precisely when QSA assessments arrive. Organisations using managed SIEM report 60% reduction in compliance audit preparation time while achieving the continuous monitoring PCI-DSS v4.0 now mandates. The system generating alerts is the same system generating audit evidence: one investment, multiple compliance outcomes.
Q2: What Are the Specific PCI-DSS Requirement 10 Mandates That SIEM Must Address?
Requirement 10 Overview: Log and Monitor All Access
PCI-DSS Requirement 10 is titled “Log and Monitor All Access to System Components and Cardholder Data.” For financial services, this isn’t abstract compliance: it’s the foundation of proving you can detect and respond to threats targeting payment data.
The requirement breaks into sub-requirements: 10.2 (audit log implementation), 10.3 (log content requirements), 10.4 (review mechanisms), 10.5 (retention requirements), and 10.7 (detection and response). As of March 31, 2025, several new mandates transition from best practice to mandatory.
Specific Logging Requirements (10.2.1.1-10.2.1.7)
Your SIEM must capture and retain logs for:
| Sub-Requirement | What Must Be Logged |
| 10.2.1.1 | All individual user access to cardholder data |
| 10.2.1.2 | All actions by any individual with administrative access |
| 10.2.1.3 | Access to all audit trails |
| 10.2.1.4 | Invalid logical access attempts |
| 10.2.1.5 | Use of and changes to identification and authentication mechanisms |
| 10.2.1.6 | Initialisation, stopping, or pausing of audit logs |
| 10.2.1.7 | Creation and deletion of system-level objects |
Log Content Requirements (10.3.1-10.3.7)
Each audit trail entry must contain: user identification, event type, date and time, success or failure indication, origination of event, and identity or name of affected data/system component/resource.
⏰ Critical v4.0 Changes Effective March 2025:
- 10.4.1.1: Automated mechanisms must perform daily log reviews (manual spot-checks are insufficient)
- 10.4.2.1: Risk-based review frequency required for non-CHD system components
- 10.5: Minimum 12 months retention, 3 months readily available
PCI-DSS Requirement → SIEM Capability Mapping
| Requirement | SIEM Capability | Implementation Approach |
| 10.2 Logging | Event collection across the CHD environment | Pre-built connectors for payment systems, core banking |
| 10.3 Log content | Field normalisation and enrichment | Automated extraction of required fields regardless of source format |
| 10.4.1.1 Daily review | Automated anomaly detection | AI-driven analysis with human analyst validation |
| 10.5 Retention | Compliant log storage | 12-month retention with 3-month hot storage |
| 10.7 Detection/Response | Real-time alerting and incident response | 24/7 SOC with documented MTTR |
How UnderDefense Simplifies Requirement 10 Compliance
We’ve pre-configured UnderDefence MAXI with PCI-DSS Requirement 10 detection rules mapped to every sub-requirement. The platform automates daily log reviews with AI-driven anomaly detection while our analysts provide human validation that auditors require.
We generate audit-ready evidence packages automatically: eliminating the 6-month SIEM implementation projects that leave financial institutions non-compliant during the gap. Our 30-day deployment ensures you’re covered before the March 2025 deadlines arrive.
Q3: How Does Managed SIEM Automate Compliance Reporting for Financial Institutions?
The Audit Preparation Nightmare
It’s Q4, and your QSA is requesting evidence for your annual PCI-DSS assessment. Your team spends three weeks pulling logs from twelve different systems, manually correlating user access records, and formatting reports into auditor-friendly packages. Meanwhile, SOX auditors want financial system access trails, and your GDPR documentation hasn’t been updated since last year’s assessment.
You’ve become a compliance documentation factory instead of a security team. Sound familiar?
Why This Problem Persists
Financial institutions face overlapping regulatory requirements: PCI-DSS 10.4, SOX Section 404, GLBA Safeguards Rule, each demanding log retention, access monitoring, and audit trails. But traditional tools generate logs without generating compliance evidence.
Your SIEM collects events. Your compliance team translates them into auditor language. This translation layer consumes resources that should be hunting threats.
The Hidden Costs Nobody Calculates
💰 120+ hours annually spent on compliance documentation per framework
💰 $50K+ in consultant fees for audit preparation assistance
💰 30% of security team capacity consumed by evidence gathering
💰 Failed audit risk from documentation gaps discovered during assessment
One CISO told me their team spent more time preparing for audits than responding to actual security incidents. That’s backwards.
How Compliance Automation Should Work
The system monitoring for threats should simultaneously generate compliance evidence. Daily log reviews required by PCI-DSS 10.4.1.1 should produce audit artefacts automatically. Access monitoring for security should double as SOX evidence.
One investment, multiple compliance outcomes. Detection and compliance aren’t separate problems: they’re the same data analysed for different purposes.
UnderDefense’s Compliance Automation Approach
UnderDefence MAXI’s compliance automation module generates pre-formatted evidence packages for PCI-DSS, SOX, HIPAA, and
ISO 27001 from the same security telemetry used for threat detection.
Our clients consistently report reducing audit preparation from three weeks to three days:
“The biggest problem they solved was our 24/7 coverage gap. We needed round-the-clock monitoring for compliance reasons, but building our own SOC wasn’t realistic with our budget and the current hiring market. They’ve also made our audit process much less painful. The reports from their platform give us clear evidence of our security controls and incident response capabilities.”
— Verified User, Marketing and Advertising |G2 Verified ReviewUnderDefense helped us navigate key compliance requirements, ensuring we met industry standards smoothly and efficiently. What stood out the most was their responsiveness and flexibility: no matter the issue, they tackled it quickly and professionally.”
— Arman N., CTO, Mid-Market | G2 Verified Review
✅ Compliance evidence becomes a byproduct of security monitoring: not a separate workstream.
Q4: What Fraud Detection Capabilities Should Financial Services SIEM Include?
The Capability Statement
Financial services SIEM must provide multi-layered fraud detection that correlates transaction patterns, user behaviour, and system access to identify account takeover, payment fraud, and money laundering indicators before financial impact occurs. Detection alone isn’t enough: you need verification and response capability built into the same system.
How SIEM-Based Fraud Detection Actually Works
SIEM aggregates data from core banking systems, payment processors, identity providers, and endpoint security to establish behavioural baselines. Machine learning models detect deviations from normal patterns:
- Rapid transfers between multiple accounts within minutes
- Transactions involving high-risk jurisdictions outside the customer’s history
- Unusual login patterns immediately preceding large wire transfers
- OAuth application grants that indicate business email compromise preparation
- Access patterns inconsistent with the job role or customer relationship
The correlation is what catches sophisticated fraud. A single anomalous login might be nothing. That same login followed by a credential change and wire transfer request within 30 minutes: that’s the pattern your SIEM should catch and escalate.
Detection Scenarios That Matter
| Fraud Type | Detection Pattern | SIEM Correlation |
| ⚠️ Account Takeover | Impossible travel + credential change + wire transfer | Identity + endpoint + transaction data |
| ⚠️ Payment Fraud | Transaction deviation + after-hours activity + new payee | Core banking + access logs + time analysis |
| ⚠️ Insider Threat | Privilege escalation + bulk export + off-scope account access | UEBA + DLP + identity correlation |
| ⚠️ Money Laundering | Structuring patterns + rapid multi-account movement | Transaction monitoring + velocity analysis |
Why This Matters Financially
Financial institutions face $4.7M average fraud losses annually. SIEM-based fraud detection reduces time-to-detection from days to minutes, enabling intervention before funds leave the institution. Cross-system correlation catches sophisticated fraud that single-point solutions miss entirely.
UnderDefense’s Fraud Detection Differentiation
UnderDefence MAXI’s fraud detection goes beyond alerting. When suspicious patterns emerge, our analysts verify directly with affected users via Slack or Teams before escalating. This ChatOps verification closes the gap between detection and confirmation.
“Their team is proactive in identifying and addressing threats, providing 24/7 oversight. With UnderDefense MAXI, we’ve reduced security breaches. Their adherence to SLAs gives me confidence in our infrastructure’s protection.”
— Oleg K., Director of Information Security | G2 Verified Review“The real-time threat updates from UnderDefense MAXI are solid. But what really caught my attention was their rapid response time. Had a slight issue, and boom: they were on it faster than you can say ‘rapid response time.’”
— Mariana D., SMM | G2 Verified Review
✅ Detection that verifies before escalating: reducing false positives by 99% while ensuring real fraud gets an immediate response.
Q5: How Does SIEM Detect and Prevent Insider Threats in Financial Institutions?
Insider threats cost financial services organisations over $20 million annually to resolve: the highest of any industry. The uncomfortable truth is that employees with legitimate access bypass your perimeter defences entirely. Firewalls don’t help when the threat is already inside. Effective SIEM detects insider threats through User and Entity Behaviour Analytics (UEBA) that establishes behavioural baselines and flags deviations: unusual data access, off-hours activity, bulk downloads, or access to accounts outside normal job scope.
Why Traditional Monitoring Fails Insiders
According to the 2024 LevelBlue Risk Radar Report, 40% of financial institutions reported an increase in insider attacks over the past year, and 45% faced more than five insider threat incidents in that period. The average cost of an insider breach? A staggering $5 million. Traditional signature-based detection doesn’t catch these threats because insiders aren’t using malware: they’re using their own credentials.
Key Detection Mechanisms
- Behavioural baseline comparison: Establishes “normal” patterns and detects deviation: accessing customer records at 2 AM when they’ve never worked nights
- Privilege escalation monitoring: Unauthorised permission changes, sudden admin tool usage, or access to systems outside job scope
- Data exfiltration signals: Bulk exports, unusual file transfers to personal email, creation of forwarding rules
- Access anomalies: Geographic impossibilities (logging in from two continents simultaneously), accessing accounts outside the assigned portfolio
- Correlation triggers: Combining access + behaviour + data movement into threat scores that surface genuine risk.
Moving From Detection to Verification
The challenge isn’t alerting: it’s acting. Most SIEMs generate alerts that get ignored because teams can’t verify whether the behaviour is actually malicious or just unusual. When our UnderDefence MAXI platform correlates identity signals from Okta or Azure AD with endpoint behaviour from CrowdStrike or SentinelOne and data access from core banking systems, we get the cross-system visibility that catches insider threats before data leaves the organisation. When UEBA flags suspicious behaviour, our analysts verify directly with the employee’s manager rather than generating another unactionable alert.
“They literally took care of all our problems. Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled.”
— Arlin O., CIO, Enterprise | G2 Verified Review
The difference between detection and prevention is human follow-through. An alert that says “suspicious access detected” creates work. A verified incident with context: “John accessed 47 customer accounts outside his portfolio at 11 PM, manager confirmed this was unauthorised”: enables immediate action.
Q6: How Does Managed SIEM Secure Hybrid Cloud Environments in Financial Services?
Financial institutions running hybrid cloud environments face a visibility fragmentation problem that’s fundamentally architectural. On-premise core banking systems generate different logs than AWS payment workloads or Azure identity infrastructure. When threats traverse these boundaries, and they do: you need unified detection, not three separate tools with three separate alert queues.
The Multi-Cloud Complexity Challenge
Most financial institutions don’t choose hybrid: they inherit it. Legacy core banking stays on-prem because migration risk exceeds benefit. New payment services deploy to AWS for scalability. Identity federates through Azure AD. Each environment has its own security tooling, its own log formats, and its own blind spots. Attackers exploit these seams.
Cloud-specific threats require cloud-specific detection: misconfigured S3 buckets exposing cardholder data, compromised IAM credentials enabling lateral movement, container escapes, and serverless function abuse. Traditional network-based detection doesn’t see any of this.
Essential Cloud Security Capabilities
✅ Cloud Security Posture Management (CSPM) integration: Continuous misconfiguration detection across AWS, Azure, GCP
✅ Multi-cloud log aggregation: AWS CloudTrail, Azure Monitor, GCP Cloud Audit Logs normalised into consistent formats
✅ Container and Kubernetes monitoring: Visibility into microservices architectures that traditional agents can’t cover
✅ Identity federation monitoring: Correlation across cloud and on-premise directories to detect credential abuse
✅ Cloud-native threat detection: Rules for cryptomining, data exfiltration via cloud storage and lateral movement between VPCs
Where Traditional Approaches Break Down
The fundamental challenge is that hybrid cloud compliance requires consistent evidence across inconsistent environments. As one security architect noted about traditional approaches: “The setup and configuration of the product is terrible. Everything is a very manual process and the documentation is horrible… They also do not have very many integrations and when they do, it is again a very manual process to set up.”
UnderDefence MAXI provides unified visibility across hybrid environments through native integrations with AWS, Azure, and GCP security services alongside your on-premise infrastructure. Our analysts understand both cloud-native attack patterns and traditional financial services threats, so whether the compromise starts with a phishing email hitting your Exchange server or a misconfigured Lambda function, detection and response happen in one platform with one team. No handoffs, no “that’s the other vendor’s problem.”
Q7: Managed SIEM vs. In-House SIEM: What’s the ROI for Financial Services?
The build vs. buy decision for SIEM determines whether you’re building a security operations centre or partnering with one. Pick wrong, and you either burn $2M+ annually on a team that can’t retain talent, or you outsource to a provider who doesn’t understand financial services threats and compliance requirements.
⚠️ The Wrong Way to Decide
Most security leaders choose based on control preference (“We want everything in-house”) or cost minimisation (“Managed is cheaper”). This ignores the critical question: Can your organisation sustain 24/7 operations with 5-7 skilled analysts while maintaining compliance expertise across PCI-DSS, SOX, and GLBA?
According to recent industry analyses, running a fully functional in-house SOC costs between $1 million and $4 million annually, with Ponemon Institute research suggesting an average of around $2.84 million. For organisations under $500M in revenue, that’s an unsustainable percentage of the IT budget.
💰 Quantified Cost Comparison
| Cost Category | In-House SIEM | Managed SIEM (UnderDefense) |
| SIEM platform licensing | $150K-$500K/year | Included |
| Security analysts (5x for 24/7) | $900K-$1.2M/year | Included |
| Detection engineering/tuning | $150K/year | Included |
| Compliance specialist | $120K/year | Included |
| Infrastructure/maintenance | $75K/year | Included |
| Total Annual TCO | $1.4M-$2M | $132K-$180K* |
*Based on $11-$15/endpoint/month for 1,000 endpoints
That’s an 85-90% cost differential with equivalent or better outcomes.
📋 Evaluation Framework
- 24/7 coverage sustainability: Can you staff nights, weekends, and holidays without burnout?
- Analyst retention: Tier 3-4 analysts average 18-month tenure industry-wide
- Detection engineering capacity: Continuous rule tuning, false positive reduction
- Compliance expertise depth: PCI-DSS, SOX, GLBA specialisation
- Response capability: Threat containment within 30 minutes
- Tool integration breadth: Correlation across 50+ log sources
- Scalability: Coverage expansion without proportional cost increase
“The biggest problem they solved was our 24/7 coverage gap. We needed round-the-clock monitoring for compliance reasons, but building our own SOC wasn’t realistic with our budget and the current hiring market. UnderDefense fills that gap without us having to hire a full team.”
— Verified User, Marketing Agency | G2 Verified Review
The question isn’t whether managed SIEM is cheaper: the math is clear. It’s whether your organisation can match managed SIEM outcomes internally when the analysts you spent 6 months training leave for a 20% raise at a competitor.
Q8: What Integration Capabilities Should a PCI-DSS Compliant SIEM Provide?
PCI-DSS Requirement 10 mandates logging for “all system components,: which in financial services means payment card processing systems, core banking platforms, ATM networks, mobile banking applications, cloud infrastructure, identity systems, and endpoint security. A compliant SIEM must ingest, normalise, and correlate logs across this entire ecosystem without gaps that auditors will flag.
🔗 Critical Integration Categories
- Payment systems: Card processing, POS terminals, payment gateways: the cardholder data environment core
- Core banking platforms: Account management, transaction processing, wire transfer systems (FIS, Jack Henry, Fiserv)
- Identity and access management: Active Directory, Okta, Azure AD, privileged access management tools
- Cloud platforms: AWS, Azure, GCP, workloads processing financial data
- Endpoint security: EDR from CrowdStrike, SentinelOne, Microsoft Defender
- Network infrastructure: Firewalls, VPN concentrators, network detection and response
- SaaS applications: Email security, collaboration tools, customer communication platforms
Integration Depth Requirements
Beyond log collection, an effective SIEM must normalize diverse formats, enrich events with threat intelligence, and correlate across sources. PCI-DSS requires specific log fields: user ID, timestamp, success/failure, affected resource, and the SIEM must extract these consistently regardless of source system format.
The common failure mode isn’t missing integrations: it’s shallow integrations. A connector that pulls logs but doesn’t parse them into actionable fields creates compliance checkbox satisfaction without operational value.
⏰ Common Integration Challenges
- Legacy core banking: Proprietary log formats, limited API access, mainframe extraction complexity
- Hybrid cloud environments: Inconsistent logging across on-prem and cloud workloads
- Third-party payment processors: Limited visibility into partner systems
- Maintenance burden: Keeping 50+ integrations functional as vendors update their APIs
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director of Information Security | G2 Verified Review
The UnderDefense Approach
UnderDefence MAXI provides 250+ pre-built integrations, including specialized connectors for FIS, Jack Henry, Fiserv, and major payment processors. Our 30-day onboarding includes integration configuration and validation: eliminating the 6-month implementation projects that traditional SIEM deployments require. We don’t just connect to your systems; we validate that the data flowing through produces actionable detection, not just log volume.
Q9: How Should Financial Institutions Evaluate Managed SIEM Providers?
Choosing a managed SIEM provider isn’t something you do casually: it’s a security architecture decision that affects compliance, operations, and risk posture for years. The stakes are high, and most vendor evaluation processes fail because they focus on feature checklists rather than operational outcomes.
⏰ The Audit Frame
Score potential managed SIEM providers against these 10 criteria to identify which vendors can deliver genuine compliance and security outcomes for financial services:
✅ Evaluation Checklist
- Do they provide 24/7/365 monitoring with documented response time SLAs? Best-effort promises aren’t acceptable: require specific MTTR commitments with penalty clauses. Financial services regulatory bodies expect continuous monitoring, not business-hours coverage.
- Can they demonstrate PCI-DSS Requirement 10 compliance expertise with pre-built detection rules? Generic detection won’t satisfy QSA audits. Ask for specific financial services use cases and correlation rules addressing cardholder data environment monitoring.
- Do they integrate with your existing security stack without requiring replacement? Vendor lock-in is expensive and risky. Check whether they demand proprietary tool replacement or work with your current investments.
- Is pricing transparent and predictable (per-endpoint/per-user)? Hidden costs destroy budget planning. Request published rates and total cost of ownership calculations, including compliance modules.
- Can they verify suspicious activity directly with users, or do they escalate back to your team? This separates real
- MDR from expensive alert forwarding. Most providers stop at escalation: you need verification capability.
- Do they provide automated compliance reporting for PCI-DSS, SOX, and GLBA? Manual evidence generation burns cycles. Confirm reporting automation covers your specific regulatory frameworks.
- Can they demonstrate financial services client references and case studies? General cybersecurity experience isn’t enough. Banking, insurance, and fintech environments have unique compliance and operational requirements.
- What is their MITRE ATT&CK coverage percentage? Vague security-speak doesn’t cut it. Request documented coverage metrics and detection testing methodology.
- Do they provide threat hunting beyond reactive alerting? Passive monitoring misses sophisticated threats. Confirm proactive threat hunting capabilities and frequency.
- What is their onboarding timeline and implementation approach? Six-month deployments create compliance gaps. Understand their methodology and resource requirements.
📊 Score Interpretation
| Score | Assessment |
| 8-10 ✓ | Enterprise-ready partnership: proceed to contract negotiation |
| 5-7 ✓ | Capability gaps requiring internal resources to fill: consider alternatives |
| 0-4 ✓ | You’re buying an alert feed, not managed detection and response: walk away |
⭐ How UnderDefense Addresses Each Criterion
UnderDefense is purpose-built for financial services security operations:
- Response Time SLAs: 2-minute Alert-to-Triage and 15-minute escalation for critical incidents, documented and guaranteed
- PCI-DSS Expertise: Pre-configured Requirement 10 detection rules plus forever-free compliance kits
- Vendor-Agnostic Integration: 250+ tool integrations: works with your existing stack
- Transparent Pricing: Published $11-15/endpoint/month rates
- ChatOps Verification: Analysts contact users directly via Slack/Teams: we don’t escalate “please investigate” tickets
- Financial Services Experience: Documented case studies across banking and fintech clients
- MITRE Coverage: 96% ATT&CK coverage with observable detection testing
- Implementation Speed: 30-day turnkey deployment, not six-month professional services engagements
“The speed of onboarding was a delight: that’s no surprise. UnderDefense had us up and running in no time. Their 24/7 detection and response service is fast and comprehensive, providing us with a granular, real-time view of our environment.”
— Valeriia D., Marketing Specialist | G2 Verified Review
Next Step
Scored your current provider or shortlist? Request UnderDefense’s financial services security assessment to benchmark against these criteria with documented proof points: we expect you to validate before committing.
Q10: What Does Managed SIEM Implementation Look Like for Financial Services?
Financial services SIEM deployment isn’t like rolling out productivity software. You’re implementing a continuous monitoring infrastructure that directly impacts regulatory compliance, which means you cannot afford coverage gaps during transition. PCI-DSS Requirement 10 mandates continuous logging of cardholder data environment access, and regulators won’t accept “we were migrating” as an explanation for missing audit trails.
📋 Implementation Overview
The typical managed SIEM implementation follows four distinct phases, with financial services-specific considerations at each stage. The goal is speed-to-value without compromising compliance continuity.
Phase 1: Discovery and Integration Planning (Days 1-7)
This phase establishes the foundation for everything that follows:
- Log Source Inventory: Document every system generating security-relevant events: servers, endpoints, network devices, cloud services, identity providers, and applications
- CHD Environment Mapping: Identify cardholder data flows and ensure monitoring covers all PCI-DSS in-scope systems
- Compliance Requirement Documentation: Catalogue specific regulatory mandates (PCI-DSS, SOX, GLBA) and map to detection requirements
- Current State Assessment: Evaluate existing logging gaps, retention policies, and detection blind spots
Phase 2: Integration Deployment (Days 8-21)
The technical implementation phase requires methodical execution:
- Connector Configuration: Deploy log collection agents and API integrations across your security stack
- Log Validation: Verify correct parsing, normalisation, and correlation of ingested events
- Baseline Establishment: Create behavioural baselines for legitimate user and system activity
- Parallel Operation: Maintain existing monitoring during transition to ensure zero coverage gaps
⚠️ Critical Financial Services Consideration
Never do a “hard cutover” from legacy monitoring. Run parallel systems until the new provider demonstrates complete coverage. PCI-DSS auditors will ask about monitoring continuity during transitions: document your dual-running period.
Phase 3: Detection Tuning and Compliance Validation (Days 22-30)
This phase separates enterprise-grade providers from alert factories:
- Custom Rule Configuration: Tune detection logic for your specific environment: legitimate administrative patterns, expected after-hours activity, approved third-party access
- False Positive Reduction: Reduce noise through contextual enrichment and behavioural analysis
- Compliance Report Verification: Validate that automated reporting meets QSA evidence requirements before go-live
- Alert Routing Configuration: Define escalation paths, notification channels, and response workflows
Phase 4: Operational Handoff (Ongoing)
Implementation isn’t complete at go-live: it transitions to continuous optimisation:
- Monthly Detection Reviews: Analyse coverage gaps and emerging threat patterns
- Quarterly Compliance Audits: Pre-stage evidence for regulatory assessments
- Ongoing Tuning: Adapt detection as your environment evolves
❌ Common Pitfalls to Avoid
- Underestimating legacy system complexity: Mainframes, legacy banking platforms, and custom applications often require specialised integration work
- Failing to validate PCI-DSS log content requirements: Requirement 10.3 specifies mandatory log fields: verify these are captured before testing ends
- Big bang deployment instead of phased rollout: Attempting to onboard everything simultaneously creates troubleshooting chaos
- No baseline metrics for improvement measurement: Without pre-implementation benchmarks, you can’t demonstrate ROI
How UnderDefense Approaches Financial Services Implementation
is designed specifically for financial services compliance timelines. We maintain parallel monitoring during transition to ensure zero coverage gaps, validate PCI-DSS Requirement 10 compliance before go-live, and provide a dedicated implementation engineer, not a ticket queue, throughout onboarding.
“UnderDefense delivered the deployment to 1200 endpoints in just 23 business days. They worked closely with us to ensure minimal disruption to our critical operations.”
— Oleksii M., Mid-Market | G2 Verified Review
Q11: How Does UnderDefense’s Managed SIEM Approach Differ From Traditional Providers?
Financial institutions evaluating managed SIEM typically consider three options: traditional MSSPs (Alert Logic, Secureworks), next-gen SIEM platforms (Splunk Cloud, Microsoft Sentinel managed), and MDR providers with SIEM capabilities (Arctic Wolf, CrowdStrike). Each solves part of the problem through fundamentally different architectures: understanding these differences determines whether you’re buying security outcomes or expensive alert forwarding.
❌ Traditional Approach Limitations
Traditional MSSPs provide monitoring without response: you receive alerts, but still need internal resources to investigate and remediate. They operate on rigid playbooks designed for compliance checkboxes rather than real-time threat context.
“We receive alerts, but not necessarily a clear path to resolution… This is not an extension of our security team as was originally sold.”
— Sr Cybersecurity Engineer, Manufacturing | Gartner Verified Review
Pure SIEM platforms require your team to build detection logic, maintain operations, and respond to incidents. You get the technology, but still need a 20-person SOC to operate it effectively.
MDR providers often force proprietary tool replacement, abandoning your existing security investments and creating compliance gaps during migration. Arctic Wolf, for example, requires replacing your current SIEM with their proprietary stack.
✅ UnderDefense’s Differentiated Approach
The AI SOC + Human Ally model combines SIEM aggregation with MDR response capabilities: eliminating the gap between detection and action.
UnderDefence MAXI Platform Architecture: Ingests from your existing stack (250+ integrations) while our analysts provide the investigation, verification, and response that MSSPs don’t offer. We work with CrowdStrike, Splunk, SentinelOne, Microsoft Defender: your current investments are protected, not replaced.
Financial Services-Specific Detection: Pre-configured rules for fraud patterns, insider threat indicators, and PCI-DSS compliance come standard, not as professional services add-ons that inflate costs.
ChatOps User Verification: When behavioural alerts need context: “Did Jane authorise this wire transfer at 2 AM?”: our analysts reach out directly via Slack or Teams. We don’t escalate “please investigate” tickets back to your team.
📊 Provider Comparison Table
| Feature | Traditional MSSP | Pure SIEM | Arctic Wolf MDR | UnderDefense |
| Integration Approach | Limited connectors | Self-managed | Proprietary stack required | 250+ tools supported |
| Response Capability | Alert forwarding | None (DIY) | Escalation-focused | Full containment/remediation |
| User Verification | ❌ None | ❌ None | ❌ Escalates to the customer | ✅ ChatOps direct |
| PCI-DSS Expertise | Generic | Configuration required | Additional services | Pre-built rules included |
| Pricing Transparency | Contact sales | Per-GB (variable) | Contact sales (~$96K median) | Published $11-15/endpoint |
| Onboarding Speed | Months | Months | Requires migration | 30-day turnkey |
| Compliance Automation | Separate product | Configuration required | Separate product | Forever-free kits included |
“Arctic Wolf provides solid detection, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology, Services | Gartner Verified Review
Decision Criteria
Choose traditional MSSP if you have internal SOC resources and just need log aggregation for compliance checkboxes.
Choose pure SIEM if you’re building an in-house security operations centre and want full control over detection engineering.
Choose UnderDefense if you want enterprise-grade security operations with financial services compliance expertise, without the $2M annual cost of building it yourself.
“UnderDefense MAXI helps us secure sensitive data and mitigate potential cyber threats. Their responsiveness and flexibility: no matter the issue, they tackled it quickly and professionally.”
— Arman N., CTO | G2 Verified Review
Q12: What Are the Best Security Solutions for Financial Services Compliance?
The leading security solutions for financial services compliance combine managed detection and response (MDR) with integrated SIEM capabilities, vendor-agnostic integration, and automated compliance reporting: eliminating the gap between security monitoring and regulatory evidence generation.
Quick Context
Financial services security has evolved beyond point solutions. The key differentiators now are integration flexibility (vendor-agnostic vs. proprietary lock-in), response capability (detection-only vs. full containment), compliance automation (manual reporting vs. continuous evidence generation), and pricing transparency (published rates vs. “contact sales”).
Selection Criteria Preview
What separates top financial services security solutions:
- Vendor-agnostic integration supporting existing security investments: not requiring expensive rip-and-replace
- Human analyst access with direct communication (not ticket-based escalation queues)
- Published response time SLAs with documented MTTR metrics
- Transparent per-endpoint pricing enabling accurate budget planning
- PCI-DSS compliance automation included as standard, not add-on professional services
- Financial services client references demonstrating regulatory expertise
The Funnel Bridge
Each solution category excels in different scenarios. The right choice depends on your current security stack, compliance requirements, and operational model. For detailed evaluation across all criteria, including pricing comparisons, deployment timelines, and compliance coverage: see our comprehensive guides below.
This analysis is based on documented response times, G2 reviews, published pricing data, and operational outcomes across 500+ MDR deployments serving financial services organisations.
1. What is managed SIEM for financial services and why do banks need it?
Managed SIEM for financial services is an outsourced security information and event management solution specifically designed to meet banking regulatory requirements like PCI-DSS, SOX, and GLBA.
We built our managed SIEM service because financial institutions face unique challenges:
-
PCI-DSS Requirement 10 mandates continuous logging and daily log reviews
-
Fragmented security stacks create “compliance chaos” with evidence scattered across multiple systems
-
Building an in-house SOC costs $2M+ annually: unsustainable for most organizations
Managed SIEM eliminates these problems by:
-
Correlating events across payment systems, identity infrastructure, and cloud environments
-
Generating compliance evidence automatically as a byproduct of threat detection
-
Providing 24/7 analyst coverage without the hiring and retention burden
With PCI-DSS v4.0 enforcement beginning March 2025, Requirement 10.4.1.1 now mandates automated mechanisms for daily log reviews. Manual spot-checks no longer satisfy auditors.
2. How does managed SIEM help financial institutions comply with PCI-DSS Requirement 10?
We approach PHI threat detection through multi-layer correlation that traditional tools miss. The challenge is that healthcare threats often look legitimate; a compromised nurse credential accessing patient records appears normal without behavioral context.
Our detection methodology includes:
- EHR access pattern analysis: Correlating Epic, Cerner, or Meditech audit logs with identity behavior to identify anomalous PHI access
- Temporal anomaly detection: Flagging after-hours activity, unusual search patterns, or bulk record exports
- IoMT network monitoring: Detecting medical devices communicating with unauthorized external IPs
- Credential compromise indicators: Identifying impossible travel, failed authentication patterns, and privilege escalation attempts
The critical differentiator is response capability. Detection-only SIEM creates alert noise; we provide full incident response with documented 2-minute Alert-to-Triage and 15-minute escalation for critical incidents for critical healthcare incidents. When anomalies require context, our analysts verify directly with affected users via Slack or Teams before escalating, closing the gap that lets breaches progress undetected.
3. What fraud detection capabilities should a financial services SIEM include?
Financial services SIEM must provide multi-layered fraud detection that correlates transaction patterns, user behavior, and system access to identify threats before financial impact occurs.
We detect fraud through cross-system correlation that single-point solutions miss:
-
Account Takeover: Impossible travel + credential change + wire transfer patterns
-
Payment Fraud: Transaction deviation + after-hours activity + new payee combinations
-
Insider Threat: Privilege escalation + bulk export + off-scope account access
-
Money Laundering: Structuring patterns + rapid multi-account movement
The correlation is what catches sophisticated fraud. A single anomalous login might be nothing. That same login followed by a credential change and wire transfer request within 30 minutes: that’s the pattern your SIEM should catch.
What separates effective fraud detection from alert noise is verification capability. When our threat detection flags suspicious patterns, our analysts verify directly with affected users via Slack or Teams before escalating: reducing false positives by 99% while ensuring real fraud gets immediate response.
4. How much does managed SIEM cost compared to building an in-house SOC?
The cost differential between managed SIEM and in-house SOC is dramatic: 85-90% savings with equivalent or better outcomes.
Running a fully functional in-house SOC costs between $1 million and $4 million annually. Here’s the breakdown:
| Cost Category | In-House | Managed SIEM |
|---|---|---|
| SIEM licensing | $150K-$500K/year | Included |
| Security analysts (5x for 24/7) | $900K-$1.2M/year | Included |
| Detection engineering | $150K/year | Included |
| Compliance specialist | $120K/year | Included |
| Total Annual TCO | $1.4M-$2M | $132K-$180K |
Based on $11-15/endpoint/month for 1,000 endpoints
The hidden cost most organizations miss is analyst retention. Tier 3-4 analysts average 18-month tenure industry-wide. The question isn’t whether managed SIEM is cheaper: the math is clear. It’s whether your organization can match outcomes internally when trained analysts leave for a 20% raise at competitors.
5. How long does managed SIEM implementation take for financial services?lthcare SOC?
Financial services SIEM implementation should complete in 30 days or less while maintaining zero compliance coverage gaps during transition.
Our implementation follows four phases:
Phase 1: Discovery (Days 1-7)
-
Log source inventory and CHD environment mapping
-
Compliance requirement documentation
-
Current state gap assessment
Phase 2: Integration (Days 8-21)
-
Connector deployment across your security stack
-
Log validation and baseline establishment
-
Parallel operation with existing monitoring
Phase 3: Tuning (Days 22-30)
-
Custom rule configuration for your environment
-
False positive reduction
-
Compliance report verification before go-live
Phase 4: Ongoing
-
Monthly detection reviews and quarterly compliance audits
Critical consideration: never do a “hard cutover” from legacy monitoring. PCI-DSS auditors will ask about monitoring continuity during transitions. Our financial services MDR maintains parallel monitoring until complete coverage is validated.
Reasoning: Implementation timeline is a practical concern for buyers facing compliance deadlines. This FAQ sets expectations and highlights the parallel-monitoring approach that prevents compliance gaps.
FAQ 6
Question: How does managed SIEM detect insider threats in financial institutions?
Answer: Insider threats cost financial services organizations over $20 million annually to resolve: the highest of any industry. We detect insider threats through User and Entity Behavior Analytics (UEBA) that establishes behavioral baselines and flags deviations.
Key detection mechanisms include:
-
Behavioral baseline comparison: Detecting when employees access customer records at 2 AM when they’ve never worked nights
-
Privilege escalation monitoring: Unauthorized permission changes or access to systems outside job scope
-
Data exfiltration signals: Bulk exports, unusual file transfers, creation of forwarding rules
-
Access anomalies: Geographic impossibilities or accessing accounts outside assigned portfolio
-
Correlation triggers: Combining access + behavior + data movement into threat scores
According to the 2024 LevelBlue Risk Radar Report, 40% of financial institutions reported increased insider attacks, with average breach costs at $5 million.
The challenge isn’t alerting: it’s acting. When UEBA flags suspicious behavior, our analysts verify directly with the employee’s manager rather than generating another unactionable alert. Our SOC team provides the human follow-through that turns detection into prevention.
6. How does managed SIEM integrate with Epic, Cerner, and other EHR systems? Answer:
Healthcare SIEM effectiveness depends on visibility of where ePHI actually lives. Without ingesting EHR audit logs, threat detection operates blindly to clinical workflows that distinguish legitimate access from breaches.
We integrate with major EHR platforms through API-based log collection:
- Epic: Chronicles audit logs capturing user access, chart modifications, and PHI export events
- Cerner (Oracle Health): Millennium audit events with OAuth 2.0 authentication and comprehensive event tracking
- Meditech: User activity tracking across clinical modules
- athenahealth: Cloud-based audit trails via API integration
Critical EHR events we monitor include:
- Access patterns (chart access outside care relationships, bulk record exports)
- Temporal anomalies (after-hours activity, unusual search patterns)
- Privilege changes (escalation requests, role modifications)
- PHI operations (copy/print events, external transfers)
The difference between generic SIEM and healthcare-ready SIEM is understanding that Dr. Smith accessing 200 patient records during morning rounds is normal, but the billing clerk accessing those same records at midnight is a breach in progress.
7.What integrations should a PCI-DSS compliant SIEM provide?
PCI-DSS Requirement 10 mandates logging for “all system components”: which in financial services means comprehensive integration across your entire technology ecosystem.
Critical integration categories include:
-
Payment systems: Card processing, POS terminals, payment gateways
-
Core banking platforms: FIS, Jack Henry, Fiserv, wire transfer systems
-
Identity management: Active Directory, Okta, Azure AD, PAM tools
-
Cloud platforms: AWS, Azure, GCP workloads processing financial data
-
Endpoint security: CrowdStrike, SentinelOne, Microsoft Defender
-
Network infrastructure: Firewalls, VPN concentrators, NDR
The common failure mode isn’t missing integrations: it’s shallow integrations. A connector that pulls logs but doesn’t parse them into actionable fields creates compliance checkbox satisfaction without operational value.
We provide 250+ pre-built integrations including specialized connectors for major payment processors. Our 30-day onboarding includes integration configuration and validation: we don’t just connect to your systems; we validate that the data flowing through produces actionable detection, not just log volume.
8. How does UnderDefense's managed SIEM differ from Arctic Wolf and traditional MSSPs?
Financial institutions typically consider three options: traditional MSSPs, pure SIEM platforms, and MDR providers with SIEM capabilities. Each solves part of the problem through fundamentally different architectures.
Traditional MSSPs provide monitoring without response. You receive alerts but still need internal resources to investigate and remediate.
Pure SIEM platforms require your team to build detection logic, maintain operations, and respond to incidents. You get technology but need a 20-person SOC to operate it.
Arctic Wolf and similar MDR providers often force proprietary tool replacement, abandoning your existing security investments and creating compliance gaps during migration.
Our differentiated approach:
| Feature | Arctic Wolf | UnderDefense |
|---|---|---|
| Integration | Proprietary stack required | 250+ tools supported |
| User Verification | Escalates to customer | ChatOps direct |
| Pricing | ~$96K median (contact sales) | Published $11-15/endpoint |
| Onboarding | Requires migration | 30 days turnkey |
We work with CrowdStrike, Splunk, SentinelOne, Microsoft Defender: your current investments are protected, not replaced. Learn more about our vendor-agnostic MDR approach.
The post Managed SIEM for Financial Services: PCI-DSS Compliance Solutions appeared first on UnderDefense.