Q1: What Is Managed SIEM, and Why Are Security Teams Shifting to It?
Managed SIEM is a security operations model where a third-party provider handles the deployment, tuning, monitoring, and management of your Security Information and Event Management platform, including log collection, event correlation, threat detection, and incident escalation, so your internal team doesn’t have to build or staff a 24/7 SOC from scratch.
Why the Shift Is Accelerating
The math stopped working for most organizations. The global cybersecurity workforce gap has ballooned to 4.8 million unfilled roles according to the ISC2 2024 Workforce Study, with demand at 10.2 million professionals against only 5.5 million available. And this isn’t just a headcount problem. It’s a skills mismatch compounded by budget cuts that are forcing layoffs even as threats escalate.
Meanwhile, log volumes are exploding. Cloud workloads, SaaS sprawl, hybrid environments: every tool you add generates telemetry that your SIEM needs to ingest, normalize, and correlate. Running a SIEM 24/7 requires multiple shifts of analysts, incident responders, and management staff, with salary costs alone ranging from $300,000 to $700,000 annually depending on region and expertise. Total operational costs for a 24/7 SIEM easily hit $2.7 million per year, and that’s before your datasets or complexity grow.
Then there’s the compliance pressure. SOC 2, HIPAA, ISO 27001, PCI DSS: each mandates continuous monitoring evidence that auditors verify. Regulations like GDPR require rapid breach notification within 72 hours, while SOX demands comprehensive reporting on system vulnerabilities. Your SIEM isn’t optional. It’s the audit trail. And if nobody’s tuning the rules or watching the alerts at 3 AM, that audit trail becomes a liability.
⚠️ The Problem with Legacy Approaches
Here’s what I’ve seen across hundreds of engagements: organizations typically land in one of two broken states.
Legacy MSSP monitoring gives you “alerts without context,” meaning checkbox coverage based on rigid playbooks rather than real-time threat understanding. You get a dashboard. You don’t get answers.
Pure-play SIEM tools give you “technology without operational expertise.” You buy Splunk or Elastic, configure it once, and watch detection quality decay within months because nobody’s tuning the correlation rules to match your evolving environment.
Managed SIEM is the convergence: technology + expertise + 24/7 operational coverage. It’s the acknowledgment that tools alone don’t save the day. People, process, and tools working together do.
How UnderDefense Approaches Managed SIEM
We don’t bolt a monitoring layer onto your stack and call it a day. We operationalize your existing SIEM, whether that’s Elastic, Splunk, or another platform, so you retain full ownership of your data, correlation rules, and business logic. This isn’t a philosophical stance. It’s a lesson learned from watching organizations lose years of custom detection tuning when they switch providers.
As one CISO we work with put it during a recent session: if your MDR provider owns your SIEM, you start over on detection engineering every time you renegotiate a contract. We handle everything from detection engineering to 3 AM escalations. You keep control. That’s the model.
Q2: How Does Managed SIEM Actually Work Behind the Scenes? (Log Collection to Threat Response)
Most articles on managed SIEM say “it collects logs and detects threats” but never explain what actually happens between raw log ingestion and a confirmed incident landing on your desk. If you’re trusting a provider with your security telemetry, you deserve operational transparency, not marketing abstractions.
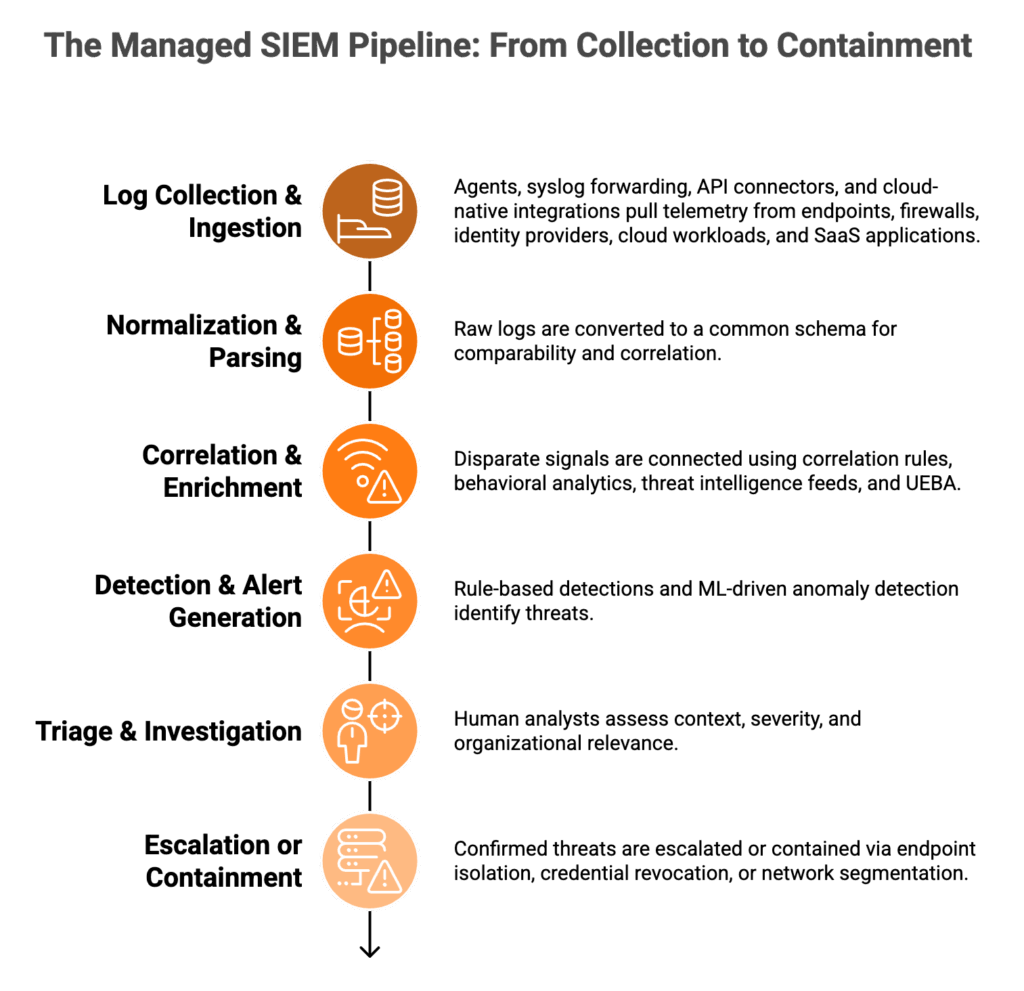
The Six-Stage Pipeline
Here’s the full managed SIEM pipeline, step by step:
- Log Collection & Ingestion: Agents, syslog forwarding, API connectors, and cloud-native integrations pull telemetry from endpoints, firewalls, identity providers (Okta, Azure AD), cloud workloads (AWS CloudTrail, GCP), and SaaS applications. Every relevant data source gets onboarded.
- Normalization & Parsing: Raw logs arrive in dozens of formats. CrowdStrike events, Okta authentication logs, AWS CloudTrail entries, and Palo Alto firewall alerts all get converted to a common schema so they’re comparable and correlatable. Without this step, your SIEM is just a log warehouse.
- Correlation & Enrichment: This is where signal emerges from noise. Correlation rules, behavioral analytics, threat intelligence feeds, and UEBA (User and Entity Behavior Analytics) connect disparate signals, tying a failed VPN login to a credential dump on the dark web to an unusual file download on an endpoint.
- Detection & Alert Generation: Rule-based detections catch known patterns, while ML-driven anomaly detection catches deviations from baseline behavior. Both should map to the MITRE ATT&CK framework so you can see exactly which tactics and techniques are being flagged.
- Triage & Investigation: Human analysts assess context, severity, and organizational relevance. This is the step that separates real threats from noise, and it’s the step most providers shortcut.
- Escalation or Containment: Confirmed threats get escalated with full context, or contained directly via endpoint isolation, credential revocation, or network segmentation.
⏰ The Gap Most Buyers Miss
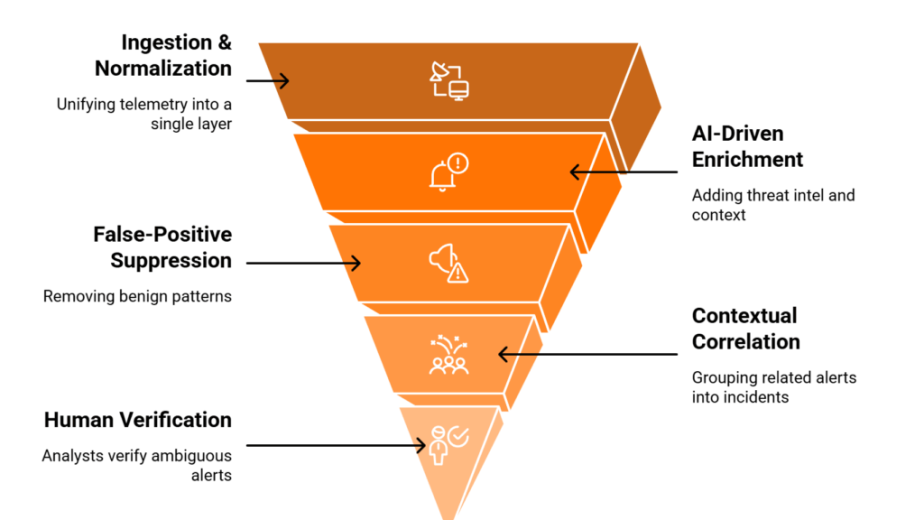
The critical differentiator lives between Step 4 (detection) and Step 6 (response). Most managed SIEM providers stop at detection. They generate the alert and throw it over the wall to your team with a “please investigate” ticket.
Here’s the operational reality: many behavioral alerts require context that technology alone can’t provide. Did Jane log in from a new location, or was her account compromised? Did your IT admin run that PowerShell script, or was it an attacker? If you had time, you’d ask, but at 2 AM your analyst is triaging 47 other alerts.
How UnderDefense Closes the Loop
We operationalize this entire pipeline: ingesting from 250+ tools, maintaining a 2-minute alert-to-triage SLA, and deploying concierge analysts who verify suspicious activity directly with affected users via Slack, Teams, or email. When the detection says “unusual OAuth grant at 2:41 AM,” our analyst messages the user to confirm, and if they didn’t authorize it, we revoke the token and contain the session before your team wakes up.
That’s 96% MITRE ATT&CK coverage backed by the one thing pure automation can’t deliver: human judgment applied at speed. The UnderDefense MAXI platform orchestrates this entire workflow in a single, auditable view.
Q3: What Services Are Typically Included in a Managed SIEM Engagement?
A fully managed SIEM engagement should cover seven core service areas. Anything less means you’re buying partial coverage and staffing the gaps internally, often without realizing it until an incident exposes the holes. Here’s what to expect and what to verify before signing.
✅ The Seven Core Services
- 24/7 log monitoring & event correlation: Continuous oversight across all ingested data sources, not just business-hours coverage with on-call afterhours.
- Detection engineering & custom rule tuning: Rules mapped to your specific environment, not generic out-of-the-box signatures that decay within weeks.
- Threat intelligence integration: Commercial and open-source feeds enriching alerts with real-world context on active threat campaigns.
- Human-led alert triage & investigation: Analysts reviewing alerts for organizational relevance, not automated forwarding of every SIEM hit to your inbox.
- Compliance reporting & audit evidence generation: Automated evidence production for SOC 2, HIPAA, ISO 27001, PCI DSS: the artifacts auditors actually request.
- SIEM platform management: Health monitoring, performance tuning, storage optimization, and index management so your platform doesn’t degrade over time.
- Incident escalation with context & response guidance: Confirmed threats escalated with full investigation context, or directly contained in advanced tiers via endpoint isolation, credential revocation, or network segmentation.
❌ What’s Often Missing (and Shouldn’t Be)
Many providers bundle items 1 and 6, then charge separately for detection engineering, threat hunting, and compliance reporting. That’s the equivalent of buying a car without an engine and paying extra for it later. If your provider’s “managed SIEM” stops at log storage and basic alerting, you’re paying for a monitoring dashboard, not managed security operations.
How UnderDefense Delivers All Seven, Plus More
UnderDefense bundles all seven as standard, plus proactive threat hunting and ChatOps user verification. The customer retains full ownership of their Elastic or Splunk instance while we operationalize it end-to-end: detection engineering, rule tuning, compliance automation, and 24/7 analyst response included from day one.
The result: 99% alert noise reduction within the first 30 days of onboarding through custom detection tuning, because your team should review confirmed incidents, not triage thousands of maybes.
“Their team cleaned up our configurations and got the noise under control within the first week. Now when we get an alert, we know it’s something worth looking into.”
— Verified User, Marketing and Advertising UnderDefense G2 – Verified Review
“At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it. Now, with their security monitoring and incident response we know our endpoints are well-protected.”
— Yaroslava K., IT Project Manager UnderDefense G2 – Verified Review
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense G2 – Verified Review
Q4: Self-Managed vs. Co-Managed vs. Fully Managed SIEM: Which Model Fits Your Organization?
Most articles frame managed SIEM as a binary: build it yourself or outsource everything. Reality is a spectrum with three distinct models, and the right choice depends on your team size, budget, compliance timeline, and whether you have the 24/7 coverage to monitor and tune a SIEM continuously.
Self-Managed SIEM
Full internal ownership. You deploy, configure, tune, and monitor the SIEM with your own staff.
✅ Strengths: Maximum control, data sovereignty, deep customization for unique business logic
❌ Limitations: Requires 3 to 5 dedicated FTEs with SOC analyst salaries ranging from $130K to $260K each, 6 to 12 month deployment, and annual TCO of $500K to $2.7M when you factor in platform licensing, staffing, training, and continuous rule tuning. Detection quality decays fast if nobody’s maintaining correlation rules, and turnover at Tier 1 is constant.
Co-Managed SIEM
You own the SIEM; the provider supplements with detection engineering, tuning, and overflow monitoring.
✅ Strengths: Retains tool ownership, augments gaps in expertise, keeps business logic in-house
❌ Limitations: Shared responsibility creates accountability gray zones during incidents. Who responds at 3 AM? Unclear SLAs on triage ownership mean your team still carries the on-call burden. As one CISO described it: “I still keep a level two or level three team in-house for business context, but the handoff points are where things break.”
Fully Managed SIEM
The provider owns the entire operational lifecycle: deployment, tuning, detection engineering, 24/7 monitoring, triage, and response, while the customer retains platform and data ownership.
✅ Strengths: Fastest time to value (30 days vs. 6 to 12 months), predictable costs, 24/7 coverage included, no hiring/training overhead
❌ Limitations: Requires trust in the provider’s detection quality and response capability, which is why you should demand observable workflows, not black-box dashboards.
Side-by-Side Comparison
| Dimension | Self-Managed | Co-Managed | Fully Managed |
|---|---|---|---|
| Staffing Requirement | 3 to 5 dedicated FTEs | 1 to 2 internal + provider | None required |
| Annual TCO Range | $500K to $2.7M+ | $250K to $800K | $11 to $15/endpoint/month 💰 |
| Time to Value | 6 to 12 months | 2 to 4 months | 30 days |
| Detection Rule Ownership | Fully internal | Shared | Provider-managed, customer-owned |
| 24/7 Coverage | Must staff 3 shifts | Partial/overflow only | ✅ Included |
| Compliance Reporting | Manual/internal | Partial automation | ✅ Automated |
| Customization Level | Unlimited | Moderate | High (vendor-agnostic) |
| Best For | Mature SOC with 5+ analysts | Partial internal capability | Teams under 5 security FTEs |
🎯 Prescriptive Guidance
Choose self-managed if you have a mature SOC with 5+ analysts, strict data sovereignty requirements, and the budget to absorb $2M+ in annual operational costs.
Choose co-managed if you have partial internal capability and need detection engineering overflow, but be crystal clear on SLAs for who owns triage during off-hours.
Choose fully managed if your team is under 5 security FTEs, you’re scaling through compliance milestones like SOC 2 or ISO 27001, or you simply can’t afford to lose 6 to 12 months building a SOC from scratch while threats don’t wait.
UnderDefense’s model uniquely lets you keep your SIEM while getting fully managed operations, with no vendor lock-in, no platform migration, and no losing years of custom detection tuning when the contract comes up for renewal. Explore managed SIEM pricing to see how it fits your budget.
Q5: What Are the Real Benefits and Limitations of Managed SIEM?
⏰ The Operational Reality No One Talks About
Picture this: a security team of two or three people sitting behind a SIEM that produces thousands of events per second. They’re tuning detection rules against evolving threats, maintaining compliance evidence, covering nights and weekends, and still expected to run vulnerability scans and answer audit questionnaires. The result? Alert fatigue, detection decay, and a SIEM that becomes expensive shelfware.
This isn’t theoretical. 71% of SOC analysts report burnout driven by alert fatigue, and the average analyst tenure continues to shrink, with some SOCs seeing turnover cycles of less than 18 months. When your most experienced analyst leaves, they take institutional knowledge about your environment with them, creating blind spots that adversaries are quick to exploit. And every time you rehire, you restart the learning curve from scratch. Running a 24/7 in-house SOC can cost over $1.7M per year when you factor in tools, personnel, and operations.
✅ The Quantified Benefits
Managed SIEM directly addresses the operational math that breaks most internal teams:
- 60 to 80% operational overhead reduction. Log management, rule tuning, parser maintenance, and platform upgrades are offloaded to dedicated engineers who do this full-time, not as a side task between firewall changes.
- 24/7 coverage without night-shift hiring. A self-managed SIEM with true 24/7 coverage requires a minimum of 5 FTEs across shifts, costing $750K to $1M per year in salary alone. Fully managed SIEM runs $60,000 to $180,000 annually.
- Faster detection. The average time to identify and contain a breach in 2024 was 277 days for organizations without dedicated monitoring. With active managed SIEM, that drops to minutes for detection and hours for containment.
- Continuous compliance evidence. SOC 2, HIPAA, ISO 27001: all require continuous log monitoring. Managed SIEM auto-generates the audit artifacts your compliance team would otherwise spend weeks assembling manually.
- Detection quality improvement. Dedicated detection engineers writing rules full-time produce higher-fidelity alerts than a generalist IT admin writing Splunk queries as a side task.
⚠️ The Honest Challenges
No approach is without tradeoffs. Here’s what you should evaluate honestly:
- Data privacy. Your logs leave your environment, unless the provider supports on-prem or customer-cloud deployment. Ask specifically: Where does my data live?
- Integration complexity. Connecting legacy tools requires connector support and API coverage. Not every managed SIEM provider handles legacy infrastructure well.
- Vendor dependency. Switching providers means re-tuning all detection logic from scratch. If your detections live in the provider’s proprietary platform, you lose them when you leave.
- Shared responsibility gray zones. Who owns escalation decisions? Who contains? If the SLA doesn’t spell it out, you’ll find out the hard way during an incident.
- Reduced control. Custom SOAR playbooks and sub-second automated workflows are harder to maintain through a third party. Teams with mature automation may feel friction.
❌ When Managed SIEM Is the Wrong Choice
There are scenarios where managed SIEM genuinely doesn’t fit:
- Mature SOC with 5+ dedicated SIEM analysts and established detection engineering pipelines.
- Strict data sovereignty requirements in government, defense, or certain financial sectors where logs cannot leave specific boundaries.
- SIEM deeply customized with proprietary detection IP that represents years of institutional knowledge.
- Fully staffed 24/7 internal SOC where the marginal cost of adding SIEM operations is lower than outsourcing.
If none of these apply, and for most organizations under 5,000 employees they don’t, managed SIEM is the more cost-effective path.
How We Designed Our Model to Address These Challenges
We built UnderDefense to tackle the top three challenges directly. Your logs stay in your data lake: Elastic, Splunk, wherever you own them. We integrate with 250+ tools including legacy infrastructure. And our SLAs explicitly define who does what during incidents, with no gray zones and no “please investigate” escalations back to your overwhelmed team.
“UnderDefense MAXI integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense G2 – Verified Review
“At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it.”
— Yaroslava K., IT Project Manager UnderDefense G2 – Verified Review
Q6: Managed SIEM vs. MDR vs. XDR vs. SOC vs. MSSP: How Do These Models Differ?
Managed SIEM, MDR, XDR, SOC-as-a-Service, and MSSP are the five most conflated terms in security operations. They overlap, but serve different purposes. Choosing wrong means paying for capabilities you don’t need or missing the ones you do.
Defining Each Model
Managed SIEM is the outsourced operation of your SIEM platform: log management, detection rule tuning, monitoring, and maintenance. You own the SIEM; someone else runs it. The provider handles ingestion, parsing, correlation, and alert generation, but response capability varies widely.
MDR (Managed Detection and Response) spans broader detection and response across endpoints, cloud, identity, and network. It may or may not include SIEM management. The critical distinction: MDR providers are expected to respond to threats, not just detect them.
XDR (Extended Detection and Response) is a vendor-native platform unifying telemetry across multiple security layers into a single detection engine. It typically ties to a single vendor ecosystem: CrowdStrike Falcon, Palo Alto Cortex, or Microsoft Sentinel. The tradeoff is integration depth versus vendor lock-in.
SOC-as-a-Service outsources the security operations center function: human analysts for monitoring, triage, and escalation. Think of it as renting a SOC team without building one internally. Coverage quality depends entirely on the analysts’ expertise and their familiarity with your environment.
MSSP (Managed Security Services Provider) is the legacy model: outsourced monitoring focused on alert forwarding from perimeter devices. Typically without deep investigation or response. An MSSP watches your firewall logs and sends you an email when something triggers a signature.
✅ Comprehensive Comparison
| Dimension | Managed SIEM | MDR | XDR | SOC-as-a-Service | MSSP |
|---|---|---|---|---|---|
| Core Focus | SIEM platform operation, log management, detection tuning | Threat detection + active response across full stack | Unified detection across vendor-native security layers | Human analyst monitoring, triage, escalation | Alert forwarding from perimeter devices |
| Technology Scope | SIEM-specific (Splunk, Elastic, QRadar) | Endpoints, cloud, identity, network, SIEM | Vendor-native multi-layer (single ecosystem) | Varies by provider | Firewalls, IDS/IPS, basic log review |
| Vendor Flexibility | Works with customer-owned SIEM | Varies: some vendor-agnostic, some proprietary | ❌ Locked to vendor ecosystem | Moderate, depends on tools supported | Limited to supported devices |
| Response Capability | Detection + alerting; response varies | Full detection, investigation, containment | Automated response within vendor platform | Escalation-focused; limited direct response | Alert notification only |
| Alert Handling | Tuned correlation rules, enriched alerts | Triage → investigate → verify → contain | Automated cross-layer correlation | Human triage and escalation | Forward raw alerts to customer |
| Compliance Support | Strong: log retention, audit trails, reporting | Varies by provider | Limited: platform-specific reporting | Minimal | Basic log retention |
| Typical Buyer | Orgs with existing SIEM needing operational support | Mid-market teams needing 24/7 detection + response | Enterprises committed to single vendor stack | Teams needing analyst coverage without full MDR | Budget-conscious orgs needing basic monitoring |
Where the Lines Blur
The confusion exists because these categories are converging. A strong MDR provider often manages your SIEM as part of the service. An XDR platform with a managed service wrapper starts to resemble MDR. The practical question isn’t “Which category do I need?” but rather “Can this provider detect threats across my entire stack, respond with context, and operate my existing tools without forcing replacement?”
How UnderDefense Fits
UnderDefense combines managed SIEM operations with full MDR: the customer owns their SIEM while we provide 24/7 detection, investigation, and response across the entire stack. It’s the managed SIEM layer inside a broader AI SOC + Human Ally model, covering what XDR platforms promise but without vendor lock-in. We integrate with 250+ existing tools, which means you’re not choosing between models. You’re getting the operational benefits of all five categories through one unified platform.
Q7: How Does Managed SIEM Support Compliance Frameworks Like SOC 2, HIPAA, and ISO 27001?
Managed SIEM directly satisfies the continuous monitoring, log retention, and incident detection controls required by SOC 2, HIPAA, ISO 27001, PCI DSS, and CMMC. For most mid-market organizations, managed SIEM is the fastest path to audit-ready security operations.
Mapping Capabilities to Specific Controls
Here’s how managed SIEM capabilities map directly to the regulatory controls your auditors are asking about:
- SOC 2 CC7.2: Continuous monitoring of security events. Managed SIEM provides 24/7 log collection, correlation, and alerting, which is exactly what auditors verify when checking CC7.2 compliance.
- HIPAA §164.312(b): Audit controls and activity logging. HIPAA requires that covered entities maintain audit trails of system activity. Managed SIEM automates log collection from every relevant system and retains it for required periods.
- ISO 27001 A.12.4: Logging and monitoring. ISO auditors verify that event logs are produced, retained, and regularly reviewed. Managed SIEM handles all three continuously, not as a quarterly project.
- PCI DSS Requirement 10: Tracking and monitoring all access to network resources and cardholder data. This is one of the most audit-intensive PCI requirements, and managed SIEM is purpose-built to satisfy it.
- CMMC Level 2 AU: Audit and accountability practices. For defense contractors, CMMC requires systematic log management that most internal teams struggle to maintain consistently.
- GDPR Article 32: Appropriate technical measures including monitoring. While GDPR doesn’t prescribe specific tools, demonstrating continuous monitoring of personal data processing is a practical requirement.
Why Compliance Teams Love Managed SIEM
The real value isn’t just checking boxes. It’s the operational efficiency. Instead of your security team spending weeks before each audit manually assembling evidence from scattered tools, managed SIEM generates compliance artifacts from the same telemetry used for daily threat detection. Same data, two outputs: security monitoring and audit evidence.
How UnderDefense Simplifies Compliance
We include forever-free compliance kits, covering SOC 2, ISO 27001, and HIPAA, as standard with every MDR engagement. UnderDefense MAXI Compliance is built on an actual security operations platform, not a standalone checklist tool. The compliance evidence is auto-generated from the same unified telemetry that powers threat detection, which means your audit documentation reflects what’s actually happening in your environment, not what a policy document says should happen.
“Really like using UnderDefense MAXI platform, as it has everything from early risk detection and compliance to incident response automation and 24/7 protection with MDR.”
— Serhii I., CEO UnderDefense G2 – Verified Review
Customers achieve full regulatory compliance readiness within 30 days of onboarding.
Q8: What Should Security Leaders Evaluate Before Choosing a Managed SIEM Provider?
The Decision Dilemma
Choosing a managed SIEM provider means trusting an external team with your security telemetry, detection logic, and incident response. Choose wrong and you’re locked into a proprietary platform, dealing with opaque alert forwarding, or spending more time managing the provider than you would managing the SIEM.
❌ The Wrong Way to Decide
Most security leaders evaluate based on brand recognition or integration count. This ignores the critical question: Does the provider operate your SIEM, or just monitor the alerts it produces? When a threat is detected, can they respond, or do they escalate an email back to your overwhelmed team?
“Analysts provide little context, and when asked for more information in the investigation nothing is ever provided or even communicated. Support incidents are not worked to completion and communication evaporates.”
— CISO, Manufacturing Arctic Wolf – Gartner Review
✅ The Right Evaluation Framework: 7 Scored Criteria
Rate each provider 0 to 2 on these criteria. Scores of 11+ = genuine operational partnership. Below 8 = you’re buying an alert feed, not managed SIEM.
- SIEM Ownership Model: Do you retain platform ownership, or get locked into theirs?
- Detection Engineering: Custom rules tuned for your environment, or generic out-of-box?
- Response Capability: Can they contain threats (isolate endpoints, revoke credentials), or just notify?
- Alert Verification: Do they verify suspicious activity with users directly, or escalate raw alerts back?
- Pricing Transparency: Published and predictable, or “contact sales”?
- Compliance Integration: Audit-ready evidence auto-generated, or a separate project?
- Onboarding Speed: 30-day deployment, or 6-month professional services engagement?
Where UnderDefense Stands
| Criterion | Score | Why |
|---|---|---|
| SIEM Ownership | ✅ 2/2 | Your SIEM stays yours: Elastic, Splunk, or others. We operate it; you own it. |
| Detection Engineering | ✅ 2/2 | Custom rules tuned during 30-day onboarding, tested with Caldera/Ransomware Monkey simulations. |
| Response Capability | ✅ 2/2 | Full containment: endpoint isolation, credential revocation, network segmentation. 2-minute alert-to-triage and 15-minute escalation for critical incidents. |
| Alert Verification | ✅ 2/2 | ChatOps: analysts verify directly with affected users via Slack, Teams, email, and SMS. |
| Pricing Transparency | ✅ 2/2 | Published $11 to $15/endpoint/month. No hidden fees. |
| Compliance Integration | ✅ 2/2 | Forever-free compliance kits (SOC 2, ISO 27001, HIPAA) included. |
| Onboarding Speed | ✅ 2/2 | 30-day turnkey deployment with custom detection tuning and validation. |
| Total | 14/14 |
💰 The Meta-Insight
The real question isn’t “Which managed SIEM has the most integrations?” but rather “Which provider can respond to threats the way a dedicated security team would?” That’s the shift from buying an alert feed to hiring an operational partner.
“Their team provided us with clear and detailed insights into security vulnerabilities, along with practical recommendations on how to fix them. This level of transparency made it easy for our team to take action and strengthen our security.”
— Arman N., CTO UnderDefense G2 – Verified Review
“We received little value from ArcticWolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
Zero ransomware cases across all MDR clients in 6 years, because detection without human-driven response is just expensive alerting.
Q9: What Does Day 1 to Day 90 With a Managed SIEM Provider Actually Look Like?
One of the biggest unknowns is what happens after you sign. Most providers are deliberately vague on onboarding timelines, and security leaders end up waiting months for value, frustrated, exposed, and unable to hold anyone accountable. Gartner has noted that ineffective SIEM deployments occur when requirements and use cases aren’t aligned upfront, and that the average deployment takes around six months due to unstructured approaches. Here’s what a well-executed managed SIEM onboarding should look like, and the milestones you should use to keep your provider honest.
⏰ Phase 1: Days 1 to 14, Discovery & Integration
This is where the real work starts, and where most providers already fall behind. A good managed SIEM partner spends the first two weeks learning your organization, not just plugging in connectors.
- Toolset audit: Full inventory of your existing security stack, covering EDR, firewalls, cloud platforms, and identity providers
- Log source identification and prioritization: Not every source matters equally; critical assets and high-risk users come first
- API/agent/syslog connector deployment: Technical integration across your environment with data flow validation at each step
- Environment baseline profiling: Establishing what “normal” looks like for your org, including who your VIPs are, what legitimate admin activity looks like, and when developers run scripts on weekends
- Communication channel setup: Dedicated Slack or Teams channels for real-time escalation, not email threads that disappear into inboxes
We invest these first two weeks learning your org because detection rules are useless without organizational context. If your provider skips this step, everything downstream suffers.
✅ Phase 2: Days 15 to 30, Detection Tuning & Noise Reduction
This is where managed SIEM starts proving its value, or exposing its weaknesses.
- Custom detection rules deployed, mapped to your specific threat profile, not generic out-of-the-box templates
- False positive suppression targeting 99% noise reduction, because alert fatigue is the enemy of actual security
- MITRE ATT&CK coverage gap analysis to identify blind spots in your detection logic
- Initial proactive threat hunting sweep across your environment
- Compliance reporting configuration for SOC 2, HIPAA, ISO 27001, automated, not manual
Validation Milestone
By Day 30, run simulated attacks (Atomic Red Team, MITRE Caldera, or Ransomware Monkey) to confirm detection coverage. If your provider can’t demonstrate that detections actually fire against real attack techniques, you have a dashboard, not a security program. UnderDefense commits to a 30-day turnkey deployment: by Day 30, you have validated detections, confirmed SLAs, and your first monthly security posture report.
🔍 Phase 3: Days 31 to 90, Operational Maturity
This is where good providers separate from great ones. The tuning doesn’t stop at Day 30. It accelerates.
- Ongoing detection refinement from real-world alert data and threat intelligence
- Monthly security posture reviews with your team, not just dashboards, but structured conversations about risk reduction
- Tabletop exercise with your internal team to validate incident response workflows end-to-end
- Continuous tuning feedback loop, where every false positive becomes a better detection rule
- Full 24/7 monitored state with documented SLAs active and measurable
⚠️ Hold Your Provider Accountable
The Reddit cybersecurity community has repeatedly flagged that providers like Arctic Wolf operate as a “black box,” where you trust they’re ingesting data but lack visibility into what’s happening.
“From what I know of the platform, it is a black box, not a SIEM that you could query yourself. I do not know what their reporting is like.”
— u/justmirsk, r/cybersecurity Reddit Thread
“Arctic Wolf solves the problem of not being able to afford a SOC. If that’s a problem you have, then they’re OK. They will ingest your logs and triage them, but you don’t get to use their platform. Reporting was not super impressive.”
— u/TheIronMark, r/cybersecurity Reddit Thread
If your managed SIEM provider can’t show you documented MITRE ATT&CK coverage, published SLA metrics, and a clear audit trail by Day 90, they’re selling monitoring, not managed security. The goal is operational maturity: your team reviews confirmed incidents, not raw alerts.
Q10: How Do the Leading Managed SIEM and SOC Providers Compare?
The leading managed SIEM and SOC-as-a-Service providers in 2026 include UnderDefense, Arctic Wolf, CrowdStrike, Rapid7, and Deepwatch, each with distinct architectural approaches, pricing models, and response capabilities.
The Landscape Has Changed
Managed SIEM has evolved well beyond log monitoring. The real differentiators now are integration flexibility (vendor-agnostic vs. proprietary lock-in), response depth (detection-only vs. full containment), pricing transparency (published vs. contact-sales), and whether you retain ownership of your SIEM platform and the business logic you’ve built inside it.
As I’ve seen across hundreds of engagements, and as JR, former CISO of Micron and DarkTrace, put it in a recent conversation: if you build custom correlation rules and automation inside a vendor’s proprietary system, that logic doesn’t come with you when you switch providers. You start the tuning process all over again.
📋 Selection Criteria That Actually Matter
- Vendor-agnostic integration vs. proprietary stack: Does the provider work with your existing SIEM and EDR, or force replacement?
- Human analyst access: Do you get direct communication with Tier 3 to 4 analysts, or ticket-based escalations?
- Published response-time SLAs and documented outcomes: Not marketing claims
- Transparent pricing vs. opaque enterprise quotes: Can you model cost before the first sales call?
- Compliance support included vs. separate add-on: SOC 2, HIPAA, and ISO 27001 reporting should be table stakes, not upsells
🔍 Where Each Provider Fits
Each provider excels in different scenarios. Arctic Wolf works well for organizations wanting single-vendor simplicity and willing to adopt their proprietary stack. CrowdStrike Falcon Complete is strongest in Falcon-native environments where endpoint is the primary telemetry source. Rapid7 offers solid SIEM-MDR convergence with full technology access and extensibility into vulnerability management. UnderDefense fits organizations that want to protect their existing security investments while getting full detection-to-response coverage, vendor-agnostic, with analysts who verify alerts directly with users rather than escalating tickets back to your team.
The right choice depends on your current security investments, team maturity, and operational model.
Credibility Anchor
This analysis is grounded in documented response times, G2 Spring 2025 rankings, published pricing, and operational outcomes across 500+ MDR deployments.
1. What is managed SIEM and how does it differ from running SIEM in-house?
Managed SIEM is a security operations model where a third-party provider handles the deployment, tuning, monitoring, and management of your SIEM platform. This includes log collection, event correlation, detection rule engineering, and incident escalation, so your internal team does not have to build or staff a 24/7 SOC from scratch.
The core difference from in-house SIEM comes down to operational overhead and expertise. Running SIEM internally requires 3 to 5 dedicated FTEs, annual costs of $500K to $2.7M, and a 6 to 12 month deployment timeline. Managed SIEM delivers validated detections within 30 days at a fraction of that cost.
We operationalize your existing SIEM, whether Splunk, Elastic, or another platform, so you retain full ownership of your data and detection logic. The provider supplies the expertise, 24/7 coverage, and continuous tuning that most internal teams cannot sustain.
2. What services should be included in a fully managed SIEM engagement?
A comprehensive managed SIEM engagement should cover seven core service areas:
-
24/7 log monitoring and event correlation
-
Detection engineering and custom rule tuning
-
Threat intelligence integration
-
Human-led alert triage and investigation
-
Compliance reporting and audit evidence generation
-
SIEM platform management (health, performance, storage)
-
Incident escalation with context and response guidance
Many providers bundle only monitoring and platform maintenance, then charge separately for detection engineering, threat hunting, and compliance reporting. We include all seven as standard with every MDR engagement, plus proactive threat hunting and ChatOps user verification. If your provider’s “managed SIEM” stops at log storage and basic alerting, you are paying for a monitoring dashboard, not managed security operations.
3. How much does managed SIEM cost compared to building an in-house SOC?
The cost difference is substantial. A self-managed SIEM with true 24/7 coverage requires a minimum of 5 FTEs across shifts, costing $750K to $1M per year in salary alone. Total operational costs easily hit $2.7M annually when you factor in platform licensing, training, and continuous rule tuning.
Fully managed SIEM runs $60,000 to $180,000 annually, depending on log volume, environment complexity, and service tier. We publish transparent pricing at $11 to $15 per endpoint per month with no hidden fees or opaque enterprise quotes.
Beyond direct cost savings, managed SIEM delivers 60 to 80% operational overhead reduction, faster detection (minutes instead of the 277-day industry average), and continuous compliance evidence generation. For organizations under 5,000 employees, this is typically the more cost-effective path.
4. What is the difference between managed SIEM, MDR, XDR, and MSSP?
These five models overlap but serve distinct purposes:
-
Managed SIEM: Outsourced operation of your SIEM platform, covering log management, detection tuning, and monitoring
-
MDR: Broader detection and response across endpoints, cloud, identity, and network, with active threat containment
-
XDR: Vendor-native platform unifying telemetry across security layers, typically locked to one ecosystem
-
SOC-as-a-Service: Outsourced analyst coverage for monitoring, triage, and escalation
-
MSSP: Legacy model focused on alert forwarding from perimeter devices
The practical question is not “which category do I need” but “can this provider detect threats across my entire stack and respond with context?” We combine managed SIEM operations with full MDR, covering what XDR platforms promise but without vendor lock-in.
5. How does managed SIEM help with SOC 2, HIPAA, and ISO 27001 compliance?
Managed SIEM directly satisfies the continuous monitoring, log retention, and incident detection controls required by major compliance frameworks:
-
SOC 2 CC7.2: Continuous monitoring of security events
-
HIPAA §164.312(b): Audit controls and activity logging
-
ISO 27001 A.12.4: Logging and monitoring
-
PCI DSS Requirement 10: Tracking access to network resources
The operational value extends beyond checkbox compliance. Instead of spending weeks before each audit manually assembling evidence, managed SIEM generates compliance artifacts from the same telemetry used for daily threat detection. We include forever-free compliance kits for SOC 2, ISO 27001, and HIPAA as standard, with audit documentation auto-generated from unified telemetry.
6. What does the onboarding process look like with a managed SIEM provider?
A well-executed managed SIEM onboarding follows three phases:
-
Days 1 to 14 (Discovery & Integration): Toolset audit, log source prioritization, connector deployment, environment baseline profiling, and communication channel setup
-
Days 15 to 30 (Detection Tuning & Noise Reduction): Custom detection rules deployed, false positive suppression targeting 99% noise reduction, MITRE ATT&CK gap analysis, and simulated attack validation
-
Days 31 to 90 (Operational Maturity): Ongoing detection refinement, monthly security posture reviews, tabletop exercises, and full 24/7 monitored state with documented SLAs
We commit to a 30-day turnkey deployment: by Day 30, you have validated detections, confirmed SLAs, and your first monthly security posture report. The industry average is six months. If your provider cannot show documented MITRE ATT&CK coverage and published SLA metrics by Day 90, they are selling monitoring, not managed security.
7. What should security leaders evaluate before choosing a managed SIEM provider?
We recommend scoring each provider on seven criteria (0 to 2 scale, with 11+ indicating a genuine operational partnership):
-
SIEM ownership model (do you retain the platform?)
-
Detection engineering (custom rules or generic templates?)
-
Response capability (containment or just notification?)
-
Alert verification (direct user verification or raw escalation?)
-
Pricing transparency (published or “contact sales”?)
-
Compliance integration (auto-generated evidence or separate project?)
-
Onboarding speed (30 days or 6 months?)
The real question is not “which provider has the most integrations” but “which provider can respond to threats the way a dedicated security team would.” We score 14/14 on this framework because we operate your existing SIEM end-to-end while you retain full ownership.
8. Can we keep our existing SIEM platform with a managed SIEM provider?
Yes, but not all providers support this. Many managed SIEM providers require migration to their proprietary platform, which means you lose years of custom detection tuning, correlation rules, and business logic when you switch.
We built our model specifically to avoid this problem. We operationalize your existing SIEM, whether Splunk, Elastic, or another platform, so you retain full ownership of your data, rules, and institutional knowledge. Our UnderDefense MAXI platform integrates with 250+ existing tools, which means no vendor lock-in, no forced platform migration, and no restarting detection engineering from scratch when the contract comes up for renewal.
This is not just a philosophical stance. It is a lesson learned from watching organizations lose years of custom detection work when switching providers.
The post Managed SIEM Explained: Real Costs, Onboarding Timelines, and Provider Pitfalls appeared first on UnderDefense.