Q1: Why Is 2026 a Turning Point for SIEM and Security Operations?
The Fragmented Security Reality
The numbers are impossible to ignore. The global modern SIEM market is projected to grow from $7.13 billion in 2024 to $13.55 billion by 2029, a 13.7% CAGR, driven by AI, cloud-native platforms, and rising cyber threats. Security budgets are increasing. Yet SOC teams are drowning. The typical enterprise runs CrowdStrike for endpoints, Splunk for logs, Okta for identity, and separate cloud consoles, creating alerts everywhere, understanding nowhere. Meanwhile, ISC2’s 2025 Cybersecurity Workforce Study found that 72% of respondents agree reducing security personnel significantly increases breach risk, with a global workforce gap of 4.8 million unfilled positions. The paradox is real: more spending, more tools, more noise, and breaches that still take too long to detect and contain. 2026 is the year incremental improvements stop working.
⚠️ The “Black Box Escalation” Trap
Legacy SIEM, built on log storage, rule-based alerts, and manual investigation, cannot match AI-armed attackers operating at machine speed. Traditional MDR providers like Arctic Wolf and ReliaQuest operate as opaque alert factories: they scale noise, not protection. They offer alert volume without organizational context. Simultaneously, traditional MSSPs deliver monitoring without intelligence, checkbox coverage based on rigid playbooks. And with 4.8 million cybersecurity roles unfilled globally, the structural reality is brutal: you cannot hire your way out of a manual SOC model.
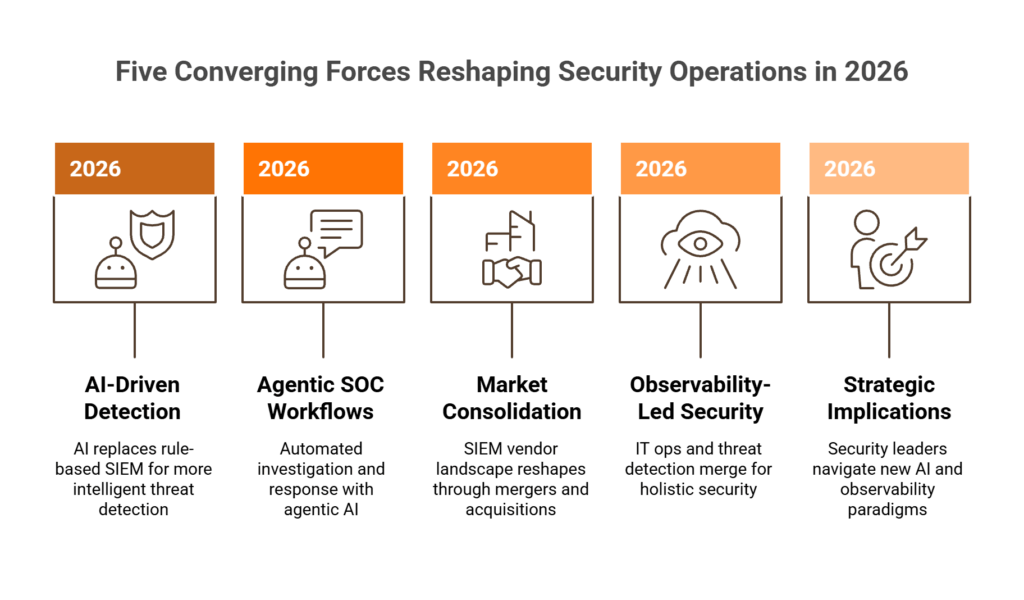
Five Converging Forces
This article maps five interconnected shifts reshaping security operations in 2026:
- AI-driven detection replacing rule-based SIEM
- Agentic SOC workflows automating investigation
- Market consolidation reshaping the vendor landscape
- Observability-led security merging IT ops with threat detection
- Strategic implications for security leaders navigating this transition
These forces are not isolated trends. They are converging simultaneously. As we see at UnderDefense every day: “Threat actors have already weaponized agentic AI, and they’re moving faster than most defenders realize. The question is not whether you need AI in your SOC, but whether your AI can match what threat actors are already using against you”.
The “AI SOC + Human Ally” Model
Here’s the operational reality: detection without response is noise. Response without context is risk. The competitive advantage in 2026 is not more tools, but a system that can reason across them.
The best SOC combines AI-speed investigation with human-led decision-making. From our experience building and running security operations across hundreds of environments: “I just can’t automate everything. I can’t get to a fully lights-out automated security stack because we always run into situations that need human analysis… It can’t just be humans and it can’t just be automation technologies. Got to have both to get to a resilient solution”. This is the model UnderDefense MAXI AISOC embodies: AI collects context, you decide.
What This Article Covers
This article maps the five forces reshaping SIEM and security operations in 2026, with specific guidance for CISOs, SOC Managers, and Security Engineers on how to navigate them without ripping out existing investments or betting on the wrong vendor in a consolidation wave.
Q2: How Is AI-Driven Detection Replacing Rule-Based SIEM, and Is SIEM Dead or Evolving?
SIEM is not dead. It is undergoing its most significant architectural transformation since its creation. The modern SIEM market is projected to grow from $7.13B (2024) to $13.55B by 2029 at 13.7% CAGR. What’s dying is legacy SIEM as passive log storage. What’s emerging is SIEM as an AI-powered security intelligence platform, converging with XDR, SOAR, and observability into a unified detection-investigation-response layer.
AI-Native Detection vs. Rule-Based Correlation
Traditional SIEM relied on predefined correlation rules and signature matching: “if X + Y within Z seconds, fire alert.” This breaks at scale. Rule libraries become unwieldy, novel attack patterns evade signatures, and false positive rates become unsustainable. AI-native SIEM uses behavioral analytics (UEBA) to establish baselines per user and entity, ML models to correlate across endpoint/identity/cloud/network telemetry, and natural language querying for investigation.
| Dimension | Rule-Based SIEM | AI-Native SIEM |
|---|---|---|
| Detection Model | Predefined correlation rules | Behavioral analytics + ML |
| False Positive Rate | High (80%+) | Significantly reduced |
| Novel Threat Coverage | ❌ Limited to known signatures | ✅ Detects anomalous behavior |
| Analyst Workload | Heavy, manual triage | Reduced, automated context |
| Time-to-Detect | Hours to days | Minutes |
| MITRE ATT&CK Coverage | Partial | 96%+ for best systems |
SIEM Architecture Evolution: From Log Warehouse to “SIEM as a Lens”
Three architectures are emerging in 2026:
- Cloud-Native SIEM (Microsoft Sentinel, Google SecOps): Elastic compute, pay-per-ingestion, born-in-cloud analytics. Cloud SIEM revenue is projected to expand at 17.5% CAGR vs. just 3.4% for on-premises solutions.
- Federated SIEM / Security Data Mesh: Query data where it lives rather than centralizing all logs, reducing ingestion costs and data sprawl.
- “SIEM as a Lens”: Viewing security data through an intelligence layer rather than storing everything centrally.
The convergence is real: SIEM + XDR + SOAR are collapsing into unified platforms. Microsoft Sentinel integrates with Defender. Palo Alto absorbed IBM QRadar SaaS customers into Cortex XSIAM. Google expanded Chronicle into Google SecOps. This is not SIEM dying. It is SIEM becoming the orchestration layer for all security telemetry.
✅ OCSF and Open Standards as AI Enablers
AI-driven detection only works when data is normalized across sources. The Open Cybersecurity Schema Framework (OCSF), now under the Linux Foundation, provides vendor-agnostic data standardization, enabling federated search, cross-platform correlation, and portable detection rules regardless of which SIEM you run. This is the structural enabler for both AI detection quality and vendor flexibility.
We built UnderDefense MAXI AISOC on this principle: working with existing SIEMs (Splunk, Sentinel, Chronicle) rather than replacing them, automating investigation across any normalized telemetry source, and delivering structured findings to analysts in seconds with 2-minute alert-to-triage.
Q3: What Are Agentic SOC Workflows, and How Do They Differ from Traditional SOAR Automation?
⏰ The Speed Mismatch: Manual SOC Can’t Keep Up
Attackers using agentic AI now operate at machine speed. Reconnaissance that took weeks happens in minutes. Commodity malware rewrites itself to evade defenses. A mediocre attacker with AI agents executes attacks that previously required elite red team skills. “With AI, attackers are becoming faster, more automated, and less skilled, yet more effective. If your SOC is still operating at human speed with manual processes, you’ve already lost the race”. The traditional SOC model, analysts responding to alerts sequentially, manually pulling logs, making phone calls to verify, cannot match this pace. You are not competing against human attackers anymore. You are competing against AI systems that never sleep.
Agentic SOC vs. Traditional SOAR: The Critical Distinction
SOAR (Security Orchestration, Automation and Response) runs static if/then playbooks: “if malware detected, isolate endpoint.” These are brittle, require constant maintenance, and can’t reason about novel scenarios. Agentic SOC workflows use AI agents that autonomously execute multi-step investigation sequences: collecting context from SIEM, enriching with threat intelligence, correlating across identity/endpoint/cloud, and generating structured investigation reports.
| Dimension | SOAR Automation | Agentic SOC Workflows |
|---|---|---|
| Flexibility | Static playbooks | Dynamic, multi-step reasoning |
| Reasoning | ❌ If/then logic only | ✅ Contextual decision-making |
| Novel Threat Handling | Breaks on unknown patterns | Adapts to new scenarios |
| Investigation Depth | Single-action response | Full investigation sequence |
| Human Interaction | Alert escalation | ChatOps user verification |
From “Alert Factory” to “Investigation Engine”
Legacy SOC = humans doing mechanical work (log pulling, IP lookups, user verification calls). Agentic SOC = AI doing mechanical work, humans doing cognitive work (threat assessment, business impact analysis, strategic response).
The key principle from our operational experience: “Automation comes only when the manual processes work smoothly and they are just time-consuming and you can avoid this boring routine. But obviously there are critical things that should be prevented and cause automatic reaction”. Agentic SOC doesn’t replace human judgment. It eliminates the mechanical investigation bottleneck so analysts focus on decisions.
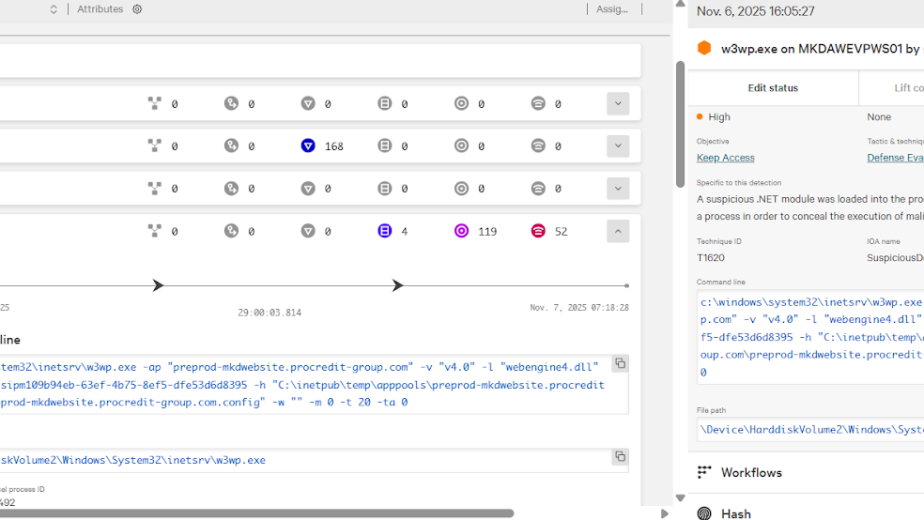
✅ UnderDefense MAXI AISOC: Agentic SOC in Practice
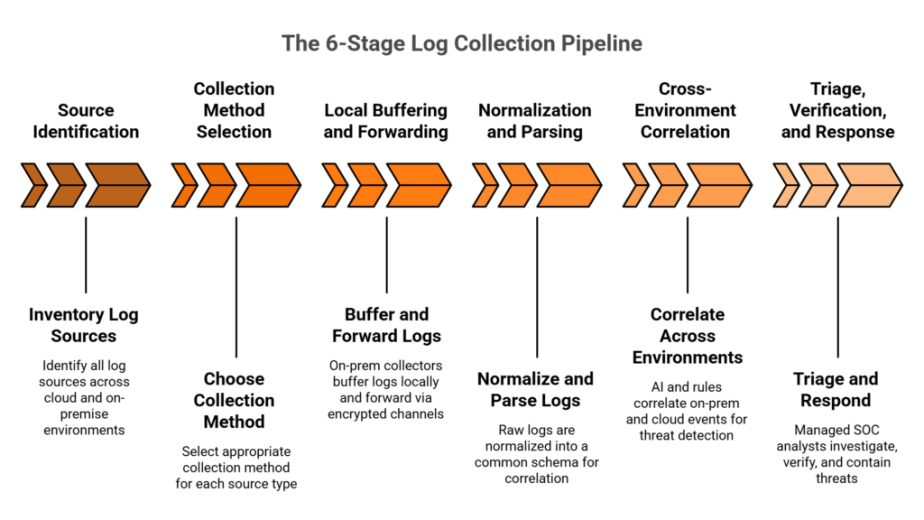
Here’s how we operationalize agentic workflows at UnderDefense:
- Automated context collection queries SIEM, pulls logs, enriches with threat intel
- Multi-system correlation connects dots across 250+ tool integrations
- Structured investigation reports delivers findings in seconds, not hours
- ChatOps user verification asks users directly via Slack/Teams for confirmation (“breaking the fourth wall”)
The core principle: “AI collects context, you decide”. The result: 2-minute alert-to-triage and 15-minute escalation for critical incidents, specifically because agentic workflows eliminate the manual investigation bottleneck. And it works with existing SIEMs (Splunk, Sentinel, Chronicle) without replacement.
Show, Don’t Tell
The question is not whether you need AI in your SOC, but whether your AI can match what threat actors are already using against you. We’ve demonstrated this in live workshops, showing how publicly available AI tools can exploit real-world applications, then demonstrating how MAXI’s agentic workflows detect and contain those same attacks. No proprietary magic. No hidden automation. Observable results you can reproduce.
Q4: Which SIEM Market Consolidation Moves Should Security Leaders Watch in 2026?
The modern SIEM market’s path to $13.55B runs through aggressive consolidation. If you’re running a security program today, these deals directly affect your roadmap, your budget, and your vendor risk.
📌 The Consolidation Wave: M&A Timeline
| Deal | Year | Strategic Implication |
|---|---|---|
| Cisco acquires Splunk ($28B) | Completed March 2024 | Largest networking-security merger in history; Splunk folded into Cisco’s security & observability stack |
| Palo Alto absorbs IBM QRadar SaaS | Completed September 2024 | QRadar customers migrated to Cortex XSIAM; IBM Consulting handles free migration for eligible clients |
| LogRhythm + Exabeam merge | Completed 2024 | Combined company retains Exabeam name; LogRhythm SIEM augmented with Exabeam’s AI-driven UEBA and Copilot |
| Google expands Chronicle → Google SecOps | 2024–2025 | Chronicle becomes full security operations platform with integrated SOAR and threat intelligence |
| Microsoft Sentinel rapid growth | 2024–2026 | Rapid enterprise adoption; deep integration with Defender XDR ecosystem |
⚠️ What Consolidation Means for Your Existing Investments
Every acquisition creates risk for customers already on those platforms:
- Vendor lock-in acquired products get sunset or folded into proprietary ecosystems
- Pricing uncertainty post-acquisition price increases are common
- Migration burden forced re-platforming to the acquirer’s stack
- Feature roadmap shifts innovation slows or pivots post-acquisition
Here’s the strategic reality from a former Micron/Darktrace CISO we spoke with: “If I switch to another vendor, I get to start all over on that tuning process. All my business logic, the correlation rules, the automation rules, that does not come with me. That’s why I want separate relationships for the MDR team versus the SIEM data capability. If you can separate those, all of your business logic stays with you”.
Strategic Response Options
Security leaders have three paths:
- Stay and absorb accept the new ecosystem (suited if you’re already deep in the acquiring vendor’s stack)
- Migrate to an independent platform costly but gives control
- Adopt a vendor-agnostic orchestration layer that works regardless of which SIEM you run. This is where open standards (OCSF) and vendor-agnostic MDR become strategic hedges against consolidation risk
The expert’s advice is clear: “I look for an MDR partner that will access the data where it lives and I want to control where that data lives”.
✅ UnderDefense: Built for Option #3
We purpose-built UnderDefense MAXI for exactly this scenario, a vendor-agnostic layer integrating with 250+ security tools including every major SIEM (Splunk, Sentinel, Chronicle, Exabeam). Whether you’re on Splunk today and Sentinel tomorrow, whether Cisco changes Splunk’s roadmap or Palo Alto sunsets QRadar features, your detection and response capability doesn’t skip a beat. Your business logic, your tuning, your investigation context stays intact.
Q5: What Is Observability-Led Security and How Does It Change Threat Detection?
Observability-led security is the convergence of traditional IT observability, including application telemetry, infrastructure metrics, and runtime behavior monitoring, with security operations. Instead of security teams seeing only “alert fired” and IT ops seeing only “service degraded,” unified observability provides full-context threat detection: understanding not just that a suspicious process ran, but what application it impacted, which services depend on it, and what the blast radius looks like if containment fails.
Why This Convergence Is Happening Now
Cloud-native architectures, microservices, and Kubernetes have blurred the line between “IT issue” and “security incident.” A container behaving anomalously could be misconfiguration or an active breach. Only cross-domain observability distinguishes them.
Here’s what’s driving this structurally:
- Telemetry overlap is massive. Up to 80% of the data flowing through SIEM and observability pipelines is the same: logs, cloud events, identity signals, infrastructure metrics, and application traces. Running separate stacks for security and ops means ingesting everything twice.
- Observability vendors are adding security. Datadog, Dynatrace, Splunk, and New Relic are layering security correlation on top of their observability cores. Meanwhile, SIEM vendors are adding observability. This convergence is structural, not optional.
- 54% of organizations already use full-stack observability, and many others are actively expanding coverage, recognizing that runtime behavior is the most reliable source of truth for detecting threats that traditional SIEM correlation rules miss.
- Palo Alto Networks’ acquisition of Chronosphere (finalized February 2026) signals that the industry’s largest security vendor sees observability as core to the next generation of threat detection.
How It Works Operationally
The practical shift is straightforward: instead of siloed dashboards, security teams get enriched context at the moment of alert.
- Real-time service dependency mapping for blast-radius analysis the system knows that if Container X is compromised, Services A, B, and C are at risk
- Application-layer behavioral baselines complementing endpoint and network baselines catching supply chain attacks and living-off-the-land techniques that signature-based SIEM misses
- Runtime anomaly detection that correlates performance traces with security events a sudden CPU spike + unusual API call + new IAM role assumption tells a different story than any single signal alone
⚠️ The Key Contrast
Traditional SIEM sees log events. Observability-led security sees the full operational context those events exist within.
Research from Enterprise Management Associates (EMA) identifies the core benefits: 59% of organizations with converged observability-security uncover security issues more effectively through intelligence and correlation capabilities, and 55% assess more security vulnerabilities thanks to the expanded visibility.
This is what enables faster, more accurate triage. The system understands not just “what happened” but “what would break if we don’t contain this in the next 5 minutes.”
How UnderDefense MAXI Operates on This Principle
UnderDefense MAXI’s multi-system correlation engine connects dots across endpoints, cloud workloads, identity systems, network traffic, and SaaS applications to deliver full-context investigation, not isolated alert analysis. This cross-domain reasoning is what enables 2-minute alert-to-triage: the system doesn’t just see the alert, it immediately understands what it means within your operational environment.
Q6: How Will the Talent Shortage and Rising SOC Costs Reshape Security Operations?
Your senior SOC analyst, the one who built half your detection rules and knows your environment inside-out, just gave two weeks’ notice. That’s the third analyst you’ve lost in 18 months. You have two junior analysts left, 3,000+ daily alerts to triage, a compliance audit in six weeks, and your CFO just asked you to justify next year’s security headcount increase.
This isn’t hypothetical, but an operational reality driving the shift to AI-augmented operations.
Why This Problem Is Systemic, Not Temporary
The ISC2 2025 Cybersecurity Workforce Study surveyed a record 16,029 professionals and found that the global cybersecurity workforce has plateaued at approximately 5.5 million, while demand has surged to 10.2 million, leaving a gap of 4.8 million unfilled positions (a 19% increase year-over-year).
But the headline number actually understates the operational pain:
- 33% of organizations say they don’t have the resources to adequately staff security teams
- 88% of respondents experienced significant cybersecurity consequences due to skills shortages
- 95% reported at least one critical skill need, up 5% from the prior year
- Analyst average tenure hovers around 18 months before burnout-driven turnover kicks in
As the former CISO of Micron and Darktrace put it on our podcast: “As that team grows and different skill sets are required, it becomes challenging to hire a pretty niche skill set. Then there’s a lot of overhead in training pipelines and keeping people progressing along a career path.”
💸 The Hidden Costs: ROI/TCO Framing
The math is brutal when you lay it out:
| Cost Factor | Traditional 24/7 SOC | AI-Augmented SOC + MDR |
|---|---|---|
| Annual fully-loaded cost | $1.5M–$2.5M (salaries, benefits, training, tools, turnover) | $11–15/endpoint/month |
| Quality consistency | Degrades on nights/weekends when seniors aren’t available | Consistent 24/7 quality, 2-minute triage |
| Knowledge retention | Custom rules and context walk out with every departure | Detection logic persists in platform |
| Analyst churn cycle | ~18 months, then restart | Managed by MDR partner |
| Capacity for proactive work | Near zero, consumed by alert triage | Freed up for strategic initiatives |
⏰ The Hybrid Model That Actually Works
The practical answer isn’t “replace humans with AI” or “hire your way out.” The answer is a hybrid that matches skill levels to value. As the former CISO of Micron explained: “I want a security engineer that understands how the business works on the inside. In a hybrid model, I can outsource the labor management of level one work and keep level two/three in-house for business judgment.”
This is exactly how AI-augmented SOC models operationalize the talent gap: AI handles mechanical investigation, including context collection, correlation, enrichment, and user verification, while human analysts focus on judgment calls that require organizational knowledge.
How UnderDefense Solves the Staffing Equation
UnderDefense MAXI AI SOC operationalizes this: augment your analysts with machine-speed investigation. It works with existing SIEM and tools (no replacement), delivers structured reports in seconds, and provides 24/7 coverage with consistent quality regardless of internal team size. Published transparent pricing ($11–15/endpoint/month) vs. opaque enterprise quotes from competitors. The result: organizations get enterprise-grade SOC capability without the $2M+ headcount investment.
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User, Program Development UnderDefense – G2 Verified Review
“Underdefense act as an extension of our team, so we don’t need additional resources, ensuring 24/7 protection. It also solved our problem of having separate security tools that didn’t work well together.”
— Inga M., CEO UnderDefense – G2 Verified Review
“They’re basically my security team since I can’t build one myself. They respond to problems so quickly.”
— Verified User, Mid-Market UnderDefense – G2 Verified Review
Q7: What Do NIS2, DORA, and the WEF Cybersecurity Outlook 2026 Mean for Your SIEM Strategy?
NIS2 (effective October 2024), DORA (January 2025), and the WEF Global Cybersecurity Outlook 2026 all demand continuous security monitoring with documented evidence of detection, investigation, and response capabilities. February 2026 marks the end of grace periods. Cybersecurity has shifted from a technical issue to a legal obligation of results. AI-driven SIEM and agentic SOC architectures produce this evidence as a byproduct of normal operations, not as a separate compliance workstream. Here’s what changes:
✅ What These Regulations Actually Require
- Automated audit trails every AI-driven investigation generates timestamped documentation of detection → investigation → response actions, mapped to framework controls. NIS2 and DORA both mandate full traceability: companies must not merely be protected, they must be able to demonstrate their resilience at any moment, under the threat of severe sanctions.
- Continuous compliance monitoring NIS2 requires demonstrating “appropriate and proportionate” security measures across 18+ critical sectors; DORA imposes strict digital operational resilience frameworks for financial entities including resilience testing, third-party risk management, and major incident reporting. Continuous AI-driven detection satisfies this far better than periodic manual reviews.
- Cross-framework coverage treating NIS2, DORA, and ISO 27001 in silos is, as compliance experts note, “the most costly mistake of 2026.” It generates documentation fatigue and exploding audit costs. An integrated approach transforms the ISMS into a single compliance hub: risk analysis performed once, a single set of evidence produced to meet multiple regulatory frameworks simultaneously.
- Non-compliance penalties are severe reaching 2% of global revenue under NIS2 and up to 7% under the EU AI Act, with personal liability for management.
⚠️ The Scope Expansion Most Teams Miss
NIS2 significantly broadens scope: SMEs, mid-sized companies, operators of essential services, digital service providers, local authorities, and industrial players must all implement stricter reporting obligations, resilience tests, end-to-end incident handling, and ICT risk management. Many countries haven’t yet passed national legislation, creating uncertainty, but the requirements are clear.
How UnderDefense Turns Security Into Compliance Evidence
UnderDefense includes forever-free compliance kits with its MDR service: SOC 2, HIPAA, and ISO 27001 audit evidence generated automatically from security operations, not bolted on as a separate product. The UnderDefense MAXI Compliance module provides auto evidence collection, continuous control validation, and reporting across frameworks, eliminating manual, time-consuming evidence gathering that overwhelms IT and security teams. Compliance becomes an output of protection, not a separate budget line.
“They’ve also made our audit process much less painful. The reports from their platform give us clear evidence of our security controls and incident response capabilities. When auditors or clients ask questions about our security posture, we can pull up exactly what they need to see.”
— Verified User, Marketing and Advertising UnderDefense – G2 Verified Review
Q8: What Does This Shift Mean for CISOs vs. SOC Managers vs. Security Engineers?
The forces reshaping SIEM and security operations in 2026 create different priorities depending on your role. A CISO’s consolidation strategy differs from a SOC Manager’s workflow transformation plan, which differs from a Security Engineer’s technology evaluation. Generic “security leaders should…” advice, which every competitor publishes, is not actionable enough. Here’s what each role should prioritize:
For CISOs & Security Directors: Strategic Priorities
- Build vendor-agnostic architecture as a hedge against M&A disruption. Don’t lock budget into a single platform during a consolidation wave. As our podcast guest (former CISO of Micron) advised: if you create custom correlation rules inside a vendor’s proprietary SIEM and later switch providers, “the business logic, the correlation rules, the automation rules, that does not come with. You get to start all over.”
- Reframe security budget from “cost center” to “risk-adjusted investment” using the NIST CSF visualization approach: “Look at NIST CSF risk families and allocate budget dollars, that one-page visual can be really enlightening for stakeholders.”
- Evaluate hybrid staffing models. Keep Tier 2–3 in-house for business knowledge, leverage AI-augmented MDR for Tier 1 and 24/7 coverage. The fully in-house model works only when you can afford the turnover tax.
- Use observability-led security to demonstrate board-level ROI through blast-radius reduction metrics and continuous compliance evidence.
For SOC Managers: Operational Priorities
- Pilot agentic SOC workflows on highest-volume alert categories first automated investigation for login anomalies, OAuth grants, and privilege escalations. Start where the noise is loudest.
- Establish 2-minute alert-to-triage as the new operational benchmark. This replaces vague “MTTR” metrics that average critical incidents with routine noise.
- Implement ChatOps user verification to close the context gap on behavioral alerts. Most behavioral alerts are unanswerable without asking the user: “Did you run that PowerShell script?” The team that can verify at scale wins.
- Map existing SOAR playbooks to identify which can be replaced by agentic workflows (routine, high-volume) and which still require static automation (compliance-driven, exception-heavy).
For Security Engineers: Technical Priorities
- Evaluate SIEM architecture options: cloud-native, federated, or hybrid, using OCSF compatibility as a key selection criterion for portability.
- Build detection-as-code practices for portable detection rules that survive vendor changes, written in flexible languages like Python, securely versioned, unit-tested, and deployed via CI/CD.
- Integrate observability telemetry (APM, infrastructure metrics) into security correlation. Start with service dependency mapping for blast-radius analysis.
- Test AI-driven investigation tools against your specific environment. Require transparent, reproducible results, not “trust me, it works.” Every investigative step should be observable and auditable.
How UnderDefense MAXI Serves All Three Personas
UnderDefense MAXI AI SOC is designed to serve all three roles simultaneously. CISOs get vendor-agnostic architecture (250+ tool integrations) and transparent pricing ($11–15/endpoint/month). SOC Managers get 2-minute triage and ChatOps verification. Engineers get existing SIEM compatibility and detection-as-code support. One platform, role-specific value, and every action taken by AI and human analysts remains observable and auditable.
Q9: Traditional MDR vs. AI-Augmented SOC: Which Model Wins in 2026?
Given the macro forces reshaping security operations, including AI-driven detection, SIEM consolidation, vendor lock-in risk, and a 3.4M cybersecurity talent gap, you’re no longer choosing between MDR vendors. You’re choosing between two fundamentally different operational architectures: Traditional MDR (outsourced monitoring with alert escalation) vs. AI-Augmented SOC (AI-driven investigation with human analyst response). This is not a feature checklist exercise. It’s a structural decision that determines whether you’re buying alert noise management or genuine threat resolution.
✅ What Traditional MDR Gets Right
Credit where it’s due. Arctic Wolf built strong brand recognition with dedicated concierge security teams and comprehensive coverage, and their MDR Basic plan starts at $44,000/year for up to 100 users on AWS Marketplace. CrowdStrike Falcon Complete delivers best-in-class endpoint detection backed by massive threat intelligence. ReliaQuest’s GreyMatter platform offers cross-tool visibility that many security teams appreciate.
❌ Where the Architecture Breaks Down
The limitations aren’t about individual features; they’re structural. Arctic Wolf requires proprietary SIEM replacement, meaning you abandon existing investments in Splunk, Sentinel, or Elastic the moment you sign. CrowdStrike sees endpoint behavior brilliantly but can’t verify whether the suspicious PowerShell execution was your IT admin or an attacker. That requires organizational context no EDR possesses alone. Pricing remains opaque across the board: Arctic Wolf’s custom enterprise quotes can exceed $96K+ annually with no published per-endpoint transparency.
Most critically, these providers operate a detect-and-escalate model. When something looks suspicious, you get a ticket: “Please investigate.” Your team still does the actual work at 2 AM.
“We received little value from ArcticWolf. The product offered little visibility… Anything you want to look at or changes you need to make must go through their engineering team.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
✅ The AI SOC + Human Ally Difference
We built UnderDefense on the opposite principle: work with what you have, and own the outcome, not just the alert. The UnderDefense MAXI platform integrates with 250+ existing tools (CrowdStrike, Splunk, Sentinel, SentinelOne, Okta) without replacing any of them. AI-driven agentic investigation handles context collection, correlation, and enrichment at machine speed, delivering 2-minute alert-to-triage. When behavioral alerts need human context (“Did Jane authorize that OAuth app at 2:41 AM?”), our analysts reach affected users directly via Slack or Teams through ChatOps verification, closing alerts competitors simply cannot resolve without customer involvement.
Full containment follows: credential revocation, endpoint isolation, lateral movement blocking. Published pricing at $11–15/endpoint/month, with no “contact sales” games.
📊 Side-by-Side Comparison
| Criteria | Traditional MDR (Arctic Wolf, CrowdStrike, ReliaQuest) | UnderDefense AI SOC + Human Ally |
|---|---|---|
| Integration Approach | Proprietary stack or limited tools | ✅ Vendor-agnostic, 250+ integrations |
| Investigation Model | Static SOAR/playbooks | ✅ Agentic AI workflows |
| User Verification | Escalates back to customer | ✅ ChatOps direct (Slack/Teams/SMS) |
| Response Capability | Detect + notify | ✅ Detect + contain + remediate |
| Pricing Transparency | Contact sales ($44K–$96K+/yr) | ✅ Published $11–15/endpoint/month |
| Compliance Inclusion | Separate product | ✅ Forever-free compliance kits |
| Onboarding Speed | Months + stack migration | ✅ 30-day turnkey deployment |
| SIEM Compatibility | Proprietary or limited | ✅ Splunk/Sentinel/Chronicle/any |
🎯 Who Should Choose What
Choose traditional MDR if you’re starting from scratch with zero existing security investments and want a single-vendor ecosystem managed externally. Choose UnderDefense if you want to protect current stack investments, need AI-driven investigation speed with human verification, transparent predictable pricing, and analysts who contain threats, not escalate alerts back to your team.
“UnderDefense integrates well with our systems, specifically with our SIEM, Splunk. Their team is proactive in identifying and addressing threats, providing 24/7 oversight.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
“Started out well but over the years the service has consistently not met expectations. The issues that we have experienced has greatly outweighed the benefits.”
— CISO, Manufacturing ($3B–$10B) Arctic Wolf – Gartner Verified Review
Q10: How Should You Evaluate Your SIEM and SOC Readiness for 2026?
Here’s a practical self-assessment. Every checkbox below maps to a specific macro shift covered in this article, and every unchecked box represents a vulnerability in your security operations architecture that attackers can exploit.
📋 The 2026 SIEM & SOC Readiness Checklist
Score your current capabilities against these 8 criteria:
☐ AI-Powered Detection: Can your SIEM detect behavioral anomalies (not just signature matches) across user, endpoint, and cloud telemetry?
☐ Agentic Investigation: Does your SOC leverage AI for automated investigation, including context collection, correlation, and enrichment, or do analysts still manually pull logs?
☐ Response Speed: Can your team contain a critical threat within 15 minutes of detection?
☐ Unified Visibility: Are your SIEM, EDR, identity, and cloud security alerts correlated in one view?
☐ Vendor Agnosticism: Is your SOC architecture independent of any single platform that consolidation could disrupt?
☐ 24/7 Consistency: Do you have round-the-clock coverage with consistent detection quality across all shifts, including weekends and holidays?
☐ Compliance Automation: Does your security monitoring automatically generate audit evidence (SOC 2, ISO 27001, HIPAA, NIS2)?
☐ User Verification: Can your SOC verify suspicious user activity directly (via Slack/Teams) instead of escalating back to your team?
⚠️ What Your Score Means
| Score | Maturity Level | What It Means |
|---|---|---|
| 7–8 ✓ | ✅ Mature | Focus on optimization, proactive threat hunting, and observability integration. Your architecture is aligned with the 2026 threat landscape. |
| 4–6 ✓ | ⚠️ Critical Gaps | Investigation speed or coverage inconsistencies are likely causing missed threats or analyst burnout. You’re running 2024 operations against 2026 threats. |
| 0–3 ✓ | ❌ Significant Exposure | Your SOC architecture is mismatched with the current threat landscape. Reactive processes dominate, and you’re at elevated breach risk. |
How UnderDefense Converts Gaps into Coverage
UnderDefense MAXI AI SOC is engineered to convert every unchecked box into a ✓: AI-driven investigation at machine speed (2-minute alert-to-triage), vendor-agnostic integration with 250+ tools, ChatOps user verification, 15-minute escalation for critical incidents, 96% MITRE ATT&CK coverage, and compliance automation included at no extra charge. Most organizations move from 2–3 checks to 7–8 within 30 days of deployment.
“Before the guys from UD stepped in, we were getting bombarded with alerts from all our security tools. Their team cleaned up our configurations and got the noise under control within the first week.”
— Verified User, Marketing and Advertising UnderDefense – G2 Verified Review
“UnderDefense has changed our approach to cybersecurity. At first, we hired them for managed SIEM service, but after they demonstrated the value of MDR, our management was motivated to act on it.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
💰 Scored Below 5?
Use the UnderDefense SOC Cost Calculator to quantify the gap between your current spend and what enterprise-grade AI-augmented SOC coverage actually costs. Most organizations are surprised by the comparison: building a 24/7 in-house SOC runs $1.5M–$2.5M/year, while equivalent AI-augmented MDR coverage starts at $11–15/endpoint/month.
Q11: Best SOC Solutions to Operationalize Your 2026 Security Strategy
The leading SOC-as-a-Service and AI-augmented SOC providers operationalizing the 2026 trends covered in this article include UnderDefense, Arctic Wolf, CrowdStrike Falcon Complete, Expel, and Red Canary, each with distinct architectural approaches to AI-driven detection, agentic workflows, and vendor integration.
🔍 Five Factors That Separate SOC Solutions in 2026
SOC solutions are now differentiated by architectural factors that directly determine whether you get genuine threat resolution or just another alert dashboard:
- Vendor-agnostic integration vs. proprietary stack lock-in
- Agentic AI investigation vs. static SOAR playbooks
- Human analyst access: direct Tier 3–4 communication vs. ticket-based escalation
- Published response time SLAs and transparent pricing
- Compliance automation included vs. separate add-on purchase
🎯 Matching Providers to Scenarios
Each provider excels in different scenarios. Arctic Wolf works for organizations wanting single-vendor simplicity with white-glove onboarding. CrowdStrike Falcon Complete fits Falcon-native environments where endpoint depth is the priority. UnderDefense serves organizations protecting existing stack investments with AI-driven investigation and human analyst response. The right choice depends on your checklist score from Q10, your current SIEM architecture, and your consolidation risk tolerance.
This analysis is based on documented response times, Frost & Sullivan market data, G2 Spring 2025 rankings, MITRE ATT&CK coverage assessments, and operational outcomes across 500+ MDR deployments.
Q12: FAQ: Common Questions About SIEM and Security Operations in 2026
Is SIEM dead in 2026?
No. SIEM is evolving from passive log storage into an AI-powered security intelligence platform. The global modern SIEM market is projected to grow from $7.13 billion in 2024 to $13.55 billion by 2029 at a 13.7% CAGR, according to Frost & Sullivan. What’s dying is the legacy model of rule-based correlation and manual investigation. What’s emerging is SIEM as the AI-driven orchestration layer for unified detection, investigation, and response, converging with XDR and SOAR capabilities into integrated platforms like Microsoft Sentinel, Google SecOps, and Palo Alto XSIAM.
What is an agentic SOC?
An agentic SOC uses AI agents that autonomously execute multi-step investigation sequences, collecting context from SIEM, enriching with threat intelligence, correlating across identity/endpoint/cloud telemetry, and verifying suspicious activity directly with users via Slack or Teams. Unlike static SOAR playbooks, agentic workflows reason about novel scenarios and adapt investigation paths in real-time. According to Omdia research, 39% of early adopters deploy agentic AI primarily for reduced costs and increased productivity. The key principle: AI performs mechanical investigation at machine speed so human analysts focus on judgment calls and business-impact decisions.
How will AI change security operations in 2026?
AI is shifting SOC operations from reactive alert triage to proactive threat investigation. Specifically:
- Behavioral analytics replace signature-based detection, catching novel threats that rules miss.
- Automated investigation eliminates manual log-pulling, reducing triage time from hours to minutes.
- AI agents verify suspicious activity directly with users, closing context gaps.
- Natural language querying lets analysts ask SIEMs questions in plain English.
The result: analysts shift from mechanical data processing to strategic threat assessment and business-impact analysis.
What is observability-led security?
Observability-led security merges IT observability (application performance, runtime behavior, infrastructure metrics) with security operations to create full-context threat detection. Instead of seeing only isolated security alerts, teams understand what application was impacted, which services depend on it, and what the blast radius looks like if containment fails. It’s especially critical in cloud-native and microservices environments where the line between IT issue and security incident is blurred.
How much does a modern AI-augmented SOC cost?
Costs vary significantly by model. Building a 24/7 in-house SOC typically runs $1.5M–$2.5M/year (5+ analysts, tools, training, turnover). AI-augmented MDR providers like UnderDefense offer equivalent 24/7 coverage at $11–15/endpoint/month with transparent published pricing, versus opaque enterprise quotes from traditional MDR providers (Arctic Wolf’s MDR Basic starts at $44,000/year for 100 users on AWS Marketplace, with custom enterprise quotes reaching significantly higher). Use the SOC Cost Calculator to compare your specific scenario.
What does SIEM market consolidation mean for my current tools?
Major M&A events, including Cisco acquiring Splunk, Palo Alto absorbing QRadar SaaS, and the LogRhythm-Exabeam merger, create vendor lock-in risk, potential price increases, and forced migration timelines. The strategic hedge: adopt vendor-agnostic architecture that works regardless of which SIEM you run. Keep SIEM ownership separate from MDR partnerships so your business logic, correlation rules, and detection tuning survive vendor changes. UnderDefense integrates with Splunk, Sentinel, Chronicle, Elastic, and any SIEM, specifically so your security posture is not held hostage to a single vendor’s roadmap.
1. How is SIEM technology evolving from legacy log management to AI-powered security operations in 2026?
We see SIEM undergoing a fundamental architectural shift, not a decline. The global modern SIEM market is projected to grow from $7.13 billion in 2024 to $13.55 billion by 2029 at a 13.7% CAGR, according to Frost & Sullivan. The core transformation centers on three converging capabilities:
-
Behavioral analytics replacing static, signature-based correlation rules to detect novel threats.
-
AI-driven investigation automating the manual log-pulling and context-collection that used to consume analyst hours.
-
Natural language querying allowing analysts to ask SIEMs questions in plain English instead of writing complex search queries.
What’s dying is the legacy model of passive log storage and rule-based alerting. What’s emerging is SIEM as the AI-driven orchestration layer for unified detection, investigation, and response, converging with XDR and SOAR capabilities into integrated platforms. The key strategic implication: your SIEM architecture needs to support agentic workflows, not just collect logs. Organizations still running rule-only SIEM are operating 2024 technology against 2026 threats.
2. What is an agentic SOC and how does it differ from traditional SOAR playbooks?
An agentic SOC uses AI agents that autonomously execute multi-step investigation sequences rather than following pre-scripted playbooks. Where traditional SOAR runs a fixed “if-then” workflow, agentic AI reasons about novel scenarios and adapts investigation paths in real-time.
In practice, this means AI agents:
-
Collect context from SIEM, EDR, identity, and cloud telemetry simultaneously.
-
Enrich alerts with threat intelligence and historical correlation automatically.
-
Verify suspicious activity directly with users via Slack or Teams, without waiting for human analyst handoff.
-
Adapt their investigation path when they discover unexpected patterns mid-triage.
According to Omdia research, 39% of early adopters deploy agentic AI primarily for reduced costs and increased productivity. At UnderDefense, our MAXI platform operationalizes agentic investigation to achieve 2-minute alert-to-triage, handling context collection, correlation, and enrichment at machine speed. The principle is straightforward: AI performs mechanical investigation so human analysts focus on judgment calls and business-impact decisions.
3. What does SIEM market consolidation mean for my current security tools and vendor contracts?
Major M&A events, including Cisco acquiring Splunk, Palo Alto absorbing QRadar SaaS, and the LogRhythm-Exabeam merger, are creating three specific risks for security teams:
-
Vendor lock-in risk: Your correlation rules, detection tuning, and business logic become tied to a platform whose roadmap you no longer control.
-
Price increases: Post-acquisition pricing typically rises as vendors consolidate market power.
-
Forced migration timelines: Legacy product sunsetting forces unplanned infrastructure changes.
We advise adopting vendor-agnostic architecture as the strategic hedge. Keep SIEM ownership separate from your MDR partnership so your detection logic survives vendor changes. Our managed detection and response service integrates with Splunk, Sentinel, Chronicle, Elastic, and any SIEM specifically so your security posture is not held hostage to a single vendor’s roadmap. The consolidation wave rewards organizations that build portability into their security architecture today.
4.How do we compare traditional MDR with AI-augmented SOC models for 2026?
This comparison centers on a structural difference, not a feature checklist. Traditional MDR providers (Arctic Wolf, CrowdStrike Falcon Complete, ReliaQuest) operate a detect-and-escalate model: when something looks suspicious, you get a ticket saying “Please investigate.” Your team still does the actual containment work.
AI-augmented SOC models flip the architecture. AI-driven investigation handles context collection, correlation, and enrichment at machine speed. Human analysts then perform verification, judgment, and full containment, including credential revocation, endpoint isolation, and lateral movement blocking.
Key structural differences include:
-
Integration approach: proprietary stack replacement vs. vendor-agnostic integration with 250+ existing tools.
-
Investigation model: static SOAR playbooks vs. agentic AI workflows.
-
User verification: escalation back to customer vs. direct ChatOps verification via Slack/Teams.
-
Pricing: opaque enterprise quotes ($44K–$96K+/year) vs. published $11–15/endpoint/month.
We built UnderDefense MAXI on the principle of owning the outcome, not just the alert. Explore our MDR pricing for transparent cost comparison.
5. How should we assess our SOC readiness for the 2026 threat landscape?
We recommend scoring your current capabilities against eight criteria that map directly to the macro shifts reshaping security operations:
-
AI-powered behavioral detection across user, endpoint, and cloud telemetry.
-
Agentic investigation with automated context collection, correlation, and enrichment.
-
Response speed: ability to contain critical threats within 15 minutes of detection.
-
Unified visibility correlating SIEM, EDR, identity, and cloud alerts in one view.
-
Vendor agnosticism independent of any single platform.
-
24/7 consistent detection quality across all shifts, including weekends and holidays.
-
Compliance automation generating audit evidence automatically (SOC 2, ISO 27001, HIPAA, NIS2).
-
User verification directly via Slack/Teams instead of ticket escalation.
Scoring 7–8 checks means your architecture is mature and aligned. Scoring 4–6 indicates critical gaps causing missed threats or burnout. Scoring 0–3 signals significant exposure with reactive processes dominating. Use our SOC cost calculator to quantify the gap between current spend and enterprise-grade coverage.
6. What is observability-led security and why does it matter for cloud-native environments?
Observability-led security merges IT observability (application performance monitoring, runtime behavior analysis, infrastructure metrics) with security operations to create full-context threat detection. Instead of seeing only isolated security alerts, your team understands:
-
What application was impacted and its business criticality.
-
Which services depend on the affected component.
-
What the blast radius looks like if containment fails.
This approach is especially critical in cloud-native and microservices environments where the line between IT performance issue and security incident is increasingly blurred. A spike in API latency could indicate a denial-of-service attack or a misconfigured deployment. Without observability context, your SOC cannot tell the difference.
We integrate observability signals with comprehensive threat detection across our platform to ensure analysts have full operational context when investigating alerts, not just security telemetry in isolation. This convergence represents one of the defining cybersecurity trends of 2026.
7. How much does it cost to build an in-house SOC versus using an AI-augmented MDR provider?
-
Costs vary dramatically by model. Building a 24/7 in-house SOC typically runs $1.5M–$2.5M per year when accounting for:
-
Minimum 5+ analysts to cover 24/7/365 shifts (salary, benefits, training).
-
SIEM licensing, EDR tools, threat intelligence feeds, and infrastructure.
-
Ongoing analyst turnover in a market with a 3.4 million cybersecurity talent gap.
-
Continuous training to keep pace with evolving attack techniques.
AI-augmented MDR providers offer equivalent 24/7 coverage at a fraction of the cost. Traditional MDR pricing remains largely opaque, with providers like Arctic Wolf starting at $44,000/year for 100 users on AWS Marketplace and custom enterprise quotes reaching $96K+ annually. UnderDefense provides published transparent pricing at $11–15/endpoint/month with no hidden costs, forever-free compliance kits included, and 30-day turnkey deployment. Use our SOC cost calculator to model your specific scenario.
-
8. Which SOC-as-a-Service providers should we evaluate for our 2026 security strategy?
The leading providers operationalizing 2026 security trends include UnderDefense, Arctic Wolf, CrowdStrike Falcon Complete, Expel, and Red Canary. Each excels in different scenarios:
-
Arctic Wolf works for organizations wanting single-vendor simplicity with white-glove onboarding and dedicated concierge teams.
-
CrowdStrike Falcon Complete fits Falcon-native environments where endpoint detection depth is the primary priority.
-
Expel offers strong transparency with cross-vendor visibility for mid-market teams.
-
Red Canary provides accessible MDR with strong endpoint focus and curated detections.
-
UnderDefense serves organizations protecting existing stack investments with AI-driven investigation, direct human analyst response, and transparent published pricing.
Five architectural factors now separate SOC solutions: vendor-agnostic integration vs. lock-in, agentic AI investigation vs. static playbooks, direct analyst access vs. ticket-based escalation, published SLAs and pricing, and compliance automation included vs. add-on. Explore our full ranking in our 12 best SOC-as-a-Service providers guide to match the right solution to your readiness score.
The post Cybersecurity Trends 2026: AI SIEM, Agentic SOC, and the Consolidation Risk You’re Ignoring appeared first on UnderDefense.