Q1. Why Does the Traditional Hiring Path Fail for 24/7 SOC Coverage?
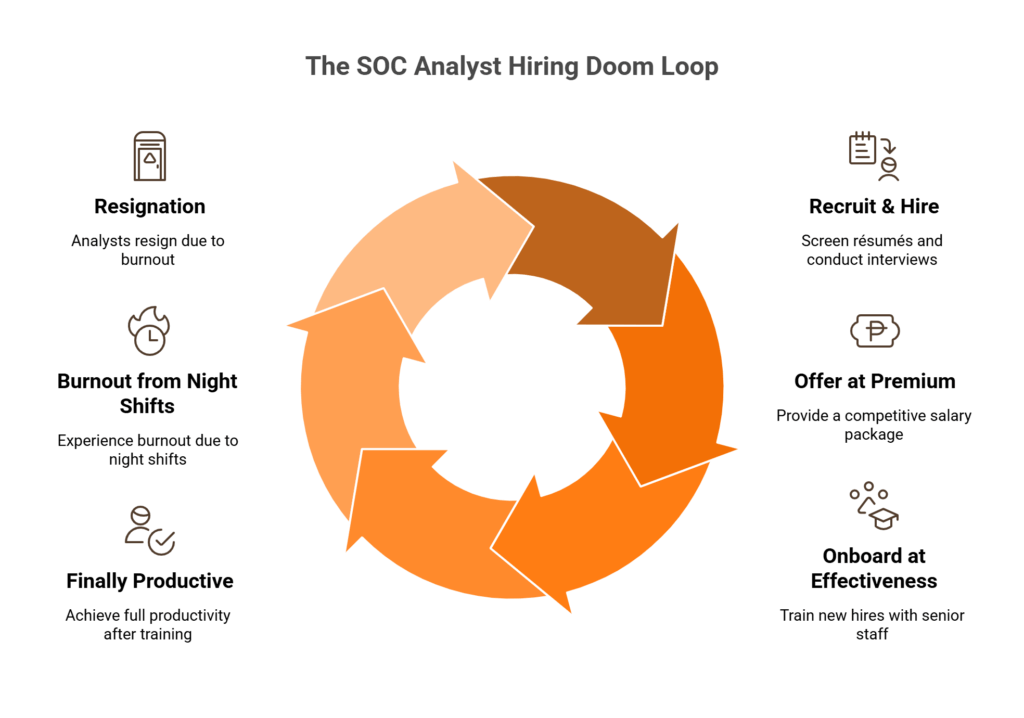
You post the SOC analyst role on a Monday in January. By March, your recruiter has screened 200 résumés, interviewed 30 candidates, and lost the top three to enterprises offering $200K+ packages. Month 4, you finally extend an offer at a 20% salary premium to close. Month 6, the new analyst starts, but they’re running at maybe 40% effectiveness while your senior engineer spends half her week onboarding them instead of doing threat-hunting work. Month 12, the analyst is finally productive, just in time for the second hire you desperately need to quit because she’s burned out from six months of overnight shifts. Month 18, the first analyst updates LinkedIn. Month 19, you’re back to square one, and that 2 AM coverage gap you set out to close? Still wide open.
If this reads like your last two years, you’re not alone.
⚠️ The Structural Root Causes
The hiring path doesn’t fail because of bad recruiters or weak employer brands. It fails because the math is structurally broken. The global cybersecurity workforce gap has hit 4.8 million unfilled positions, a 19% year-over-year increase, while 90% of security teams report critical skills gaps, especially in AI and cloud security. SOC analyst median tenure hovers around 18 months, driven by alert fatigue, night-shift burnout, and the relentless monotony of triaging thousands of alerts that turn out to be false positives.
Here’s the part most staffing plans ignore: true 24/7 coverage requires a minimum of 5–6 FTEs just for shift rotation, and that’s before PTO, sick leave, or training days. Even if you successfully hire all six, a single resignation collapses your coverage model overnight.
💸 The Hidden Costs That Compound
The financial damage extends far beyond base salaries:
- $150K–$250K+ fully loaded cost per analyst (salary, benefits, tools, and training)
- 3–6 months average time-to-fill for mid-level SOC roles
- 6-month ramp period at ~40% effectiveness
- 15–25% recruiter fees on first-year salary
- Opportunity cost of senior staff pulled from strategic work into training
- Compounding cycle when the entire process repeats every 18 months
Multiply this across three to four hires, and the hiring path alone can consume $500K–$1M before a single overnight alert is investigated with confidence.
✅ What the Destination Actually Looks Like
The goal isn’t eliminating your security team but eliminating the dependency on hiring as your coverage strategy. In the model this article builds toward, your team focuses on strategic security initiatives during business hours. AI handles autonomous triage and investigation 24/7 with consistent accuracy, no fatigue at 3 AM Saturday. Confirmed threats get escalated with full context and recommended actions. Night and weekend incidents are contained before your team wakes up.
This article walks through three pillars to get there: (1) the economics and speed advantages of AI-augmented investigation, (2) practical coverage blueprints for teams of 2, 5, and 10 with shift matrices you can implement immediately, and (3) how to evaluate the right AI SOC platform without getting locked into a vendor’s ecosystem. The question isn’t whether to hire but how to design coverage that doesn’t depend on hiring.
Q2. What Does It Really Cost to Build a 24/7 SOC, and Why Can’t You Hire Your Way There in 2026?
Most SOC budget proposals start with headcount. That’s the first mistake. Before you can staff a single shift, you need to understand the 168-hours-per-week math that breaks every understaffed security team.
24/7 coverage requires three 8-hour shifts, seven days a week, totaling 4.2 FTEs at absolute minimum. Factor in PTO, sick leave, training days, and the reality that you can’t have a single-point-of-failure on any shift, and the real number lands at 5–6 FTEs. Most organizations that take this seriously budget for 7–8. At $100K–$180K fully loaded per analyst, staffing alone runs $500K–$1.08M/year, before a single tool license is purchased.
💰 The Technology Stack No One Budgets Accurately
Staffing is only half the equation. Here’s what the infrastructure actually costs:
| Component | Annual Cost Range |
|---|---|
| SIEM licensing | $50K–$250K |
| EDR/XDR platform | $15–$50/endpoint/month |
| SOAR platform | $100K–$300K |
| Threat intelligence feeds | $25K–$100K |
| Security data lake/storage | $30K–$100K |
| Facility & hardware overhead | $50K–$150K |
Total year-one build cost: $1M–$2M+. Ongoing annual cost: $1.5M–$2.5M.
For a mid-market company with 500–2,000 employees, this is often the entire security budget, leaving nothing for proactive threat hunting, compliance automation, or incident response retainers.
❌ The Talent Shortage That Makes Even Funded Hiring Impossible
Even organizations with approved budgets can’t execute. The ISC2 2025 Cybersecurity Workforce Study documents 4.8 million unfilled cybersecurity positions globally, with demand growing 35% year-over-year against roughly 10% supply growth. Over 90% of organizations report skills gaps in critical areas like cloud security and AI. Mid-market companies consistently lose hiring competitions to enterprises dangling $200K+ compensation packages with equity and remote-first flexibility.
For the first time, ISC2 found that economic pressures and budget cuts have actually overtaken a lack of qualified talent as the primary driver of staffing shortages. Companies want to hire but can’t get budget approval, and even those that do can’t find the people.
⏰ The Night-Shift Premium Problem
This is the cost modeling no competitor covers. Analysts willing to work overnight and weekend rotations command 15–30% salary premiums. Night-shift turnover runs approximately 2x daytime rates. And investigation accuracy drops 20–30% during overnight hours due to cognitive fatigue, meaning you pay more for demonstrably lower-quality outcomes.
| Shift | Hours | Fully Loaded $/Hour | Turnover Rate |
|---|---|---|---|
| Day (8AM–4PM) | Standard | $55–$90 | Baseline |
| Swing (4PM–12AM) | +10–15% | $65–$100 | 1.3x |
| Night (12AM–8AM) | +20–30% | $75–$115 | 2.0x |
✅ The AI-Augmented Alternative (Side-by-Side)
| Model | Annual Cost | FTEs Required | Coverage Quality |
|---|---|---|---|
| Traditional 24/7 SOC | $1.5M–$2.5M | 5–8 | Degrades off-hours |
| AI-Augmented SOC (2–3 analysts) | $300K–$720K | 2–3 | Consistent 24/7 |
The math produces a 40–60% cost reduction with equivalent or superior coverage. UnderDefense’s published pricing of $11–$15/endpoint/month includes 24/7 AI-driven monitoring, dedicated human analysts, compliance automation, and the full technology stack, replacing the need to build $1M+ infrastructure and compete for analysts who simply don’t exist. Use the SOC Cost Calculator to model your specific scenario.
Q3. How Does AI Increase Investigation Speed Across Every Shift, and Where Do Humans Still Matter?
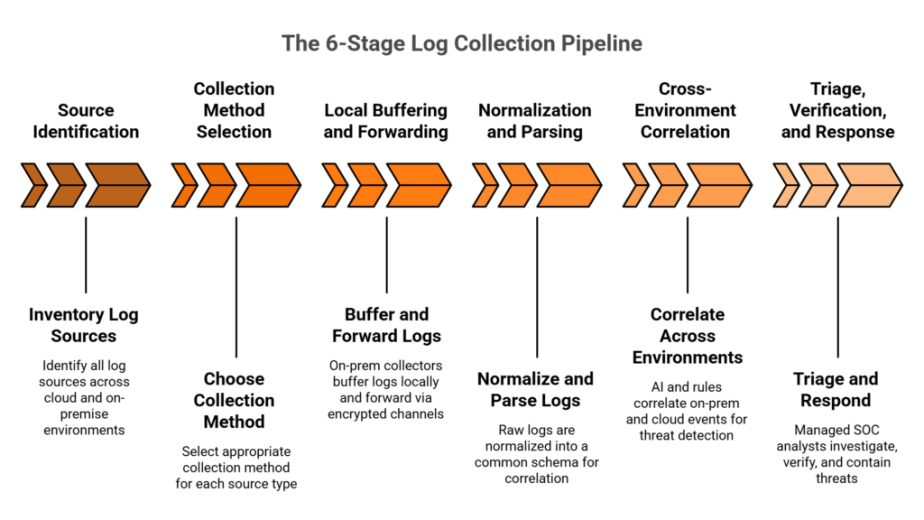
A typical SOC analyst investigating a single alert manually touches 4–6 different tools: SIEM, EDR, identity provider, threat intelligence platform, and ticketing system, spending 25–45 minutes per investigation. At 3 AM on a Saturday, that same investigation takes longer, misses more context, and produces lower-confidence decisions. Alert volume doesn’t decrease off-hours. Investigation quality does. This is the night-shift quality problem, and hiring more analysts doesn’t solve it because the degradation is cognitive, not structural.
❌ The “Detection Without Investigation” Trap
Traditional MDR and MSSP approaches, whether it’s Arctic Wolf’s proprietary-stack escalation model, CrowdStrike’s endpoint-focused OverWatch, or legacy MSSPs offering log monitoring, share a common architectural limitation: they detect and escalate, but the investigation burden falls back on your team. In a mid-market environment generating 11,000+ daily alerts, escalation-based models collapse at scale. Alert volume without context is noise with a vendor logo on it.
“Started out well but over the years the service has consistently not met expectations. The issues that we have experienced has greatly outweighed the benefits.”
— CISO, Manufacturing (3B–10B) Arctic Wolf – Gartner Verified Review
⭐ AI Investigation Benchmarks That Change the Math
The data from 2025 is unambiguous. The CSA Benchmark Study shows AI-assisted analysts complete investigations 45–61% faster with 22–29% higher accuracy than manual counterparts. Intezer’s AI SOC averages 2 minutes 21 seconds per investigation, with a median of just 15 seconds. Rapid7’s AI Alert Triage achieves a 99.93% benign classification accuracy across 8 trillion weekly alerts. Critically, AI performance doesn’t degrade at 3 AM.
But here’s where the conversation gets honest. AI and humans aren’t interchangeable. They’re complementary:
✅ AI automates: alert enrichment, log correlation, false-positive dismissal (99%+), IOC matching, baseline deviation analysis, and automated containment of known-bad indicators
✅ Humans decide: “Is this authorized?” contextual verification, business-impact assessment, containment scope decisions, stakeholder communication, and policy exceptions
✅ How UnderDefense Bridges the Gap
We built the UnderDefense MAXI platform specifically around this delineation. MAXI performs autonomous alert enrichment and correlation across 250+ integrated tools, completing AI investigation in under 60 seconds. When investigation requires organizational context, such as “Did this user authorize this OAuth app at 2:41 AM?”, our dedicated concierge analysts verify directly with affected users via Slack, Teams, or email. This closes the last-mile gap that pure AI cannot: human judgment for ambiguous threats.
“The biggest win for me was getting actual control over our security alerts. Their team cleaned up our configurations and got the noise under control within the first week. Now when we get an alert, we know it’s something worth looking into.”
— Verified User, Marketing & Advertising UnderDefense – G2 Verified Review
“UnderDefense has changed our approach to cybersecurity. With their security monitoring and incident response we know our endpoints are well-protected. It was a huge relief for our whole team.”
— Yaroslava K., IT Project Manager UnderDefense – G2 Verified Review
The Real Contrast
Traditional SOC: 25-minute manual investigation, quality drops 20–30% on night shifts, analyst burns out at month 18. AI-augmented SOC: 2-minute investigation, consistent accuracy 24/7, analyst focuses on confirmed threats only. The goal isn’t replacing humans with AI but freeing humans from the work AI does better, so they can do the work only humans can do.
Q4. What Happens During Your Coverage Gaps? Adversary Breakout Time vs. Staffing Reality
It’s 2:17 AM on a Saturday. An attacker achieves initial access through a compromised VPN credential. By 2:22 AM, five minutes in, they’ve dumped Active Directory credentials. By 2:34 AM, they’ve moved laterally to your file server. By 2:46 AM, 29 minutes after initial access (the current average breakout time), they’ve established persistence and begun data staging. Your on-call analyst’s phone buzzed at 2:18 AM with an alert. One of 47 that week. They silenced it and went back to sleep.
This isn’t hypothetical but the documented adversary playbook running against your staffing model.
⏰ The Numbers That Should Keep You Up at Night
CrowdStrike’s 2025 Global Threat Report documents the average eCrime breakout time dropping to 48 minutes, down from 62 minutes the prior year, with the fastest observed breakout at just 51 seconds. The 2026 report accelerates this further: average breakout now sits at 29 minutes, with a fastest recorded time of 27 seconds. Meanwhile, a typical understaffed SOC has zero human coverage for 76–128 hours per week across nights, weekends, and holidays.
Map those two data points onto a single 24-hour clock and the gap becomes visceral. Your staffed hours, roughly 8 AM to 6 PM Monday through Friday, cover maybe 50 of the week’s 168 hours. The remaining 118 hours are precisely when adversaries are most active, because they know no one is watching.
💸 The Compounding Cost of Every Uncovered Hour
IBM’s 2025 Cost of a Data Breach Report puts hard numbers on this gap. Breaches identified and contained in under 200 days averaged $3.87 million. Those exceeding 200 days cost $5.01 million, a 29% increase. When the attacker discloses the breach first, through extortion or public leak, average cost jumps to $5.08 million. Every hour of coverage gap is a compounding risk multiplier, and the hours you’re most likely unstaffed are exactly when adversaries are most active.
Organizations with continuous SOC coverage contain breaches dramatically faster. The difference between a 3 AM detection at minute-two and a Monday-morning discovery at hour-fifty isn’t incremental. For mid-market companies where a single breach can exceed annual revenue, it’s existential.
✅ How AI Closes the Breakout Window
In the same 2:17 AM scenario with AI-augmented coverage, the timeline inverts. AI investigates the 2:18 AM VPN anomaly alert in 15 seconds. It correlates the credential anomaly with the Active Directory dump four minutes later, auto-contains the compromised account, and isolates affected endpoints by 2:23 AM. A human analyst receives a full incident summary with recommended actions, not a raw alert. Total breakout window closed: under 6 minutes versus 29 minutes for the attacker.
We built UnderDefense’s AI + Human Ally model specifically for this scenario. UnderDefense MAXI detects and auto-investigates in under 60 seconds. Our concierge analysts verify and contain within a 2-minute alert-to-triage and 15-minute escalation SLA for critical incidents. Your team gets a morning incident report, not a 3 AM phone call. Across 500+ MDR clients, this model has maintained 100% ransomware prevention precisely because we close the breakout window before the attacker reaches persistence.
Q5. Practical 24/7 Coverage Model for a Team of 2: The AI-First Blueprint
A team of 2 covers 16 of 168 weekly hours. That’s 9.5% of the week with human eyes on your environment. The remaining 90.5%, nights, weekends, and holidays, is where adversaries operate and where most breaches begin. Traditional thinking says 24/7 coverage with two people is impossible. With an AI-first operating model, it’s not only possible but how most of our mid-market clients actually run.
Here’s the shift model that works:
⏰ The Team-of-2 Shift Matrix
| Time Block | Mon–Fri | Sat–Sun |
|---|---|---|
| 8AM–5PM | Analyst A (primary) | AI Autonomous |
| 9AM–6PM | Analyst B (staggered, 1-hr overlap) | AI Autonomous |
| 6PM–8AM | AI Autonomous + On-Call Escalation | AI Autonomous + On-Call Escalation |
The one-hour overlap (9AM–10AM) is intentional. It’s your daily handoff window for reviewing overnight AI activity, triaging escalated incidents, and aligning on priorities. Outside business hours, the AI SOC platform handles autonomous investigation 24/7. Only confirmed critical incidents trigger on-call escalation via context-rich mobile alerts, not raw alert text. Expected distribution: AI handles 85–95% of alerts autonomously; human on-call activation averages 2–4 times per week.
💰 Technology Requirements and Cost Reality
The infrastructure for this model requires four components: an AI SOC platform with autonomous triage and investigation, SOAR with pre-built containment playbooks for auto-response during off-hours (credential revocation, endpoint isolation, and firewall rule injection), a mobile escalation app delivering full investigation summaries, and an MDR partner for Tier-2/3 support. Total cost: $8K–$15K/month versus $50K–$90K/month to hire 4–5 additional analysts.
✅ Day in the Life: Tuesday 3 AM Incident
This is where the model proves itself:
- 3:02 AM, UnderDefense MAXI detects anomalous PowerShell execution on the finance server.
- 3:02:15 AM, AI enriches with user context (service account, no scheduled maintenance), threat intel (matches Cobalt Strike staging behavior), and network context (lateral movement from a user workstation).
- 3:02:45 AM, AI confidence: HIGH THREAT. Auto-containment triggered, endpoint isolated, service account disabled.
- 3:03 AM, Context-rich mobile alert sent to on-call Analyst A: “Confirmed threat contained. Cobalt Strike staging detected and isolated. Recommended morning action: forensic review of source workstation.”
- 3:04 AM, Analyst A acknowledges, reviews summary, confirms containment is sufficient, goes back to sleep.
- 8:15 AM, Full forensic review during business hours with complete incident timeline.
Total human time: 2 minutes. Total threat exposure: 45 seconds.
⚠️ Risk Mitigation for Single Points of Failure
The critical vulnerability for teams of 2 is PTO and illness. The mitigation: your MDR partner serves as surge capacity. UnderDefense’s concierge analysts step in as on-call backup during PTO periods, maintaining continuous coverage without interruption. AI containment playbooks auto-isolate confirmed threats above 95% confidence thresholds without human approval. Monthly tabletop exercises keep both analysts cross-trained on all escalation procedures.
We built UnderDefense’s model specifically for this team size. UnderDefense MAXI provides autonomous AI investigation across your existing tool stack with 250+ integrations, while dedicated concierge analysts act as after-hours Tier-2/3, verifying ambiguous alerts with affected users via ChatOps and containing confirmed threats before your team starts their day.
Q6. Practical 24/7 Coverage Model for a Team of 5: The Hybrid Operations Blueprint
Five analysts is the traditional minimum for 24/7 shift coverage. But here’s the paradox most SOC planning documents ignore: in a traditional model, all five analysts are consumed by Tier-1 triage, processing 11,000+ daily alerts, leaving zero capacity for proactive threat hunting, process improvement, or strategic security initiatives. You have 24/7 “eyes on glass,” but those eyes are watching noise, not hunting threats.
With AI augmentation, those same 5 analysts transform from alert processors into threat hunters and incident responders.
⏰ The Team-of-5 Hybrid Shift Model
| Shift | Hours | Staffing | Primary Function |
|---|---|---|---|
| Day | 8AM–4PM | 2 analysts | AI-escalated investigations + threat hunting |
| Swing | 4PM–12AM | 2 analysts | AI-escalated investigations + vulnerability assessment |
| Night | 12AM–8AM | 1 analyst (AI supervisor) | Review AI-escalated confirmed threats + proactive hunting |
Weekly rotation follows a 5-days-on / 2-days-off pattern, with one analyst always off-rotation for rest or training. AI handles 80–90% of Tier-1 triage across all shifts, meaning human analysts only engage with pre-investigated, context-enriched incidents.
⭐ The Role Evolution That Fixes Retention
This is the retention argument that salary bumps can’t replicate. The role transformation looks like this:
- Before AI: 80% alert triage, 20% investigation, monotonous, burnout-inducing, 18-month median tenure.
- After AI: 20% AI-escalated review, 40% proactive threat hunting, 40% incident response and process improvement, meaningful, career-building, 2–3x longer retention.
Analysts doing strategic work stay dramatically longer than those drowning in false positives. This addresses the 18-month burnout cycle at its root cause, not with higher compensation, but with better work. When your SOC analyst spends Tuesday morning hunting for signs of credential abuse instead of closing 400 false-positive alerts, they’re building skills, finding real threats, and staying engaged.
💰 Cost Comparison: Same Team, Different Outcomes
| Model | Annual Cost | Effective Coverage Quality |
|---|---|---|
| Traditional 5-person SOC (all triage) | $800K–$1.4M (salaries + tooling) | Reactive, triage-heavy, minimal hunting |
| AI-augmented 5-person SOC | $560K–$1.08M (salaries + AI platform) | 3–5x higher effective coverage, proactive hunting |
The cost reduction of 20–30% is meaningful, but the real ROI is qualitative: your team shifts from reactive alert processing to proactive threat elimination. That’s the difference between a SOC that generates tickets and a SOC that prevents breaches.
✅ How UnderDefense Eliminates Tier-1 Entirely
We designed UnderDefense’s model for exactly this transformation. UnderDefense MAXI AI investigates every alert across your existing tool stack, no rip-and-replace. Our concierge analysts verify ambiguous cases directly with affected users via Slack, Teams, or email, closing the contextual gap that pure automation cannot. Your 5 analysts focus exclusively on threat response, hunting, and organizational security strategy, the work they were actually hired to do.
Q7. Practical 24/7 Coverage Model for a Team of 10: The Scaled Operations Blueprint
Organizations with 10 security professionals face constant pressure to scale to 15–20 to cover 24/7 with adequate depth: two analysts per shift, dedicated incident responders, proactive threat hunters, and a compliance/GRC function. At $150K–$180K fully loaded per additional hire, that’s $750K–$1.8M in salary alone to fill the gap. AI augmentation lets a team of 10 deliver the output of a 15–20 person enterprise SOC at current headcount.
⏰ The Team-of-10 Scaled Model
| Role | Headcount | Coverage |
|---|---|---|
| Shift analysts (3-shift rotation, 2 per shift) | 6 | 24/7 (always 2 on duty) |
| Dedicated threat hunters | 2 | Business hours primary, AI-assisted off-hours |
| Incident response lead | 1 | Business hours + on-call for major incidents |
| SOC manager / compliance officer | 1 | Business hours, strategic oversight |
The rotation builds in rest days, training blocks, and flex coverage for surge events. AI handles autonomous triage 24/7 across all shifts, meaning your on-duty pair reviews only pre-investigated, confirmed threats rather than raw alert volume.
✅ Capability Multiplier Metrics
The enterprise-grade outcomes from a mid-market team size:
| Metric | Traditional 10-Person SOC | AI-Augmented 10-Person SOC |
|---|---|---|
| Mean-time-to-investigate | 25–45 minutes | 2–5 minutes (90–95% reduction) |
| Alert-to-triage (critical incidents) | 4–8 hours | 30–90 minutes (60–70% reduction) |
| Proactive threat hunts/month | 2–4 | 12–15 (3x increase) |
| Compliance evidence generation | 15–20 hrs/week manual | Automated |
| Tier-1 triage burden on humans | 80%+ of analyst time | Zero |
These aren’t theoretical projections. They’re the operational reality when AI eliminates triage and your team focuses exclusively on investigation, response, hunting, and strategy.
💸 Where AI Changes the Budget Conversation
The traditional path to these capabilities requires 15–20 FTEs at $1.5M–$3.6M additional salary. The AI-augmented path requires the same 10 FTEs plus $120K–$360K/year in platform cost, delivering equivalent or superior outcomes at a fraction of the scaling expense. The budget conversation shifts from “we need 5 more headcount” to “we need to deploy the headcount we have more effectively.”
“UnderDefense is a great choice for teams like ours that are short on resources. It automates many tasks, plus, with 24/7 monitoring, we know we’re always protected.”
— Inga M., CEO UnderDefense – G2 Verified Review
“With UnderDefense MAXI, we’ve reduced security breaches. Their adherence to SLAs gives me confidence in our infrastructure’s protection. As the Information Security Director, it lets me focus on strategy, knowing the day-to-day security is managed effectively.”
— Oleg K., Director Information Security UnderDefense – G2 Verified Review
We enhance teams of 10 by becoming the AI investigation and Tier-1 layer: UnderDefense MAXI eliminates triage workload across your existing 250+ tool integrations, concierge analysts augment night shifts with user verification and containment, and forever-free compliance kits automate SOC 2/ISO 27001/HIPAA evidence, delivering enterprise-grade operations without enterprise-grade headcount growth.
Q8. How Do AI-Augmented SOC Models Compare to Traditional MDR and MSSPs?
You’ve established that hiring alone won’t get you to 24/7. Now the question becomes: how do you fill the gap? The market offers three architecturally distinct approaches: traditional MSSPs, standard MDR providers, and AI SOC platforms with human response. The right choice depends on your team size, existing tool investments, and whether you need detection alone or detection AND response.
❌ Traditional MSSP: Monitoring Without Action
✅ Lowest cost entry point, broadest log coverage, and checkbox compliance.
❌ Alert-only model with no investigation capability. Rigid playbook-based escalation returns every alert to your team for manual investigation. You’re paying for monitoring, not outcomes.
⚠️ Standard MDR (Arctic Wolf, CrowdStrike, ReliaQuest): Detection + Escalation
✅ 24/7 threat detection, dedicated account teams, and strong brand recognition.
❌ Proprietary vendor lock-in forces tool replacement. Opaque pricing ($96K+ median contracts). Escalation-based response returns investigation burden to your team. No direct user verification for ambiguous threats.
“Arctic Wolf provides solid detection and response capabilities, but overly relies on the client’s team for remediation, which really hurts the value of the service.”
— VP of Technology, Services Arctic Wolf – Gartner Verified Review
“Still not quite there with the remediation side of things. We receive alerts, but not necessarily a clear path to resolution. This is not an extension of our security team as was originally sold.”
— Sr Cybersecurity Engineer, Manufacturing Arctic Wolf – Gartner Verified Review
✅ AI SOC + Human Ally (UnderDefense): Autonomous Investigation + Containment
✅ AI-driven investigation at machine speed across your existing tool stack.
✅ Human-verified response with organizational context and direct user verification.
✅ Vendor-agnostic integration preserving your current SIEM and security investments.
❌ Newer category requiring trust in AI-driven triage, mitigated by published accuracy benchmarks (99.93%) and documented case studies.
The 7-Criteria Comparison
| Criteria | Traditional MSSP | Standard MDR | UnderDefense AI SOC |
|---|---|---|---|
| Integration | Limited connectors | Proprietary stack | 250+ vendor-agnostic |
| Investigation | ❌ None | ⚠️ Analyst-dependent | ✅ AI-autonomous (<60s) |
| Response/Containment | ❌ Alert only | ⚠️ Escalation tickets | ✅ Full containment |
| User Verification | ❌ None | ❌ None | ✅ ChatOps (Slack/Teams) |
| Pricing Transparency | ⚠️ Variable | ❌ “Contact sales” | ✅ $11–$15/endpoint/mo |
| Compliance Included | ❌ Separate product | ❌ Separate product | ✅ Forever-free kits |
| Onboarding Speed | 1–3 months | 3–6 months | ✅ 30-day turnkey |
“Not having to worry about ransomware, alert overload and reporting. Getting a clear view of my security posture, where the threats are coming from and how they are handled. They literally took care of all our problems.”
— Arlin O., CIO UnderDefense – G2 Verified Review
Choose a traditional MSSP if you need basic log monitoring and have internal investigation staff. Choose standard MDR if you want 24/7 detection within a single-vendor ecosystem and can accept escalation-based response. Choose UnderDefense if you need autonomous investigation with human-verified response across your existing tool stack, transparent pricing, and 24/7 coverage without growing your team.
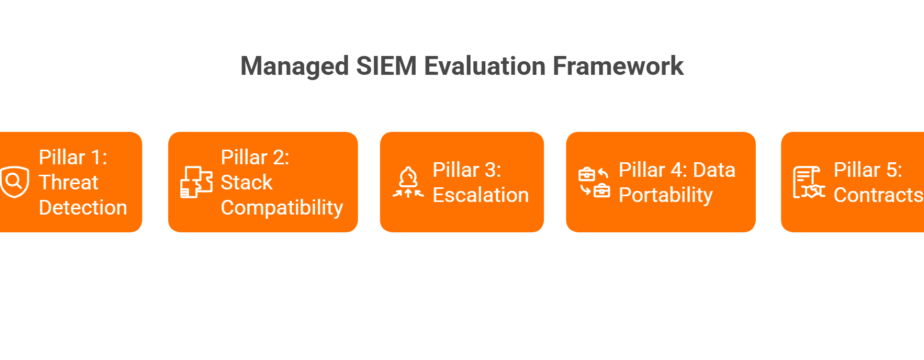
Q9. What Should You Evaluate When Choosing an AI SOC Platform to Scale Without Hiring?
Choosing an AI SOC platform is a 3–5 year architectural commitment that will define how your security operations function across every shift, every weekend, and every holiday. Pick wrong, and you’re locked into a tool that monitors without responding, requires constant tuning your team can’t support, or forces you to rip-and-replace your existing security investments. This decision deserves a framework, not a feature checklist.
⚠️ The Wrong Way to Evaluate
Most security teams evaluate based on alert volume handled, integration count on the vendor’s website, or brand recognition. This ignores the critical question: can the platform investigate AND respond to threats autonomously, or does it just classify alerts faster and escalate them back to you? The fastest triage in the world still fails if it creates 500 “please investigate” tickets per day. That’s not coverage but delegation with extra steps.
✅ The 7-Criteria Evaluation Framework
Score each AI SOC platform 0–2 on these criteria. Together, they separate genuine operational partners from monitoring tools with AI marketing:
- Autonomous Investigation Depth, Does it enrich, correlate, and make disposition decisions, or just classify alert severity?
- Human Response Layer, Does it include analysts who can verify with affected users and contain threats, or just escalate tickets?
- Integration Flexibility, Vendor-agnostic across 250+ tools, or proprietary lock-in requiring stack replacement?
- Published Response SLAs, Documented response SLAs with case study evidence, or vague “best effort” language?
- Pricing Transparency, Published per-endpoint rates you can model internally, or opaque “contact sales” gates?
- Compliance Automation, Included with security monitoring, or a separate purchase that inflates total cost?
- Time-to-Value, 30-day deployment with custom detection tuning, or a 6-month implementation project?
⭐ How to Interpret Your Scores
Platforms scoring 12–14 represent genuine operational partnerships: AI that investigates, humans who respond, and architecture that enhances your existing investments. Scoring 8–11 means partial coverage with gaps your team still fills manually. Below 8 means you’re buying faster alerting, not 24/7 coverage.
✅ UnderDefense Scorecard
| Criteria | Score | Evidence |
|---|---|---|
| Autonomous Investigation | ✅ 2/2 | Under 60-second AI investigation with enrichment |
| Human Response Layer | ✅ 2/2 | Concierge analysts + ChatOps user verification |
| Integration Flexibility | ✅ 2/2 | 250+ tools, fully vendor-agnostic |
| Published Response SLAs | ✅ 2/2 | 2-minute alert-to-triage, 15-minute escalation for critical incidents, documented case studies |
| Pricing Transparency | ✅ 2/2 | $11–$15/endpoint/month, published |
| Compliance Automation | ✅ 2/2 | Forever-free SOC 2/ISO 27001/HIPAA kits |
| Time-to-Value | ✅ 2/2 | 30-day turnkey onboarding |
| Total | 14/14 |
We built UnderDefense to score 14/14 on this framework, not because we designed the framework around our product, but because we designed our product around what security teams actually need: AI that investigates autonomously, humans who respond with context, and architecture that works with your existing security stack instead of replacing it.
💰 Use This Framework Internally
Run this scorecard against every vendor on your shortlist. Share it with your CISO, your CFO, and your procurement team. The vendors who can’t answer these seven questions transparently are the ones who will surprise you with hidden costs, slow deployments, and escalation-based response models that put the investigation burden back on your team.
Q10. What Are the Best SOC Solutions for Small Security Teams in 2026?
The leading SOC solutions for small security teams (2–10 analysts) in 2026 include AI SOC platforms (UnderDefense MAXI, Dropzone AI), managed MDR services (Arctic Wolf, CrowdStrike Falcon Complete), and SOC-as-a-Service providers, each with distinct cost structures, integration approaches, and coverage models that determine whether you actually achieve 24/7 or just pay for the label.
⭐ What Actually Matters for Small Teams
The critical question isn’t which solution has the most features but which model eliminates the coverage gap without requiring you to hire. The key differentiators that separate real coverage from expensive monitoring:
- Autonomous investigation, AI-driven disposition decisions, not just alert classification or severity scoring.
- Human response capability, Full containment and remediation, not escalation tickets that land back on your desk.
- Vendor-agnostic integration, Works with your existing SIEM, EDR, and XDR investments without forcing replacement.
- Transparent pricing, Published per-endpoint rates you can model in a spreadsheet, not “contact sales” gates behind NDA-protected quotes.
✅ 5 Questions to Ask Every Vendor
Before scheduling another demo, filter with these:
- Does the solution provide autonomous investigation or just faster alerting?
- Can it respond to threats (contain, isolate, and remediate) or only detect and notify?
- Does it integrate with your existing tools or require replacement?
- Is pricing published and per-endpoint, or hidden behind enterprise sales cycles?
- Can it onboard in weeks, not months?
If a vendor can’t answer all five clearly, they’re selling monitoring, not coverage.
💰 Your Right Choice Depends on Context
Team size, existing security investments, and whether you need monitoring or monitoring-plus-response all shape the decision. A team of 2 needs a fundamentally different model than a team of 10. For a detailed cost comparison tailored to your specific scenario, use the SOC Cost Calculator to model the numbers before you talk to any vendor. For a full vendor evaluation with features, pricing, and deployment timelines, see our complete provider breakdown.
This analysis is based on documented response times, published pricing, G2 reviews (Spring 2026), and operational outcomes across 500+ MDR deployments and 250+ tool integrations.
1. How can a security team of 2 achieve 24/7 monitoring coverage?
We’ve designed a practical AI-first operating model specifically for teams of 2 that delivers genuine 24/7 coverage. The blueprint uses staggered business-hours shifts (8AM–5PM and 9AM–6PM) with a one-hour overlap for daily handoff, while an AI SOC platform handles autonomous investigation during all off-hours, nights, weekends, and holidays.
The key is shifting from human-dependent coverage to AI-primary coverage with human oversight. AI handles 85–95% of alerts autonomously, and on-call escalation activates only for confirmed critical incidents, averaging 2–4 times per week. Your MDR partner serves as surge capacity during PTO and illness, eliminating single-point-of-failure risk.
Total infrastructure cost runs $8K–$15K/month versus $50K–$90K/month to hire 4–5 additional analysts. For the full shift matrix and a real-world 3 AM incident walkthrough, see our continuous security monitoring guide.
2. What does it actually cost to build an in-house 24/7 SOC in 2026?
We’ve modeled the true cost across hundreds of client engagements. Year-one build cost lands at $1M–$2M+, with ongoing annual costs of $1.5M–$2.5M. Staffing alone (5–8 FTEs at $100K–$180K fully loaded per analyst) runs $500K–$1.08M before tool licenses. The technology stack adds $270K–$950K annually: SIEM licensing ($50K–$250K), SOAR ($100K–$300K), EDR/XDR ($15–$50/endpoint/month), threat intelligence feeds ($25K–$100K), and data storage ($30K–$100K).
Night-shift analysts command 15–30% salary premiums with approximately 2x daytime turnover rates, and investigation accuracy drops 20–30% during overnight hours due to cognitive fatigue. An AI-augmented model with 2–3 analysts costs $300K–$720K annually with consistent 24/7 coverage quality. Use our SOC Cost Calculator to model your specific scenario.
3. How much faster does AI investigate security alerts compared to human analysts?
We’ve documented dramatic speed improvements across our client base and the broader industry. The CSA 2025 Benchmark Study shows AI-assisted analysts complete investigations 45–61% faster with 22–29% higher accuracy. Intezer’s AI SOC averages 2 minutes 21 seconds per investigation with a median of just 15 seconds. Our UnderDefense MAXI platform completes AI investigation in under 60 seconds.
The critical advantage isn’t just speed but consistency. Human investigation quality drops 20–30% during overnight hours due to cognitive fatigue, while AI maintains identical accuracy at 3 AM Saturday as it does at 10 AM Tuesday. A typical manual investigation touches 4–6 tools and takes 25–45 minutes. AI automates alert enrichment, log correlation, false-positive dismissal, and IOC matching, while humans handle contextual verification, business-impact assessment, and containment scope decisions.
4. Why is the cybersecurity hiring shortage making 24/7 SOC coverage impossible?
The structural math is broken. The global cybersecurity workforce gap has reached 4.8 million unfilled positions, a 19% year-over-year increase, while over 90% of security teams report critical skills gaps. True 24/7 coverage requires a minimum of 5–6 FTEs just for shift rotation, and SOC analyst median tenure hovers around 18 months due to alert fatigue and night-shift burnout.
For the first time, ISC2 found that economic pressures and budget cuts have overtaken lack of qualified talent as the primary driver of staffing shortages. Mid-market companies consistently lose hiring competitions to enterprises offering $200K+ packages. Even fully funded hiring takes 3–6 months to fill, followed by a 6-month ramp at roughly 40% effectiveness. A single resignation collapses coverage overnight. We’ve seen this cycle repeat across hundreds of engagements, which is why we built our MDR service to eliminate the dependency on hiring as a coverage strategy.
5. What happens to security alerts during nights and weekends when no one is monitoring?
Adversaries know exactly when you’re understaffed, and they exploit it. CrowdStrike’s 2026 Global Threat Report documents average eCrime breakout time dropping to 29 minutes, with a fastest recorded time of 27 seconds. A typical understaffed SOC has zero human coverage for 76–128 hours per week across nights, weekends, and holidays.
IBM’s 2025 Cost of a Data Breach Report quantifies the damage: breaches contained in under 200 days averaged $3.87 million, while those exceeding 200 days cost $5.01 million, a 29% increase. When the attacker discloses the breach first, average cost jumps to $5.08 million. Every uncovered hour is a compounding risk multiplier. With AI-augmented coverage, the 3 AM alert gets investigated in 15 seconds, correlated, and auto-contained before your team wakes up. Learn more about closing this gap with documented SLA frameworks.
6. How do AI-augmented SOC models compare to traditional MDR and MSSPs?
We evaluate three architecturally distinct approaches across seven criteria. Traditional MSSPs offer the lowest cost entry point with broad log coverage, but provide alert-only models with no investigation capability, returning every alert to your team.
Standard MDR providers (Arctic Wolf, CrowdStrike, ReliaQuest) deliver 24/7 detection with dedicated teams, but proprietary vendor lock-in forces tool replacement, pricing is opaque ($96K+ median contracts), and escalation-based response puts investigation burden back on you.
AI SOC platforms with human response, like UnderDefense, provide autonomous investigation in under 60 seconds across your existing tool stack, human-verified containment with direct user verification via ChatOps, vendor-agnostic integration with 250+ tools, and transparent pricing at $11–$15/endpoint/month. The right choice depends on whether you need monitoring alone or detection AND response.
7. What evaluation criteria should I use when choosing an AI SOC platform?
We recommend a 7-criteria scoring framework (0–2 per criterion, 14 points maximum) that separates genuine operational partners from monitoring tools with AI marketing:
- Autonomous Investigation Depth: enrichment and disposition decisions, not just severity classification
- Human Response Layer: analysts who verify and contain, not just escalate tickets
- Integration Flexibility: vendor-agnostic across 250+ tools, not proprietary lock-in
- Published Response SLAs: documented 2-minute alert-to-triage and 15-minute escalation benchmarks
- Pricing Transparency: published per-endpoint rates, not “contact sales” gates
- Compliance Automation: included, not a separate upsell
- Time-to-Value: 30-day deployment, not 6-month implementation
Platforms scoring 12–14 represent genuine partnerships. Below 8 means you’re buying faster alerting, not coverage. Run this scorecard against every vendor and share it with your CISO, CFO, and procurement team.
8. How does AI SOC coverage improve analyst retention and reduce burnout?
We’ve observed that the 18-month SOC analyst burnout cycle isn’t caused by compensation gaps but by the nature of the work itself. In a traditional model, analysts spend 80% of their time on Tier-1 alert triage, processing thousands of false positives daily, leading to monotonous, burnout-inducing work.
With AI handling autonomous triage, the role transformation is dramatic: 20% AI-escalated review, 40% proactive threat hunting, and 40% incident response and process improvement. Analysts doing strategic work stay 2–3x longer than those drowning in false positives. When your SOC analyst spends Tuesday morning hunting for signs of credential abuse instead of closing 400 false-positive alerts, they’re building skills, finding real threats, and staying engaged. This addresses retention at its root cause, not with higher compensation but with better work. See how this model scales in our SOC automation guide.
The post 24/7 Security Monitoring Without Growing Your Team: The Practitioner’s Blueprint from 500+ MDR Deployments appeared first on UnderDefense.