Q1. What Is an AI SOC for Healthcare, and Why Has It Become a Clinical Necessity?
An AI SOC for healthcare is a security operations center powered by artificial intelligence that continuously monitors EHRs, patient portals, IoMT devices, and clinical endpoints to detect ransomware and cyber threats in real time, while automating HIPAA compliance evidence collection and reporting.
That definition sounds clean. The reality inside most hospitals is anything but.
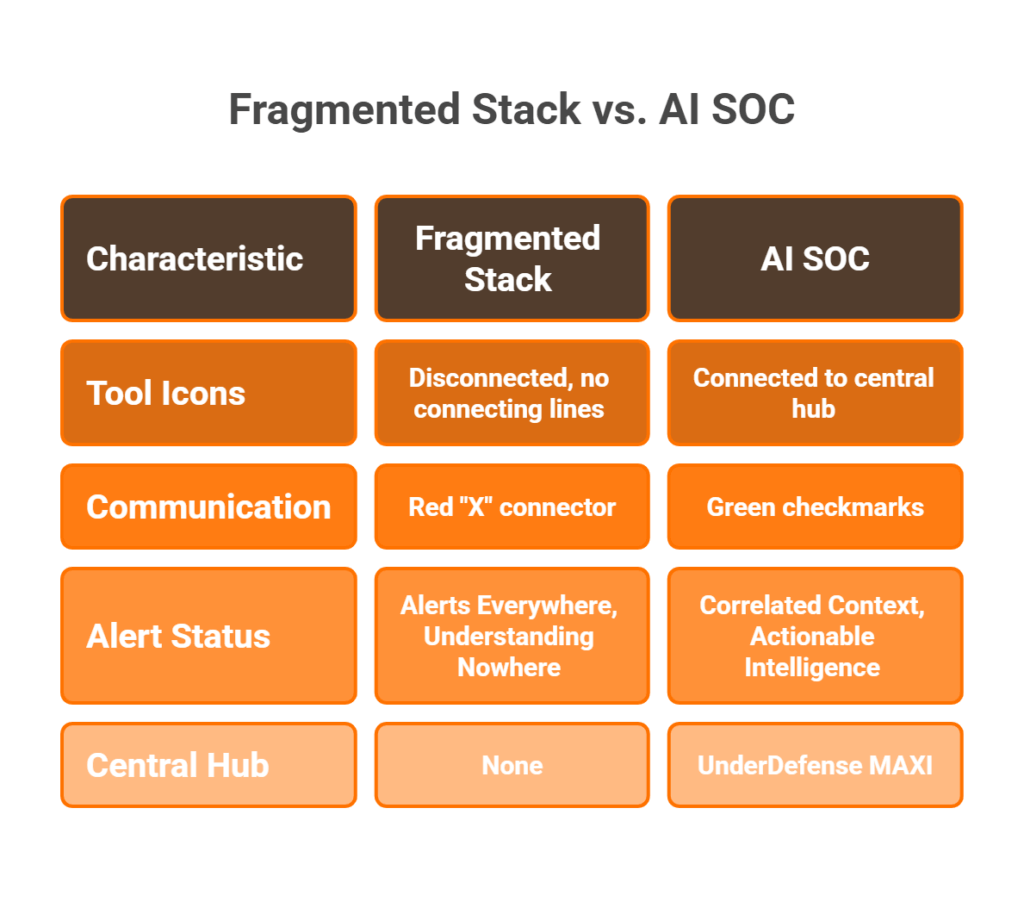
The Fragmented Security Reality in Healthcare
Here’s what I see in almost every healthcare engagement: CrowdStrike on endpoints, Splunk ingesting logs from a dozen sources, a separate EHR audit tool nobody looks at, and HIPAA compliance tracked in spreadsheets that get updated quarterly, if someone remembers. Alerts everywhere, understanding nowhere. A night-shift nurse accessing 50 patient records looks the same as an attacker performing reconnaissance, because no single tool has enough context to tell the difference.
The operational cost of this fragmentation isn’t abstract but measured in missed detections, delayed incident response, and disrupted patient care. When your EDR doesn’t talk to your identity provider, and your SIEM can’t correlate EHR access patterns with endpoint behavior, you’re flying blind in a sector where downtime puts lives at risk.
The “Black-Box Escalation” Trap
Traditional MDR providers and legacy MSSPs make this worse, not better. Arctic Wolf flags suspicious EHR access patterns and sends an escalation ticket: “Please investigate.” CrowdStrike Falcon Complete isolates the endpoint but has zero clinical context about whether that access pattern is a radiologist on call or an attacker moving laterally. Legacy MSSPs offer checkbox HIPAA monitoring with rigid playbooks that can’t distinguish between a nurse pulling records at 3 AM during a code blue and a compromised account exfiltrating PHI.
“We received little value from ArcticWolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
The pattern is consistent: detection without clinical context, escalation without action, monitoring without outcomes.
The AI SOC + Human Ally Model
Detection without response in healthcare isn’t just noise but a patient safety risk. The competitive advantage today isn’t having more security tools. It’s having a system that reasons across EHR logs, identity events, endpoint behavior, IoMT traffic, and HIPAA compliance requirements simultaneously, and then acts on those conclusions.
That’s the architectural shift behind the AI SOC + Human Ally model. AI handles the scale problem: correlating millions of events across disparate tools in real time. Humans handle the judgment problem: verifying whether Dr. Smith really authorized that remote session at 3 AM, deciding whether to isolate a medical device mid-procedure, and communicating remediation steps to clinical staff who don’t speak “security.”
How UnderDefense Delivers This for Healthcare
We built the UnderDefense MAXI platform around this exact architecture:
- Unified telemetry connecting EHR systems, endpoints, cloud workloads, identity providers, and IoMT devices, across 250+ vendor integrations
- Vendor-agnostic detection that works with your existing stack, not against it, with no rip-and-replace
- 24/7 proactive threat hunting with 96% MITRE ATT&CK technique coverage
- Concierge analyst response where our team verifies suspicious EHR access directly with clinical staff via Slack or Teams, resolving alerts without burdening hospital IT
- Automated HIPAA compliance evidence collection included at no extra cost, not bolted on as an upsell
“UnderDefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO UnderDefense G2 – Verified Review
The Proof Point
When a leading German healthcare organization needed to unify fragmented security across clinical systems, legacy devices, and cloud infrastructure, we deployed UnderDefense MAXI and had 24/7 coverage operational within weeks, not months. The result: consolidated visibility, faster detection, and HIPAA-grade compliance reporting from day one.
Stop renting alert dashboards that don’t understand HIPAA. Start hiring an AI SOC with a dedicated healthcare security ally.
Q2. Why Are Hospitals and Clinics the #1 Ransomware Target, and What Makes Healthcare So Vulnerable?
Healthcare is the most-targeted sector for ransomware globally, and the threat landscape in 2025 set new records across nearly every metric. Understanding why requires looking at both the numbers and the structural vulnerabilities that make this sector uniquely exposed.
The 2025–2026 Ransomware Landscape: Hard Numbers
| Metric | Value | Source |
|---|---|---|
| Ransomware attacks on healthcare providers (2025) | 445 | Comparitech, Jan 2026 |
| Additional attacks on healthcare businesses | 191 | Comparitech, Jan 2026 |
| Global YoY increase in ransomware attacks | 49% | HIPAA Journal, Feb 2026 |
| Healthcare sector ranking by attack volume | #1 most targeted | HIPAA Journal, Feb 2026 |
| Health-ISAC cyber incident surge (2025) | 55% increase | Health-ISAC, Feb 2026 |
| Average healthcare breach cost (2025) | $7.42 million | IBM Cost of a Data Breach Report 2025 |
| Healthcare’s rank for breach cost by industry | #1 (since 2011) | IBM/Ponemon |
⚠️ The Change Healthcare Breach: A Defining Cautionary Case
In February 2024, the ransomware attack on Change Healthcare became the single most consequential cyberattack in U.S. healthcare history. The numbers: 192.7 million individuals affected, $3.09 billion in estimated total cost, and a $22 million ransom payment.
The 6 Vulnerability Factors That Make Healthcare Uniquely Exposed
- 24/7 uptime pressure — Hospitals can’t “go offline” to patch. Healthcare organizations experience an average of 17 days of downtime per ransomware incident, with each day costing approximately $1.9 million.
- Massive attack surface — EHR platforms (Epic, Cerner/Oracle Health), patient portals, IoMT devices, reception kiosks, and telehealth endpoints each serve as an entry point.
- Legacy systems that can’t be patched — Clinical devices running outdated operating systems remain in production because replacing a $500K MRI machine isn’t a quarterly budget item.
- PHI dark web value — Healthcare records sell for 10–40x more than credit card numbers because they contain identity, insurance, and medical data that enables long-term fraud.
- Staffing shortages — The U.S. faces a shortage of nearly 265,000 cybersecurity professionals, with only 83% of available positions filled.
- Compliance resource drain — HIPAA audit preparation diverts security teams from active defense.
⏰ Cost-of-Inaction: What Reactive Security Actually Costs
| Impact Category | Data Point |
|---|---|
| Average ransomware downtime (healthcare) | 17 days per incident |
| Daily cost of downtime | $1.9 million |
| Average ransom demand (healthcare, 2025) | $615,000 |
| HIPAA penalty range | $100–$50,000 per violation; up to $1.5M per category/year |
| Average breach cost (healthcare, 2025) | $7.42 million |
| Total downtime losses (2018–2024) | $21.9 billion |
How UnderDefense Addresses This Landscape
We address this threat landscape through 24/7 AI-driven monitoring across the full healthcare attack surface, with automated HIPAA evidence collection built into the platform. Across 500+ MDR clients, including healthcare organizations facing these exact threats, we maintain a 100% ransomware prevention record. At $11–15 per endpoint per month, it’s a fraction of a single day’s downtime cost.
Q3. How Does an AI SOC Detect and Disrupt Healthcare Ransomware Across the Kill Chain?
Modern healthcare ransomware doesn’t start with encryption. It starts with a phishing email to a billing clerk, moves through credential harvesting, lateral movement, privilege escalation, and data exfiltration, often over days or weeks, before a single file gets encrypted. An AI SOC’s value lies in detecting and disrupting each stage before the damage becomes irreversible.
The Healthcare Ransomware Kill Chain
Standalone EDR might catch Stage 1 (the initial phishing payload) and Stage 5 (ransomware execution). But Stages 2–4, where the attacker quietly harvests credentials, moves laterally through clinical networks, and escalates privileges to access EHR systems, happen in the gaps between tools. That’s where most healthcare breaches actually succeed.
5-Stage Kill Chain with AI SOC Interventions
| Stage | Attack Activity | MITRE ATT&CK Tactics | AI SOC Intervention |
|---|---|---|---|
| 1. Initial Access | Phishing email to reception/clinical staff | Initial Access (T1566) | Detects anomalous email patterns, sandboxes attachments, and blocks malicious URLs |
| 2. Credential Harvest | Stolen creds via phishing; portal credential stuffing | Credential Access (T1110, T1556) | UEBA flags impossible travel, unusual auth patterns, and failed login spikes |
| 3. Lateral Movement | Reception endpoint → AD → EHR network segment | Lateral Movement (T1021, T1570) | Correlates cross-tool signals (endpoint + identity + network) |
| 4. Privilege Escalation | Admin access to EHR; bulk record queries | Privilege Escalation (T1078, T1068) | Detects abnormal privilege changes, bulk PHI access, and after-hours queries |
| 5. Exfiltration & Encryption | PHI exfil to external C2; ransomware deploy | Exfiltration (T1041), Impact (T1486) | Automated containment: endpoint isolation, credential revocation, and network segmentation |
Why Traditional Tools Miss Stages 2–4
- EDR alone sees the endpoint but has no identity context. It can’t distinguish a legitimate admin session from a compromised credential moving laterally.
- SIEM alone sees the logs but can’t respond. The alert sits in a queue while the attacker escalates privileges.
- Legacy MSSPs detect patterns but escalate back to hospital IT with “please investigate” tickets.
“Lack of true remediation in the response, costing us significantly in resources and introducing risks in security.”
— VP of Technology Arctic Wolf – Gartner Verified Review
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated.”
— CISO, Manufacturing Arctic Wolf – Gartner Verified Review
How UnderDefense Covers the Full Kill Chain
Our UnderDefense MAXI platform correlates signals across all five stages simultaneously. When suspicious activity emerges at Stage 3 or 4, where other tools go blind, our concierge analysts don’t just escalate. They verify directly with clinical staff: “Dr. Smith, did you authorize this remote session at 3 AM?”
The documented results: 0.5-hour median time to respond (MTTR) and detection that runs 2 days faster than comparable endpoint-only solutions. That speed difference is the difference between catching an attacker at credential harvest versus discovering encrypted EHR databases on Monday morning.
Q4. How Does an AI SOC Monitor and Protect EHRs and IoMT Medical Devices in Real Time?
Two asset classes define healthcare’s unique security challenge: Electronic Health Records (EHRs) that contain the most sensitive patient data, and Internet of Medical Things (IoMT) devices that are physically connected to patients but invisible to traditional security tools. An AI SOC for healthcare must cover both, because attackers target both.
✅ Capability: Unified EHR + IoMT Monitoring
An AI SOC continuously monitors EHR platforms (Epic, Cerner/Oracle Health, Meditech) at the behavioral level and IoMT medical devices (infusion pumps, imaging systems, and patient monitors) via agentless network traffic analysis, detecting threats that native audit logs and standalone EDR cannot correlate.
Native EHR audit logs generate thousands of events daily. Without threat context, those events are noise. IoMT devices can’t run endpoint agents because they’re embedded systems with proprietary firmware. Traditional EDR literally doesn’t see them.
EHR Monitoring: 5 Detection Use Cases
- Bulk record access detection — Flagging when a user queries 500+ records versus the normal 20–30. This is how PHI exfiltration begins, disguised as clinical workflow.
- After-hours PHI access correlation — Cross-referencing user shift schedules with EHR access timestamps.
- Abnormal HL7/FHIR API traffic — Monitoring integration interfaces for data exfiltration disguised as interoperability traffic.
- Privilege escalation detection — A billing account suddenly accessing clinical records triggers immediate investigation.
- Cross-referencing EHR + endpoint behavior — Suspicious EHR login concurrent with PowerShell execution on the same workstation.
🔍 IoMT Device Monitoring: 5 Critical Capabilities
- Network behavioral analysis — Establishing baseline communication patterns for every medical device, then detecting deviations.
- Baseline traffic profiling — Mapping normal DICOM traffic patterns for imaging systems and HL7 communication for patient monitors.
- Network segmentation validation — Continuously verifying IoMT devices remain isolated in designated VLANs.
- Firmware vulnerability correlation — Mapping device inventory against known CVEs in real time.
- Medical protocol anomaly detection — Flagging irregularities in DICOM and HL7 protocol traffic that could indicate data manipulation or command injection.
💡 Why This Matters + How UnderDefense Delivers
Our UnderDefense MAXI platform ingests EHR audit logs and IoMT network telemetry alongside 250+ other data sources, correlating signals no single tool can see. When ambiguous EHR access emerges, our concierge analysts verify directly with the clinician: “Dr. Chen, did you access 340 Radiology records at 11:47 PM?”
“Their SOC team is responsive and knows their stuff. When they escalate something, they include the context we need to understand the issue quickly. We’re not wasting time piecing together what happened from different systems anymore.”
— Verified User in Marketing and Advertising UnderDefense G2 – Verified Review
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense G2 – Verified Review
That’s the difference between an alert dashboard and an AI SOC with a human ally: clinical context that closes alerts without burdening hospital IT, protecting both patient data and care delivery.
Q5. Can an AI SOC Defend Patient Portals and Reception Desks, Healthcare’s Most Overlooked Attack Surface?
The Monday Morning Nobody Talks About
Monday morning at a 200-bed regional hospital. A front-desk receptionist clicks a phishing link disguised as a scheduling system update. Within 90 minutes, the attacker harvests credentials, moves laterally to the clinical network, and queries the EHR. Meanwhile, 47 patients use the portal to check lab results. Three accounts were compromised last week via credential stuffing from a third-party breach, but nobody noticed because portal security logs aren’t monitored.
This isn’t hypothetical. Health-ISAC logged 585 health-sector cyber incidents in 2025 alone, a 21% year-over-year increase, with disruptions to hospital operations, scheduling, and unauthorized exposure of patient health information topping the impact list. Reception desks and patient portals sit at the dead center of these incidents, yet they’re the last things most security programs cover.
Why Reception and Portal Security Falls Through the Cracks
Reception desks and patient portals occupy a uniquely dangerous position: they sit at the intersection of public-facing access and internal network connectivity. Reception PCs handle scheduling, insurance verification, and EHR lookups, but they’re operated by non-technical staff who are prime phishing targets. Patient portals expose authentication endpoints and APIs to the open internet, handling sensitive PHI around the clock.
Here’s the operational reality: neither is typically covered by EDR agents or legacy MSSP playbooks focused on server-side alerts. Most MDR providers monitor what’s behind the firewall. They don’t watch what’s walking through the front door.
The Hidden Cost of Ignoring the Perimeter
The numbers behind these blind spots are brutal:
⚠️ Phishing as initial access: Over 80% of ransomware incidents begin with phishing targeting non-technical staff. Receptionists, billing clerks, and scheduling coordinators are the #1 entry point.
💸 Breach notification cascade: A single compromised patient portal account triggers mandatory HIPAA breach notification for every affected individual. Three undetected accounts become three notification events and three potential OCR inquiries.
⏰ Credential stuffing dwell time: Credential stuffing attacks against portals go undetected for months, quietly accumulating compromised accounts while security teams chase server-side alerts.
❌ Kiosk firmware gaps: Check-in kiosks running outdated firmware with flat network access become prime footholds, and most organizations don’t even inventory them in their asset management systems.
How an AI SOC Closes the Front Door
This is exactly the kind of gap where an AI SOC earns its keep. At UnderDefense, our UnderDefense MAXI platform monitors the full healthcare perimeter, not just the server room. That means patient portal auth logs (credential stuffing patterns, session anomalies, and API abuse), reception endpoint behavior (phishing click detection, lateral movement from non-clinical subnets), and check-in kiosk integrity monitoring.
When a receptionist clicks a suspicious link, the concierge analyst doesn’t just flag an alert. They verify directly via Teams or Slack: “Sarah, did you download this file at 9:14 AM?” If malicious, the endpoint is isolated before lateral movement begins, typically within minutes, not weeks.
The Contrast That Matters
The difference is stark: from “ransomware entered through reception and nobody noticed for 3 weeks” to “phishing detected, user verified, endpoint isolated in under 10 minutes.”
Traditional MDR providers don’t cover this surface because they’re focused on what their proprietary tools can see: servers, endpoints with agents, and cloud workloads. They miss the operational perimeter where healthcare actually gets breached. An AI SOC that integrates with your existing stack, monitors portal authentication in real time, and can talk directly to the affected user? That’s how you defend the attack surface nobody else is watching.
Q6. Why Do Alert Fatigue and Healthcare Workforce Shortages Make an AI SOC Essential, Not Optional?
Healthcare security teams are drowning, not because threats are too sophisticated, but because humans can’t scale to process the volume. The average hospital generates thousands of daily security alerts with a team of two or three analysts. AI SOC automation isn’t a luxury. It’s the only viable staffing model that actually works in healthcare’s operational reality.
The Numbers Behind the Breaking Point
The data paints a clear picture of a system that’s fundamentally unsustainable:
⚠️ Workforce crisis at scale: The global cybersecurity workforce gap has reached 4.8 million unfilled positions, with 59% of security teams reporting critical skills shortages. In the U.S. alone, over 450,000 cybersecurity roles remain open, and 55% of health systems plan to increase cybersecurity staffing, yet lack the talent pipelines to meet those goals.
❌ Alert volume exploding: 77% of organizations saw increased alert volume in 2025, with 46% experiencing a spike of 25% or more in a single year. Security teams aren’t falling behind. They’re being buried alive under noise that masks real threats.
💸 Analyst burnout and turnover: SOC analysts average just 18 months of tenure before burnout-driven turnover. Healthcare organizations face 30%+ annual turnover in security roles, meaning by the time an analyst understands your clinical workflows, EHR integrations, and compliance requirements, they’re already job-hunting.
⏰ Detection lag compounds cost: Without AI automation, healthcare mean time to detect (MTTD) stretches to 200+ days. That means threats dwell in your environment for over six months before anyone notices, and every extra day expands the blast radius of compromised PHI.
❌ Coverage gaps after hours: Only a fraction of healthcare organizations maintain true 24/7 security monitoring. The rest rely on business-hours-only coverage with after-hours alert queuing, meaning attacks launched at 2 AM sit unreviewed until morning, giving attackers an eight-hour head start.
Why Traditional Hiring Can’t Solve This
The math simply doesn’t work. Even if you find qualified candidates, which is increasingly unlikely given a 4.8-million-person global shortage, you’re competing with tech giants and financial services firms offering significantly higher compensation. A mid-market hospital in Ohio isn’t outbidding Goldman Sachs for Tier 3 SOC analysts. And once you do hire, the 18-month burnout clock starts ticking immediately. You spend six months onboarding, get twelve months of productive work, and then start the cycle again.
This isn’t a problem you can train your way out of. It’s an architectural constraint that requires a fundamentally different operating model.
How an AI SOC Breaks the Staffing Equation
UnderDefense eliminates the staffing equation entirely. We provide 24/7/365 AI-driven monitoring with dedicated Tier 3–4 concierge analysts, delivering enterprise SOC coverage without requiring healthcare organizations to hire, train, and retain a full security team. Our UnderDefense MAXI platform reduces customer-facing alerts by up to 99% through custom detection tuning, because your three-person IT team should review confirmed incidents, not triage 10,000 daily maybes.
The operational math is simple: you can spend 18 months hiring an analyst who leaves in 18 months, or you can deploy an AI SOC with human allies who already know the healthcare threat landscape and are monitoring your environment tonight. As one CISO I work with put it, you don’t need more analysts. You need fewer alerts that actually matter, and experts who already know how to act on them.
Q7. How Does an AI SOC Automate HIPAA Compliance, and Which Specific Safeguards Does It Cover?
Most healthcare organizations I talk to have two separate worlds: the security tools that protect their environment and the compliance spreadsheets that document it. These worlds rarely talk to each other, and that gap is where audit failures live. An AI SOC closes it by generating compliance evidence as a byproduct of continuous monitoring, not as a bolt-on afterthought.
HIPAA Safeguard ↔ AI SOC Capability Matrix
| HIPAA Section | Safeguard Category | AI SOC Automated Capability |
|---|---|---|
| §164.308(a)(1) | Administrative, Risk Analysis | Continuous risk assessment via real-time threat detection and vulnerability correlation |
| §164.308(a)(3) | Administrative, Workforce Security | Automated workforce access monitoring, anomalous user behavior detection |
| §164.308(a)(6) | Administrative, Incident Response | Automated incident detection, investigation logging, and response documentation |
| §164.310(a) | Physical, Facility Access | Facility access monitoring via badge/endpoint correlation and kiosk integrity checks |
| §164.312(a) | Technical, Access Control | Continuous access control monitoring, unauthorized access alerting |
| §164.312(b) | Technical, Audit Controls | Automated audit log collection, correlation, and retention across all monitored systems |
| §164.312(e) | Technical, Transmission Security | Monitoring of transmission security including HL7/FHIR interface integrity |
| §164.314(a) | Organizational, BAA Compliance | Continuous vendor risk monitoring and BAA compliance status tracking |
The Compliance Automation Self-Assessment
Score your organization honestly against these seven checkpoints:
- ☐ Does your security monitoring automatically generate audit-ready evidence for §164.312 access controls?
- ☐ Are EHR access logs continuously correlated with user behavior for §164.308(a)(1) risk analysis?
- ☐ Does the system document incident detection, investigation, and response for breach notification under §164.408?
- ☐ Can you produce a complete audit trail within hours, not weeks, when OCR arrives?
- ☐ Is compliance evidence generated as a byproduct of monitoring, or maintained in separate spreadsheets?
- ☐ Does the system monitor transmission security (§164.312(e)), including HL7/FHIR interfaces?
- ☐ Are Business Associate Agreement compliance statuses tracked continuously?
What Your Score Means
✅ 6–7 checks: Mature compliance automation. Your security and compliance systems are integrated and audit-ready.
⚠️ 3–5 checks: Significant manual gaps. You’re likely maintaining parallel systems that drift out of sync between audits.
❌ 0–2 checks: Unsustainable, spreadsheet-driven compliance. One OCR audit could expose critical documentation gaps that trigger enforcement action.
Most healthcare organizations I work with score 2–3 on their first assessment. The root cause is always the same: security tools and compliance tools are completely separate systems, maintained by different people, on different schedules, with no shared data pipeline.
How UnderDefense Closes the Gap
UnderDefense MAXI generates HIPAA compliance evidence as an automatic byproduct of 24/7 monitoring, not a separate product you bolt on. Access logs, incident documentation, risk assessment data, and audit trails are all continuously produced and audit-ready from day one. We include forever-free compliance kits with our MDR service, so there’s no separate compliance tool purchase required. Most healthcare clients go from 2–3 checks to 7/7 within 30 days of deployment, because when monitoring and compliance share the same data pipeline, the spreadsheets disappear.
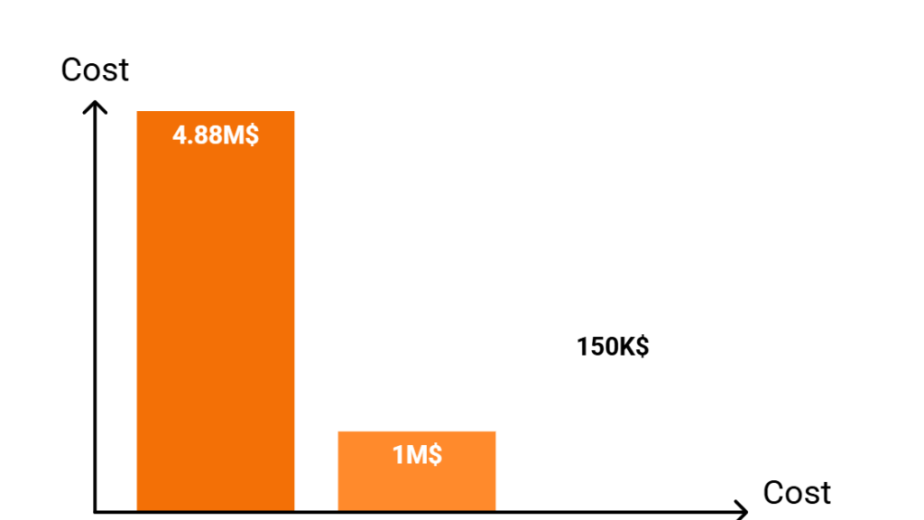
Q8. What Is the Real ROI of an AI SOC for Healthcare, and How Do You Calculate It?
“Better security” isn’t a line item a CFO can approve. Healthcare organizations need to quantify AI SOC return across five measurable categories, not in abstract risk-reduction language, but in documented financial impact that maps directly to the budget conversation.
The 5-Category Healthcare AI SOC ROI Framework
1. Ransomware Downtime Prevention 💸
Ransomware downtime costs U.S. healthcare organizations an average of $1.9 million per day, with typical incidents forcing 17+ days of operational disruption. Across 2018–2024, providers suffered over $21.9 billion in collective downtime losses. An AI SOC with a 0.5-hour MTTR for critical incidents prevents the multi-week outages that drive these numbers into the tens of millions per incident.
2. HIPAA Fine Avoidance ⚠️
OCR penalty tiers for 2025 range from $145 per violation (Tier 1, lack of knowledge) up to $2,190,294 per violation for willful neglect not corrected (Tier 4). Annual penalty caps reach $2,190,294 per identical provision. Continuous compliance monitoring prevents the documentation gaps and undetected breaches that trigger the highest enforcement tiers.
3. Breach Cost Reduction 💰
Healthcare breaches remain the most expensive across all industries, with the average incident reaching $7.42 million in 2024, and total industry losses exceeding $21.9 billion from ransomware downtime alone. The critical variable is dwell time: reducing MTTD from 200+ days to hours prevents breach escalation, limits affected records, and dramatically lowers total incident cost.
4. Cyber Insurance Premium Savings ✅
Organizations with documented 24/7 AI SOC monitoring, published MTTR SLAs, and continuous compliance evidence report 15–30% cyber insurance premium reductions. Insurers reward what they can verify, and an AI SOC produces the exact audit trail underwriters are looking for when setting rates.
5. Analyst Hiring Cost Elimination 💸
A full in-house 24/7 SOC requires 8–12 analysts at $95K–$130K salary each, totaling $760K–$1.56M per year before training, benefits, and turnover costs. With 18-month average analyst tenure, you’re also absorbing constant recruitment and onboarding cycles. An AI SOC with a Human Ally model delivers equivalent coverage at a fraction of that spend.
Sample ROI Calculation: 200-Bed Hospital (~2,000 Endpoints)
| Cost Category | In-House SOC | AI SOC (UnderDefense) |
|---|---|---|
| Annual staffing / service cost | ~$1.2M/year (8–10 analysts) | $264K–$360K/year ($11–$15 × 2,000 × 12) |
| Compliance tooling | $50K–$100K/year (separate tools) | $0 (forever-free compliance kits included) |
| Net annual savings | — | $840K–$936K/year |
| Ransomware downtime prevention value | Not quantified (reactive) | $1.9M/day avoided with 0.5h MTTR |
| HIPAA fine avoidance | Manual, gap-prone | Continuous, audit-ready |
| Estimated Year 1 ROI | — | 3–5x |
How UnderDefense Simplifies the Calculation
We publish transparent pricing, $11–$15 per endpoint per month, so there’s no “contact sales” ambiguity in your budget model. We provide a free SOC Cost Calculator on the UnderDefense website to model ROI for your specific healthcare environment, and forever-free HIPAA compliance kits are included with every MDR engagement. No separate compliance tool purchase. No hidden professional services fees. The math should be as clear as the security, because when a CFO asks “what does this cost and what do we save,” you should be able to answer in one table, not a 40-page business case.
Q9. Which AI SOC Deployment Model Fits Your Healthcare Organization, From 5-Physician Clinic to 500-Bed Hospital?
The Decision Dilemma
Choosing an AI SOC for a 5-physician dermatology clinic requires a fundamentally different approach than securing a 500-bed hospital with 15,000 endpoints and 3,000 IoMT devices. Pick wrong, and you’re overpaying for capabilities you’ll never use, or underprotecting an environment that’s one phishing click away from a ransomware headline.
The Wrong Way to Choose
Most healthcare IT leaders default to one of three flawed criteria: picking the cheapest per-endpoint option (ignoring whether the provider can actually respond to threats), selecting the biggest brand (assuming name recognition equals healthcare expertise), or assuming their clinic is “too small to target.” That last one is especially dangerous. Over 60% of healthcare ransomware attacks target organizations with fewer than 500 employees. Small doesn’t mean safe. It means under-resourced.
3-Tier Healthcare AI SOC Decision Matrix
| Tier 1: Small Clinic (1–50 endpoints) | Tier 2: Mid-Size Practice / Regional Hospital (50–500 endpoints) | Tier 3: Large Hospital Network (500–5,000+ endpoints) | |
|---|---|---|---|
| Typical Profile | Solo/group practice, outpatient center | Regional hospital, specialty group, ASC | Multi-site health system, academic medical center |
| Key Needs | Email security, endpoint protection, basic HIPAA compliance, portal monitoring | EHR monitoring, IoMT visibility, 24/7 coverage, HIPAA audit automation | Full kill chain coverage, IoMT segmentation, multi-site correlation, multi-framework compliance |
| Deployment Model | ✅ Fully managed AI SOC, turnkey | ✅ AI SOC + dedicated analyst, custom detection tuning | ✅ AI SOC + concierge team, proactive threat hunting |
| Budget Range | 💰 $11–$15/endpoint/month | 💰 $11–$15/endpoint/month + custom scoping | 💰 $11–$15/endpoint/month + portfolio pricing |
| Time to Value | ⏰ 30-day turnkey | ⏰ 30-day deploy + 60-day tuning | ⏰ 30-day deploy + 90-day optimization |
Where UnderDefense Scales Across All Three Tiers
UnderDefense covers the full healthcare spectrum. For small clinics, we deliver turnkey 30-day deployment with immediate 24/7 coverage, no security hire required. For mid-size practices, dedicated analysts tune detection rules to your clinical workflows. For large hospital networks, a full concierge team provides proactive threat hunting with 96% MITRE ATT&CK coverage and multi-site correlation.
Transparent pricing at $11–$15/endpoint/month scales linearly across all tiers. ❌ Arctic Wolf’s $96K+ median annual contract prices out smaller clinics entirely. ❌ CrowdStrike’s Falcon-native lock-in doesn’t cover the full healthcare attack surface. Patient portals, IoMT, and EHR audit logs fall outside its endpoint focus.
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User, Program Development UnderDefense G2 – Verified Review
“We received little value from ArcticWolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
The question isn’t whether your healthcare organization is big enough for an AI SOC but whether you can afford to be the next ransomware headline without one.
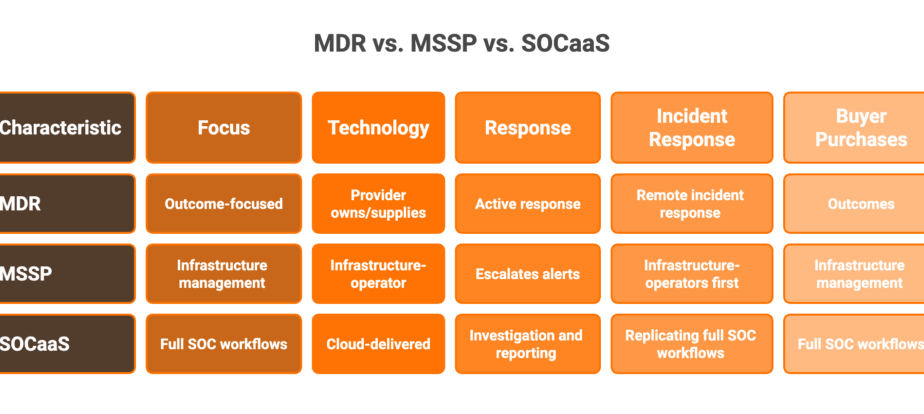
Q10. How Do Traditional MDR Providers and Legacy MSSPs Compare to a Healthcare-Focused AI SOC?
Why This Comparison Matters
Healthcare organizations face a three-way choice: traditional MDR providers with broad detection but no healthcare context, legacy MSSPs with 24/7 monitoring but rigid playbooks, or a healthcare-focused AI SOC combining AI-driven detection across the full clinical attack surface with human-verified response and automated compliance.
Traditional MDR: Strong Detection, Healthcare Blind Spots
Arctic Wolf brings strong brand recognition and a dedicated concierge security team. However, it operates on proprietary vendor lock-in. You must replace your existing SIEM and tools with their stack. Pricing is opaque ($96K+ median annual), and there’s no HIPAA compliance automation built in.
CrowdStrike Falcon Complete delivers excellent endpoint detection within the Falcon ecosystem. But EHR audit logs, patient portal authentication, and IoMT device behavior all fall outside its coverage. Both escalate healthcare alerts back to your team without clinical context.
“This is not an extension of our security team as was originally sold… Still not quite there with the remediation side of things.”
— Sr. Cybersecurity Engineer, Manufacturing Arctic Wolf – Gartner Verified Review
UnderDefense’s Healthcare-Differentiated Approach
We don’t force stack replacement. UnderDefense MAXI integrates with 250+ existing tools and monitors the complete healthcare environment: endpoints, EHR access, patient portals, IoMT devices, identity systems, and cloud. Concierge analysts verify directly with clinical staff. HIPAA evidence is auto-generated, not a bolt-on product.
Healthcare Security: 8-Criteria Comparison
| Criterion | Arctic Wolf | CrowdStrike Falcon Complete | Legacy MSSP | UnderDefense AI SOC |
|---|---|---|---|---|
| EHR Monitoring | ❌ Not covered | ❌ Endpoint-only | ⚠️ Log collection, no context | ✅ Full EHR access monitoring |
| Patient Portal Coverage | ❌ No | ❌ No | ❌ No | ✅ Auth logs, API abuse detection |
| IoMT Visibility | ⚠️ Limited | ❌ No | ❌ No | ✅ Device behavior monitoring |
| HIPAA Compliance Automation | ❌ Separate product | ❌ Not included | ⚠️ Manual reports | ✅ Auto-generated, forever-free |
| Response Capability | ⚠️ Escalates to customer | ✅ Endpoint containment | ❌ Alert-only | ✅ Full containment + user verification |
| Integration Approach | ❌ Proprietary stack required | ⚠️ Falcon-native | ⚠️ Limited | ✅ 250+ existing tools |
| Pricing Transparency | ❌ Contact sales ($96K+) | ❌ Contact sales | ⚠️ Varies | ✅ Published $11–$15/endpoint/mo |
| Onboarding Speed | ⚠️ Requires migration | ✅ Fast for Falcon users | ⚠️ Weeks to months | ✅ 30-day turnkey |
“The biggest win for me was getting actual control over our security alerts. Their team cleaned up our configurations and got the noise under control within the first week.”
— Verified User, Marketing and Advertising UnderDefense G2 – Verified Review
Who Should Choose What
Choose Arctic Wolf if you’re starting from scratch with no existing security investments and prefer a single-vendor ecosystem. Choose CrowdStrike if you’re all-in on Falcon and only need endpoint coverage. Choose UnderDefense if you need full healthcare attack surface visibility, HIPAA automation, and analysts who verify alerts directly with clinical staff rather than escalating tickets back to your team.
Q11. Who Are the Best AI SOC Providers for Healthcare Security in 2026?
The leading AI SOC platforms for healthcare in 2026 include UnderDefense, Stellar Cyber, Censinet, and Seceon, each with distinct approaches to EHR monitoring, HIPAA compliance automation, and clinical threat detection. Traditional MDR providers like Arctic Wolf and CrowdStrike Falcon Complete also compete in healthcare but with limited healthcare-specific capabilities.
What Separates Healthcare-Grade AI SOC Providers
AI SOC for healthcare has evolved beyond general-purpose 24/7 monitoring. The key differentiators now are healthcare asset coverage (EHR + IoMT + patient portals), HIPAA compliance automation (built-in vs. bolt-on), response capability (clinical context verification vs. generic alert escalation), and scalable pricing (transparent per-endpoint vs. opaque enterprise quotes).
What to evaluate before shortlisting:
- EHR integration depth — Does it natively monitor Epic, Cerner, or MEDITECH access logs, or just ingest generic syslog?
- IoMT medical device visibility — Can it detect anomalous behavior from infusion pumps, imaging systems, and connected monitors, or only traditional endpoints?
- HIPAA compliance evidence — Is audit-ready evidence generated automatically as a byproduct of monitoring, or does it require a separate compliance tool?
- Concierge analyst verification — Can analysts verify suspicious activity directly with clinical staff via Slack or Teams, or do they escalate tickets back to your team?
- Published transparent pricing — Is the cost published per-endpoint with no hidden fees, or hidden behind “contact sales”?
Finding the Right Fit
Each provider excels in different healthcare scenarios: Stellar Cyber for Open XDR flexibility in large health systems, Censinet for risk management context across medical device ecosystems, and UnderDefense for full-stack integration with clinical response and HIPAA automation. The right choice depends on your existing security investments, organization size, and compliance maturity.
This analysis is based on documented MTTR metrics, HIPAA compliance capabilities, G2 Spring 2025 healthcare reviews, and operational outcomes across 500+ MDR deployments.
Q12. How Does UnderDefense’s AI SOC + Human Ally Model Protect Healthcare Organizations in Practice?
The Healthcare Challenge in One Frame
Healthcare faces the highest ransomware targeting of any industry, with attack surfaces spanning EHRs, patient portals, reception desks, and thousands of IoMT devices, all while managing HIPAA requirements that general-purpose security tools were never designed to address. The stakes are uniquely high: disrupted patient care, exposed PHI, regulatory penalties, and erosion of the trust that healthcare depends on.
Why General-Purpose Security Falls Short
Traditional MDR providers and legacy MSSPs weren’t built for this environment. They lack EHR integration, can’t distinguish a nurse accessing records at 2 AM during a legitimate shift change from a compromised credential doing the same thing, don’t automate HIPAA evidence collection, and escalate alerts without clinical context. Your already-stretched IT team becomes the manual correlation layer between detection and response.
⏰ 2:14 AM, An Operational Walkthrough
Here’s what it looks like when an AI SOC with a Human Ally actually works:
- 2:14 AM — UnderDefense MAXI detects anomalous EHR access from a nurse’s account: unusual record volume, accessed from an unfamiliar workstation.
- 2:15 AM — AI correlates the EHR anomaly with concurrent PowerShell execution on the same endpoint, a behavioral pattern consistent with credential compromise.
- 2:17 AM — Concierge analyst messages the nurse via Teams: “Hi Maria, did you just run a system command from Workstation 4B?”
- 2:19 AM — Maria confirms she didn’t. Within 8 minutes: credentials revoked, endpoint isolated, and lateral movement blocked.
- 2:22 AM — Incident fully documented with HIPAA-compliant audit trail: detection method, verification steps, containment actions, and timeline.
- 7:00 AM — CISO reviews a complete incident report over coffee. No PHI compromised. No ransomware deployed. No 3 AM phone call.
That’s the difference between “suspicious login detected, please investigate” and “threat verified, contained, and documented before your team woke up.”
Proof Points and the German Healthcare Case Study
A German healthcare leader scaled its IT security team with UnderDefense MDR, achieving enterprise-grade 24/7 coverage without building an internal SOC. Across 500+ MDR clients, the numbers tell the story:
✅ 100% ransomware prevention record over 6+ years of operation
⏰ 0.5-hour MTTR for critical incidents, verified, not estimated
⭐ 2-day faster threat detection vs. CrowdStrike OverWatch in documented case studies
✅ 96% MITRE ATT&CK coverage with custom detection tuning
✅ 99% alert noise reduction, your team reviews incidents, not maybes
💰 $11–$15/endpoint/month transparent pricing with forever-free HIPAA compliance kits
“Their team provided us with clear and detailed insights into security vulnerabilities, along with practical recommendations on how to fix them. This level of transparency made it easy for our team to take action.”
— Arman N., CTO, Mid-Market UnderDefense G2 – Verified Review
“It’s reassuring to know they’re always watching for threats, and it doesn’t cost a fortune. They catch and stop problems quickly, which is a huge relief.”
— Serhii B., CISO, Mid-Market UnderDefense G2 – Verified Review
Your healthcare organization’s EHRs, patient portals, and reception desks are being targeted right now. Book a 15-minute healthcare security assessment with UnderDefense to see how UnderDefense MAXI protects your clinical environment, or use the SOC Cost Calculator to model what 24/7 protection actually costs for your organization.
1. What is an AI SOC for healthcare, and how does it differ from traditional security monitoring?
An AI SOC for healthcare is a security operations center powered by artificial intelligence that continuously monitors Electronic Health Records, patient portals, IoMT medical devices, and clinical endpoints to detect ransomware and cyber threats in real time.
Unlike traditional security monitoring, which relies on siloed tools like standalone EDR or SIEM, an AI SOC correlates signals across all clinical systems simultaneously. This means EHR access patterns, endpoint behavior, identity events, and network traffic are analyzed together, not in isolation.
The critical difference is clinical context. A traditional SOC flags “unusual login at 3 AM” as suspicious regardless of context. A healthcare AI SOC cross-references that login against shift schedules, device location, and EHR access volume to determine whether it’s a nurse on call or a compromised credential. We built our UnderDefense MAXI platform around this exact architecture, combining AI-driven correlation with concierge analysts who verify alerts directly with clinical staff before escalating.
This approach eliminates the “black-box escalation” trap where traditional providers send “please investigate” tickets back to your already-stretched hospital IT team.
2. How does an AI SOC automate HIPAA compliance for healthcare organizations?
An AI SOC automates HIPAA compliance by generating audit-ready evidence as a direct byproduct of continuous 24/7 security monitoring, rather than requiring separate compliance tools or manual spreadsheet tracking.
Specifically, an AI SOC maps to key HIPAA Security Rule requirements:
-
§164.308(a)(1): Continuous risk assessment via real-time threat detection
-
§164.312(a): Automated access control monitoring and unauthorized access alerting
-
§164.312(b): Automated audit log collection, correlation, and retention
-
§164.308(a)(6): Incident detection, investigation logging, and response documentation
Most healthcare organizations we work with maintain security tools and compliance documentation as completely separate systems, updated by different people on different schedules. This creates the gaps that OCR audits expose.
We include forever-free compliance kits with every MDR engagement, so access logs, incident documentation, risk assessment data, and audit trails are continuously produced and audit-ready from day one. No separate compliance tool purchase required, and no quarterly spreadsheet scramble before audits.
3. Why are hospitals and clinics the #1 target for ransomware, and how does an AI SOC prevent attacks?
Healthcare is the most-targeted sector for ransomware globally because of a unique combination of six vulnerability factors: 24/7 uptime pressure that prevents patching windows, a massive attack surface spanning EHRs and IoMT devices, legacy systems running outdated firmware, PHI records that sell for 10–40x more than credit card numbers on the dark web, chronic cybersecurity staffing shortages, and compliance resource drain from HIPAA audit preparation.
The numbers reflect this: 445 ransomware attacks hit healthcare providers in 2025 alone, with the average breach costing $7.42 million. Healthcare organizations experience an average of 17 days of downtime per ransomware incident, costing approximately $1.9 million per day.
An AI SOC prevents attacks by detecting and disrupting each stage of the ransomware kill chain, from initial phishing through credential harvesting, lateral movement, privilege escalation, and exfiltration, before encryption ever begins. We maintain a 100% ransomware prevention record across 500+ MDR clients by catching threats at Stages 2–4, where standalone EDR and legacy MSSPs typically go blind.
4. How does an AI SOC monitor and protect EHR systems and IoMT medical devices?
An AI SOC monitors EHR platforms like Epic, Cerner/Oracle Health, and Meditech at the behavioral level and IoMT medical devices like infusion pumps, imaging systems, and patient monitors via agentless network traffic analysis.
For EHR monitoring, the AI SOC provides five key detection capabilities:
-
Bulk record access detection (flagging 500+ record queries vs. normal 20–30)
-
After-hours PHI access correlation against shift schedules
-
Abnormal HL7/FHIR API traffic monitoring
-
Privilege escalation detection when billing accounts access clinical records
-
Cross-referencing EHR login with endpoint behavior like PowerShell execution
For IoMT devices, which cannot run traditional endpoint agents, the AI SOC establishes baseline communication patterns for every device and detects deviations. This includes DICOM traffic profiling for imaging systems, network segmentation validation, firmware vulnerability correlation against known CVEs, and medical protocol anomaly detection.
Our UnderDefense MAXI platform ingests EHR audit logs and IoMT network telemetry alongside 250+ other data sources, correlating signals that no single tool can see independently.
5. What does an AI SOC for healthcare cost, and what is the ROI?
At UnderDefense, we publish transparent pricing at $11–$15 per endpoint per month, which includes 24/7 AI-driven monitoring, concierge analyst response, and forever-free HIPAA compliance kits.
For a 200-bed hospital with approximately 2,000 endpoints, the annual cost ranges from $264K–$360K. Compare that to an in-house 24/7 SOC requiring 8–12 analysts at $95K–$130K each, totaling $760K–$1.56M per year before training, benefits, and turnover costs. Net annual savings: $840K–$936K.
ROI extends across five measurable categories:
-
Ransomware downtime prevention ($1.9M/day avoided)
-
HIPAA fine avoidance (up to $2.19M per violation tier)
-
Breach cost reduction ($7.42M average healthcare breach)
-
Cyber insurance premium savings (15–30% reductions documented)
-
Analyst hiring cost elimination
We provide a free SOC Cost Calculator to model ROI for your specific environment, with estimated Year 1 ROI of 3–5x. You can also review our full MDR pricing breakdown for detailed per-endpoint cost structures.
6. Which AI SOC deployment model works best for small clinics vs. large hospital networks?
The right deployment model depends on your organization size, endpoint count, and clinical complexity. We’ve designed a 3-tier framework:
Tier 1 (Small Clinic, 1–50 endpoints): Solo or group practices need turnkey, fully managed AI SOC deployment with email security, endpoint protection, basic HIPAA compliance, and portal monitoring. Time to value: 30-day turnkey. No security hire required.
Tier 2 (Mid-Size Practice, 50–500 endpoints): Regional hospitals and specialty groups need EHR monitoring, IoMT visibility, 24/7 coverage, and HIPAA audit automation. This tier includes a dedicated analyst with custom detection tuning for your clinical workflows. Time to value: 30-day deploy plus 60-day tuning.
Tier 3 (Large Hospital Network, 500–5,000+ endpoints): Multi-site health systems need full kill chain coverage, IoMT segmentation, multi-site correlation, and multi-framework compliance. A full concierge team delivers proactive threat hunting with 96% MITRE ATT&CK coverage. Time to value: 30-day deploy plus 90-day optimization.
All tiers are priced at $11–$15/endpoint/month with linear scaling, so small clinics aren’t priced out of enterprise-grade protection.
7. How does an AI SOC handle alert fatigue and cybersecurity staffing shortages in healthcare?
Healthcare security teams face a compounding crisis: the global cybersecurity workforce gap has reached 4.8 million unfilled positions, 77% of organizations saw increased alert volume in 2025, and SOC analysts average just 18 months of tenure before burnout-driven turnover. Healthcare organizations face 30%+ annual turnover in security roles.
An AI SOC breaks the staffing equation by automating the scale problem entirely. Instead of hiring 8–12 analysts to staff a 24/7 operation, we reduce customer-facing alerts by up to 99% through custom detection tuning. Your three-person IT team reviews confirmed incidents, not 10,000 daily maybes.
The operational math is simple: you can spend 18 months hiring an analyst who leaves in 18 months, or deploy an AI SOC with human allies who already know the healthcare threat landscape. We provide 24/7/365 SOC coverage with dedicated Tier 3–4 concierge analysts, delivering enterprise coverage without requiring healthcare organizations to hire, train, and retain a full security team.
Without AI automation, healthcare mean time to detect stretches to 200+ days. With an AI SOC, threats are identified and contained in hours, not months.
8. How does UnderDefense's AI SOC compare to Arctic Wolf and CrowdStrike for healthcare?
The comparison comes down to healthcare-specific coverage, response capability, compliance automation, and pricing transparency.
Arctic Wolf offers strong brand recognition and a dedicated concierge team, but it requires proprietary stack replacement, has opaque pricing ($96K+ median annual), and provides no built-in HIPAA compliance automation. EHR monitoring and patient portal coverage are not included.
CrowdStrike Falcon Complete delivers excellent endpoint detection within the Falcon ecosystem, but EHR audit logs, patient portal authentication, and IoMT device behavior all fall outside its coverage scope.
UnderDefense integrates with 250+ existing tools without rip-and-replace, monitors the complete healthcare environment (endpoints, EHR access, patient portals, IoMT devices, identity systems, and cloud), and includes forever-free HIPAA compliance kits. Concierge analysts verify directly with clinical staff via Slack or Teams rather than escalating tickets back to your team.
Published pricing at $11–$15/endpoint/month, 30-day turnkey deployment, and a documented 100% ransomware prevention record across 500+ MDR clients make the case concrete. You can review the full 8-criteria comparison in our SOC provider guide.
The post AI SOC for Healthcare: Defend EHRs and Automate HIPAA Compliance appeared first on UnderDefense.