After nine years running Agentic SOC operations, we’ve seen every AI security claim stress-tested against real incidents. Most don’t survive contact with a production environment.
The Gap Between the Demo and the Production Environment
The pressure on security teams has never been higher, which makes the seduction of AI marketing particularly dangerous.
The organizations extracting real value from AI security aren’t buying into the hype. They understand exactly what it does, where it fits, and how to measure whether it’s working. That clarity starts with calling out the myths by name.
The 8 Myths Every Security Leader Will Encounter
Below is a preview of the most damaging misconceptions in the market today. Some of them will cost organizations millions if left unchallenged. The full guide breaks down all eight with evidence, data, and the questions you should be asking vendors instead.
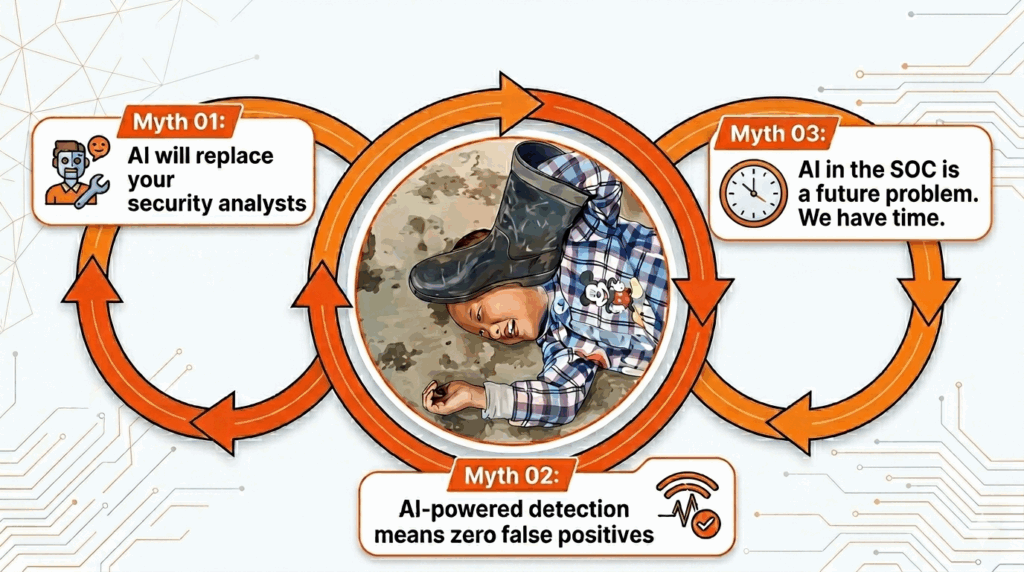
Myth 01
“AI will replace your security analysts.”
This creates anxiety and leads to underinvestment in talent, just when AI is making analysts more productive than ever. The reality is a division of labor, not a replacement.
Myth 02
“AI-powered detection means zero false positives.”
SANS 2025 data identifies false positives as the top analyst pain point, with stale model data as the leading cause. Reduction is real; elimination is not. A system tuned to hit zero FPs will miss actual threats.
Myth 03
“AI in the SOC is a future problem. We have time.”
Threat actors already operate at machine speed: running recon, generating polymorphic malware, and iterating phishing lures in real time. Waiting isn’t a neutral position. It’s a structural disadvantage.
5 More Myths Unpacked in the Full Guide
Change the way you think about buying AI security tools.
What “Autonomous” Actually Means When the Demo Ends
“Autonomous” is the most overstretched word in AI security marketing. In production, it typically means one thing: the AI handles known threat patterns within defined parameters. It doesn’t mean fully self-directing without human oversight. Any vendor claiming otherwise deserves harder questions.
“A SOC that responds to machine-speed attacks with more analysts working harder is bringing a horse to a car race. The contest isn’t about effort anymore. It’s about architecture.”
The Cloud Security Alliance has formalized four stages of AI maturity in security operations. Where your organization sits today determines what “autonomous” can realistically mean for you, and whether a vendor’s claims are aspirational or achievable in your environment.
Before You Buy: Are You Actually Ready?
One of the most valuable sections of the full guide is the Agentic SOC Readiness Assessment — a 15-question checklist across data infrastructure, process maturity, and governance. Here’s a preview:
Readiness Snapshot
☐ Our SIEM is collecting and normalizing logs from all critical systems.
☐ We have documented incident response playbooks.
☐ We have defined what the AI can do autonomously vs. what requires human approval.
Scoring below 7 out of 15 means AI will amplify your existing weaknesses, not solve them. The guide tells you exactly which gaps to close first and in what order.
The Questions That Cut Through Vendor Noise
Section 5 of the full guide is something we’ve never seen done this clearly anywhere else: a set of direct questions, organized by AI architecture, integration depth, real-world performance, and the human layer. They will help you immediately separate vendors who can deliver from those still catching up to their own marketing.
Sample: “Have you ever missed a ransomware incident in a client environment? If so, what happened?” The answer tells you everything.
A Realistic Roadmap for the Next 12 Months
The guide closes with a phased deployment framework based on real production experience across 500+ MDR client environments. Here’s what the structure looks like, with the detail behind each phase waiting in the full guide.
Phase 1
Months 1–3
Foundation
Stabilize data, establish baselines, reduce noise. Pick 1–2 use cases for immediate AI deployment.
One straight-talking guide
All 8 myths, the complete 15-point readiness assessment, the vendor evaluation questions, and the full 3-phase deployment roadmap.
The post 8 Things AI SOC Vendors Promise. We Ran Them Against 500+ Real Incidents. appeared first on UnderDefense.