Q1: What Is Managed SIEM Readiness, and Why Should Security Leaders Assess It Now?
The Readiness Gap Nobody Talks About
Managed SIEM readiness is the intersection of organizational, technical, and operational conditions that indicate a company should transition from self-managed, or nonexistent, security monitoring to a managed SIEM service. It is not about whether you want a SIEM. It is about whether your people, processes, and environment can actually operationalize one.
Most mid-market organizations (200–2,000 employees) dramatically overestimate their readiness. SOC teams face an average of hundreds of alerts daily, yet the vast majority lack the minimum staffing needed for effective detection engineering, meaning alerts fire, but nobody is tuning, correlating, or acting on them fast enough. Meanwhile, 65% of security teams report lacking SIEM-specific expertise like log parsing, detection rule tuning, and UEBA configuration.
Having a SIEM Deployed Is Not the Same as Being SIEM-Ready
⚠️ Here is what I have seen happen repeatedly: an organization deploys managed SIEM after a breach or during a failed compliance audit. Emergency deployments mean rushed onboarding, misconfigured log sources, and months of noisy, untuned detection rules before the system delivers real value.
IBM’s 2024 Cost of a Data Breach Report puts the global average breach cost at $4.88 million, a 10% jump from the prior year and the largest annual increase since the pandemic. Organizations without 24/7 security monitoring and AI-driven automation face breach costs roughly 33% higher than those that have invested proactively.
Why Reactive Adoption Costs You 2-3x More
The operational reality is just as painful. Security teams reconfigure broken detection rules constantly, some monthly, proving that even organizations with SIEM often lack the operational maturity to extract value from it. Reactive adoption turns what should be a strategic investment into an expensive fire drill.
The Four-Pillar Assessment Framework
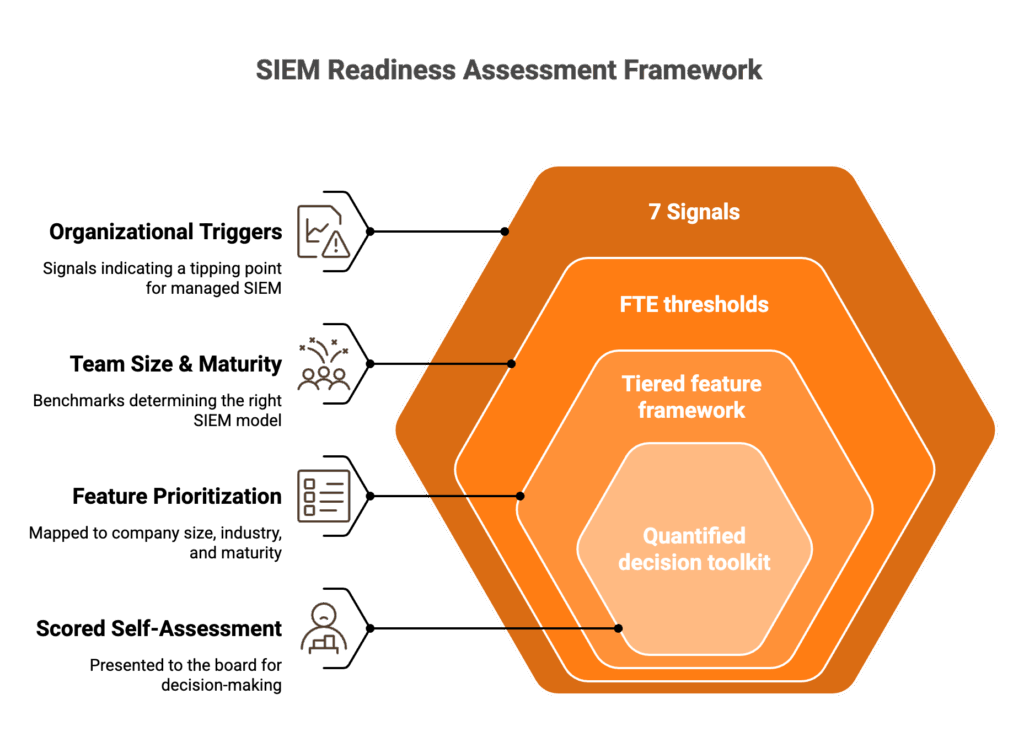
This article introduces a unique four-pillar framework, the only guide combining all four dimensions into one resource:
- Organizational Triggers The 7 signals that indicate your tipping point for managed SIEM.
- Team Size & Maturity Benchmarks FTE thresholds and maturity levels that determine whether in-house, co-managed, or fully managed SIEM is the right model.
- Feature Prioritization by Org Profile A tiered feature framework mapped to your company’s size, industry, and maturity.
- Scored Self-Assessment Checklist A quantified decision toolkit you can present to your board.
Each pillar builds on the previous one. The triggers tell you if you need managed SIEM. The benchmarks tell you which model. The features tell you what to prioritize. And the self-assessment gives you a score you can take to your CFO.
⏰ Where UnderDefense Fits In
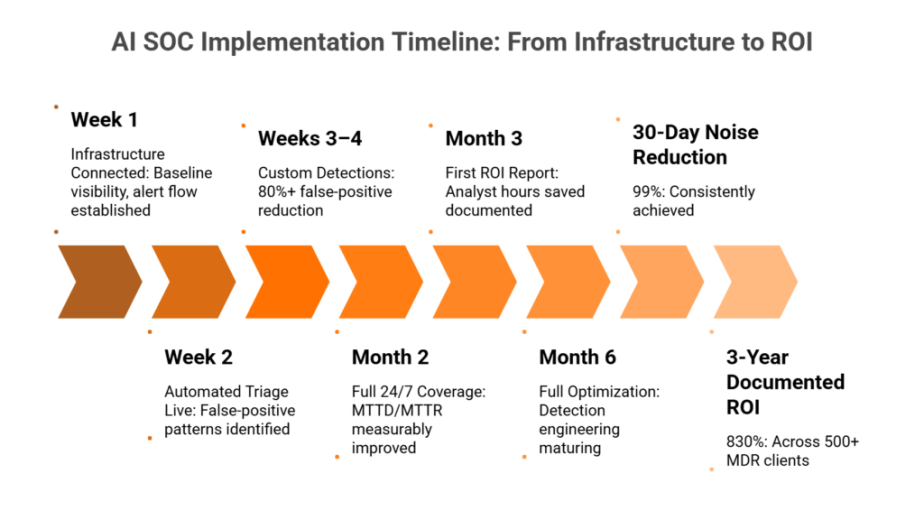
UnderDefense’s 30-day onboarding model and vendor-agnostic UnderDefense MAXI platform were designed around these readiness signals. The platform connects to 250+ existing security tools within the first week, begins 24/7 monitoring in week two, and delivers tuned detection with compliance reporting by day 30, enabling organizations to act on assessment results immediately rather than enduring 6-month deployment cycles typical of legacy SIEM implementations.
The goal here is not to sell you a platform. It is to give you a structured way to figure out if you actually need one, and if so, how to avoid the costly mistakes that come from making that decision reactively.
Q2: What Are the 7 Organizational Triggers That Signal It’s Time for Managed SIEM?
The Scenario That Changes Everything
Your CISO presents to the board after a near-miss phishing incident. The question is not whether the SOC detected it, but why detection took 72 hours and required three analysts working overtime to correlate logs across Splunk, CrowdStrike, and Okta manually. The board asks: Why aren’t we monitoring this 24/7?
This is the moment most organizations realize they need managed SIEM. But the triggers were visible months earlier.
7 Triggers, Quantified
- Recent security incident or near-miss exposing monitoring gaps. Organizations without 24/7 monitoring take significantly longer to identify and contain breaches, with dwell times stretching into months.
- New or tightening compliance mandate. SOC 2 Type II continuous monitoring, HIPAA §164.312 audit controls, PCI-DSS v4.0 requirement 10.4.1 for automated log review, GDPR Article 32, ISO 27001 Annex A.12.4. Compliance is no longer annual, it is continuous, and managed SIEM delivers audit evidence automatically.
- Security team attrition or chronic understaffing. Unfilled security roles open 90+ days and key analyst departures that create permanent knowledge gaps.
- Alert volume exceeding team capacity. Hundreds of daily alerts with less than 50% investigation rate. When your team is triaging noise instead of hunting threats, you are already behind.
- Organizational growth. M&A activity, cloud migration, or remote workforce expansion creating new attack surfaces faster than the team can instrument.
- Budget cycle alignment. A new fiscal year or board-approved security investment creating a window for operational transformation rather than emergency spending.
- Technology stack sprawl. Five or more disconnected security tools without unified correlation, creating “alert islands” where threats hide between tools.
💸 The Hidden Costs of Ignoring Triggers
- Analyst burnout: Average SOC analyst tenure sits around 18 months. Each departure costs $50K–$80K in replacement and ramp-up.
- Compliance fines: $100K–$7.5M for HIPAA violations; €20M or 4% of global revenue for GDPR.
- Breach cost differential: $4.88M average per IBM’s 2024 report, with costs 33% higher for organizations lacking security AI and automation.
- Detection dwell time: Increases dramatically when analysts are overwhelmed with noise, the exact scenario trigger #4 describes.
✅ The UnderDefense Approach
Triggers should activate a structured 30-day transition, not a 6-month emergency project. UnderDefense’s UnderDefense MAXI platform connects to 250+ existing tools within the first week, begins 24/7 monitoring in week two, and delivers tuned detection with compliance reporting by day 30. A documented case study shows how full-spectrum security with SIEM and SOC helped one organization avoid a potential $650K loss.
From 72-hour manual log correlation to real-time unified detection, that is the shift from reactive trigger response to managed SIEM readiness.
“We received little value from ArcticWolf. The product offered little visibility when we were using it… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
“Started out well but over the years the service has consistently not met expectations. The issues that we have experienced has greatly outweighed the benefits… Analysts provide little context, and when asked for more information in the investigation nothing is ever provided.”
— CISO, Manufacturing (3B–10B USD) Arctic Wolf – Gartner Verified Review
“Solid detection and response capabilities, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology, Services Arctic Wolf – Gartner Verified Review
Q3: How Many Security FTEs Do You Need, and What Maturity Level Indicates Managed vs. In-House SIEM?
The Decision Dilemma
Two questions determine your SIEM operating model: Do you have enough people? and Are your processes mature enough to operationalize a SIEM investment? Most organizations overestimate both. Only a small fraction maintain the minimum 4+ FTEs needed for detection engineering alone, and teams frequently reconfigure broken detection rules monthly, indicating even well-staffed teams lack operational maturity.
Framework A: FTE Staffing Thresholds
Running in-house SIEM effectively requires 6–10 dedicated security FTEs: 2–3 analysts for true 24/7 shift coverage, 1 detection engineer, 1 SIEM administrator, 1 threat hunter, plus management oversight. A single Tier 2 SOC analyst costs $85K–$120K/year (US), meaning 24/7 coverage alone requires 4.5 FTEs minimum at $380K–$540K annually, before SIEM licensing ($50K–$300K), infrastructure, and training.
| Security FTE Count | Recommended SIEM Model |
|---|---|
| <3 FTEs | ✅ Fully Managed SIEM |
| 3–6 FTEs | ✅ Co-Managed SIEM (retain control, offload 24/7 monitoring) |
| 7+ FTEs with dedicated SIEM engineer | ⚠️ In-House SIEM viable, but still costly |
The skills dimension matters equally: 65% of security teams lack SIEM-specific expertise (log parsing, detection rule tuning, UEBA configuration). You need both headcount and expertise. If either falls below threshold, managed SIEM is indicated.
Framework B: Maturity-to-Action Matrix
| Maturity Level | Description | Recommended Model |
|---|---|---|
| Level 1: Reactive/Ad-Hoc | No dedicated security staff, basic antivirus, log review only after incidents | ✅ Fully Managed SIEM |
| Level 2: Developing | 1–3 security staff, basic SIEM deployed but underutilized, compliance-driven | ✅ Fully Managed SIEM |
| Level 3: Defined/Proactive | 4–6 security staff, documented processes, active monitoring during business hours | ✅ Co-Managed SIEM |
| Level 4: Optimized/Predictive | 7+ security staff with SIEM engineer, 24/7 SOC, active threat hunting | ⚠️ In-House SIEM viable |
⚠️ Key Insight
If your team spends >60% of time on reactive alert triage rather than proactive threat hunting, you are Level 1–2 regardless of headcount. If unfilled security roles have been open >90 days, deduct one level from your self-assessment. Most mid-market organizations (200–2,000 employees) realistically operate at Level 1–2.
Applying Both Frameworks Together
Cross-reference your FTE count with your maturity level. An organization with 5 FTEs (suggesting co-managed) but operating at Level 2 maturity (suggesting fully managed) should default to fully managed with a maturity roadmap to co-managed within 12–18 months. The lower score wins, because understaffed teams with immature processes trying to co-manage a SIEM burn out faster than teams with no SIEM at all.
How UnderDefense Bridges the Gap
UnderDefense provides Tier 3–4 analyst coverage, detection engineering, and SIEM administration as a service, effectively delivering 8–12 FTEs of security operations capability through the UnderDefense MAXI platform. The documented case study of a German healthcare leader scaling its IT security team with UnderDefense MDR demonstrates this model in practice.
Persona examples: A 200-employee fintech with 2 security analysts → Fully managed, compliance-first. A 1,000-employee healthcare org with an 8-person SOC → Co-managed, augmenting the existing team.
“There has been some shift in the thoroughness or evidence of human analysis prior to escalation… automation capabilities often fall short of correlating with concurrent or historic activity, which is often a rich source of context.”
— Verified User, Computer Software, Mid-Market Expel – G2 Verified Review
“The pre-sales crew is great. Really make you think you’ll get high tier support… The scan engine doesn’t function. I’m unable to scan our IP ranges, and they’ve ignored requests to get this resolved.”
— Verified User, Farming, Mid-Market Rapid7 – G2 Verified Review
Q4: What Must-Have Features Should You Prioritize in Managed SIEM, Based on Your Organization’s Profile?
Tier 1: Non-Negotiable Features
These are baseline requirements for any managed SIEM, regardless of organization size:
- 24/7/365 real-time monitoring and alerting with defined SLAs, not business-hours-only coverage.
- Log collection and correlation across hybrid environments, cloud, on-prem, SaaS, and identity all feeding into a single detection layer.
- Compliance reporting automation for SOC 2, HIPAA, PCI-DSS, ISO 27001, and GDPR. Evidence generation should not be manual spreadsheet work.
- Vendor-agnostic integration with your existing security stack (EDR, identity, cloud, network), no rip-and-replace requirements.
- Documented SLAs for detection and response times (MTTD/MTTR). If a provider cannot publish specific numbers, that tells you something.
- Dedicated analyst access, direct communication with security engineers, not just ticket-based support queues.
Tier 2: High-Value Differentiators
These features separate adequate managed SIEM from excellent:
- UEBA (User and Entity Behavior Analytics) for insider threat and compromised account detection.
- SOAR integration for automated response playbooks that contain threats in minutes, not hours.
- Threat intelligence feeds integrated directly into detection logic, not a separate dashboard.
- Custom detection rule development and continuous tuning by the provider’s engineering team.
- Direct user verification via ChatOps (Slack, Teams, email) to close false positives without escalating back to your team.
Tier 3: Advanced Capabilities
For mature organizations or PE portfolio use cases:
- Detection-as-code with version control, enabling reproducible, auditable detection engineering.
- Multi-tenancy for PE portfolio or multi-business-unit organizations.
- Proactive threat hunting beyond alert-driven detection.
- API-first architecture for custom integrations.
- Compliance evidence auto-generation for multiple frameworks simultaneously.
Persona-Based Prioritization Matrix
| Org Profile | Size / Team | Priority Features |
|---|---|---|
| 🏥 Small team / high compliance (fintech, healthcare <500 employees, 1–3 FTEs) | <500 employees | Tier 1 + compliance automation + vendor-agnostic integration. Do not over-invest in SOAR or detection-as-code yet. |
| 🚀 Mid-market / scaling fast (SaaS 500–1,500 employees, post-Series B/C) | 500–1,500 employees | Tier 1 + UEBA + ChatOps verification + threat hunting. Alert volume is your bottleneck. |
| 💼 PE portfolio / multi-entity | Multiple companies | Multi-tenancy + unified compliance reporting + transparent per-endpoint pricing. One platform across portfolio companies. |
| 🛡️ Mature SOC / augmentation (7+ FTEs) | 1,000+ employees | Co-managed model with detection-as-code + API integration + custom rule development. |
How UnderDefense Covers All Three Tiers
The UnderDefense MAXI platform delivers across all three feature tiers, including ChatOps user verification (Tier 2, unique to UnderDefense among managed SIEM providers) and proactive threat hunting with 96% MITRE ATT&CK coverage (Tier 3). Transparent pricing at $11–$15/endpoint/month scales predictably across all profiles without hidden costs or forced tool replacement.
For security leaders building a vendor shortlist, map your organization to one of the four profiles above, then use the tiered feature list as your evaluation checklist. Any provider that cannot deliver Tier 1 completely should not make the cut, regardless of brand recognition or market share.
Q5: Managed SIEM vs. In-House SIEM vs. Co-Managed: Which Model Fits Your Organization?
The managed vs. in-house vs. co-managed decision is not just about budget. It is about operational reality. Each model trades off control, cost, and capability differently. Choosing wrong either burns out your team or limits your visibility. Here is how to think through it clearly.
⚠️ The In-House SIEM Reality
Running SIEM in-house gives you full control over detection logic, deep customization, and institutional knowledge retention. That is the upside. The downside is brutal: you need 6 to 10 security FTEs to sustain true 24/7 coverage, because a single reliable seat filled around the clock requires 8 to 12 analysts. Tier 1 analysts cost $55K to $70K, Tier 2 runs $70K to $95K, and Tier 3 hits $90K to $120K+. Add SIEM licensing ($50K to $300K/year for platforms like Splunk or Elastic), and you are looking at $500K to $1.2M annually before you have tuned a single detection rule.
Deployment timelines compound the problem. Enterprise-wide SIEM implementations span 6 to 12 months for full optimization, with roughly 20% of companies taking 12+ months just to reach viability. That is not time-to-value, but time-to-frustration. Best fit: Level 4 maturity organizations with 7+ dedicated security FTEs and a SIEM engineer who lives and breathes detection engineering.
✅ The Managed SIEM Approach
Managed SIEM flips the equation: you get 24/7 coverage from day 30, Tier 3 to 4 analyst access, compliance automation included, and predictable per-endpoint pricing. The tradeoff is less direct control over detection logic, but a good provider mitigates that with transparency and collaboration.
Here is where most managed providers fall short, though. Traditional MSSPs give you monitoring without actionable context, offering checkbox coverage driven by rigid playbooks. And proprietary MDR providers like Arctic Wolf force you to abandon your existing SIEM investment entirely.
“We received little value from ArcticWolf. The product offered little visibility… Anything you want to look at or changes you need to make in the product must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
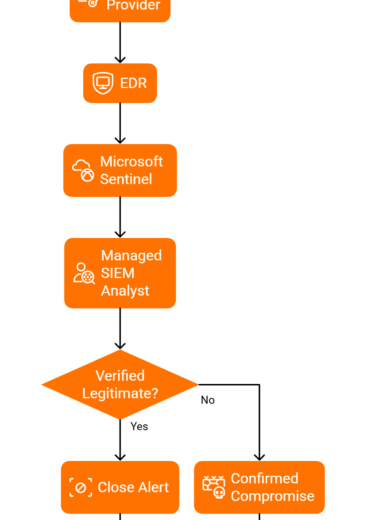
UnderDefense takes a structurally different approach. We integrate with 250+ existing tools, including CrowdStrike, Splunk, SentinelOne, and Microsoft Sentinel, without forcing replacement. Pricing is transparent at $11 to $15/endpoint/month. And our concierge analysts do not just escalate alerts. They verify suspicious activity directly with affected users via Slack or Teams, then contain threats with full remediation through the UnderDefense MAXI platform.
📊 Side-by-Side Comparison
| Dimension | In-House SIEM | Fully Managed (UnderDefense) | Co-Managed (UnderDefense) |
|---|---|---|---|
| 💰 Annual Cost | $500K–$1.2M+ | $11–$15/endpoint/month | Custom (hybrid pricing) |
| FTEs Required | 6–10 | 0 (dedicated analysts included) | 4–6 (your team + UD analysts) |
| ⏰ Time-to-Value | 6–12 months | 30 days | 30–45 days |
| 24/7 Coverage | Self-staffed | ✅ Included | ✅ After-hours covered |
| Compliance Automation | Build it yourself | ✅ Forever-free kits included | ✅ Included |
| Response Capability | Depends on team | ✅ Full containment + remediation | ✅ Shared response model |
| Customization Depth | Full control | High (collaborative tuning) | Full (you retain detection logic) |
| Vendor Lock-in | Tool-dependent | ❌ None (vendor-agnostic) | ❌ None |
🎯 Which Model Should You Choose?
- Choose in-house if you have 7+ FTEs, a dedicated SIEM engineer, $500K+ annual budget, and Level 4 maturity.
- Choose fully managed if you have <6 FTEs or need 24/7 coverage within 30 days without building a SOC from scratch.
- Choose co-managed if you have 4 to 6 FTEs and want to retain control over detection logic while offloading after-hours monitoring, alert triage, and incident response.
“UnderDefense has changed our approach to cybersecurity. At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it.”
— Yaroslava K., IT Project Manager UnderDefense G2 – Verified Review
Q6: The Scored Self-Assessment Checklist: How Ready Is Your Organization for Managed SIEM?
Score your organization across these 4 categories (20 items total, 1 point each) to determine your managed SIEM readiness level. Be honest. This assessment only works if you answer based on current reality, not aspirational plans.
📋 Category A: Operational Triggers (5 Items)
- ☐ Security incident or near-miss in the past 12 months
- ☐ Upcoming or active compliance audit (SOC 2, HIPAA, ISO 27001, PCI DSS)
- ☐ Alert volume exceeds 100/day across your security tools
- ☐ Unfilled security roles open for 90+ days (84% of organizations report difficulty recruiting cybersecurity professionals)
- ☐ 5+ disconnected security tools without unified log correlation
📋 Category B: Team Capacity (5 Items)
- ☐ Fewer than 4 security FTEs total
- ☐ No dedicated SIEM engineer or detection engineer on staff
- ☐ No true 24/7/365 monitoring coverage, with gaps on nights, weekends, and holidays
- ☐ >60% of analyst time consumed by reactive alert triage rather than strategic work
- ☐ Security analyst turnover within the past 12 months
📋 Category C: Technical Readiness (5 Items)
- ☐ No unified log correlation across endpoint + cloud + identity sources
- ☐ Compliance evidence gathering for audits is manual and time-consuming
- ☐ No UEBA or behavioral analytics capability deployed
- ☐ No automated response playbooks (SOAR), meaning containment actions are manual
- ☐ Detection rules not reviewed or tuned in 6+ months
📋 Category D: Business Drivers (5 Items)
- ☐ Board or C-suite actively asking about security posture and cyber risk
- ☐ Upcoming M&A, cloud migration, or rapid headcount scaling
- ☐ Cyber insurance provider requiring enhanced monitoring controls
- ☐ Compliance obligations span 2+ frameworks simultaneously (e.g., SOC 2 + HIPAA)
- ☐ Current security spend feels reactive rather than strategic
📊 Score Interpretation
| Score | Readiness Level | What It Means |
|---|---|---|
| 0–6 ✅ | Low Urgency | Monitor quarterly. Begin internal capability planning and gap assessment. |
| 7–12 ⚠️ | Moderate Readiness | Begin vendor evaluation now. Target a 90-day transition plan. |
| 13–17 ⭐ | High Readiness | Managed SIEM is operationally critical. Target 30 to 60 day deployment. |
| 18–20 ❌ | Urgent Action Required | Security gaps are actively creating breach and compliance risk. Every week without managed SIEM increases exposure. |
How UnderDefense Closes the Gap
If you scored 13+, UnderDefense’s 30-day onboarding addresses exactly this urgency. UnderDefense MAXI connects to your existing tools in week 1, begins 24/7 monitoring in week 2, and delivers tuned detection with compliance reporting by day 30. Most teams go from 2 to 3 checks to 17+ within the first month.
The average data breach now costs $4.88 million. That is not a theoretical number, but lost business, regulatory fines, and customer attrition combined. The scored gap between your current state and managed coverage represents real financial exposure, every single day.
Scored 7+? Use the SOC Cost Calculator to model the financial impact, or book a 15-minute security gap assessment to map your results to an action plan.
Q7: What Objections Delay the Managed SIEM Decision, and How Do You Address Them Internally?
Even when the self-assessment score says “act now,” internal resistance slows everything down. Here are the four objections I hear most often, along with the data-backed responses security leaders can take straight to their CFO or board.
❌ Objection 1: “We Already Invested Heavily in Our SIEM/EDR Stack”
This is the single most common concern, especially from organizations that spent $100K to $300K on Splunk, Elastic, or Microsoft Sentinel licensing. Totally fair. Nobody wants to feel like they are throwing money at redundancy.
Here is the reality: managed SIEM does not replace your investment. It operationalizes it. Most internal teams lack the bandwidth for 24/7 monitoring, continuous detection tuning, and incident response across the full stack. UnderDefense integrates with 250+ existing tools, including Splunk, Elastic, Sentinel, and CrowdStrike, providing the analyst coverage and detection engineering your tools need to actually deliver ROI.
“We were looking for an MDR provider and were choosing EDR tools. CrowdStrike was our favorite choice, but after a few calls with UnderDefense we realized that we could get way more value.”
— Oleksii M., Mid-Market UnderDefense G2 – Verified Review
❌ Objection 2: “We’ll Lose Control and Visibility”
Control anxiety is legitimate. Legacy MSSPs earned this skepticism with their black-box portals and ticket-based escalation queues where context goes to die.
The resolution: co-managed models preserve control. With UnderDefense, you see every alert, every response action, and every detection rule in the UnderDefense MAXI console. Concierge analysts communicate via your Slack or Teams channels, not behind a gated portal. You retain veto power over response actions for any category you choose. This is not outsourcing your security. It is extending your team with analysts who know your environment.
“This is not an extension of our security team as was originally sold.”
— Sr. Cybersecurity Engineer, Manufacturing Arctic Wolf – Gartner Peer Review
That is the trap with opaque providers. UnderDefense’s “show, don’t tell” model means you can audit every workflow yourself.
💰 Objection 3: “The ROI Is Hard to Justify to the CFO/Board”
Security ROI is notoriously hard to quantify. Here is a framework that works: cost avoidance + cost comparison.
- Managed SIEM: $11 to $15/endpoint/month
- In-house 24/7 SOC: 8 to 12 FTEs at $55K to $120K each = $440K to $1.44M/year in salaries alone
- SIEM licensing: $50K to $300K/year additional
- Breach cost avoidance: $4.88M average per IBM’s 2024 report
Frame it this way: managed SIEM at ~$132K/year (for 1,000 endpoints) vs. $750K+ for a bare-minimum in-house SOC, before SIEM licensing, recruiting fees, or turnover costs. Use the SOC Cost Calculator to build the exact model for your board deck.
❌ Objection 4: “We’re Not Big Enough or Mature Enough for SIEM Yet”
This was true when SIEM meant $500K deployments and 6 to 12 month implementations. It is no longer true.
Modern managed SIEM deploys in 30 days with transparent per-endpoint pricing, with no minimum thresholds, no forced tool replacement, and no professional services fees. If you have compliance obligations and digital assets to protect, you are big enough. Reference the maturity framework from the earlier section. Level 1 to 2 organizations are precisely who managed SIEM is designed for.
“Building our cybersecurity from scratch felt like a daunting challenge. Enter UnderDefense MAXI and its 30-day impact report… For a marketing agency taking baby steps in security, these reports were our guiding star.”
— Val R., Small Business UnderDefense G2 – Verified Review
Q8: How to Evaluate Managed SIEM Providers Once You’ve Confirmed Readiness
Once your self-assessment confirms readiness (score 7+), evaluation becomes a structured comparison across 5 architectural criteria, not a feature checklist or brand-recognition contest.
🔍 5 Vendor Selection Criteria That Actually Matter
- Integration Approach: Does the provider work with your existing stack (SIEM, EDR, cloud, identity), or does it force proprietary tool replacement? Vendor-agnostic flexibility protects your investments. Proprietary lock-in means starting over.
- Response Capability: Can the provider contain and remediate threats (revoke credentials, isolate endpoints, block lateral movement), or does it stop at detection and escalate back to your team? Detection without response is just expensive alerting.
- Analyst Access Model: Do you get direct communication with Tier 3 to 4 analysts via Slack/Teams, or are you stuck in ticket-based support queues? The difference between “here’s more work for you” and “here’s the answer” comes down to analyst access.
- Pricing Transparency: Are rates published and predictable (per-endpoint, per-month), or hidden behind “contact sales” pages? Arctic Wolf’s median annual contract runs ~$96K with no published per-endpoint rates. UnderDefense publishes $11 to $15/endpoint/month.
- Time-to-Value: Does deployment take 30 days or 6+ months? Every week without coverage is exposure. If onboarding requires stack migration, budget for 3 to 6 months of vulnerability.
The Architectural Difference
Each criterion reveals a different architectural philosophy. The right provider depends on your current stack, team maturity (use the framework from earlier sections), and compliance requirements.
For detailed provider comparisons with pricing, response times, and integration capabilities, including head-to-head breakdowns of UnderDefense, Arctic Wolf, CrowdStrike, Expel, and Red Canary, see the full analysis below.
Use the SOC Cost Calculator to model your exact managed vs. in-house cost comparison before the first vendor call.
Credibility Anchor
This evaluation framework is based on documented response times, G2 Spring 2025 rankings (where UnderDefense earned 12 badges including Best Support), published pricing data, and operational outcomes across 500+ managed security deployments.
Q9: How Does the AI SOC + Human Ally Model Redefine What Managed SIEM Can Deliver?
Here is the uncomfortable truth about most managed SIEM deployments: they have become expensive log storage with a compliance label slapped on top. Organizations collect data across CrowdStrike, Splunk, Okta, and a dozen cloud consoles, but without 24/7 analyst coverage and continuous detection engineering, those logs sit in a warehouse gathering digital dust. The SIEM becomes an audit artifact, not a security multiplier.
❌ The “Alert Forwarding” Trap
Traditional MSSPs and monitoring-only MDR providers stop at detection and notification. Arctic Wolf and ReliaQuest forward alerts to your team with “please investigate” tickets, meaning you still need analysts to triage, verify, and respond. You are paying for alert forwarding, not managed security operations.
CrowdStrike Falcon Complete limits you to their proprietary ecosystem. The result: vendor lock-in or alert fatigue, pick your poison.
“Started out well but over the years the service has consistently not met expectations. The issues that we have experienced has greatly outweighed the benefits.”
— CISO, Manufacturing ($3B–$10B) Arctic Wolf – Gartner Verified Review
⚡ The AI-Era Transformation
The managed SIEM category has evolved beyond monitoring + alerting to detection + verification + response in a single workflow. AI-driven correlation across all telemetry, including endpoint, identity, cloud, and network, combined with human analysts who verify alerts with affected users and contain threats immediately. Detection without response is noise. Response without context is risk. The new standard is an AI SOC with a Human Ally, a system that reasons across your tools and acts on your behalf.
✅ UnderDefense’s AI SOC + Human Ally
This is what we built the UnderDefense MAXI platform to deliver, and it is the operational philosophy that drives everything at UnderDefense:
- Vendor-agnostic integration with 250+ tools, no forced replacement of your existing stack
- AI-driven correlation and enrichment across all telemetry with 98% verdict accuracy
- Proactive threat hunting with 96% MITRE ATT&CK coverage
- ChatOps user verification via Slack/Teams/email, confirming suspicious activity directly with affected users
- Full containment and remediation, including credential revocation, endpoint isolation, and lateral movement blocking
- 💰 $11–$15/endpoint/month transparent pricing, 30-day onboarding, and forever-free compliance kits (SOC 2, ISO 27001, HIPAA)
Stop renting alert dashboards. Start hiring an AI SOC with a dedicated security ally.
“Their expert management of our SIEM has added to the value of our security investments and tools… UnderDefense has changed our approach to cybersecurity.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
“Being a digital marketing company, we’re all about swift communication. UnderDefense MAXI’s MDR and especially their incident response capabilities are top-tier. But the real game-changer is their seamless integration with Slack.”
— Alexander B., CEO UnderDefense – G2 Verified Review
⭐ The Proof
UnderDefense detected and contained threats 2 days faster than CrowdStrike OverWatch in documented case studies, maintaining a 100% ransomware prevention record across 500+ MDR clients over 6 years. The UnderDefense MAXI platform holds 4.9/5.0 on G2 with 12 badges in MDR, Incident Response, and System Security (Spring 2025).
👉 Book a demo to see the UnderDefense MAXI platform in action, or use the SOC Cost Calculator to model your ROI before you commit, because we expect you to validate before you decide.
1. What are the clearest signs that my organization needs managed SIEM?
We see six consistent organizational triggers that signal managed SIEM readiness. First, a security incident or near-miss within the past 12 months exposes operational gaps that reactive tools cannot close. Second, upcoming compliance audits for SOC 2, HIPAA, ISO 27001, or PCI DSS create urgency around continuous monitoring and audit evidence. Third, alert volumes exceeding 100 per day across your security tools overwhelm teams without unified correlation. Fourth, unfilled security roles open for 90 or more days indicate you are fighting a talent market where 84% of organizations struggle to recruit cybersecurity professionals. Fifth, running five or more disconnected security tools without unified log correlation creates blind spots that attackers exploit. Sixth, when more than 60% of analyst time goes to reactive alert triage instead of strategic work, your team is drowning in noise instead of defending. If three or more of these apply, we recommend beginning vendor evaluation immediately. Our scored self-assessment checklist helps you quantify your exact readiness level across 20 operational criteria.
2. How many security FTEs do I need before considering managed SIEM vs. building in-house?
Running SIEM in-house with true 24/7 coverage requires 6 to 10 security FTEs, because a single reliable seat filled around the clock demands 8 to 12 analysts when accounting for shifts, PTO, and turnover. Tier 1 analysts cost $55K to $70K, Tier 2 runs $70K to $95K, and Tier 3 hits $90K to $120K or more. Add SIEM licensing at $50K to $300K per year for platforms like Splunk or Elastic, and you are looking at $500K to $1.2M annually before tuning a single detection rule. In contrast, organizations with fewer than 6 FTEs are strong candidates for fully managed SIEM, while teams with 4 to 6 FTEs often benefit from a co-managed model that retains internal detection logic ownership while offloading after-hours monitoring and incident response. We publish transparent pricing at $11 to $15 per endpoint per month through UnderDefense MAXI, with no minimum thresholds or forced tool replacement.
3. What must-have features should I prioritize when evaluating managed SIEM providers?
We recommend evaluating managed SIEM providers across five architectural criteria that separate genuine security operations from expensive alerting services.
-
Integration approach: Does the provider work with your existing stack, including SIEM, EDR, cloud, and identity tools, or force proprietary replacement? Vendor-agnostic flexibility protects your investments.
-
Response capability: Can the provider contain and remediate threats, such as revoking credentials, isolating endpoints, and blocking lateral movement, or does it stop at detection and escalate back to your team?
-
Analyst access model: Do you get direct communication with Tier 3 to 4 analysts via Slack or Teams, or are you stuck in ticket-based support queues?
-
Pricing transparency: Are rates published and predictable per endpoint per month, or hidden behind “contact sales” pages?
-
Time-to-value: Does deployment take 30 days or 6 or more months?
Our SIEM Buyers Guide provides a detailed evaluation framework across all five criteria with scoring methodology.
4. How does managed SIEM compare to in-house SIEM and co-managed models?
Each model trades off control, cost, and capability differently, and choosing wrong either burns out your team or limits your visibility.
In-house SIEM gives you full control over detection logic and deep customization but requires 6 to 10 FTEs, $500K to $1.2M annual spend, and 6 to 12 months for full optimization. Best for Level 4 maturity organizations with 7 or more dedicated security FTEs.
Fully managed SIEM delivers 24/7 coverage from day 30, Tier 3 to 4 analyst access, and compliance automation at predictable per-endpoint pricing. Best for organizations with fewer than 6 FTEs or those needing rapid deployment without building a SOC from scratch.
Co-managed SIEM preserves your team’s control over detection logic while offloading after-hours monitoring, alert triage, and incident response. Best for teams with 4 to 6 FTEs who want a hybrid approach.
We offer both fully managed and co-managed models through UnderDefense’s managed SIEM service, integrating with 250 or more existing tools without forcing replacement.
5. How do I justify managed SIEM ROI to my CFO or board of directors?
We recommend framing the business case around cost avoidance plus cost comparison, which is the language CFOs understand.
-
Managed SIEM cost: $11 to $15 per endpoint per month, which translates to approximately $132K per year for 1,000 endpoints.
-
In-house 24/7 SOC cost: 8 to 12 FTEs at $55K to $120K each equals $440K to $1.44M per year in salaries alone, plus $50K to $300K per year in SIEM licensing.
-
Breach cost avoidance: The average data breach now costs $4.88M per IBM’s 2024 report, encompassing lost business, regulatory fines, and customer attrition.
Frame it this way: managed SIEM at roughly $132K per year versus $750K or more for a bare-minimum in-house SOC, before recruiting fees or turnover costs. Use our SOC Cost Calculator to build the exact model for your board deck with your organization’s specific endpoint count and compliance requirements.
6. Can I keep my existing security tools if I switch to managed SIEM?
Yes, and this is one of the most important questions to ask any managed SIEM provider. Many providers, including Arctic Wolf, require you to abandon your existing SIEM and security tools entirely and adopt their proprietary stack. This means writing off $100K to $300K in prior investments and starting from scratch.
We built UnderDefense to work the opposite way. Our UnderDefense MAXI platform integrates with 250 or more existing tools, including CrowdStrike, Splunk, SentinelOne, Microsoft Sentinel, Elastic, and Okta, without forcing replacement. We provide the analyst coverage and detection engineering your tools need to actually deliver ROI. Think of it this way: managed SIEM does not replace your investment, it operationalizes it. You keep your tooling, we add the 24/7 human intelligence, continuous tuning, and incident response capability that makes your existing stack effective.
7. How long does managed SIEM take to deploy and reach full operational value?
Deployment timelines vary dramatically between in-house and managed approaches, and every week without coverage represents real financial exposure.
In-house SIEM implementations typically span 6 to 12 months for full optimization, with roughly 20% of companies taking 12 or more months just to reach viability. That delay is not time-to-value, but time-to-frustration.
With UnderDefense, our managed SIEM onboarding follows a structured 30-day deployment timeline. UnderDefense MAXI connects to your existing tools in week 1, begins 24/7 monitoring in week 2, and delivers tuned detection with compliance reporting by day 30. Co-managed deployments typically reach full operational value within 30 to 45 days. Most teams go from 2 to 3 checklist items to 17 or more within the first month, as measured by our scored self-assessment framework.
8. What is the AI SOC with Human Ally model, and why does it matter for managed SIEM?
The AI SOC with Human Ally model represents the next evolution of managed SIEM, moving beyond traditional monitoring plus alerting to detection plus verification plus response in a single workflow.
Traditional MSSPs and monitoring-only MDR providers stop at detection and notification. They forward alerts to your team with “please investigate” tickets, meaning you still need analysts to triage, verify, and respond. You are paying for alert forwarding, not managed security operations.
The AI SOC model combines AI-driven correlation across all telemetry, including endpoint, identity, cloud, and network, with human analysts who verify alerts directly with affected users via Slack or Teams and contain threats immediately. Detection without response is noise. Response without context is risk.
At UnderDefense, this philosophy drives the UnderDefense MAXI platform: 98% verdict accuracy through AI enrichment, proactive threat hunting with 96% MITRE ATT&CK coverage, ChatOps user verification, and full containment including credential revocation and endpoint isolation. We detected threats 2 days faster than CrowdStrike OverWatch in documented case studies, maintaining a 100% ransomware prevention record across 500 or more MDR clients.
The post When to Get Managed SIEM: The 20-Point Readiness Checklist appeared first on UnderDefense.