Q1: What Does an AI SOC Actually Cost in 2026? (Real Pricing From 4 Leading Providers)
AI SOC and MDR pricing in 2026 ranges from roughly $119 to $440+ per endpoint or user annually, depending on the provider, tier, and contract structure. But that range is nearly useless without naming names, so here’s what four leading providers actually charge, sourced from Vendr verified buyer data, published marketplace rates, and pricing calculators.
⚠️ Why “Average MDR Pricing” Articles Mislead You
Most content on this topic gives you a lazy “$3–$15/endpoint/month” range with zero vendor attribution. That helps nobody building a business case. If you’re a CISO presenting to your CFO, you need named vendors, real dollar figures, and absolute clarity on what’s included versus what’s an expensive add-on. That’s what this section delivers: no vague benchmarks, just numbers you can actually use in a budget spreadsheet.
The 4-Vendor Pricing Comparison
| Provider | Pricing Model | Per-Endpoint/User Annual Cost | 500-Endpoint Mid-Market Estimate | What’s Included in Base | What Costs Extra |
|---|---|---|---|---|---|
| Arctic Wolf | Custom quote, channel-only | ~$192–$360/user/yr (public sector data); ~$20/user/mo (SelectHub) | $96K–$180K/yr | 24/7 monitoring, Concierge Security Team, basic cloud monitoring, up to $3M Security Operations Warranty | CDR, Managed Risk, Security Awareness Training, IR retainer, extended log retention |
| Red Canary | Resource-based (endpoints + identities + cloud) | Core: $120/endpoint/yr + $100/user/yr + $250/cloud resource/yr | $60K–$79.5K/yr (Core + Active Remediation) | 24/7 detection, EDR integration (CrowdStrike, SentinelOne, Defender), executive dashboards | Active Remediation ($39/endpoint), Security Data Lake, Complete/Enterprise tier upgrades |
| Alert Logic (Fortra) | Node-based, tiered (min. 25 nodes) | Avg ~$46K/yr (Vendr data); starts at $550/mo for 25 nodes | $30K–$75K/yr (Professional tier, ~100 nodes) | 24/7 SOC monitoring, vulnerability scanning, compliance reporting, Fortra Threat Brain intel | Enterprise tier (requires Professional base), extended retention, Managed WAF |
| UnderDefense | Per-asset, published calculator | $119/asset/yr (EDR); $140/asset/yr (cloud/SaaS/email) | ~$59.5K–$70K/yr | 24/7 monitoring, concierge analysts, compliance kits, 250+ integrations, 30-day onboarding | Nothing standard is an add-on |
💰 The Transparency Gap You Should Care About
Here’s the pattern that should concern you as a buyer. UnderDefense and Alert Logic publish pricing or make it easily calculable from their websites. Arctic Wolf requires a VAR or channel partner quote, as there are no published list prices anywhere, and the same deployment can cost 40% more or less depending on which reseller you engage. Red Canary publishes Core Plan rates but keeps Complete and Enterprise pricing behind a sales conversation.
When vendors hide pricing, your negotiation leverage shrinks. You can’t benchmark what you can’t see. The hidden-fee checklist in Q3 of this article becomes your armor in those conversations: print it, bring it to the call, and watch how the conversation changes.
✅ Why UnderDefense’s Model Stands Apart
Among these four providers, we’re the only one where the published per-asset price includes compliance kits, 250+ tool integrations, full onboarding, and concierge analyst response with no add-on surprises at renewal. The SOC Cost Calculator lets you model your exact scenario before ever talking to sales. That’s “show, don’t tell” applied to pricing: you see the number, you validate it yourself, and you bring it to your CFO with confidence. No guessing, no waiting for a channel partner to call you back with a quote that expires in 48 hours.
Q2: How Do These Prices Break Down by Organization Size? (SMB, Mid-Market & Enterprise Scenarios With Real Vendor Numbers)
Knowing per-endpoint pricing is one thing. Knowing what you’ll actually write on the purchase order is another. Here’s how those vendor numbers from Q1 translate across three real-world organization profiles, the same profiles most security leaders use when building budgets internally.
The Three Scenarios You Can Map to Your Environment
- SMB: 250 endpoints, 5 servers, single cloud environment, basic compliance needs (SOC 2 or ISO 27001)
- Mid-Market: 1,000 endpoints, 20 servers, multi-cloud (AWS + Azure), SOC 2 and HIPAA required
- Enterprise: 5,000 endpoints, 100 servers, hybrid cloud, full compliance suite including PCI DSS
These aren’t hypothetical constructs but mirror the environments we onboard at UnderDefense every month, and they reflect what Vendr buyer data shows as typical deployment sizes for each vendor.
💸 The Scenario Cost Comparison Table
| Org Size | Arctic Wolf (Est.) | Red Canary (Core + Remediation) | Alert Logic (Professional) | UnderDefense (Published) | In-House SOC (Build-Your-Own) |
|---|---|---|---|---|---|
| SMB (250 endpoints) | $48K–$90K | $37.5K–$49.8K | $15K–$38K | $29.8K–$35K | $500K–$800K |
| Mid-Market (1,000 endpoints) | $192K–$360K | $120K–$159K | $50K–$100K | $119K–$140K | $1.2M–$2M |
| Enterprise (5,000 endpoints) | $960K–$1.8M | $600K–$795K | $200K–$500K | $595K–$700K | $2.5M–$4M+ |
Sources: Arctic Wolf estimates from Vendr buyer data and public sector price lists; Red Canary Core Plan published rates + $39/endpoint Active Remediation add-on; Alert Logic Vendr average and tiered structure; UnderDefense published per-asset calculator; In-house benchmarks from Ponemon Institute ($2.84M average) and industry surveys.
Why the Ranges Vary So Dramatically Within Each Vendor
This is the part most comparison articles skip. Arctic Wolf’s channel-only model means VAR markups fluctuate wildly, and the same 500-user deployment can cost 40% more depending on which reseller picks up the phone. Red Canary’s multi-domain pricing model (endpoints, identities, and cloud resources each priced separately) compounds fast for organizations with complex environments. A 500-endpoint company that also needs identity protection for 500 users and coverage for 100 cloud resources could see costs jump from $60K to well over $130K on the Complete Plan.
⏰ Alert Logic’s Tier Stacking Problem
Alert Logic’s tiered structure means Enterprise requires Professional as a base, so you can’t skip a tier. The price you see for “Enterprise” isn’t the Enterprise premium alone but the Professional license plus the Enterprise add-on. That stacking effect catches mid-market buyers off guard during renewals.
✅ The UnderDefense Simplification Factor
At every organization size in the table above, UnderDefense delivers the narrowest cost range. Fewer pricing variables, fewer surprises. The fastest deployment at 30 days versus months of tuning. And the most inclusive base price: compliance kits, integrations, onboarding, and concierge analyst response are all baked in. When your CFO asks “what’s the real number?” you want to give one number, not a range that depends on which reseller answers your RFP. The managed SOC pricing calculator confirms this: model your exact environment, see the all-inclusive figure, and bring it to your board with zero ambiguity.
Q3: What Hidden Fees Should You Watch For in AI SOC Contracts? (The 12-Point Fee Audit Checklist)
The quoted price is never the real price. After reviewing hundreds of MDR contracts, both as a practitioner and as someone whose team competes against these vendors daily, here are the 12 line items that inflate your total cost of ownership well beyond the sales deck.
⚠️ The 12-Point Fee Audit Checklist
Print this. Take it into your next vendor negotiation.
- ☐ Data ingestion overage charges: Providers cap log volume; overages spike during investigations
- ☐ Custom integration/connector fees: Non-standard tools (legacy SIEM, niche EDR) require paid professional services
- ☐ Onboarding & professional services: $5K–$50K range (Red Canary per Vendr)
- ☐ SIEM/log platform licensing: Proprietary SIEM means you lose data and rules if you leave
- ☐ Compliance reporting add-ons: PCI, HIPAA, SOC 2 reports often sold as a separate SKU
- ☐ Threat intelligence feed surcharges: Premium feeds beyond basic IOCs cost extra
- ☐ Incident response retainer fees: Arctic Wolf charges IR separately from MDR (Vendr data)
- ☐ Data retention beyond standard window: 90-day default is common; 1-year retention is a paid upsell
- ☐ API call or automation fees: SOAR integrations may be metered or capped
- ☐ Dedicated analyst tier upgrades: Alert Logic Enterprise requires Professional base, stacking costs
- ☐ Early termination penalties: ❌ Arctic Wolf contracts: non-cancellable, non-refundable (Vendr)
- ☐ Annual price escalation clauses: ❌ Arctic Wolf: 5–8% auto-increase, negotiable to 4–5% (Vendr)
How to Score Your Vendor
- 0–3 items unchecked = transparent vendor; reasonable shape
- 4–7 items unchecked = significant cost risk. Request full TCO before signing
- 8–12 items unchecked = likely underestimating true spend by 25–40%
Most buyers we talk to score 6–9 on their first audit. That’s not because vendors are malicious but because MDR pricing evolved from enterprise software models that weren’t designed for transparency.
✅ How UnderDefense Covers Every Item
Every item listed above is included in our published per-asset price: compliance kits, 250+ integrations, full onboarding, concierge analyst access, and no annual escalation clause buried on page 14 of the MSA. We built the pricing model this way deliberately. If your CFO can’t verify total spend in five minutes, the pricing model is broken.
“UnderDefense MAXI helped us save money on security by automating tasks and making things run smoother. Additionally, their network tools helped us see what’s happening on our network better, which has helped us stop threats before they become big problems.”
— Julia K., Marketing Manager, Mid-Market UnderDefense G2 – Verified Review
“Really like using UnderDefense MAXI platform, as it has everything from early risk detection and compliance to incident response automation and 24/7 protection with MDR.”
— Serhii I., CEO, Small-Business UnderDefense G2 – Verified Review
“UnderDefense’s clear alerts save us time and keep our operations running smoothly.”
— Verified User in Hospitality, Mid-Market UnderDefense G2 – Verified Review
Q4: How Does AI SOC Pricing Compare to Traditional SOC and In-House SOC? (The Side-by-Side Cost Analysis)
This is the decision most CISOs and IT Directors are actually wrestling with: build it yourself, outsource to a traditional MSSP, or go with an AI-powered MDR. Each model has legitimate tradeoffs, and the cost gap is larger than most people expect.
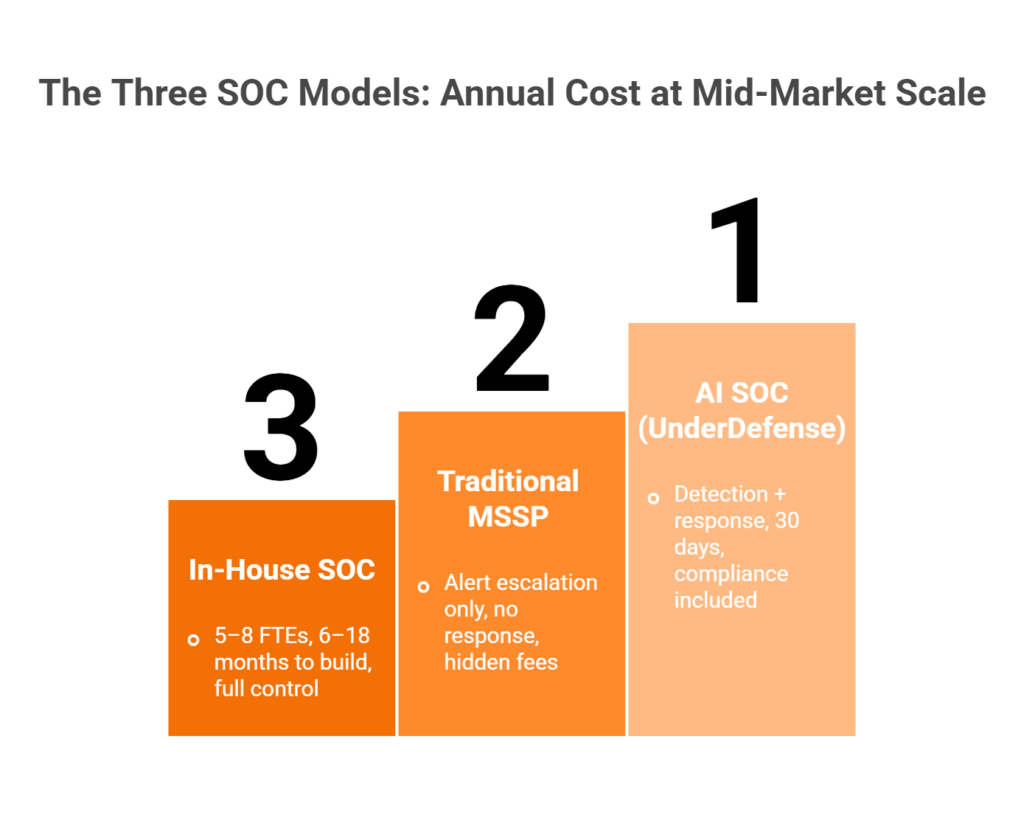
⏰ The Three Models, Framed Honestly
- In-House SOC: $1M–$4M+/year. Full control, full ownership. You manage the team, the tools, and the 2 AM ransomware calls.
- Traditional MSSP: $100K–$500K/year. Alert-only monitoring, where they watch dashboards and escalate tickets. Investigation and response remain yours.
- AI SOC with Human Response: $36K–$700K/year. Detection, containment, compliance, and concierge analyst response handled end-to-end.
💸 What In-House Actually Costs
True 24/7/365 coverage requires 5–8 analysts across tiers (168 hours/week ÷ 40 = 4.2 FTEs just for one around-the-clock seat). At $150K–$300K fully loaded per analyst, staffing alone runs $750K–$2.4M. Add SIEM licensing ($80K–$250K/yr), infrastructure ($50K–$200K/yr), and a 6–18 month build timeline. The Ponemon Institute pegs the average at $2.84M annually. The upside: full control and institutional knowledge. The downside: analyst burnout, 30%+ Tier 1 turnover, and most time consumed by commodity alerts AI handles in milliseconds.
How AI SOC Changes the Equation
AI-driven correlation reduces headcount needs by 60–80%. Automated triage eliminates 90%+ false positives before a human ever sees them. Integrated response collapses detection-to-containment from hours to minutes. At UnderDefense, we pair this with vendor-agnostic integration (250+ tools), 30-day onboarding, concierge response, 96% MITRE ATT&CK coverage, and 2-minute alert-to-triage and 15-minute escalation for critical incidents.
The Side-by-Side Comparison
| Dimension | In-House SOC | Traditional MSSP | AI SOC (UnderDefense) |
|---|---|---|---|
| Annual Cost (mid-market) | $1.2M–$2M+ | $100K–$500K | $119K–$140K |
| Staffing Required | 5–8 FTEs minimum | 0 (alert escalation only) | 0 (detection + response included) |
| Time to Operational | 6–18 months | 1–3 months | 30 days |
| Response Capability | Full (if staffed) | Alert escalation only | Detection + concierge containment |
| Tool Integration | Custom-built | Limited, often proprietary | 250+ vendor-agnostic |
| Pricing Transparency | High (you control budget) | Variable (hidden fees) | Published per-asset, no escalation |
| Compliance Support | Build your own | Add-on or separate vendor | Included (SOC 2, ISO, HIPAA) |
| Scalability | Hire more (months) | Upgrade tier (weeks) | Add assets, same price (days) |
🎯 When to Choose Each Model
- Go in-house if you have $2M+ budget, can retain senior analysts, and need sovereign control. Heavily regulated enterprises with unique threat profiles often justify this.
- Go traditional MSSP if you only need basic log monitoring and already have an internal team for investigation. This use case is shrinking fast.
- Go AI SOC if you want detection and response, need to be operational in 30 days, and demand predictable pricing without building from scratch. This is where the market is heading.
“They’re basically my security team since I can’t build one myself. They respond to problems so quickly.”
— Verified User, Mid-Market UnderDefense G2 – Verified Review
“We handle a vast amount of sensitive client data at our agency. UnderDefense MAXI has played a key role in protecting our infrastructure and improving our overall security, helping us spot the potential threats early.”
— Verified User in Marketing and Advertising, Mid-Market UnderDefense G2 – Verified Review
“With AW, they wanted a price increase per year of the multi-year contract that we couldn’t keep approved. They walked a bit of it back.”
— u/anonymous, r/k12sysadmin Reddit Thread
Q5: How Are AI SOC Pricing Models Evolving in 2026? (Per-Endpoint vs. Per-GB and the Agentic AI Shift)
For years, the security industry operated under a pricing model that actively punished you for doing the right thing. Per-GB ingestion pricing, the model most legacy SIEMs and MSSPs built their economics around, created a perverse incentive: the more visibility you wanted, the more you paid. In practice, that meant organizations suppressed logs, filtered out telemetry, and created security blind spots to stay within budget. Not because they didn’t care about security, but because they literally couldn’t afford to see everything.
Why Per-GB Broke Down
Think about what happened when cloud adoption accelerated. Every new SaaS application, every containerized workload, and every identity event generated more logs. AWS CloudTrail alone can produce hundreds of gigabytes per day in a moderately complex environment. Under per-GB pricing, your cloud expansion became a billing event, not a security improvement. Organizations were making architectural security decisions based on cost avoidance instead of threat coverage. That’s backwards. And now, agentic AI makes this model architecturally obsolete. As the Everest Group noted in early 2026, “agentic AI does not map cleanly to endpoint counts, as one AI agent can monitor thousands of endpoints, while one rogue device might consume disproportionate resources.” When a single AI agent can continuously process, correlate, and triage across thousands of log sources, the marginal cost of processing additional logs approaches zero. The per-GB model was designed for a world where human analysts manually reviewed events, and that world is rapidly disappearing.
The 2026 Standard: Per-Endpoint Pricing
The industry has responded. Per-endpoint pricing is now the dominant model for AI SOC and MDR services, and for good reason: it’s predictable, it scales linearly with your environment, and it doesn’t punish you for collecting more telemetry. You know exactly what you’ll pay when you add 50 endpoints next quarter, without waiting for a surprise true-up based on log volume. Agentic AI accelerates this shift further. When autonomous investigation collapses the labor economics that drove legacy pricing, with fewer analyst-hours per alert, faster triage, and automated containment, the cost structure fundamentally changes. Providers that still charge per-GB are essentially charging you for a resource (human analysis time) that AI is replacing. It’s like paying for horse feed after you bought a car.
Where UnderDefense Stands
We built our pricing to reflect both of these shifts. UnderDefense publishes per-asset pricing, $11–15 per endpoint per month, with no ingestion surprises, no quarterly true-ups, and no hidden overage fees. The UnderDefense MAXI platform uses an AI + human concierge model where AI handles detection, triage, and enrichment across your full telemetry stack, and dedicated analysts own the response. You don’t pay more because your Splunk instance grew, or because a noisy detection rule triggered 10,000 events instead of 1,000. The cost stays tied to what actually matters: the assets you’re protecting.
Looking Forward: Can Your Provider’s Model Survive?
As agentic AI matures through 2026–2027, expect per-endpoint pricing to become even more favorable for buyers. The Everest Group outlines emerging models: outcome-based pricing, workflow-execution pricing, even “digital FTE” models where AI agents are contracted like human analysts. These are still early, but the direction is clear. The industry is moving toward paying for results, not inputs. The question security leaders should ask right now isn’t “what’s my per-GB rate?” but whether your current provider’s economic model can survive when AI eliminates the labor overhead they’ve been charging you for. If their pricing depends on human analyst hours, and AI replaces 70% of that work, who captures the savings: you, or them?
Q6: How Do You Calculate AI SOC ROI and Justify It to Your CFO? (The Formula, Worked Example, and Board-Ready Template)
The hardest conversation in security isn’t about threat actors or zero-days. It’s the one where you walk into a boardroom and explain why the company should spend $180K per year on something that, if it works perfectly, produces zero visible incidents. CFOs think in payback periods, cost avoidance, and return on investment. If you can’t speak that language, your budget request dies in committee.
The ROI Formula
Here’s the formula that actually holds up under CFO scrutiny:
ROI = [(Cost Avoidance + Efficiency Gains + Risk Reduction) – AI SOC Investment] / AI SOC Investment × 100
Let’s define each variable with real benchmarks:
- Cost Avoidance: IBM’s 2025 Cost of a Data Breach Report puts the global average breach at $4.44 million, with U.S. organizations averaging a record $10.22 million. For mid-market organizations (1,000–5,000 employees), a conservative single-breach avoidance estimate lands around $244K when factoring probability-weighted exposure.
- Efficiency Gains: A fully loaded Tier-1 SOC analyst costs $85K–$110K annually (salary, benefits, training, tooling, and turnover). Replacing 2 FTE equivalents of alert triage and investigation work = ~$180K in efficiency gains.
- Risk Reduction: Quantified through cyber insurance premium reductions (typically 10–20% with documented 24/7 monitoring) and compliance penalty avoidance. Conservative estimate: $30K annually.
⭐ Worked Example: 1,000 Endpoints
| Component | Value |
|---|---|
| AI SOC Investment (annual) | $180,000 |
| Cost Avoidance (probability-weighted breach prevention) | $244,000 |
| Efficiency Gains (2 FTE-equivalent analyst replacement) | $180,000 |
| Risk Reduction (insurance + compliance) | $30,000 |
| Total Value | $454,000 |
| ROI | 152% |
| Payback Period | ~5 months |
This isn’t theoretical. These are numbers you can reproduce with your own loaded analyst rates, your insurer’s premium schedule, and IBM’s published benchmarks.
💰 5 Metrics Your CFO Actually Cares About
- Payback period: How many months until the investment pays for itself? (Target: under 8 months.)
- Cost avoidance vs. cost savings: CFOs distinguish between “we didn’t spend money we would have” and “we reduced existing spend.” Frame AI SOC as avoidance first, savings second.
- FTE-equivalent dollars: Translate analyst-hours saved into headcount economics. “This platform replaces 2.1 FTEs of Tier-1 work” resonates more than “it reduces MTTR.”
- Risk-adjusted return: Apply probability weighting to breach scenarios. A 15% annual breach probability × $4.44M average cost = $666K in expected annual loss.
- Insurance premium trajectory: Document your premium trend line. Show how 24/7 MDR coverage bends it downward.
📝 The 5-Slide Board Template
| Slide | Content | Key Data Point |
|---|---|---|
| 1. Current State | Existing coverage gaps, alert volume, analyst capacity | “X% of alerts uninvestigated in <24 hours” |
| 2. Cost of Inaction | Breach probability × average cost; compliance exposure | IBM benchmark: $4.44M global average |
| 3. Solution & Cost | AI SOC scope, integration plan, pricing | Published per-endpoint rate, total annual cost |
| 4. ROI & Payback | The formula above, populated with your numbers | “152% ROI, 5-month payback” |
| 5. Timeline & Quick Wins | 30/60/90-day milestones | “Full deployment in 30 days, first impact report at Day 30” |
With UnderDefense’s published pricing and documented outcomes, including a 30-day impact report that most reviewers specifically call out, every slide gets filled with real numbers, not “contact sales” placeholders.
❌ What Happens with Opaque Vendors
Here’s where this exercise falls apart: when your provider won’t publish pricing, won’t commit to onboarding timelines, and won’t document SLA-backed response times in the contract. Your CFO sees “TBD” on Slide 3, “pending custom quote” on Slide 4, and loses confidence in the entire business case. Transparent pricing isn’t a nice-to-have but what makes this presentation possible.
Q7: What Should You Ask Vendors Before Signing an AI SOC Contract? (The 10-Question Procurement Checklist)
Signing an MDR or AI SOC contract is a 1–3 year commitment that determines your security posture, budget predictability, and operational agility. Get it right, and you’ve bought yourself a force multiplier. Get it wrong, and you’re locked into an expensive alert feed that your team still has to investigate manually.
❌ The Wrong Way to Decide
Too many procurement decisions get made on brand recognition, integration count, or the lowest quote, without interrogating the contract terms that determine real cost. A vendor can quote $8/endpoint/month and still cost you more than a $15/endpoint provider once you factor in onboarding fees, add-on modules, data portability restrictions, and annual escalation rates. Arctic Wolf, for instance, uses custom quote-based pricing with 12–36 month contract terms and no published per-endpoint rate, making apples-to-apples comparison nearly impossible without deep procurement diligence.
✅ The 10-Question Procurement Checklist
Ask every vendor these ten questions. Score each 0–2 (0 = no/unclear, 1 = partial, 2 = full). The total tells you whether you’re evaluating a partner or an alert feed.
1. What is your pricing model, and how does it handle volume growth?
Per-endpoint is predictable. Per-GB punishes growth. Ask for the formula that calculates your bill at 2× your current endpoint count.
2. What’s included vs. add-on?
Compliance reporting, threat hunting, incident response, and user verification: if any of these are add-ons, your actual cost is higher than the quote.
3. What’s your onboarding timeline, and is there a fee?
Some vendors take 90+ days to reach full operational status. Others charge $15K–$50K for “implementation.” If onboarding takes three months, you’re unprotected for a quarter.
4. Do you integrate with my existing stack, or require replacement?
Vendor-agnostic providers work with your current SIEM, EDR, and cloud tools. Proprietary-stack vendors require you to rip and replace, adding migration cost and losing your tuned detection logic.
5. What’s your documented MTTR?
Not marketing MTTR, but contractual 2-minute alert-to-triage and 15-minute escalation for critical incidents, backed by SLA penalties. If they can’t put it in writing, they can’t guarantee it.
6. Do you respond/contain, or detect/escalate?
⚠️ This is the critical distinction. “We send you an alert” is not the same as “we isolate the endpoint, verify with the affected user, and contain the threat.” Ask specifically: what actions do your analysts take without requiring my team’s approval?
7. How do you verify suspicious user activity?
ChatOps-based user verification (contacting the actual user via Slack or Teams to confirm whether an action is legitimate) eliminates hours of manual investigation. If the vendor’s answer is “we escalate to your team for verification,” that’s not response but homework.
8. Is compliance reporting included?
SOC 2, HIPAA, PCI-DSS, and ISO 27001: if reporting is an add-on module or requires a separate engagement, budget accordingly.
9. What are your termination terms and data portability?
This is where contracts get ugly. Some providers lock you into non-cancellable multi-year terms with no data export. If you can’t take your detection rules, correlation logic, and historical data when you leave, you’re starting from scratch with the next vendor.
10. Can you provide customer references in my industry?
Generic case studies aren’t enough. Ask for a reference call with a company of similar size, stack, and compliance requirements.
Scoring Your Vendor
| Score Range | Verdict |
|---|---|
| 15–20 | ✅ True partner, invest with confidence |
| 10–14 | ⚠️ Gaps to negotiate before signing |
| Below 10 | ❌ Alert feed, not an MDR partner |
UnderDefense scores 18–20 on this framework: published per-asset pricing ($11–15/endpoint/month), vendor-agnostic integration across 250+ tools, 30-day onboarding with no implementation fee, documented response times backed by SLA, full respond-and-contain capability including ChatOps user verification, compliance reporting included, and flexible contract terms with full data portability.
“The speed of onboarding was a delightful surprise. In times where integrating new systems can take weeks, UnderDefense had us up and running in no time. Their 24/7 detection and response service is fast and comprehensive.”
— Valeriia D., Marketing Specialist UnderDefense G2 – Verified Review
“We were looking for an MDR provider and were choosing EDR tools. After a few calls with UnderDefense we realized that we could get way more value, so they truly became our go-to cybersecurity ally.”
— Oleksii M., Mid-Market UnderDefense G2 – Verified Review
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User in Program Development UnderDefense G2 – Verified Review
The bottom line: validate before you commit. A 30-day onboarding window with a documented impact report gives you the evidence to confirm whether a vendor delivers, before you’re locked in for years.
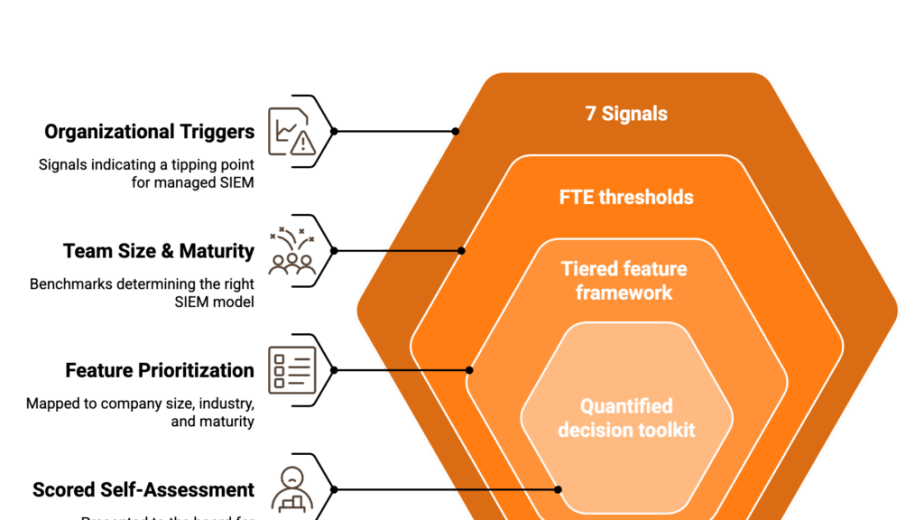
Q8: Which SOC-as-a-Service Providers Should You Evaluate in 2026?
Leading AI-powered SOC-as-a-Service providers for 2026 include UnderDefense, Arctic Wolf, CrowdStrike Falcon Complete, Expel, Red Canary, and Torq, each with distinct pricing models, response capabilities, and integration philosophies.
How the Market Has Split
The SOC-as-a-Service landscape has fractured into three distinct camps:
- Vendor-agnostic AI SOC platforms (UnderDefense, Expel): work with your existing stack, focus on detection + response across tools you already own, and publish transparent pricing.
- Proprietary ecosystem players (Arctic Wolf, CrowdStrike): deliver strong capabilities within their own technology stack, but often require tool replacement or operate behind custom-quote pricing walls.
- Pure-play AI automation (Torq, Radiant): focus on SOAR-style orchestration and agentic AI workflows, strong on automation but lighter on dedicated human analyst response.
The pricing and operational experience differs dramatically between camps. CrowdStrike Falcon Complete runs $179–$250+/endpoint/year at mid-market scale. Arctic Wolf doesn’t publish per-endpoint pricing at all, with enterprise contracts exceeding $96K+ annually. UnderDefense publishes $11–15/endpoint/month, fully inclusive of 24/7 monitoring, response, and compliance reporting.
What to Evaluate
When shortlisting providers, compare across five dimensions:
- Pricing transparency: Per-endpoint vs. per-GB vs. custom-quote. Can you calculate your annual cost without a sales call?
- Response capability: Detect-and-escalate vs. detect-respond-contain. Does the SOC take action, or hand you a ticket?
- Integration flexibility: How many of your current tools are supported? Do they require replacing your SIEM or EDR?
- Human analyst access: Is there a named analyst or concierge team, or do you submit tickets into a queue?
- Compliance inclusion: Are SOC 2, HIPAA, and ISO 27001 reporting built in, or billed separately?
Choosing the Right Fit
Each provider excels in different scenarios. CrowdStrike Falcon Complete is a natural fit if you’re already standardized on Falcon EDR. Arctic Wolf suits organizations willing to adopt their proprietary Concierge Security platform. Expel works well for teams that want strong investigation workflows with broad tool coverage. UnderDefense is built for organizations that need vendor-agnostic coverage, transparent pricing, and an AI SOC + Human Ally model that owns outcomes, not just alerts.
The right choice depends on your current stack, budget model, and operational requirements. Rather than relying on marketing comparisons, score each provider against the 10-question procurement checklist above, and validate with a proof-of-value deployment before committing to a multi-year contract.
Analysis based on Vendr verified buyer data, published pricing, documented SLAs, and G2 reviews across 500+ MDR deployments.
Q9: What’s the Bottom Line? (AI SOC Pricing Decision Matrix for 2026)
You’ve read the pricing models, the ROI math, the procurement checklist, and the provider landscape. Now here’s the tool that ties it all together: a decision matrix that maps your organization type, budget constraints, and operational requirements to the right provider and pricing model.
✅ AI SOC Provider Decision Matrix for 2026
| Org Type | Best-Fit Provider | Recommended Pricing Model | Expected Annual Range | Key Requirement | ⚠️ Biggest Hidden Cost Risk |
|---|---|---|---|---|---|
| SMB (<500 endpoints) | UnderDefense | Per-endpoint ($11–15/ep/mo) | $66K–$90K | Vendor-agnostic, fast onboarding, compliance included | Onboarding fees and add-on modules disguised as “base price” |
| Mid-Market (500–2,000 endpoints) | UnderDefense, Expel | Per-endpoint | $90K–$360K | 24/7 response + containment, ChatOps user verification, existing stack integration | Per-GB ingestion overages; vendor lock-in destroying tuned detection logic on exit |
| Enterprise (2,000+ endpoints) | UnderDefense, CrowdStrike Falcon Complete | Per-endpoint or custom | $240K–$500K+ | Named analyst concierge, SLA-backed response times, multi-cloud coverage | Annual escalation clauses (Arctic Wolf: up to 8% annually), non-cancellable multi-year commitments |
| Highly Regulated (HIPAA, PCI, SOC 2) | UnderDefense, Red Canary | Per-endpoint with compliance bundled | $90K–$250K | Audit-ready reporting included in base price, data sovereignty, compliance evidence on demand | Compliance reporting sold as add-on; $15K–$50K “professional services” for audit support |
4 Decision Rules That Cut Through the Noise
These four rules will eliminate 80% of bad-fit providers before you even schedule a demo:
💰 Predictable budgeting → per-endpoint, reject per-GB. If your cloud footprint is growing (and whose isn’t?), per-GB pricing guarantees budget overruns. Per-endpoint scales linearly and lets your CFO forecast with confidence.
✅ Existing SIEM/EDR investments → vendor-agnostic, reject proprietary lock-in. If you’ve spent years tuning Splunk, CrowdStrike, or SentinelOne detection rules, a provider that requires replacing your stack means losing all that institutional knowledge. As one Arctic Wolf reviewer put it plainly:
“Anything you want to look at or changes you need to make in the product must go through their engineering team. As an MSP, this is a horrible way to do business for us.”
— Matt C., Manager, Cybersecurity Services Arctic Wolf – G2 Verified Review
⚠️ Need response, not just detection → verify containment in the base price. “Detect-and-escalate” is not the same as “detect-respond-contain.” If your MDR provider hands you a ticket at 2 AM instead of isolating the compromised endpoint, you’re paying for a notification service, not security operations.
“Lack of true remediation in the response, costing us significantly in resources and introducing risks in security.”
— VP of Technology, Services Arctic Wolf – Gartner Verified Review
📝 Compliance driver → confirm audit support is bundled. If SOC 2, HIPAA, or ISO 27001 reporting is an add-on, your “all-inclusive” quote isn’t all-inclusive. Ask to see the compliance deliverables before signing.
Get Your Number in 60 Seconds
We built UnderDefense to survive exactly the scrutiny this article describes: published per-asset pricing, vendor-agnostic integration across 250+ tools, 24/7 AI SOC + Human Ally response, compliance reporting included, and flexible contracts with full data portability.
Use the SOC Cost Calculator: enter your endpoint count, select your coverage tier, and get a transparent, all-inclusive price in 60 seconds. No sales call required. No “contact us for pricing.” No surprises at renewal.
⭐ The Track Record
500+ organizations trust UnderDefense today, with 100% ransomware prevention, 2-minute alert-to-triage and 15-minute escalation for critical incidents, and full deployment in 30 days, not 90, not “several months.”
“It’s reassuring to know they’re always watching for threats, and it doesn’t cost a fortune. They catch and stop problems quickly, which is a huge relief.”
— Serhii B., Chief Information Security Officer UnderDefense G2 – Verified Review
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., Enterprise (1,000+ emp.) UnderDefense G2 – Verified Review
“UnderDefense is surprisingly affordable considering the level of protection we get. Their proactive threat hunting and rapid response have saved us from incidents that could have been incredibly costly.”
— Verified User in Program Development UnderDefense G2 – Verified Review
1. How much does an AI SOC cost per endpoint in 2026?
AI SOC pricing in 2026 ranges from approximately $10 to $37 per endpoint per month, depending on the provider, tier, and what’s included in the base price. At the transparent end of the spectrum, we publish per-asset pricing at $11–15 per endpoint per month, which includes 24/7 monitoring, concierge analyst response, compliance kits, 250+ tool integrations, and full onboarding with no add-on surprises.
At the higher end, providers like Arctic Wolf can run $16–30/user/month through channel partners, while CrowdStrike Falcon Complete ranges from $15–21/endpoint/month at mid-market scale. The critical distinction is what “base price” actually covers. A $10/endpoint quote that excludes compliance reporting, active remediation, or incident response retainers can easily exceed $20/endpoint once add-ons are factored in.
For a 500-endpoint mid-market organization, annual costs range from approximately $59.5K (UnderDefense) to $180K (Arctic Wolf), before accounting for hidden fees like data ingestion overages, onboarding charges, or annual escalation clauses. We recommend using the SOC Cost Calculator to model your exact environment and get an all-inclusive figure you can bring directly to your CFO.
2. What hidden fees should you watch for in AI SOC and MDR contracts?
We’ve reviewed hundreds of MDR contracts and consistently see 12 line items that inflate total cost of ownership by 25–40% beyond the initial quote. The most common hidden fees include:
-
Data ingestion overage charges (providers cap log volume, and overages spike during active investigations)
-
Onboarding and professional services fees ($5K–$50K range)
-
Compliance reporting sold as a separate SKU (SOC 2, HIPAA, PCI reports)
-
Incident response retainer fees charged separately from MDR monitoring
-
Annual price escalation clauses (Arctic Wolf contracts include 5–8% auto-increases per Vendr data)
-
Early termination penalties with non-cancellable, non-refundable terms
-
SIEM/log platform licensing tied to proprietary systems that lock in your data
The pattern is clear: vendors that hide pricing behind custom quotes also tend to bury these costs deep in contract terms. We built our pricing model to include every one of these items in the published per-asset rate, with no escalation clauses and no add-on surprises at renewal.
3. How does AI SOC pricing compare to building an in-house SOC?
The cost gap between an AI SOC and an in-house SOC is dramatic at every organization size. A mid-market in-house SOC costs $1.2M–$2M annually, driven by 5–8 analyst FTEs ($150K–$300K fully loaded each), SIEM licensing ($80K–$250K/yr), and a 6–18 month build timeline. The Ponemon Institute pegs the average at $2.84M per year.
An AI SOC with human response covers the same mid-market environment for $119K–$140K annually, with detection, containment, compliance, and concierge analyst response handled end-to-end. That’s roughly 90% less than in-house, operational in 30 days instead of months, and with zero staffing burden.
Traditional MSSPs fall in between at $100K–$500K, but deliver alert-only monitoring with no response capability. The key tradeoff: in-house gives you full control and institutional knowledge, while AI SOC gives you 24/7 detection and response at a fraction of the cost. For most mid-market organizations without a $2M+ security budget, AI SOC is the clear economic winner.
4. How do you calculate AI SOC ROI to justify the investment to your CFO?
We use a formula that has held up under CFO scrutiny across hundreds of budget presentations:
ROI = [(Cost Avoidance + Efficiency Gains + Risk Reduction) – AI SOC Investment] / AI SOC Investment × 100
For a worked example at 1,000 endpoints with a $180K annual AI SOC investment: cost avoidance (probability-weighted breach prevention) contributes $244K, efficiency gains from replacing 2 FTE equivalents of Tier-1 alert triage contribute $180K, and risk reduction through insurance premium decreases and compliance penalty avoidance adds $30K. Total value: $454K. ROI: 152%. Payback period: approximately 5 months.
The five metrics CFOs care about most are payback period (target under 8 months), cost avoidance vs. cost savings, FTE-equivalent dollar translation, risk-adjusted return using probability-weighted breach scenarios, and insurance premium trajectory. Use our SOC cost comparison guide to populate these numbers with your own data and build a board-ready 5-slide presentation that turns “TBD” into real figures.
5. What is the difference between per-endpoint and per-GB pricing for AI SOC?
Per-endpoint and per-GB represent fundamentally different pricing philosophies, and in 2026, the industry has decisively shifted toward per-endpoint. Per-GB pricing charges based on the volume of log data ingested, which means your bill increases every time your cloud footprint grows, a noisy detection rule fires, or an investigation generates additional telemetry. This model, common among legacy SIEMs and older MSSPs, creates a perverse incentive: organizations suppress logs and filter out telemetry to control costs, creating security blind spots.
Per-endpoint pricing charges a fixed rate per protected asset, regardless of how much log data that asset generates. It’s predictable, scales linearly, and lets your CFO forecast with confidence. When you add 50 endpoints next quarter, you know exactly what the cost will be.
Agentic AI has made per-GB architecturally obsolete. When a single AI agent processes thousands of log sources at near-zero marginal cost, charging per-GB means paying for human analysis time that AI has already replaced. We publish per-asset pricing at $11–15/endpoint/month with no ingestion surprises, no quarterly true-ups, and no hidden overage fees through the UnderDefense MAXI platform.
6. What should you ask AI SOC vendors before signing a contract?
We recommend a 10-question procurement checklist scored on a 0–2 scale per question. The most critical questions are:
-
What is your pricing model, and how does it handle volume growth?
-
What’s included vs. add-on? (Compliance reporting, threat hunting, incident response, and user verification should all be in base price.)
-
What’s your onboarding timeline, and is there a fee?
-
Do you integrate with my existing stack, or require replacement?
-
What’s your documented, SLA-backed response time?
-
Do you respond and contain, or detect and escalate?
-
How do you verify suspicious user activity?
-
Is compliance reporting included?
-
What are your termination terms and data portability?
-
Can you provide customer references in my industry?
Score 15–20 and you’re evaluating a true partner. Score below 10 and you’re looking at an alert feed, not an MDR provider. We score 18–20 on this framework with published pricing, vendor-agnostic integration across 250+ tools, 30-day onboarding, full respond-and-contain capability, and flexible contracts with full data portability. Download our SOC Provider Evaluation Checklist for the complete scoring template.
7. Which AI SOC and SOC-as-a-Service providers should you evaluate in 2026?
The SOC-as-a-Service landscape in 2026 has fractured into three camps: vendor-agnostic AI SOC platforms (UnderDefense, Expel), proprietary ecosystem players (Arctic Wolf, CrowdStrike), and pure-play AI automation providers (Torq, Radiant).
When shortlisting, compare across five dimensions: pricing transparency (can you calculate cost without a sales call?), response capability (detect-and-escalate vs. detect-respond-contain), integration flexibility (how many of your current tools are supported?), human analyst access (named concierge team vs. ticket queue), and compliance inclusion (built in or billed separately).
CrowdStrike Falcon Complete fits organizations already standardized on Falcon EDR at $179–$250+/endpoint/year. Arctic Wolf suits those willing to adopt their proprietary platform, though enterprise contracts exceed $96K+ annually with no published per-endpoint rate. We built UnderDefense for organizations that need vendor-agnostic coverage, transparent pricing at $11–15/endpoint/month, and an AI SOC + Human Ally model through UnderDefense MAXI that owns outcomes, not just alerts.
8. Can we switch from Arctic Wolf to another MDR provider without losing our data and detection logic?
Switching from Arctic Wolf presents challenges across all three lock-in layers. Because Arctic Wolf operates a proprietary cloud-native platform that functions as a SIEM replacement, your logs, detection rules, and historical telemetry all live inside their ecosystem. Multiple Gartner reviewers reported that when they asked Arctic Wolf to provide logs during an investigation, no logs could be provided.
To minimize exit friction, we recommend:
-
Requesting explicit data export terms in writing before signing any contract.
-
Asking what standard formats (JSON, CEF, Syslog) are supported for export.
-
Confirming post-termination data retention policies. Some providers delete data 30 days after contract end.
-
Evaluating BYOS-compatible providers where your data stays in your SIEM from day one.
At UnderDefense, we designed for zero exit friction. Your data stays in your SIEM, your detection rules stay portable, and there is nothing to migrate if you leave. Learn more about how organizations are switching cybersecurity providers without operational disruption.
The post AI SOC Pricing Guide 2026: Complete Cost Breakdown appeared first on UnderDefense.